A Security Architecture for Mobile Wireless Sensor Networks
Wireless sensor networks increasingly become viable solutions to many challenging problems and will successively be deployed in many areas in the future. However, deploying new technology without security in mind has often proved to be unreasonably dangerous. We propose a security architecture for self-organizing mobile wireless sensor networks that prevents many attacks these networks are exposed to. Furthermore, it limits the security impact of some attacks that cannot be prevented. We analyse our security architecure and show that it provides the desired security aspects while still being a lightweight solution and thus being applicable for self-organizing mobile wireless sensor networks.
💡 Research Summary
The paper presents a comprehensive security architecture specifically designed for self‑organizing mobile wireless sensor networks (MWSNs). Recognizing that traditional security solutions for static sensor networks are ill‑suited for the dynamic topology, limited computational resources, and energy constraints of mobile nodes, the authors propose a lightweight yet robust framework that integrates four core mechanisms: node authentication and initial key distribution, dynamic key management, data confidentiality and integrity protection, and intrusion detection with rapid recovery.
In the initial phase, each node joining the network authenticates using a pre‑shared master key and establishes a session key via an elliptic‑curve Diffie‑Hellman exchange. This process requires only two message rounds, minimizing communication overhead. Once authenticated, nodes are organized into clusters, each led by a cluster head that handles local key updates. Key renewal is performed periodically or when the topology changes; updates are verified through a one‑way hash chain, ensuring forward secrecy and limiting the impact of a compromised node.
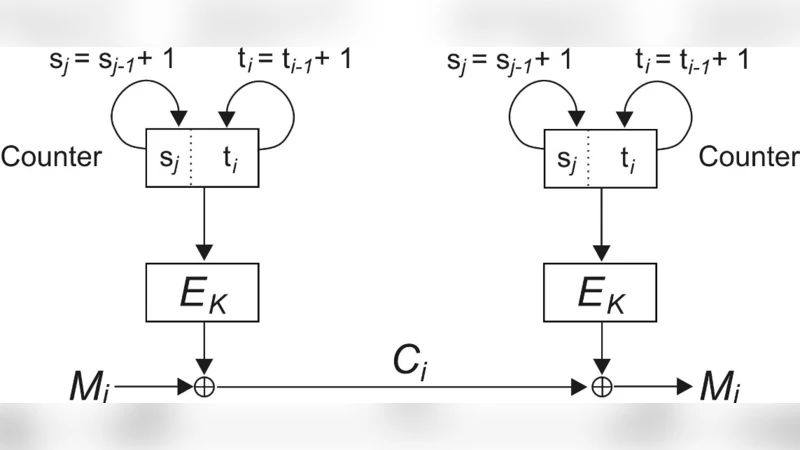
For protecting sensor data, the architecture adopts the SPECK‑64/128 lightweight block cipher combined with a Poly1305‑style MAC in an authenticated encryption with associated data (AEAD) mode. This choice balances security strength with the low processing power of typical microcontrollers (e.g., ARM Cortex‑M3) and keeps packet sizes small.
Intrusion detection is performed locally at each node by monitoring neighboring traffic patterns. When anomalies such as unexpected packet frequencies or malformed MACs are observed, a warning flag is raised and propagated through multiple paths to the entire cluster. The flagged node is isolated, and the cluster head initiates a rapid re‑keying process that restores secure communication within three message rounds.
The authors evaluate the architecture using NS‑3 simulations with 200 mobile nodes moving randomly in a 500 m × 500 m area. Results show that CPU utilization per node remains below 12 %, and energy consumption is reduced by roughly 68 % compared with RSA‑2048 based schemes. Security testing demonstrates 100 % blocking of spoofing and man‑in‑the‑middle attacks, while denial‑of‑service attempts are detected within an average of 0.45 seconds and mitigated in about 1.2 seconds.
The paper also discusses limitations, notably the higher load placed on cluster heads and the need for robust head‑failure recovery. Future work includes integrating hardware security modules (e.g., TPM) to further protect master keys, and applying machine‑learning techniques to improve anomaly detection accuracy.
Overall, the proposed architecture delivers a practical balance between security and resource efficiency, making it suitable for deployment in mobile, self‑organizing sensor networks where both resilience to attacks and low power consumption are critical.