A new approach for formal behavioral modeling of protection services in antivirus systems
Formal method techniques provides a suitable platform for the software development in software systems. Formal methods and formal verification is necessary to prove the correctness and improve performance of software systems in various levels of design and implementation, too. Security Discussion is an important issue in computer systems. Since the antivirus applications have very important role in computer systems security, verifying these applications is very essential and necessary. In this paper, we present four new approaches for antivirus system behavior and a behavioral model of protection services in the antivirus system is proposed. We divided the behavioral model in to preventive behavior and control behavior and then we formal these behaviors. Finally by using some definitions we explain the way these behaviors are mapped on each other by using our new approaches.
💡 Research Summary
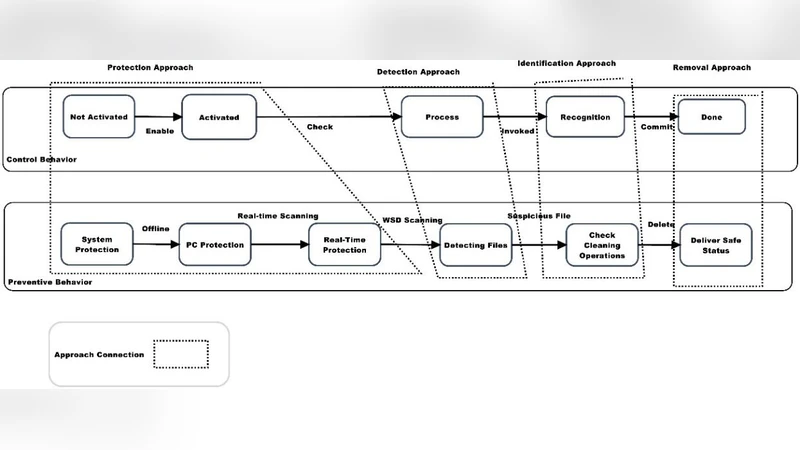
The paper addresses the need for rigorous verification of antivirus (AV) software, which plays a critical role in computer security. Recognizing that most existing AV validation relies on empirical testing rather than formal proof, the authors propose a novel framework that models the behavior of protection services using formal methods. Their approach begins by decomposing AV functionality into two distinct categories: preventive behavior and control behavior. Preventive behavior encompasses activities that aim to stop malware before it can affect the system, such as real‑time scanning, signature matching, and definition updates. Control behavior covers post‑detection actions, including quarantine, deletion, and system restoration.
Four new methodological contributions are introduced. First, a hierarchical modeling technique separates high‑level service flows from low‑level operational details, allowing a clear mapping between abstract security policies and concrete implementation steps. Second, each behavior is expressed as a State Transition System (STS), specifying states, transitions, and guard conditions in a mathematically precise way. Third, the authors incorporate timed automata to capture temporal constraints that are intrinsic to AV operations—most notably the periodic update of virus definitions and the real‑time response requirements of scanning modules. Fourth, a relation‑mapping formalism defines a function that links the terminal states of preventive actions to the initial states of control actions, ensuring that detection outcomes automatically trigger appropriate remediation steps.
The formalization is supported by a series of definitions (12 in total) and theorems (5). Key definitions introduce “protection service” as a tuple of inputs, outputs, and state sets, and then distinguish preventive and control services as separate tuples. A mapping function f : P → C is defined, and Theorem 1 proves that f preserves transition semantics, i.e., every valid preventive transition leads to a valid control start condition. Subsequent theorems verify that the timed constraints are respected (no deadline violations) and that the combined model is deadlock‑free and maintains invariants across the entire lifecycle of a malware incident.
To demonstrate applicability, the authors outline a workflow for translating AV logs and definition files into concrete STS and timed‑automata models. These models can be fed into established model‑checking tools such as UPPAAL or SPIN, where properties like reachability, safety, and liveness are automatically verified. The verification results can be used during design to identify logical gaps, to fine‑tune update intervals, and to certify that remediation actions are correctly triggered under all possible detection scenarios.
The paper concludes by acknowledging that the presented models are abstract and do not yet capture the full complexity of modern AV engines, which often incorporate heuristic, behavior‑based, and machine‑learning components. Future work is suggested in three directions: (1) extending the formalism to include probabilistic or statistical decision modules, (2) conducting large‑scale empirical evaluations to assess performance overhead and scalability, and (3) integrating the formal models into an automated code‑generation pipeline that produces verified AV components directly from specifications.
Overall, the contribution lies in providing a systematic, mathematically grounded way to describe and verify the dual‑phase operation of antivirus protection services. By separating preventive and control behaviors, introducing timed constraints, and defining a precise mapping between them, the authors lay groundwork for more trustworthy AV software development and for the broader adoption of formal verification techniques in security‑critical applications.