Analysis of Phishing Attacks and Countermeasures
One of the biggest problems with the Internet technology is the unwanted spam emails. The well disguised phishing email comes in as part of the spam and makes its entry into the inbox quite frequently nowadays. While phishing is normally considered a consumer issue, the fraudulent tactics the phishers use are now intimidating the corporate sector as well. In this paper, we analyze the various aspects of phishing attacks and draw on some possible defenses as countermeasures. We initially address the different forms of phishing attacks in theory, and then look at some examples of attacks in practice, along with their common defenses. We also highlight some recent statistical data on phishing scam to project the seriousness of the problem. Finally, some specific phishing countermeasures at both the user level and the organization level are listed, and a multi-layered anti-phishing proposal is presented to round up our studies.
💡 Research Summary
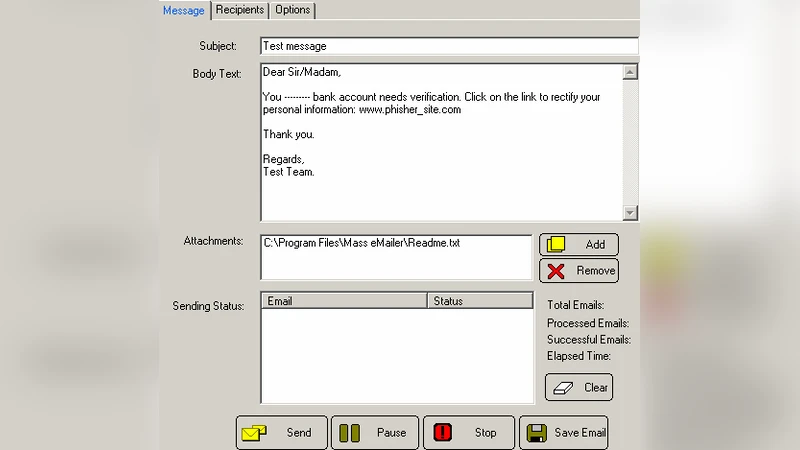
The paper provides a comprehensive examination of phishing attacks, tracing their evolution from simple spam‑based scams to sophisticated, targeted threats that jeopardize both individual users and corporate enterprises. It begins by categorizing phishing techniques into several distinct families: traditional bulk phishing, spear‑phishing, pharming, clone‑phishing, mobile‑phishing, and social‑media‑based phishing. For each family, the authors describe the underlying social‑engineering tactics—such as authority impersonation, urgency cues, and personalization—and the technical mechanisms employed, including URL obfuscation, DNS cache poisoning, malicious advertisements, and malicious macro‑enabled documents.
To illustrate real‑world impact, the paper presents detailed case studies. One notable example is a 2022 spear‑phishing campaign against a major financial institution, where attackers harvested executive LinkedIn profiles, crafted a counterfeit invoice with a malicious macro, and successfully exfiltrated roughly ten million dollars after compromising an accountant’s workstation. Another case involves a pharming operation that hijacked DNS records of a popular e‑commerce site, leading unsuspecting shoppers to a counterfeit login portal and resulting in massive credential theft. These incidents underscore how attackers blend psychological manipulation with evolving network and software vulnerabilities.
The defensive portion of the study is divided into user‑level and organization‑level countermeasures. At the user level, the authors advocate regular phishing‑awareness training, careful inspection of email headers and links, and a policy of never entering credentials on unsolicited pages. At the organizational level, they recommend a layered technical stack: full deployment of email authentication standards (DKIM, SPF, DMARC) to block forged messages; URL filtering and web‑proxy solutions to prevent access to known malicious domains; sandbox environments for dynamic analysis of attachments; and behavior‑based anomaly detection systems.
A significant contribution of the paper is its discussion of machine‑learning‑driven phishing detection. By engineering features from email metadata, textual content, and hyperlink structures, hybrid models that combine supervised classifiers with unsupervised clustering achieve high detection rates while maintaining low false‑positive levels. The authors also stress the importance of integrating external threat‑intelligence feeds to enrich detection capabilities.
Beyond technical controls, the authors emphasize governance measures: implementing the principle of least privilege, enforcing multi‑factor authentication (MFA) for privileged accounts, conducting periodic penetration testing and security audits, and establishing a formal incident‑response plan that includes automated quarantine of suspicious messages and rapid user notification.
Synthesizing these elements, the paper proposes a multi‑layered anti‑phishing framework composed of four interlocking tiers: (1) human awareness and education, (2) email authentication and filtering technologies, (3) organizational policies and access controls, and (4) real‑time intelligence‑driven analytics powered by machine learning. The framework is designed so that the failure of any single layer does not compromise overall security, thereby providing resilience against the continuously evolving phishing landscape. In conclusion, the authors argue that sustained investment in education, cutting‑edge detection technologies, and robust security governance is essential to mitigate the growing threat posed by phishing attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment