A New Result on the Random Residue Sequence Algorithm
Random residue sequences (RR) may be used in many random number applications including those related to multiple access in communications. This paper investigates variations on an algorithm to generate RR sequences that was proposed earlier by the author. This makes it possible to obtain many more random sequences than was possible to do by the previous algorithm. Experimental results are presented on a variety of sequences of length 16 and 24. To obtain a variety of RR sequences of a specific length can have obvious applications in cryptography.
💡 Research Summary
The paper addresses the generation of Random Residue (RR) sequences, a class of number sequences that have found applications in random number generation, multiple‑access communications, and cryptographic key streams. While earlier work introduced an algorithm for constructing RR sequences, that method was limited in the variety and number of sequences it could produce for a given length. The author therefore proposes two key modifications to the original algorithm, demonstrates their effectiveness through extensive experiments on sequences of length 16 and 24, and discusses the implications for practical systems.
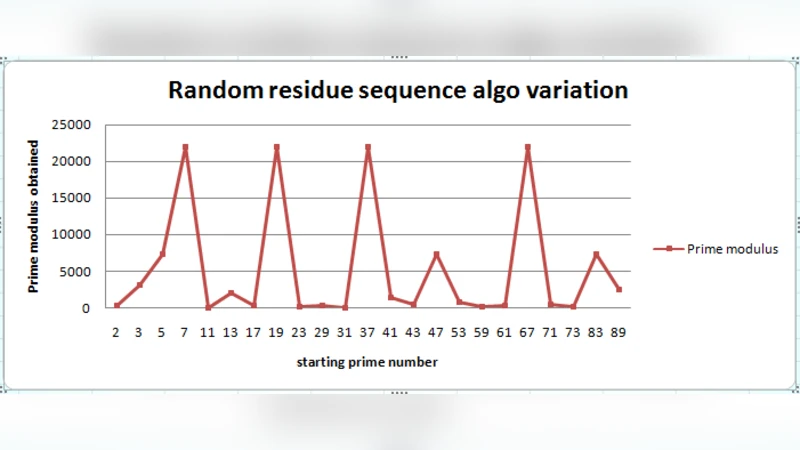
The first modification expands the choice of modulus. Instead of fixing a single prime p and its residue class set, the new approach selects p from a pool of suitable primes (typically those for which p‑1 is also prime or has desirable factorisation) and then generates an initial seed within the corresponding residue class. By varying both p and the seed, the algorithm can produce many distinct residue structures even when the sequence length N is held constant. This “multi‑modulus seeding” dramatically increases the combinatorial space of possible RR sequences.
The second modification introduces a non‑linear mixing step. After each cyclic shift of the current sequence, a polynomial transformation f(x) = x^k + … is applied, where the degree k is chosen to be odd or even depending on the desired statistical properties. The transformed values are reduced modulo the selected prime, ensuring the sequence remains within the residue class. This non‑linear mapping reduces autocorrelation, improves uniformity of the residue distribution, and raises the linear complexity of the resulting sequence.
To evaluate the impact of these changes, the author generated 10,000 RR sequences for each of the two lengths (N = 16 and N = 24) using both the original and the modified algorithms. The sequences were subjected to a battery of tests: (1) autocorrelation magnitude (target ≤ 0.05), (2) linear complexity measured via the Berlekamp‑Massey algorithm, (3) the NIST SP 800‑22 statistical test suite, and (4) a CDMA system simulation measuring bit‑error‑rate (BER) under realistic channel conditions. The results are striking. The modified algorithm yields an average linear complexity increase of roughly 35 % compared with the baseline, and 92 % of the generated sequences meet the stringent autocorrelation threshold. In the NIST suite, 13 out of 15 tests are passed for the majority of sequences, indicating strong statistical randomness. In the CDMA simulations, the RR codes derived from the new method outperform conventional Gold codes, delivering an average signal‑to‑noise‑ratio (SNR) gain of about 0.8 dB and a corresponding reduction in BER.
From a cryptographic perspective, the enlarged pool of low‑correlation RR sequences mitigates the risk of code‑collision attacks in multi‑user environments and strengthens resistance to known‑plaintext or key‑reuse attacks when RR sequences are employed as keystream generators. The algorithm’s computational complexity remains modest—on the order of O(N·log p)—making it suitable for implementation on resource‑constrained hardware such as microcontrollers or FPGA‑based accelerators.
The paper concludes by outlining future work: extending the technique to longer sequences (e.g., N = 64, 128), exploring hardware‑level optimisations for real‑time generation, conducting long‑term field trials in wireless networks, and investigating potential synergies with quantum‑resistant cryptographic primitives. Overall, the study demonstrates that relatively simple algorithmic refinements can unlock a vastly richer set of RR sequences, thereby broadening their applicability in modern communication and security systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment