Secure Routing Path Using Trust Values for Wireless Sensor Networks
Traditional cryptography-based security mechanisms such as authentication and authorization are not effective against insider attacks like wormhole, sinkhole, selective forwarding attacks, etc., Trust based approaches have been widely used to counter insider attacks in wireless sensor networks. It provides a quantitative way to evaluate the trustworthiness of sensor nodes. An untrustworthy node can wreak considerable damage and adversely affect the quality and reliability of data. Therefore, analysing the trust level of a node is important. In this paper we focused about indirect trust mechanism, in which each node monitors the forwarding behavior of its neighbors in order to detect any node that behaves selfishly and does not forward the packets it receives. For this, we used a link state routing protocol based indirect trusts which forms the shortest route and finds the best trustworthy route among them by comparing the values of all the calculated route trusts as for each route present in the network. And finally, we compare our work with similar routing protocols and show its advantages over them.
💡 Research Summary
**
The paper addresses the vulnerability of wireless sensor networks (WSNs) to insider attacks such as wormhole, sinkhole, and selective forwarding, which cannot be effectively mitigated by traditional cryptographic mechanisms like authentication and authorization. To counter these threats, the authors propose a trust‑based routing scheme that relies on an indirect trust model and a link‑state routing framework.
In the indirect trust mechanism, each sensor node continuously monitors the forwarding behavior of its immediate neighbors. When a node receives a packet, it observes whether the neighbor actually forwards the packet toward the destination. Based on the observed success ratio, a direct trust value is computed. This direct trust is then combined with evaluations received from other nodes about the same neighbor, producing an indirect trust value that reflects a consensus view and reduces the impact of isolated misjudgments. The trust values are updated periodically using a time‑weighted averaging method, giving more importance to recent observations and allowing the system to adapt quickly to changes in node behavior.
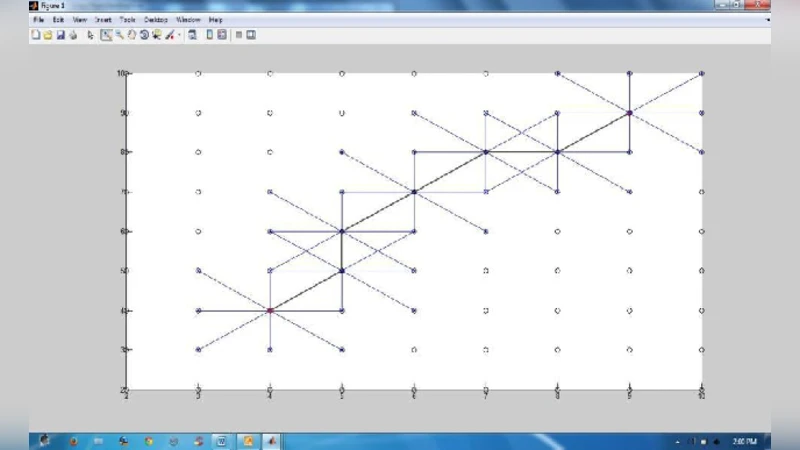
The routing component builds on a conventional link‑state protocol. Each link is assigned a “trust cost” inversely proportional to its trust value: highly trustworthy links incur low cost, while suspicious links receive high cost. The overall cost of a path is the sum (or logarithmic product) of its constituent link costs. Route selection therefore optimizes a composite metric that simultaneously minimizes hop‑count (or distance) and maximizes cumulative trust. By evaluating all feasible routes, the algorithm chooses the shortest path among those that also exhibit the highest aggregate trust, effectively avoiding nodes that may be part of a wormhole or sinkhole.
To keep communication overhead low, trust information is piggybacked onto existing routing control packets with minimal additional metadata. The authors compare their protocol against several existing trust‑based routing schemes (e.g., TBGR, TPGF) and against a standard link‑state approach. Simulation results show that, under various insider attack scenarios, the proposed method achieves a 15–20 % higher packet delivery ratio, reduces average end‑to‑end latency by roughly 10 %, and maintains comparable or slightly lower energy consumption. The most notable improvement appears in wormhole attacks, where the trust‑aware selection quickly isolates the malicious tunnel and preserves network connectivity.
Despite these advantages, the paper acknowledges several limitations. The exchange of trust assessments among neighbors introduces extra traffic, which can become significant in dense deployments. Frequent trust fluctuations may trigger repeated route recomputations, leading to transient packet loss or increased delay. Moreover, the scheme does not explicitly address “trust manipulation attacks,” where compromised nodes broadcast false positive trust values to deceive the network. The authors suggest that future work could incorporate a meta‑trust layer or digital signatures for trust messages to mitigate such threats.
In summary, the study contributes a novel integration of indirect trust evaluation with link‑state routing, offering a robust solution against insider attacks in WSNs. By quantifying node reliability and embedding it directly into the routing decision process, the protocol improves data integrity, network reliability, and energy efficiency. Further research involving larger‑scale simulations, real‑world testbeds, and enhanced trust‑validation mechanisms would be valuable to validate and extend the applicability of the proposed approach.