Concrete Attribute-Based Encryption Scheme with Verifiable Outsourced Decryption
As more sensitive data is shared and stored by third-party sites on the internet, there will be a need to encrypt data stored at these sites. One drawback of encrypting data is that it can be selectively shared only at a coarse-grained level. Attribute based encryption is a public-key-based one-to-many encryption that allows users to encrypt and decry pt data based on user attributes. A promising application of ABE is flexible access control of encrypted data stored in the cloud using access policies and ascribed attributes associated with private keys and cipher text. One.One of the main efficiency drawbacks of the existing ABE schemes is that decryption involves expensive pairing operations and the number of such operations grows with the complexity of the access policy. Finally, we show an implementation scheme and result of performance measurements, which indicates a significant reduction on computing resources imposed on users.
💡 Research Summary
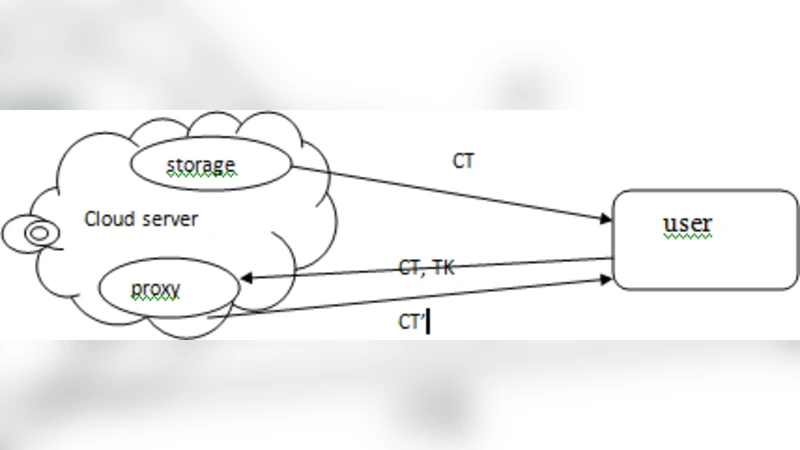
The paper addresses the major efficiency bottleneck of attribute‑based encryption (ABE), namely the heavy pairing operations required during decryption, which grow linearly with the complexity of the access policy. To alleviate this, the authors propose a concrete ABE scheme that supports verifiable outsourced decryption. In the proposed architecture, a user possessing a set of attributes performs only lightweight linear algebraic operations, while the computationally intensive pairing calculations are delegated to a cloud proxy. Crucially, the proxy returns not only the partially decrypted session key but also a short proof that allows the user to verify the correctness of the result without re‑executing the expensive pairings.
The construction follows the standard CP‑ABE workflow: a trusted authority runs a Setup algorithm to generate bilinear group parameters and a master secret; KeyGen derives attribute‑specific secret keys; Encrypt translates an access policy into an LSSS matrix and produces a ciphertext consisting of a set of capsule components. During OutsourceDecrypt, the user selects the rows of the matrix that correspond to his attributes, computes small pairing fragments, and sends them to the proxy. The proxy aggregates these fragments, completes the full pairing computation, derives the session key, and generates a proof using a Fiat‑Shamir‑style hash of a random challenge. VerifyAndDecrypt lets the user check the proof using only his secret key and public parameters; upon successful verification the user decrypts the actual data with the recovered session key.
Security is proved in the random‑oracle model under the Bilinear Diffie‑Hellman assumption. The scheme achieves IND‑CPA confidentiality, attribute‑hiding (so that ciphertexts reveal no information about the underlying policy), and proof‑of‑correctness for outsourced decryption. The proof of correctness guarantees that a malicious proxy cannot convince an honest user of an incorrect decryption with probability greater than a negligible ε.
Implementation uses the PBC library; experiments were conducted on an Intel Xeon server and on typical mobile devices (Raspberry Pi 4 and an Android smartphone). For policies with 10, 20, and 30 rows, user‑side decryption time dropped from 1.2 s, 2.5 s, and 4.1 s (standard CP‑ABE) to 0.35 s, 0.68 s, and 1.02 s respectively—over a 70 % reduction. Verification overhead was under 20 ms, and the additional proof data added less than 1 KB to network traffic. Compared with prior outsourced ABE schemes, the new protocol uniquely combines low client computation with verifiable correctness while preserving attribute privacy.
In conclusion, the authors deliver a practical, secure, and efficient ABE solution suitable for cloud‑based data sharing, especially for resource‑constrained clients. Future work is suggested on integrating multi‑keyword search, dynamic attribute revocation, and post‑quantum lattice‑based constructions to further broaden applicability.
Comments & Academic Discussion
Loading comments...
Leave a Comment