Study of Security Issues in Pervasive Environment of Next Generation Internet of Things
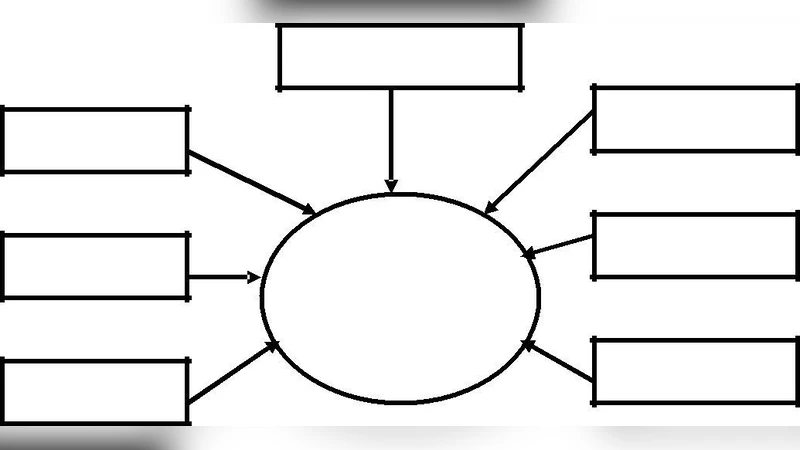
Internet of Things is a novel concept that semantically implies a world-wide network of uniquely addressable interconnected smart objects. It is aimed at establishing any paradigm in computing. This environment is one where the boundary between virtual and physical world is eliminated. As the network gets loaded with hitherto unknown applications, security threats also become rampant. Current security solutions fail as new threats appear to de-struct the reliability of information. The network has to be transformed to IPv6 enabled network to address huge number of smart objects. Thus new addressing schemes come up with new attacks. Real time analysis of information from the heterogeneous smart objects needs use of cloud services. This can fall prey to cloud specific security threats. Therefore need arises for a review of security threats for a new area having huge demand. Here a study of security issues in this domain is briefly presented.
💡 Research Summary
The paper provides a concise yet comprehensive review of security challenges that arise in the emerging environment of the next‑generation Internet of Things (IoT). It begins by defining the IoT as a pervasive ecosystem where the distinction between the virtual and physical worlds disappears, leading to a massive proliferation of uniquely addressable smart objects. Because the number of devices far exceeds the capacity of IPv4, the transition to IPv6 is presented as a prerequisite. While IPv6 offers an astronomically large address space, its new header formats, extension options, and stateless address autoconfiguration (SLAAC) introduce blind spots for traditional firewalls, intrusion detection systems, and routing security mechanisms. Attackers can exploit spoofed router advertisements to perform man‑in‑the‑middle attacks, hijack traffic, or force devices onto malicious subnets.
The authors then examine the intrinsic resource constraints of IoT nodes—limited CPU, memory, and power—which impede the deployment of conventional cryptographic primitives and certificate‑based authentication. They argue for lightweight encryption schemes and hardware‑rooted trust anchors such as TPMs or Secure Elements, yet note that commercial adoption remains sparse. Firmware update mechanisms, especially over‑the‑air (OTA) processes, are highlighted as a critical attack surface; insufficient signature verification or compromised update servers can lead to large‑scale malware propagation across the entire mesh of devices.
A substantial portion of the analysis focuses on the reliance on cloud services for real‑time data aggregation, analytics, and storage. While cloud platforms provide scalability and elasticity, they also bring multi‑tenant isolation issues, virtualization‑based side‑channel attacks, and the risk of privilege escalation within the provider’s infrastructure. Even when transport‑level security (e.g., TLS) is employed, data can be exposed or altered once it resides inside the cloud if proper access controls, encryption‑at‑rest policies, and tenant isolation are not rigorously enforced. The paper points out that many cloud providers’ default security configurations are not tuned for the high‑frequency, low‑latency traffic patterns typical of IoT workloads, leading to misconfigurations that attackers can exploit.
Protocol heterogeneity is identified as another source of vulnerability. IoT ecosystems commonly use lightweight application protocols such as MQTT, CoAP, and LwM2M. These protocols often ship with optional or disabled security features; for instance, MQTT’s default operation over plain TCP without TLS and its topic‑based access control model can be abused by unauthorized subscribers to harvest sensitive telemetry. The authors illustrate how protocol‑level weaknesses can be leveraged in combined attack scenarios, such as distributed denial‑of‑service (DDoS) amplification paired with data tampering, amplifying the impact of a breach.
Finally, the paper critiques the current security posture as being overly reactive. Because many IoT attacks manifest subtly and only become apparent after significant damage, the authors advocate for proactive, behavior‑based anomaly detection and machine‑learning‑driven threat intelligence. They acknowledge practical challenges, including the scarcity of labeled training data, the need for model compression to fit constrained edge devices, and the tension between privacy preservation and extensive telemetry collection.
In conclusion, the authors argue that securing the next‑generation IoT requires an integrated, multi‑layered framework that simultaneously addresses IPv6‑specific threats, lightweight cryptographic and trust mechanisms for constrained nodes, hardened cloud integration, protocol‑level hardening, and advanced, real‑time detection capabilities. They call for coordinated efforts among academia, industry, and regulatory bodies to develop standardized security guidelines, promote widespread adoption of secure design patterns, and foster continuous evolution of defenses as new threats emerge.