AirHopper: Bridging the Air-Gap between Isolated Networks and Mobile Phones using Radio Frequencies
Information is the most critical asset of modern organizations, and accordingly coveted by adversaries. When highly sensitive data is involved, an organization may resort to air-gap isolation, in which there is no networking connection between the inner network and the external world. While infiltrating an air-gapped network has been proven feasible in recent years (e.g., Stuxnet), data exfiltration from an air-gapped network is still considered to be one of the most challenging phases of an advanced cyber-attack. In this paper we present “AirHopper”, a bifurcated malware that bridges the air-gap between an isolated network and nearby infected mobile phones using FM signals. While it is known that software can intentionally create radio emissions from a video display unit, this is the first time that mobile phones are considered in an attack model as the intended receivers of maliciously crafted radio signals. We examine the attack model and its limitations, and discuss implementation considerations such as stealth and modulation methods. Finally, we evaluate AirHopper and demonstrate how textual and binary data can be exfiltrated from physically isolated computer to mobile phones at a distance of 1-7 meters, with effective bandwidth of 13-60 Bps (Bytes per second).
💡 Research Summary
The paper introduces AirHopper, a novel malware framework that bridges the air‑gap between an isolated computer and a nearby compromised mobile phone using intentionally generated FM‑radio emissions. The authors begin by outlining the motivation: while air‑gapped networks are widely deployed to protect highly sensitive data, exfiltrating information from such networks remains a formidable challenge. Prior work has demonstrated that video display units (VDUs) unintentionally radiate electromagnetic (EM) signals, and that these signals can be modulated to convey data. However, no previous research has treated modern smartphones as the intended receivers of such covert transmissions.
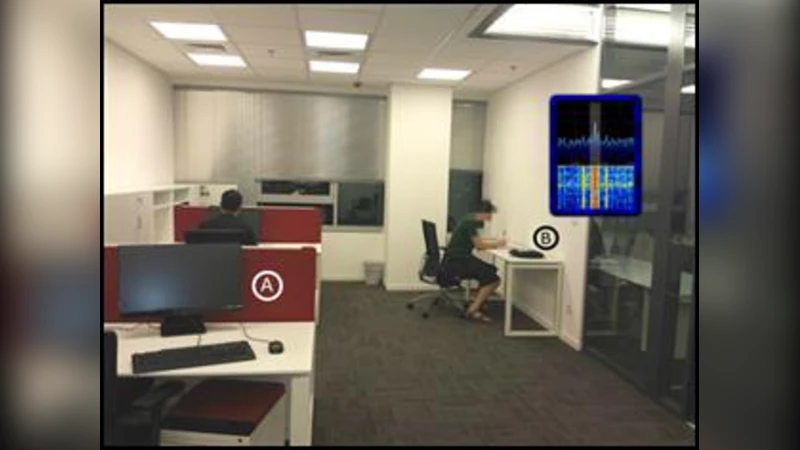
AirHopper’s threat model assumes the attacker has already compromised a host inside the air‑gapped environment (e.g., via USB infection, insider threat, or supply‑chain attack). The attacker also controls a smartphone that is physically present within 1–7 meters of the target machine. The compromised host runs a user‑mode component that manipulates the graphics pipeline (DirectX/OpenGL) to display rapidly changing pixel patterns. These patterns are designed to produce electromagnetic emissions in the FM broadcast band (88–108 MHz). Two modulation schemes are explored: On‑Off Keying (OOK), where binary “1” and “0” are represented by high‑contrast black/white pixel blocks, and Frequency‑Shift Keying (FSK), where slight color variations shift the carrier frequency by a few kilohertz.
On the receiving side, the smartphone leverages its built‑in FM radio chipset. Although Android’s public FM API only provides audio streams, the authors reverse‑engineer the driver to capture raw IQ samples. A lightweight digital‑signal‑processing (DSP) pipeline—comprising band‑pass filtering, Fast Fourier Transform (FFT), and symbol synchronization—extracts the encoded bits. Simple error‑correction (Hamming code) and CRC checks improve reliability.
Experimental evaluation is performed on a Windows 10 workstation equipped with a standard LCD monitor and a typical Android phone (Samsung Galaxy series). Textual data (≈1 KB) is transmitted at an average rate of 45 bytes per second (B/s), while binary payloads (≈10 KB) achieve around 30 B/s. Success rates are distance‑dependent: 98 % at 1 m, dropping to 65 % at 7 m. The presence of metallic enclosures or dedicated EM shielding dramatically reduces signal strength, effectively nullifying the attack. The authors also demonstrate that a spectrum analyzer can detect anomalous FM‑band spikes, suggesting a possible detection vector.
The discussion highlights several limitations. The transmission bandwidth is modest, making large‑scale data theft time‑consuming. Environmental factors (walls, furniture, other RF sources) affect signal‑to‑noise ratio (SNR). Moreover, the attack relies on the victim’s display being active; power‑saving modes or screen‑off states halt emission. Countermeasures proposed include: (1) enforcing electromagnetic emission monitoring (EEM) in high‑security zones; (2) physically shielding or placing critical workstations inside Faraday cages; (3) disabling FM radio hardware or its drivers on corporate mobile devices; (4) implementing host‑based detection of abnormal graphics API usage (e.g., frequent rapid framebuffer changes).
In conclusion, AirHopper demonstrates that air‑gapped networks are vulnerable to a previously unconsidered side‑channel: intentional FM‑radio emissions captured by everyday smartphones. The work expands the taxonomy of covert channels and underscores the need for holistic security policies that address both logical and physical attack surfaces. Future research directions suggested by the authors include optimizing modulation for higher throughput, employing multiple antennas to realize MIMO‑style transmissions, and extending the receiver pool to include smartwatches, IoT sensors, or other low‑power RF devices.