Cyber-Physical Systems -- eine Herausforderung an die Automatisierungstechnik?
We discuss challenges to control systems engineering arising from the advent of cyber-physical systems (CPS). After discussing the terminology, general, IT-related issues are treated which need cooperation with computer science, in particular software engineering. Then we study those challenges that require specific core competencies from control systems engineering. We sketch solution approaches for the exemplary problem of dealing with changes in the physical environment of a CPS. —- Der Beitrag befasst sich mit den methodischen Herausforderungen, die durch die Verbreitung der Cyber-Physical Systems (CPS) in der Automatisierungstechnik entstehen, und stellt L"osungsans"atze vor. Nach einer Behandlung des Begriffs CPS werden zun"achst die allgemeinen, IT-bezogenen Fragestellungen angesprochen, die gemeinsam mit der Informatik gel"ost werden m"ussen. Danach gehen wir auf die Herausforderungen ein, deren Behandlung spezifisch automatisierungstechnische Kernkompetenzen erfordern und skizzieren f"ur eine beispielhafte Problemstellung, den Umgang mit "Anderungen in der physikalischen Umgebung, wie entsprechende L"osungen aussehen k"onnen.
💡 Research Summary
The paper addresses the methodological challenges that the proliferation of Cyber‑Physical Systems (CPS) introduces to automation engineering and proposes concrete solution approaches. After a concise definition of CPS, the authors first examine the broad, IT‑related issues that demand close cooperation with computer science, especially software engineering. They argue that traditional control‑engineering practices, which focus primarily on hardware and static system models, are insufficient for the dynamic, networked nature of CPS. Consequently, they advocate for the integration of modern software development practices—model‑based design, automatic code generation, formal verification, continuous integration/continuous deployment, and container‑based deployment—into the control‑system development lifecycle.
The second part of the paper shifts focus to challenges that specifically require core competencies of control‑systems engineering. The authors use the problem of dealing with changes in the physical environment of a CPS as a representative example. In a CPS, sensor and actuator configurations may shift, components wear out, and external conditions such as temperature, humidity, or vibration can vary, causing system parameters to drift in real time. Ignoring these variations can degrade control performance and jeopardize safety. To address this, the paper outlines three complementary strategies.
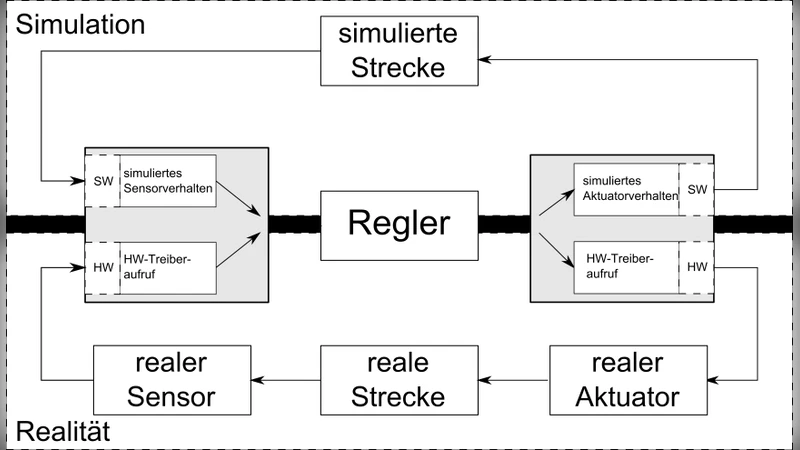
First, a digital‑twin approach is proposed, wherein a high‑fidelity virtual replica of the physical plant runs in parallel and is continuously updated with streaming sensor data. This twin provides an up‑to‑date model that can be used for prediction, diagnostics, and what‑if analysis.
Second, online parameter estimation and adaptive control techniques are recommended. By embedding recursive identification algorithms within the controller, the system can adjust its gains or even restructure its control law on the fly, maintaining stability and performance despite parameter drift.
Third, the authors sketch an automated workflow that links change detection, model reconstruction, and control‑policy recomputation. Edge‑computing resources host lightweight analytics that trigger model updates when significant deviations are detected. Container orchestration platforms (e.g., Kubernetes) manage the deployment of updated control modules, ensuring minimal downtime. This pipeline leverages event‑driven architectures, real‑time verification, and safety monitors to guarantee that any new control configuration complies with predefined safety constraints before it is activated.
Beyond these technical measures, the paper emphasizes the need for a multi‑layered security and safety architecture. Because CPS intertwine physical processes with cyber components, a risk‑based design approach is essential. The authors suggest modeling the interdependencies between physical and cyber layers, applying defense‑in‑depth principles, and integrating intrusion detection, authentication, and fault‑tolerant mechanisms throughout the system stack.
In the concluding section, the authors argue that future automation engineers must develop a hybrid skill set that combines deep knowledge of system dynamics and control theory with proficiency in software architecture, data‑flow management, cybersecurity, and cloud/edge infrastructure. They call for curriculum reforms, interdisciplinary research initiatives, and stronger industry‑academia collaborations to cultivate these competencies. By adopting the proposed integration of software‑engineering practices, digital‑twin technologies, adaptive control, and robust security frameworks, automation engineering can meet the challenges posed by CPS and continue to drive sustainable innovation in the era of interconnected, intelligent systems.