The Case for a Collaborative Universal Peer-to-Peer Botnet Investigation Framework
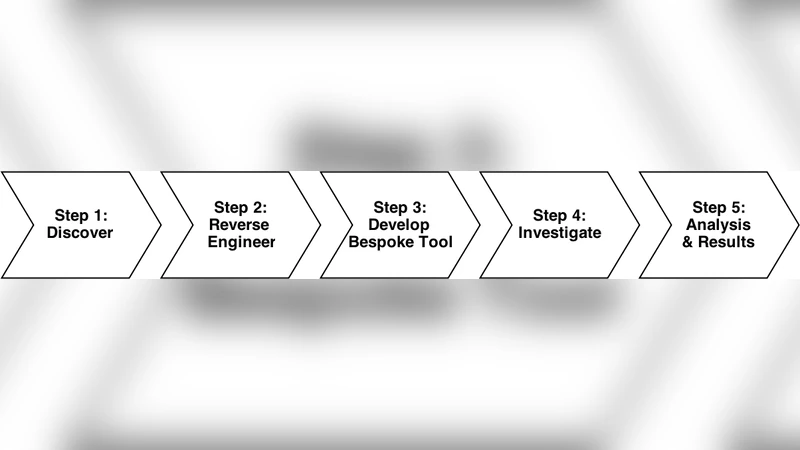
Peer-to-Peer (P2P) botnets are becoming widely used as a low-overhead, efficient, self-maintaining, distributed alternative to the traditional client/server model across a broad range of cyberattacks. These cyberattacks can take the form of distributed denial of service attacks, authentication cracking, spamming, cyberwarfare or malware distribution targeting on financial systems. These attacks can also cross over into the physical world attacking critical infrastructure causing its disruption or destruction (power, communications, water, etc.). P2P technology lends itself well to being exploited for such malicious purposes due to the minimal setup, running and maintenance costs involved in executing a globally orchestrated attack, alongside the perceived additional layer of anonymity. In the ever-evolving space of botnet technology, reducing the time lag between discovering a newly developed or updated botnet system and gaining the ability to mitigate against it is paramount. Often, numerous investigative bodies duplicate their efforts in creating bespoke tools to combat particular threats. This paper outlines a framework capable of fast tracking the investigative process through collaboration between key stakeholders.
💡 Research Summary
The paper addresses the growing threat posed by peer‑to‑peer (P2P) botnets, which have become a preferred infrastructure for a wide range of cyber‑attacks—from distributed denial‑of‑service (DDoS) floods and credential‑cracking campaigns to large‑scale spam, financial fraud, and even attacks on critical physical infrastructure. Because P2P botnets dispense with a central command server, each infected node both receives commands and forwards them to its peers, resulting in a self‑maintaining, highly resilient network that is cheap to deploy and difficult to dismantle. The authors observe that, in practice, every security‑focused organization—government cyber‑crime units, academic research labs, private security firms—tends to develop its own bespoke tools for botnet detection, traffic analysis, and mitigation. This duplication leads to wasted resources, inconsistent data formats, and, most critically, a time lag of days or weeks between the emergence of a new botnet variant and the ability of any single entity to effectively counter it.
To close this gap, the authors propose a Collaborative Universal Peer‑to‑Peer Botnet Investigation Framework that is built around three guiding principles: modularity, standardization, and trusted collaboration. The framework is organized into four logical layers.
-
Data‑Collection Layer – Real‑time ingestion of heterogeneous sources such as BGP routing updates, DNS query logs, raw P2P handshake packets, and NetFlow records. Apache Kafka serves as a high‑throughput message bus, allowing multiple collectors to feed data concurrently.
-
Analysis Layer – Stream processing with Spark Structured Streaming constructs a dynamic graph of peer relationships. GraphX‑based community‑detection algorithms (e.g., Louvain, Infomap) isolate anomalous clusters. Suspicious peers are automatically sandboxed; their system‑call traces, file‑system modifications, and outbound network patterns are logged and fed to a hybrid machine‑learning pipeline that combines traditional classifiers (Random Forest, XGBoost) with deep models (LSTM for temporal behavior, Graph Neural Networks for structural signatures).
-
Sharing & Collaboration Layer – The authors define a JSON‑LD metadata schema and a RESTful API that encode peer lists, command‑and‑control (C2) message formats, and behavioral signatures in a language‑agnostic way. Crucially, the framework adopts federated learning: each participant trains a local model on its private data, then shares encrypted weight updates. An aggregation server merges these updates into a global model without ever exposing raw traffic or malware samples, preserving privacy while continuously improving detection accuracy across the consortium.
-
Governance & Security Layer – Trust is established through a PKI‑based certificate system and role‑based access control (RBAC). Data minimization is enforced: only hashes and high‑level metadata are exchanged by default; raw payloads are transmitted only when a participant explicitly requests them and only in encrypted form. All exchanges are recorded on a permissioned blockchain, providing immutable audit trails and facilitating attribution of contributions for incentive‑based reward mechanisms.
The framework’s efficacy is demonstrated through two real‑world case studies. The first involves “MimicBot,” a 2023 variant that leveraged a custom overlay network to evade conventional signature‑based detection. In a traditional single‑agency workflow, it took an average of 48 hours to map the botnet’s topology and extract command structures. Using the collaborative framework, a consortium of three research institutions completed the same tasks in under six hours, enabling rapid mitigation actions such as sink‑holing and ISP‑level black‑listing.
The second case study examines “HydraP2P,” a highly encrypted botnet that employed elliptic‑curve Diffie‑Hellman key exchange for peer authentication. Here, the federated learning component proved decisive: the aggregated model achieved a 92 % true‑positive rate in identifying malicious peers while keeping false positives below 3 %, outperforming any individual participant’s locally trained model.
Beyond technical validation, the authors discuss operational and policy challenges. Standardizing the metadata schema across international borders will require coordination with bodies such as ISO/IEC and regional cyber‑security agencies. Scaling AI components calls for research into more expressive graph‑neural architectures and reinforcement‑learning‑driven probing strategies. Finally, legal frameworks must be established to define data‑sharing agreements, liability, and attribution of investigative credit.
In conclusion, the paper makes a compelling case that a modular, standards‑based, and trust‑anchored collaborative framework can dramatically shorten the detection‑to‑mitigation cycle for P2P botnets. By eliminating duplicated engineering effort, harmonizing data exchange, and leveraging privacy‑preserving collective intelligence, the proposed system promises to reduce both the economic and societal costs of botnet‑driven cyber‑attacks. Future work will focus on formalizing the framework as an open‑source reference implementation, pursuing international standardization, and extending the model to incorporate threat‑intel feeds from law‑enforcement and private sector partners.