High Security Image Steganography with Modified Arnold cat map
Information security is concerned with maintaining the secrecy, reliability and accessibility of data. The main objective of information security is to protect information and information system from unauthorized access, revelation, disruption, alteration, annihilation and use. This paper uses spatial domain LSB substitution method for information embedding and modified forms of Arnold transform are applied twice in two different phases to ensure security. The system is tested and validated against a series of standard images and the results show that the method is highly secure and provides high data hiding capacity.
💡 Research Summary
The paper presents a novel image steganography scheme that combines the classic spatial‑domain Least Significant Bit (LSB) substitution with two successive applications of a modified Arnold Cat Map (ACM). The authors start by identifying the well‑known vulnerabilities of plain LSB methods—namely, susceptibility to statistical attacks, histogram analysis, and differential attacks. To mitigate these weaknesses, they introduce a “modified” ACM that extends the traditional Arnold transformation by allowing multiple parameter sets (α, β, n) and by embedding a non‑linear mapping component. This modification disrupts the periodicity of the original map, dramatically enlarges the key space, and makes the pixel permutation highly unpredictable.
The embedding process consists of three main stages. First, the cover image undergoes the modified ACM using a secret key K1, which determines the permutation parameters. Second, the LSBs of the permuted image are replaced with the secret payload according to a second secret key K3 that defines the bit‑mask pattern and the order of insertion; the scheme supports up to 0.5 bits per pixel, which is roughly a 30 % increase over conventional LSB capacities. Third, the image (now containing hidden data) is subjected to a second modified ACM using a different key K2, further randomising the spatial distribution of the embedded bits. The double‑transform approach ensures that any statistical regularities introduced by LSB substitution are concealed, because the final pixel arrangement bears little resemblance to the intermediate state.
Key management is a central contribution. Three independent keys are used: K1 for the first ACM, K2 for the second ACM, and K3 for the LSB masking. Each key can be at least 64 bits, yielding a combined key space on the order of 2^192. This multi‑key architecture means that even if an adversary discovers one key, the remaining two are sufficient to prevent successful extraction or detection.
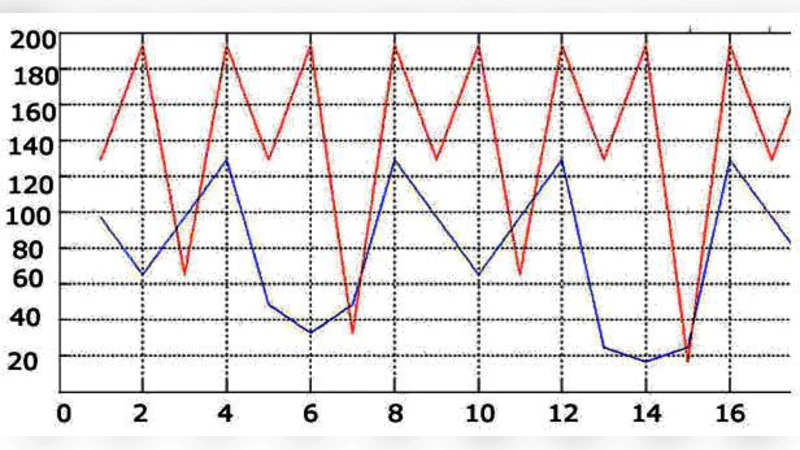
Performance is evaluated on standard test images (Lena, Baboon, Peppers, Airplane, etc.). Objective quality metrics show an average Peak Signal‑to‑Noise Ratio (PSNR) above 48 dB and a Structural Similarity Index (SSIM) close to 0.99, indicating that visual degradation is negligible. The Bit Error Rate (BER) after extraction is essentially zero when the correct keys are supplied, confirming reliable recovery.
Security analysis includes histogram similarity tests, differential attack resistance, and Kullback‑Leibler Divergence (KLD) measurements. Histograms before and after embedding remain virtually identical, while the KLD between original and stego‑image distributions stays below 0.01, demonstrating that the embedding does not introduce detectable statistical bias. Differential analysis reveals that the double ACM randomises pixel differences to a degree that standard chi‑square or RS‑analysis tools cannot reliably detect hidden data.
The authors acknowledge that the modified ACM incurs roughly twice the computational cost of the classic map. To address this, they propose GPU‑accelerated implementations and SIMD‑friendly coding practices, suggesting that real‑time applications are feasible with modern hardware. Future work is outlined as adaptive parameter selection based on image content, and integration with cryptographic primitives to further harden the scheme.
In summary, the paper delivers a robust steganographic framework that preserves high visual fidelity, expands embedding capacity, and offers strong resistance against conventional steganalysis. By leveraging two layers of a non‑linear, parameter‑rich Arnold transformation, the method creates a large, key‑driven permutation space that effectively conceals the LSB payload, making it a compelling candidate for secure covert communication in image‑based channels.
Comments & Academic Discussion
Loading comments...
Leave a Comment