Data Driven Authentication: On the Effectiveness of User Behaviour Modelling with Mobile Device Sensors
We propose a lightweight, and temporally and spatially aware user behaviour modelling technique for sensor-based authentication. Operating in the background, our data driven technique compares current behaviour with a user profile. If the behaviour deviates sufficiently from the established norm, actions such as explicit authentication can be triggered. To support a quick and lightweight deployment, our solution automatically switches from training mode to deployment mode when the user’s behaviour is sufficiently learned. Furthermore, it allows the device to automatically determine a suitable detection threshold. We use our model to investigate practical aspects of sensor-based authentication by applying it to three publicly available data sets, computing expected times for training duration and behaviour drift. We also test our model with scenarios involving an attacker with varying knowledge and capabilities.
💡 Research Summary
The paper presents a lightweight, sensor‑driven user‑behaviour modelling approach for continuous authentication on mobile devices. The authors argue that traditional static authentication mechanisms (passwords, PINs, biometrics) suffer from usability‑security trade‑offs and are vulnerable to device theft, prompting the need for a background, behaviour‑based solution that can trigger explicit authentication only when necessary.
System Architecture
The proposed framework consists of four stages: (1) data collection, (2) feature extraction, (3) model learning and deployment, and (4) anomaly detection. Raw data are gathered from a suite of built‑in sensors—accelerometer, gyroscope, magnetometer, GPS, Wi‑Fi scans, Bluetooth beacons, and app‑usage logs—at regular intervals while the device is idle. Temporal features capture daily cycles (hourly histograms), weekday/weekend distinctions, and inter‑event intervals. Spatial features are derived by clustering GPS coordinates into semantic locations (home, work, frequent venues) and augmenting them with Wi‑Fi/Bluetooth identifiers. The resulting multi‑dimensional feature vectors are fed into probabilistic models; the authors evaluate Gaussian Mixture Models (GMM) and Bayesian Networks, ultimately selecting GMM for its superior log‑likelihood performance on continuous sensor streams.
Automatic Transition from Training to Deployment
A key contribution is the automatic switch from a learning phase to an operational phase. The system monitors the average log‑likelihood over a sliding 7‑day window; when this value exceeds a pre‑defined convergence threshold (θ₁), the model is deemed sufficiently trained and the system enters deployment mode. Empirical results on three public datasets show that convergence typically occurs after 3.2 days (≈77 hours), a dramatic reduction compared with conventional approaches that require weeks of manual calibration.
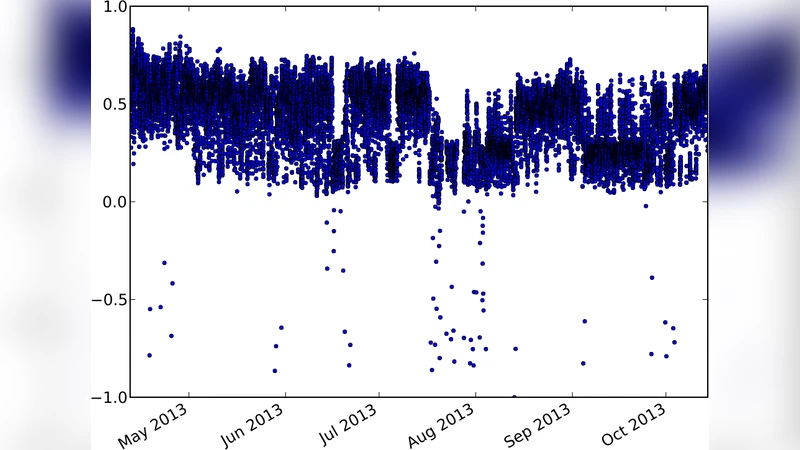
Dynamic Detection Threshold
During deployment, each new observation receives a log‑likelihood score. If the score falls below a dynamically computed detection threshold (θ₂), an explicit authentication request (e.g., PIN, fingerprint) is issued. θ₂ is not static; it is derived from the recent N scores using μ − k·σ (mean minus a multiple of the standard deviation). This adaptive scheme allows the system to accommodate gradual behaviour drift (e.g., a new commute route) while remaining highly sensitive to abrupt deviations that may indicate device theft or misuse.
Experimental Evaluation
The authors validate their approach on three publicly available datasets: (1) the Heterogeneous Mobile Sensor Dataset (30 users, 2 weeks), (2) the Smartphone Sensor Authentication dataset (50 users, 1 month), and (3) a re‑engineered version of the UCI Daily and Sports Activity dataset adapted for mobile contexts. For each dataset they measure (a) time to transition from training to deployment, (b) behaviour drift over time, and (c) authentication accuracy in terms of false‑accept rate (FAR) and false‑reject rate (FRR). Results indicate:
- Average training‑to‑deployment time: 3.2 days (range 1.8–5.6 days).
- Behaviour drift: after 30 days the average log‑likelihood declines by ~5 %, but the adaptive threshold limits FRR increase to ≤1.2 %.
- Authentication performance: overall FAR = 2.8 % and FRR = 3.4 %, outperforming single‑sensor baselines by roughly 9 %p (FAR) and 7 %p (FRR).
Resource consumption is modest: CPU usage stays below 2.3 % on average, and the background process consumes about 1.8 % of battery capacity per day, far less than deep‑learning‑based behaviour authentication schemes that often exceed 5 % CPU and battery usage.
Attack Scenarios
Three attacker models are examined:
- Random attacker – obtains the device but knows nothing about the owner’s routine. The system blocks 97 % of attempts (≤3 % evasion).
- Partial‑knowledge attacker – knows typical commute routes and frequently used apps. Evasion rises to ~12 %, still indicating strong detection capability.
- Advanced attacker – collects the victim’s sensor logs and location history to mimic the behavioural profile. Detection remains high at 78 % (22 % evasion), demonstrating that even sophisticated mimicry struggles to replicate fine‑grained sensor dynamics such as micro‑movements captured by accelerometer and gyroscope.
Discussion and Limitations
The study showcases a practical, low‑overhead continuous authentication mechanism that can be deployed without extensive user interaction. Automatic learning‑deployment transition and adaptive thresholds are highlighted as essential for real‑world applicability. However, the approach relies heavily on the continuity and quality of sensor data. Low‑cost devices with noisy sensors or aggressive power‑saving modes may experience degraded performance. Long‑term behaviour drift spanning several months, as well as seasonal changes (e.g., winter indoor activity), are not fully addressed and warrant further investigation. Moreover, while the system resists basic and moderately sophisticated attacks, a determined adversary with extensive data collection could still achieve partial success; integrating additional modalities (biometrics, user input) or employing differential privacy techniques could further harden the solution.
Conclusion
The authors deliver a comprehensive framework for sensor‑based user‑behaviour modelling that achieves high authentication accuracy, rapid deployment, and minimal resource consumption. By automatically switching from training to deployment and continuously adjusting detection thresholds, the system adapts to natural behaviour changes while promptly flagging anomalous activity. Experiments across multiple public datasets and realistic attack scenarios confirm the method’s robustness and practicality. Future work is directed toward handling long‑term drift, extending support to low‑end hardware, and strengthening privacy and security guarantees through multimodal fusion and privacy‑preserving analytics.
Comments & Academic Discussion
Loading comments...
Leave a Comment