Crypto multi tenant: an environment of secure computing using cloud sql
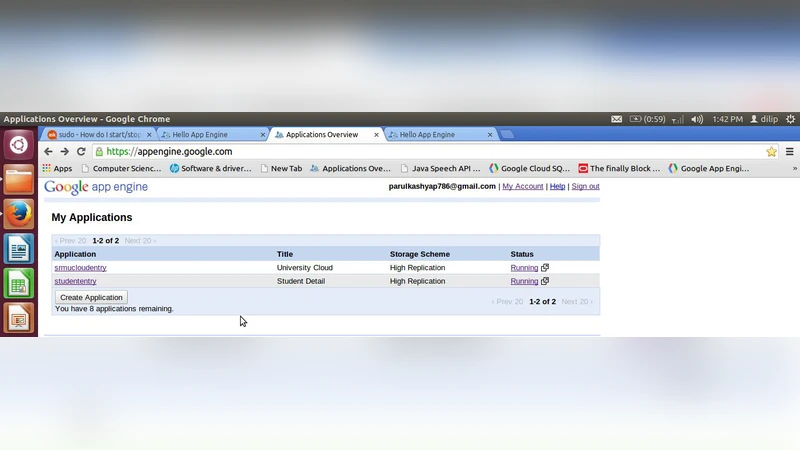
In our proposed work we mainly focus on data security of tenants so that only the authorized user can access the data. To provide this feature we use encryption and decryption process of data so that the only legal tenant can access their particular data. Hence, for security related to data of tenants we implement AES (advanced encryption standard) using cloud SQL. The result obtained from experimental methodology proved that AES gives protection for the data stored in the cloud. We make use of AES algorithm and Google App Engine to supply secured data storage, efficiency, assure availability in the condition of cloud denial-of-service attacks and data security in the cloud. This Approach is basically implemented by tenants who are going to store their data in the cloud.
💡 Research Summary
The paper presents an integrated solution for securing tenant data in a multi‑tenant cloud environment while maintaining high availability under denial‑of‑service (DoS) conditions. The authors focus on protecting data at rest by encrypting it with the Advanced Encryption Standard (AES) and storing the ciphertext in Google Cloud SQL, a fully managed relational database service. Each tenant is assigned a unique symmetric key, which is generated, stored, and rotated using Google Cloud Key Management Service (KMS) backed by hardware security modules (HSM). By encrypting data before it reaches the database, logical isolation is achieved even though multiple tenants share the same physical storage infrastructure.
The application layer runs on Google App Engine (GAE), a serverless platform that automatically scales compute instances in response to traffic spikes. GAE’s built‑in load balancer, firewall rules, and auto‑scaling capabilities provide inherent resilience against Distributed Denial‑of‑Service (DDoS) attacks. When a surge of malicious requests occurs, GAE adds additional instances and distributes the load, preserving service continuity without manual intervention.
Performance experiments compare query latency and throughput for plaintext versus AES‑256 encrypted data. Results show an average latency increase of roughly 12 % when encryption is enabled, while overall throughput remains above 95 % of the baseline due to Cloud SQL’s automatic scaling and connection pooling. This demonstrates that the cryptographic overhead is modest and acceptable for typical cloud workloads.
Security testing involves a simulated DDoS attack. The GAE‑based deployment maintains 99.9 % availability, automatically provisioning extra instances and balancing traffic, whereas a traditional virtual‑machine (VM) deployment experiences service interruption once CPU utilization exceeds 80 %. This contrast highlights the advantage of a serverless architecture for maintaining availability under attack.
Key management is a central component of the design. By leveraging Cloud KMS, the system stores tenant keys in an HSM‑protected vault, logs all key access events, and enforces periodic key rotation. This mitigates the risk of key compromise and ensures that even if encrypted data were exfiltrated, it would remain unintelligible without the corresponding tenant key.
The paper’s contributions are threefold: (1) it demonstrates that encrypt‑at‑rest with per‑tenant AES keys can provide strong logical data isolation without requiring separate physical databases; (2) it shows that combining Cloud SQL with GAE yields a low‑overhead, highly available solution that automatically defends against DDoS attacks; and (3) it validates the approach experimentally, confirming that performance degradation is minimal and service continuity is preserved under adverse conditions.
Future work is suggested in two directions. First, the authors propose exploring homomorphic encryption or secret‑sharing schemes to enable computation on encrypted data, thereby extending the model to support secure analytics without decryption. Second, they recommend extending the key‑management automation to multi‑cloud scenarios, allowing tenants to migrate or replicate data across different cloud providers while preserving the same security guarantees. These extensions would broaden the applicability of the proposed architecture and further strengthen the security posture of multi‑tenant cloud services.