A First Look at Firefox OS Security
With Firefox OS, Mozilla is making a serious push for an HTML5-based mobile platform. In order to assuage security concerns over providing hardware access to web applications, Mozilla has introduced a number of mechanisms that make the security landscape of Firefox OS distinct from both the desktop web and other mobile operating systems. From an application security perspective, the two most significant of these mechanisms are the the introduction of a default Content Security Policy and code review in the market. This paper describes how lightweight static analysis can augment these mechanisms to find vulnerabilities which have otherwise been missed. We provide examples of privileged applications in the market that contain vulnerabilities that can be automatically detected. In addition to these findings, we show some of the challenges that occur when desktop software is repurposed for a mobile operating system. In particular, we argue that the caching of certificate overrides across applications–a known problem in Firefox OS–generates a counter-intuitive user experience that detracts from the security of the system.
💡 Research Summary
The paper provides a systematic examination of the security architecture of Firefox OS, Mozilla’s HTML5‑based mobile platform that allows web applications direct access to device hardware. To mitigate the inherent risks of such openness, Mozilla has introduced two primary defensive mechanisms: a default Content Security Policy (CSP) that is automatically applied to every app, and a manual code‑review process for applications submitted to the Firefox OS Marketplace. While these measures represent a significant step forward compared to earlier mobile operating systems, the authors demonstrate that they are not sufficient to guarantee the absence of exploitable flaws in real‑world deployments.
To bridge this gap, the researchers built a lightweight static‑analysis framework tailored to the peculiarities of Firefox OS. The tool parses JavaScript source into an abstract syntax tree (AST) and then scans for a set of well‑defined patterns: CSP violations (e.g., dynamic insertion of inline scripts that bypass the policy), usage of unsafe dynamic code execution primitives such as eval or new Function, DOM‑based cross‑site scripting (XSS) vectors, and improper use of privileged APIs (e.g., navigator.mozApps.install) without adequate input validation. Because the analysis is purely syntactic and runs in a matter of seconds, it can be integrated into the Marketplace submission pipeline to provide continuous, automated vetting of new apps.
Applying the analyzer to a corpus of privileged applications currently available in the Marketplace, the authors uncovered several classes of vulnerabilities that had escaped both the default CSP and human code review. First, many apps declared a CSP but subsequently constructed script elements at runtime, effectively sidestepping the policy’s restriction on inline code. Second, a non‑trivial number of apps still contained calls to eval or new Function, opening a direct path for attacker‑controlled code injection. Third, privileged APIs were invoked without sanitizing parameters, creating opportunities for privilege escalation or unauthorized access to device resources. Each of these findings could be automatically flagged by the static analyzer, illustrating its practical utility as a complementary security layer.
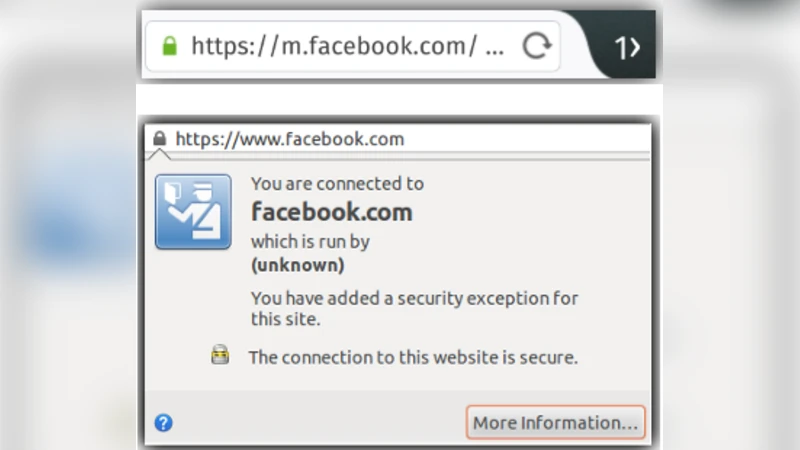
Beyond application‑level bugs, the paper highlights a systemic issue inherited from desktop Firefox: the caching of SSL certificate overrides across applications. When a user encounters a certificate error in a particular app and chooses to “add an exception,” the exception is stored in a global cache rather than being scoped to the offending app. Consequently, any other app that later accesses the same domain will automatically trust the previously overridden certificate, even if the user never interacted with that second app. This behavior is especially problematic on mobile devices, where users are less likely to scrutinize security warnings and where app isolation is weaker than on desktops. An attacker could deliberately trigger a certificate warning in a benign‑looking app, persuade the user to add an exception, and then exploit the globally trusted certificate from a malicious app to harvest credentials or perform man‑in‑the‑middle attacks.
The authors argue that addressing these shortcomings requires a multi‑pronged approach. First, the Marketplace should incorporate automated static (and, where feasible, dynamic) analysis as a mandatory gate before any app is published. Second, the certificate‑override mechanism must be redesigned to be app‑specific or to require explicit, per‑app confirmation each time an overridden certificate is used, thereby preventing inadvertent credential leakage across app boundaries. Third, development guidelines should be tightened to forbid the use of dynamic code execution constructs and to mandate thorough validation of all inputs to privileged APIs. Linting rules and continuous‑integration checks could enforce these policies at the developer level.
In conclusion, while Firefox OS’s default CSP and marketplace code review represent a solid foundation, the paper demonstrates that they alone cannot guarantee a secure ecosystem. Lightweight static analysis can effectively uncover hidden vulnerabilities in privileged applications, and a careful redesign of certificate‑override handling can eliminate a counter‑intuitive user experience that currently undermines security. By integrating automated analysis into the app‑submission workflow and refining system‑wide security policies, Mozilla can significantly raise the security posture of Firefox OS and provide a safer environment for HTML5‑driven mobile applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment