Analyzing Social and Stylometric Features to Identify Spear phishing Emails
Spear phishing is a complex targeted attack in which, an attacker harvests information about the victim prior to the attack. This information is then used to create sophisticated, genuine-looking attack vectors, drawing the victim to compromise confidential information. What makes spear phishing different, and more powerful than normal phishing, is this contextual information about the victim. Online social media services can be one such source for gathering vital information about an individual. In this paper, we characterize and examine a true positive dataset of spear phishing, spam, and normal phishing emails from Symantec’s enterprise email scanning service. We then present a model to detect spear phishing emails sent to employees of 14 international organizations, by using social features extracted from LinkedIn. Our dataset consists of 4,742 targeted attack emails sent to 2,434 victims, and 9,353 non targeted attack emails sent to 5,912 non victims; and publicly available information from their LinkedIn profiles. We applied various machine learning algorithms to this labeled data, and achieved an overall maximum accuracy of 97.76% in identifying spear phishing emails. We used a combination of social features from LinkedIn profiles, and stylometric features extracted from email subjects, bodies, and attachments. However, we achieved a slightly better accuracy of 98.28% without the social features. Our analysis revealed that social features extracted from LinkedIn do not help in identifying spear phishing emails. To the best of our knowledge, this is one of the first attempts to make use of a combination of stylometric features extracted from emails, and social features extracted from an online social network to detect targeted spear phishing emails.
💡 Research Summary
The paper investigates whether publicly available LinkedIn information can improve the detection of spear‑phishing emails, which are targeted attacks that leverage victim‑specific context. Using Symantec’s enterprise email scanning service, the authors assembled a real‑world dataset comprising 4,742 confirmed spear‑phishing messages sent to 2,434 employees of 14 international organizations, 9,353 non‑targeted spam/phishing messages sent to 5,912 employees, and an additional 6,601 benign messages from the Enron corpus. For each recipient, the authors extracted the most frequently occurring “to” domain, derived first and last names from the email address, and crawled the corresponding public LinkedIn profile.
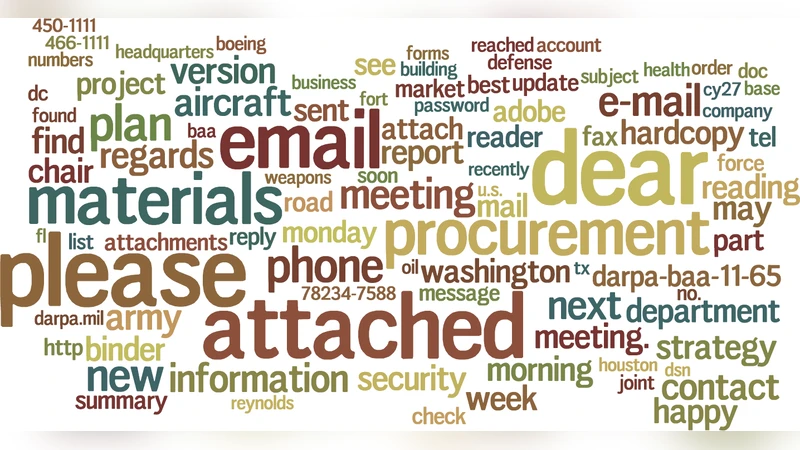
Feature engineering was performed along two dimensions. First, a set of 54 stylometric features was derived from the email itself, including subject length, body word count, special‑character ratios, attachment types and sizes, HTML structural complexity, and header anomalies. Second, 12 social features were harvested from LinkedIn profiles, such as current job title, years of experience, education level, listed skills, number of connections, and profile visibility settings. The combined feature vector was fed into four classification algorithms—Logistic Regression, Support Vector Machine, Random Forest, and Gradient Boosting—using a 10‑fold cross‑validation scheme.
Results show that the best overall accuracy (97.76 %) and F1‑score (0.94) were achieved when both stylometric and social features were used. However, when the social features were omitted, the stylometric‑only model achieved a higher accuracy of 98.28 % and an F1‑score of 0.96. Feature importance analysis revealed that email‑based attributes (e.g., subject‑body word patterns, attachment extensions, header irregularities) dominate the decision process, while LinkedIn‑derived attributes contribute minimally. This indicates that, despite attackers’ reliance on victim information to craft convincing messages, the textual and structural cues present in the email itself are more reliable for automated detection.
The authors discuss several limitations. The study focuses exclusively on LinkedIn; other platforms such as Facebook or Twitter, which may contain richer or more personal data, were not examined. Users without public LinkedIn profiles were excluded, potentially introducing sampling bias. Moreover, the dataset reflects a snapshot in time; attackers may evolve their language and attachment strategies, necessitating periodic model retraining. Future work is suggested to explore multimodal social data, incorporate deep language models (e.g., BERT) for richer textual analysis, and develop real‑time detection pipelines.
In conclusion, the research provides empirical evidence that stylometric analysis of email content is highly effective for spear‑phishing detection, while publicly available LinkedIn information does not add measurable value. This insight guides security practitioners to prioritize sophisticated content‑based feature extraction over extensive social‑profile harvesting when designing anti‑phishing solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment