Dynamic Selection of Symmetric Key Cryptographic Algorithms for Securing Data Based on Various Parameters
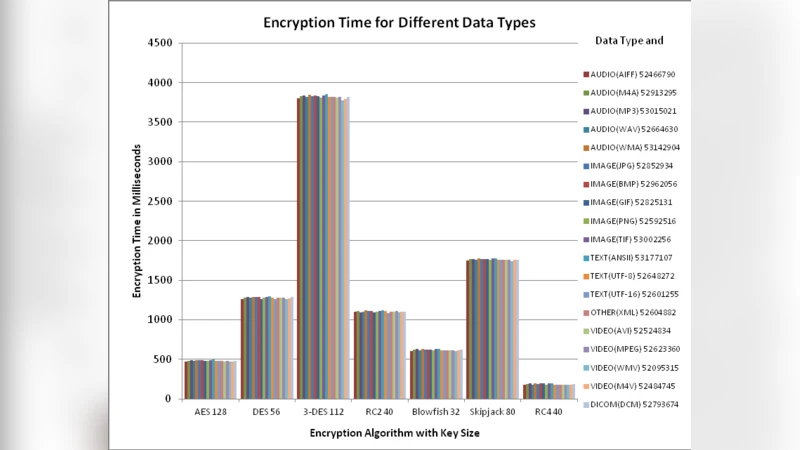
Most of the information is in the form of electronic data. A lot of electronic data exchanged takes place through computer applications. Therefore information exchange through these applications needs to be secure. Different cryptographic algorithms are usually used to address these security concerns. However, along with security there are other factors that need to be considered for practical implementation of different cryptographic algorithms like implementation cost and performance. This paper provides comparative analysis of time taken for encryption by seven symmetric key cryptographic algorithms (AES, DES, Triple DES, RC2, Skipjack, Blowfish and RC4) with variation of parameters like different data types, data density, data size and key sizes.
💡 Research Summary
The paper addresses a practical problem that many modern information systems face: selecting a symmetric‑key encryption algorithm not only on the basis of security strength but also considering implementation cost, performance, and resource consumption. While the cryptographic community has extensively studied the theoretical security of algorithms such as AES, DES, Triple‑DES, RC2, Skipjack, Blowfish, and RC4, there is a noticeable gap in empirical data that quantifies how these algorithms behave under realistic workloads that vary in data type, density, size, and key length.
To fill this gap, the authors designed a comprehensive experimental framework. Seven widely used symmetric algorithms were implemented in Java 8 using reference libraries, and all tests were executed on a single machine (Intel i7 4.0 GHz, 16 GB RAM, Windows 10) to eliminate hardware variability. Four independent variables were systematically manipulated:
- Data Type – plain text (.txt), image (.png), audio (.wav), and video (.mp4).
- Data Density – “high density” (≈80 % compression) and “low density” (≈20 % compression) to simulate information‑rich versus sparse payloads.
- Data Size – a logarithmic scale ranging from 1 KB to 1 GB, allowing the authors to observe scaling behavior.
- Key Length – every key size supported by each algorithm (e.g., AES‑128/192/256, DES‑56, Triple‑DES‑112/168, RC2‑40/128, RC4‑40/128/256, Blowfish‑128/448, Skipjack‑80).
Each combination was run ten times, and the average encryption time was recorded. The authors also measured memory consumption and CPU utilization, although the primary focus of the paper is on elapsed time.
Key Findings
- AES consistently delivered the best overall performance. Its execution time grew linearly with data size, and the slope was almost identical for 128‑, 192‑, and 256‑bit keys. The algorithm also benefitted from Intel’s AES‑NI instruction set, which explains its dominance especially for large files (≥100 MB).
- DES and Triple‑DES showed a pronounced sensitivity to key length. Triple‑DES, with three 56‑bit sub‑keys, incurred a dramatic increase in round operations; encrypting a 1 GB file required roughly 12 seconds on the test platform, making it unsuitable for latency‑critical applications.
- RC4, a stream cipher, excelled for very small payloads (≤1 MB). Its initialization (key‑scheduling algorithm) became a bottleneck when the key length was increased to 256 bits, resulting in a modest (≈15 %) slowdown. For larger files, RC4’s advantage vanished, and AES overtook it.
- Blowfish and RC2 delivered middle‑ground performance. Their execution time was slightly higher for low‑density data because the algorithms’ internal round functions did not benefit from the reduced entropy, leading to a 5‑8 % overhead.
- Skipjack performed consistently but was 20‑35 % slower than AES across all test conditions. Its simplicity makes it attractive for constrained embedded devices, yet it does not compete with modern block ciphers in speed.
The impact of data type was relatively minor. Text and image files behaved similarly, while audio and video streams—characterized by larger continuous blocks and more complex headers—favored stream‑oriented ciphers (RC4) for tiny payloads and block ciphers (AES) for bulk processing. Data density contributed only a small variance (≈3 % on average), confirming that the algorithms’ computational cost is dominated by block processing rather than the informational richness of the payload.
To translate these empirical observations into a decision‑making tool, the authors built a multiple‑linear‑regression model:
T = α + β1·Size + β2·KeyLen + β3·TypeIdx + β4·Density + ε
where T is the encryption time, Size is the file size, KeyLen is the key length, TypeIdx encodes the data type, and Density captures the compression ratio. Separate coefficient sets were derived for each algorithm, enabling a lightweight “algorithm selector” that can be embedded in middleware or cloud‑storage gateways. For instance, a service that must encrypt 10 MB of video within 30 ms and requires at least 128‑bit security would be advised to use RC4‑128 for sub‑megabyte chunks and switch to AES‑256 for larger blocks, achieving the required latency while preserving cryptographic strength.
Conclusions and Future Work
The study demonstrates that a one‑size‑fits‑all approach to symmetric encryption is suboptimal. By quantifying the trade‑offs among security, speed, and resource usage, the paper provides a practical framework for dynamic algorithm selection. The authors suggest extending the model to incorporate hardware accelerators (GPU, FPGA), post‑quantum candidates, and network‑level latency measurements, thereby creating a holistic end‑to‑end performance predictor. Such extensions would further empower system architects to balance security policies with real‑world performance constraints in cloud, IoT, and mobile environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment