Calm Before the Storm: The Challenges of Cloud Computing in Digital Forensics
Cloud computing is a rapidly evolving information technology (IT) phenomenon. Rather than procure, deploy and manage a physical IT infrastructure to host their software applications, organizations are increasingly deploying their infrastructure into remote, virtualized environments, often hosted and managed by third parties. This development has significant implications for digital forensic investigators, equipment vendors, law enforcement, as well as corporate compliance and audit departments (among others). Much of digital forensic practice assumes careful control and management of IT assets (particularly data storage) during the conduct of an investigation. This paper summarises the key aspects of cloud computing and analyses how established digital forensic procedures will be invalidated in this new environment. Several new research challenges addressing this changing context are also identified and discussed.
💡 Research Summary
The paper examines how the rapid adoption of cloud computing reshapes the landscape of digital forensics, rendering many traditional investigative procedures ineffective. It begins by outlining the core characteristics of cloud services—Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS)—and explains how responsibility for data storage, management, and access is distributed among providers and customers across these models.
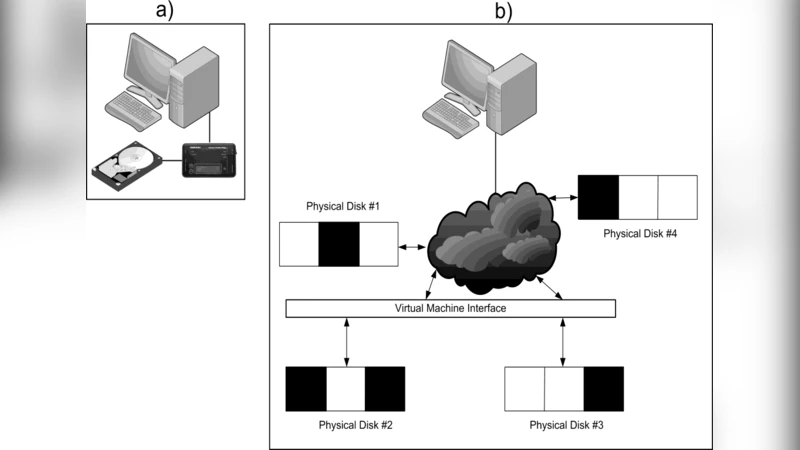
Next, the authors map the classic forensic workflow—identification, collection, preservation, analysis, and reporting—onto cloud environments and highlight the specific breakdown points. Physical disk imaging, a cornerstone of evidence acquisition, is no longer feasible; investigators must rely on provider‑supplied APIs, virtual‑machine snapshots, or forensic‑ready export functions, each of which may be restricted by service‑level agreements or technical limitations. Multi‑tenancy introduces the risk of cross‑contamination, as data from different customers co‑resides on shared hardware, raising privacy and admissibility concerns.
Jurisdictional complexity is another major obstacle. Cloud data can be replicated across data centers in multiple countries, subjecting it to a patchwork of national privacy statutes and criminal procedure codes. Consequently, investigators must first determine the physical location of the relevant data and then navigate mutual legal assistance treaties or other international cooperation mechanisms, which are often slow and bureaucratically cumbersome.
The paper stresses the pivotal role of logs and metadata. While cloud providers generate extensive operational, access, and event logs, these are typically non‑standardized, retained for limited periods, and may be filtered before delivery to investigators. Ensuring log integrity and establishing a reliable chain of custody therefore requires explicit contractual provisions and, ideally, a standardized logging framework.
From a technical standpoint, existing forensic tools are largely designed for physical media or static virtual images and lack native support for API‑driven extraction, encrypted storage handling, or real‑time data streaming. The authors advocate for the development of cloud‑aware forensic interfaces, cryptographic hash verification mechanisms, and automated chain‑of‑custody management systems that can operate within the provider’s ecosystem without compromising data segregation.
Finally, the paper outlines a research agenda: (1) model‑specific evidence‑collection guidelines; (2) techniques for isolating and protecting tenant data in multi‑tenant clouds; (3) standardized protocols for cross‑border evidence sharing; (4) universal logging formats and long‑term retention policies; (5) automated forensic toolkits tailored to cloud architectures; and (6) legal and contractual frameworks that embed forensic support clauses into service agreements. By addressing these challenges, the digital forensic community can adapt its methodologies to maintain evidentiary reliability in the increasingly dominant cloud computing era.