Wireless Sensor Networks Attacks and Solutions
A few years ago, wireless sensor networks (WSNs) used by only military. Now, we have seen many of organizations use WSNs for some purposes such as weather, pollution, traffic control, and healthcare. Security is becoming on these days a major concern for wireless sensor network. In this paper I focus on the security types of attacks and their detection. This paper anatomizes the security requirements and security attacks in wireless sensor networks. Also, indicate to the benchmarks for the security in WSNs.
💡 Research Summary
The paper provides a comprehensive overview of security challenges and countermeasures in wireless sensor networks (WSNs), tracing their evolution from exclusively military applications to widespread civilian use in domains such as environmental monitoring, traffic management, and healthcare. Because sensor nodes operate on limited battery power, possess modest computational resources, and communicate over open wireless channels, they are intrinsically vulnerable to a broad spectrum of attacks. The authors first delineate the fundamental security objectives—confidentiality, integrity, and availability—and then expand the discussion to include WSN‑specific requirements: authentication, data freshness, energy efficiency, scalability, and resilience to node capture.
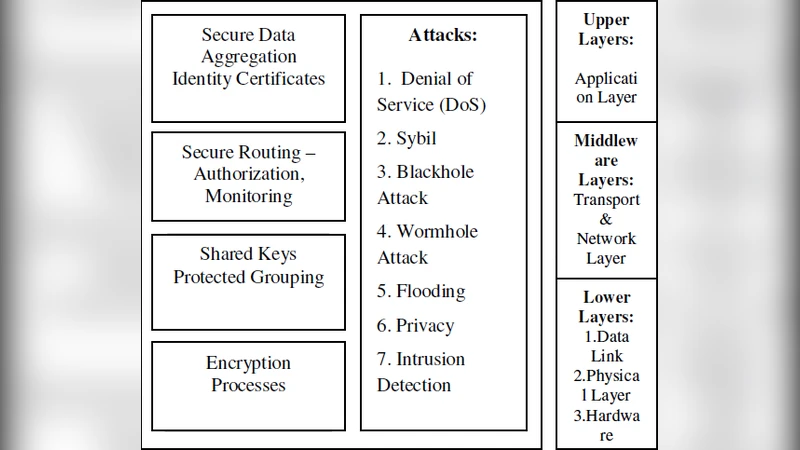
A detailed taxonomy of attacks is presented, organized by protocol layer. At the physical layer, jamming and eavesdropping are highlighted as primary threats that can disrupt or intercept radio transmissions. The data‑link layer suffers from MAC‑address spoofing and frame collisions. The network layer hosts the most diverse and damaging attacks, including selective forwarding, sinkhole, wormhole, Sybil, and hello‑flood attacks. These attacks manipulate routing information, concentrate traffic through malicious nodes, or create false identities, leading to packet loss, increased latency, and accelerated energy depletion. Application‑layer threats such as data tampering and denial‑of‑service are also examined. For each attack type, the paper quantifies its impact on packet delivery ratio, node lifetime, and overall network topology.
In response to these threats, the authors evaluate a suite of detection and mitigation techniques. Lightweight cryptography, particularly elliptic‑curve cryptography (ECC), is advocated for key exchange because it offers strong security with minimal computational overhead. The paper proposes a hybrid key‑management scheme that combines pre‑distributed key pools with dynamic re‑keying to limit the damage caused by node capture. Multi‑path routing is recommended to avoid single points of failure, while trust‑based routing algorithms assign reputation scores to neighboring nodes and exclude low‑trust participants from forwarding decisions. Anomaly‑based intrusion detection systems (IDS) employing statistical models or machine‑learning classifiers are discussed for real‑time detection of abnormal traffic patterns, such as sudden spikes in packet loss indicative of jamming. Simulation results demonstrate that ECC reduces energy consumption by over 70 % compared with RSA, and trust‑aware routing maintains a packet delivery rate above 85 % even under selective‑forwarding attacks.
To enable objective assessment of security solutions, the paper defines a set of benchmark metrics: packet loss rate under attack, key‑renewal frequency and associated energy cost, detection accuracy (precision and recall), overall energy overhead introduced by security mechanisms, and the extension of network lifetime achieved through protective measures. These metrics are intended to be applicable both in controlled laboratory experiments and in real‑world deployments, facilitating transparent comparison of competing approaches.
The conclusion emphasizes that the principal challenge for WSN security lies in balancing robust protection with the stringent energy constraints of sensor nodes. Future research directions suggested include energy‑harvesting‑enabled self‑repairing security modules, lightweight blockchain frameworks for decentralized trust management, deep‑learning‑based IDS optimized for low‑power hardware, and the development of standardized security architectures that can be readily integrated into emerging IoT ecosystems. By addressing these open issues, the authors argue that WSNs can evolve into reliable, secure backbones for smart cities, Industry 4.0, and remote health‑care applications.