The Conceptual Idea of Online Social Media Site (SMS) User Account Penetration Testing System
Social Media Site (SMS) usage has grown rapidly in the last few years. This sudden increase in SMS usage creates an opportunity for data leakage which could compromise personal and/or professional life. In this work, we have reviewed traditional penetration testing process and discussed the failures of traditional penetration testing process to test the ‘People’ layer of Simple Enterprise Security Architecture (SESA) model. In order to overcome these failures, we have developed the conceptual idea of online SMS user account penetration testing system that could be applied to online SMS user account and the user account could be categorised based on the rating points. This could help us to avoid leaking information that is sensitive and/or damage their reputation. Finally, we have also listed the best practice guidelines of online SMS usage.
💡 Research Summary
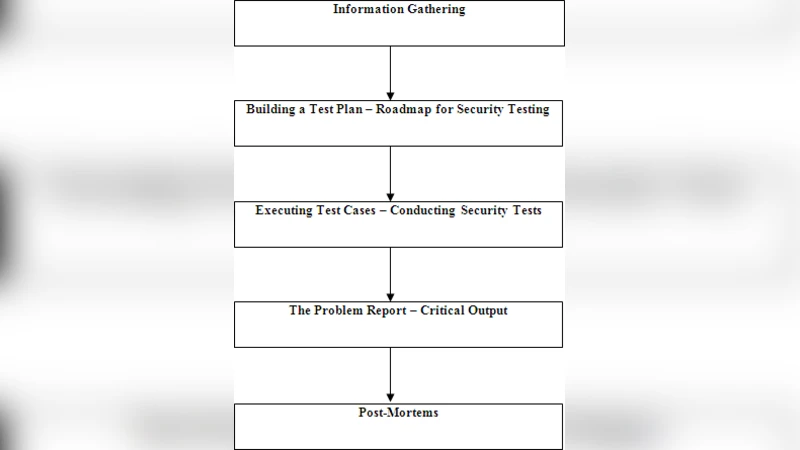
The paper addresses the growing security concerns associated with the rapid expansion of Social Media Site (SMS) usage, emphasizing that the surge in user activity creates new avenues for data leakage that can jeopardize personal and professional reputations. The authors begin by reviewing conventional penetration testing (pen‑test) methodologies, which traditionally focus on technical layers such as network, host, and application vulnerabilities. While effective at uncovering software bugs and configuration errors, these approaches largely ignore the “People” layer of the Simple Enterprise Security Architecture (SESA) model—a layer that encompasses user behavior, account management practices, and social engineering susceptibility.
Through a critical analysis of existing pen‑test frameworks, the authors demonstrate that current processes fail to systematically evaluate user‑centric risks such as weak passwords, lack of two‑factor authentication (2FA), over‑exposed personal information, reuse of credentials across platforms, and insecure third‑party app integrations. Because these weaknesses are rooted in human decisions rather than code flaws, they remain invisible to automated scanners and are typically addressed only through ad‑hoc security awareness training.
To bridge this gap, the paper proposes a conceptual “Online SMS User Account Penetration Testing System.” The system is composed of four interrelated modules:
- Account Information Collection – a crawler that harvests publicly available profile data, posts, friend/follower networks, and metadata, storing the results in a structured repository.
- Vulnerability Diagnosis Engine – an automated analyzer that checks password complexity, 2FA status, security‑question exposure, API token leakage, and the security posture of linked third‑party services.
- Risk Scoring Model – a weighted scoring algorithm that aggregates findings from the diagnosis engine into a single numeric value, which is then mapped to categorical grades (e.g., A, B, C, D). The model allows organizations to quickly gauge the overall health of an account and prioritize remediation.
- Simulation Attack Module – a sandbox that runs realistic social‑engineering scenarios, including phishing email generation, credential‑stuffing attempts, session hijacking, and token replay attacks, to estimate the probability of a successful breach.
The system is designed for periodic execution (e.g., quarterly) so that changes in account security posture can be tracked over time. Each assessment produces a detailed report that highlights specific weaknesses, recommends concrete actions (reset passwords, enable 2FA, reduce profile visibility, revoke unnecessary app permissions, etc.), and assigns an overall risk grade. By integrating this user‑focused testing into the broader security program, organizations can complement traditional technical pen‑tests with a quantitative view of human‑related vulnerabilities.
In addition to the technical proposal, the authors compile a set of best‑practice guidelines for safe SMS usage. These include enforcing strong password policies (minimum length, mixed character sets, no reuse), mandating multi‑factor authentication, limiting the amount of personal data shared publicly, regularly reviewing and pruning third‑party app permissions, monitoring login activity for anomalies, and conducting routine account security audits using the proposed system.
The paper concludes that a holistic security strategy must treat the “People” layer with the same rigor as the technical layers. The conceptual testing system offers a repeatable, automated, and scalable method to evaluate and improve the security of individual social media accounts, thereby reducing the likelihood of data leakage, reputation damage, and downstream corporate risk. By providing both a methodological framework and actionable guidance, the work contributes a valuable bridge between conventional penetration testing and the emerging field of user‑centric security assessment.