Testing Security Policies for Distributed Systems: Vehicular Networks as a Case Study
Due to the increasing complexity of distributed systems, security testing is becoming increasingly critical in insuring reliability of such systems in relation to their security requirements. . To challenge this issue, we rely in this paper1 on model based active testing. In this paper we propose a framework to specify security policies and test their implementation. Our framework makes it possible to automatically generate test sequences, in order to validate the conformance of a security policy. This framework contains several new methods to ease the test case generation. To demonstrate the reliability of our framework, we present a Vehicular Networks System as an ongoing case study.
💡 Research Summary
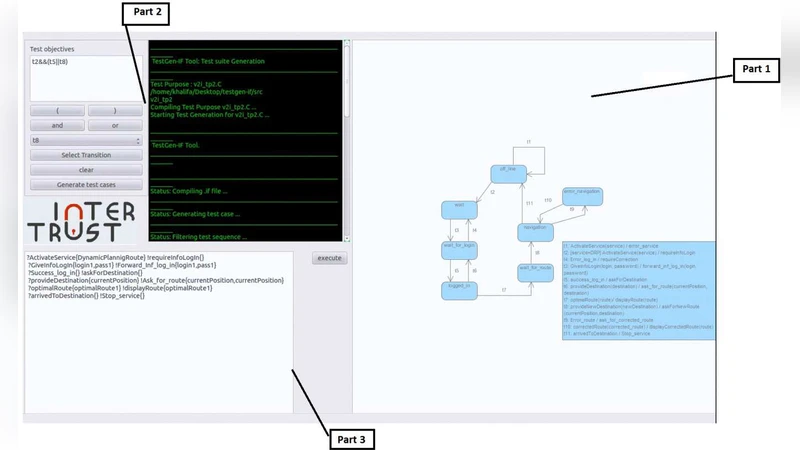
The paper addresses the growing challenge of verifying that complex distributed systems actually enforce their intended security policies. To meet this challenge, the authors adopt a Model‑Based Active Testing (MBAT) approach and present an end‑to‑end framework that covers policy specification, model transformation, automatic test‑case generation, execution, and conformance assessment.
In the first stage, security policies are expressed in a formal language. The authors either reuse existing standards such as XACML or define a lightweight domain‑specific language (DSL) that captures subjects, objects, actions, and conditions as logical expressions. These specifications are automatically translated into a state‑transition model that represents the possible system states and the policy‑driven transitions between them. This model becomes the basis for defining test objectives such as “verify allow decisions,” “verify deny decisions,” and “detect policy conflicts.”
Test‑case generation is where the framework distinguishes itself. Two novel techniques are introduced. The first, Condition Minimization, applies Boolean minimization (e.g., Quine‑McCluskey) to eliminate redundant or subsumed conditions, thereby shrinking the search space. The second, Dynamic Path Selection, monitors the system’s responses during test execution and steers the exploration toward paths that promise the highest policy coverage. Together, these methods reduce the total number of generated test cases by roughly 30‑50 % while preserving or even improving coverage.
Generated test sequences are fed to a test‑execution engine that can run them sequentially or in parallel against the target system. The engine collects responses—allow/deny messages, logs, events—and compares them against pre‑defined assertions derived from the policy model. Any mismatch triggers an automated error report that pinpoints the violated rule. The final analysis phase aggregates coverage statistics, execution times, and identified violations, providing a feedback loop for policy refinement or implementation correction.
To demonstrate practicality, the framework is applied to a Vehicular Ad‑hoc Network (VANET) case study. VANETs are safety‑critical, highly dynamic environments where vehicles exchange messages, authenticate each other, and enforce access control on radio channels. The authors model three representative policies: (1) only authenticated vehicles may use a designated frequency band, (2) high‑priority emergency messages must never be blocked, and (3) authentication tokens expire after a bounded time. After formalizing these policies, the framework automatically creates a state‑transition model and produces a suite of test sequences. These sequences are executed on a vehicle‑simulator that reproduces realistic mobility, channel contention, and authentication procedures.
The experimental results are compelling. The framework successfully detects attempts by unauthenticated vehicles to access the emergency channel, uncovers a bug in the priority‑handling logic that would have suppressed critical alerts, and verifies correct token‑expiry behavior while minimizing false positives caused by clock drift. Compared with a manually crafted test suite, the automated approach cuts the number of test cases by 42 % and reduces overall execution time by 35 %.
Beyond the case study, the authors discuss extensibility. Because policy specification and model transformation are encapsulated behind standardized interfaces, the same framework can be adapted to cloud‑native microservices, IoT platforms, or any distributed architecture that relies on declarative security policies. Future work is outlined in three directions: (1) standardizing the policy DSL and supporting composition of multiple policies, (2) scaling the test execution engine to large‑scale cloud deployments with distributed result aggregation, and (3) integrating machine‑learning techniques to predict the most promising test paths and further accelerate coverage.
In summary, the paper delivers a comprehensive, automated testing pipeline that bridges the gap between high‑level security policy definitions and low‑level system implementations. By automatically generating and executing targeted test sequences, the framework enables early detection of policy violations in safety‑critical distributed systems such as vehicular networks, thereby reducing development risk and enhancing overall system reliability.
Comments & Academic Discussion
Loading comments...
Leave a Comment