Evaluation of Enhanced Security Solutions in 802.11-Based Networks
Traditionally, 802.11-based networks that relied on wired equivalent protocol (WEP) were especially vulnerable to packet sniffing. Today, wireless networks are more prolific, and the monitoring devices used to find them are mobile and easy to access. Securing wireless networks can be difficult because these networks consist of radio transmitters and receivers, and anybody can listen, capture data and attempt to compromise it. In recent years, a range of technologies and mechanisms have helped make networking more secure. This paper holistically evaluated various enhanced protocols proposed to solve WEP related authentication, confidentiality and integrity problems. It discovered that strength of each solution depends on how well the encryption, authentication and integrity techniques work. The work suggested using a Defence-in-Depth Strategy and integration of biometric solution in 802.11i. Comprehensive in-depth comparative analysis of each of the security mechanisms is driven by review of related work in WLAN security solutions.
💡 Research Summary
The paper opens by recalling the well‑known weaknesses of the original Wired Equivalent Privacy (WEP) protocol, which relied on a static secret key, a short 24‑bit initialization vector, and the RC4 stream cipher. Because IVs frequently repeated, attackers could recover the keystream with relatively modest traffic captures, making packet sniffing and injection trivial. The authors then trace the evolutionary path of Wi‑Fi security: WPA introduced TKIP and a Message Integrity Code (MIC) to provide per‑packet key mixing and basic integrity, yet TKIP itself was later shown to be vulnerable to cryptanalysis. WPA2, formalized as the 802.11i amendment, replaced TKIP with AES‑CCMP, adopted the robust CCM mode for simultaneous encryption and authentication, and integrated the 802.1X/EAP framework for strong, certificate‑based authentication. This combination dramatically raised the bar for confidentiality, authentication, and integrity. WPA3 further advances the state of the art by employing Simultaneous Authentication of Equals (SAE) to thwart offline dictionary attacks on pre‑shared keys, and by mandating a 192‑bit security suite for enterprise deployments.
Methodologically, the authors define four evaluation dimensions—encryption strength, authentication robustness, integrity verification, and implementation cost/performance overhead—and apply them uniformly across the protocols. Their comparative matrix shows that, in terms of raw cryptographic security, WPA3 > WPA2 > WPA > WEP, while authentication strength follows the order of EAP‑based methods > pure PSK, and integrity is strongest with CCMP > TKIP > MIC. Performance measurements indicate that modern hardware acceleration for AES makes the overhead of CCMP negligible for most client devices, whereas TKIP incurs a modest CPU penalty.
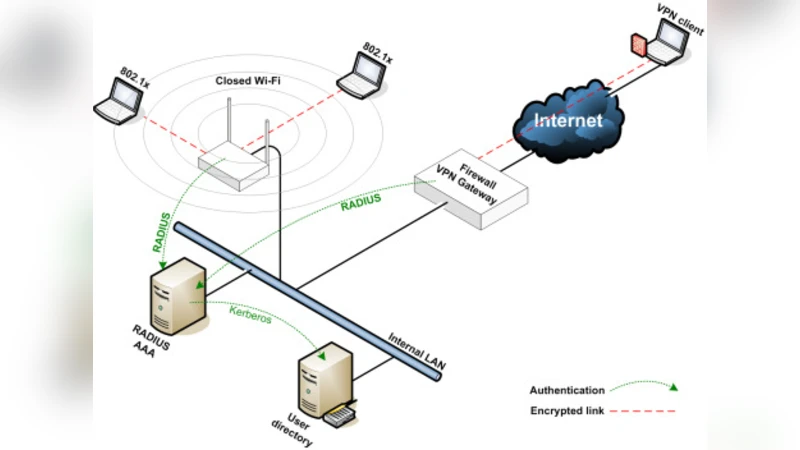
Beyond protocol analysis, the paper advocates a Defense‑in‑Depth (DiD) posture for wireless networks. Physical security of access points, VLAN‑based segmentation, intrusion detection/prevention systems (IDS/IPS), regular firmware patching, and continuous monitoring are recommended as complementary layers that mitigate the impact of any single protocol failure. The authors argue that a multi‑layered approach reduces the attack surface and provides resilience against emerging threats such as rogue APs, evil twin attacks, and side‑channel exploits.
A novel contribution of the work is the proposal to embed biometric authentication into the 802.11i framework, effectively creating a two‑factor scheme that pairs a traditional credential (PSK or certificate) with a user’s physiological trait (fingerprint, iris, or facial recognition). The paper outlines practical considerations: secure storage of biometric templates in TPMs or Secure Enclaves, encrypted transmission via TLS‑EAP tunnels, and compliance with privacy regulations through template minimization and de‑identification. While acknowledging increased hardware costs and potential user‑acceptance hurdles, the authors contend that biometric augmentation dramatically raises the difficulty of credential theft and replay attacks.
In conclusion, the authors assert that WPA2/CCMP (802.11i) remains the most widely deployed and balanced solution today, but future deployments should progressively adopt WPA3 and biometric two‑factor authentication while embedding DiD controls at the organizational level. They identify open research avenues such as quantum‑resistant cipher suites for Wi‑Fi, AI‑driven anomaly detection on the radio spectrum, and lightweight biometric protocols suitable for IoT devices.