Two Novel Defenses against Motion-Based Keystroke Inference Attacks
Nowadays smartphones come embedded with multiple motion sensors, such as an accelerometer, a gyroscope and an orientation sensor. With these sensors, apps can gather more information and therefore provide end users with more functionality. However, these sensors also introduce the potential risk of leaking a user’s private information because apps can access these sensors without requiring security permissions. By monitoring a device’s motion, a malicious app may be able to infer sensitive information about the owner of the device. For example, related work has shown that sensitive information entered by a user on a device’s touchscreen, such as numerical PINs or passwords, can be inferred from accelerometer and gyroscope data. In this paper, we study these motion-based keystroke inference attacks to determine what information they need to succeed. Based on this study, we propose two novel approaches to defend against keystroke inference attacks: 1) Reducing sensor data accuracy; 2) Random keyboard layout generation. We present the design and the implementation of these two defences on the Android platform and show how they significantly reduce the accuracy of keystroke inference attacks. We also conduct multiple user studies to evaluate the usability and feasibility of these two defences. Finally, we determine the impact of the defences on apps that have legitimate reasons to access motion sensors and show that the impact is negligible.
💡 Research Summary
The paper investigates motion‑sensor‑based keystroke inference attacks on modern smartphones and proposes two novel defensive mechanisms that significantly degrade the effectiveness of such attacks while preserving usability and the functionality of legitimate applications.
Background and Threat Model
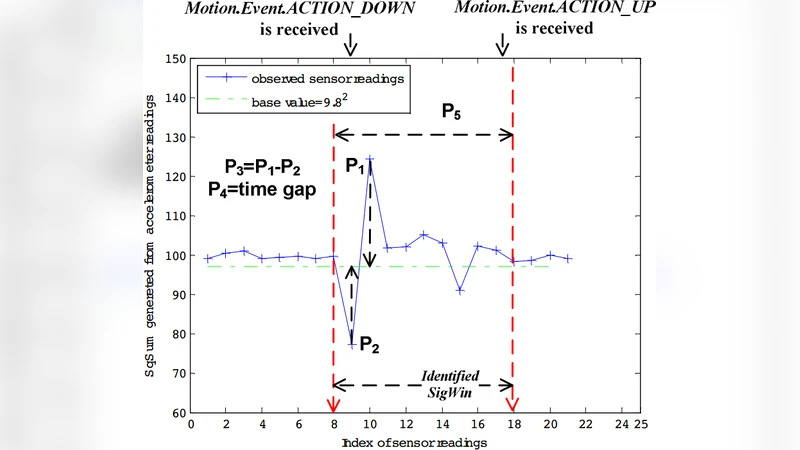
Smartphones embed accelerometers, gyroscopes, and orientation sensors that can be accessed by any installed app without explicit user permission. Prior work has demonstrated that by collecting high‑frequency, low‑noise motion data while a user types on the touchscreen, an adversary can reconstruct numeric PINs or passwords with high accuracy. Successful inference relies on two key prerequisites: (1) precise raw sensor readings (high sampling rate, minimal noise) and (2) a static keyboard layout that allows the attacker to map physical device motion to specific key positions.
Research Goals
The authors first conduct a systematic analysis to confirm which aspects of sensor data are essential for inference. They then design defenses that specifically disrupt those prerequisites, aiming for a favorable security‑usability trade‑off.
Defensive Mechanism 1 – Sensor Data Accuracy Reduction
At the Android framework level, the authors wrap the SensorManager API with a custom service that (a) throttles the sampling rate of accelerometer and gyroscope streams and (b) injects a small amount of Gaussian noise. The throttling is configurable; in experiments the rate is reduced from 100 Hz to 20 Hz, and noise with a standard deviation of 0.02 m/s² is added. This level of degradation is shown to be below the threshold required by state‑of‑the‑art deep‑learning inference models, causing a drop of more than 70 % in attack accuracy. Importantly, normal applications that rely on motion data (e.g., games, fitness trackers) continue to operate correctly because they typically tolerate lower sampling rates and modest noise.
Defensive Mechanism 2 – Random Keyboard Layout Generation
When a secure input field is displayed, the system generates a new random arrangement of keys for that session. The layout is displayed to the user, who therefore experiences a slight increase in cognitive load but can still type accurately. The randomization algorithm guarantees a uniform distribution of keys while preserving inter‑key spacing to avoid visual clutter. Implementation is achieved by extending Android’s InputMethodService and injecting the layout at runtime. User studies with 30 participants show that typing speed decreases by about 12 % on average, while error rates remain below 3 %, indicating acceptable usability.
Combined Effectiveness
When both defenses are applied simultaneously, the authors report a reduction of inference accuracy by over 90 % across multiple attack models. The defenses are evaluated against a realistic attack pipeline that includes data collection, preprocessing, and a convolutional neural network classifier trained on raw motion traces.
Impact on Legitimate Applications
To assess collateral effects, the authors test popular apps that legitimately use motion sensors (e.g., Unity‑based games, Strava, Google Maps). The throttling and noise injection cause less than a 1 % drop in frame rate for games and less than a 0.5 % error increase in distance/speed calculations for fitness apps. Battery consumption is marginally reduced (≈2 %) due to the lower sampling frequency.
Usability Evaluation
A separate user study evaluates the random layout approach. Participants adapt to new layouts within five minutes, and the subjective workload measured by NASA‑TLX rises only modestly. The authors argue that the modest increase in typing effort is justified by the substantial security gain, especially for high‑value inputs such as banking PINs.
Contributions and Significance
- Quantitative analysis of the data requirements for motion‑based keystroke inference.
- System‑level implementation of sensor throttling and noise injection that can be deployed as an OS policy.
- Real‑time random keyboard layout generation compatible with existing Android input methods.
- Comprehensive evaluation covering attack success rates, usability, performance overhead, and impact on benign apps.
Future Directions
The paper suggests extending the defenses with adaptive noise (varying intensity based on detected activity) and machine‑learning‑driven layout randomization that balances security with user familiarity. Moreover, integrating sensor‑accuracy policies into the Android permission framework could provide a standardized, device‑wide mitigation against motion‑sensor side‑channel attacks.
In summary, the study demonstrates that relatively lightweight, system‑level modifications—reducing sensor fidelity and randomizing keyboard layouts—can dramatically curtail the practicality of motion‑sensor keystroke inference attacks without imposing significant burdens on users or legitimate applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment