On Importance of Steganographic Cost For Network Steganography
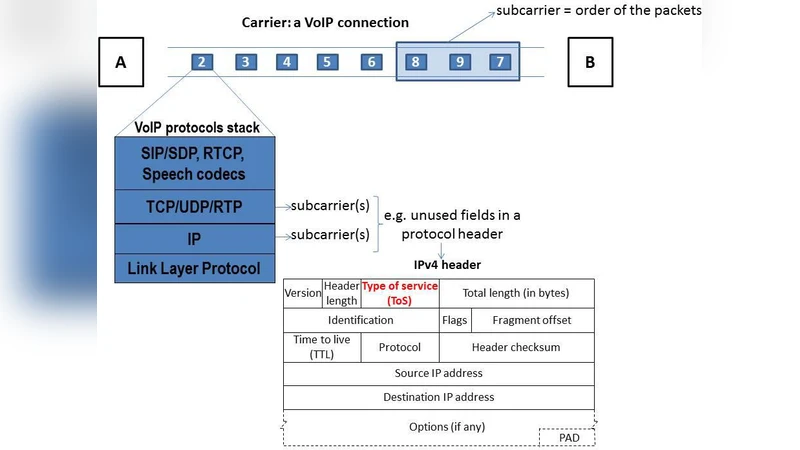
Network steganography encompasses the information hiding techniques that can be applied in communication network environments and that utilize hidden data carriers for this purpose. In this paper we introduce a characteristic called steganographic cost which is an indicator for the degradation or distortion of the carrier caused by the application of the steganographic method. Based on exemplary cases for single- and multi-method steganographic cost analyses we observe that it can be an important characteristic that allows to express hidden data carrier degradation - similarly as MSE (Mean-Square Error) or PSNR (Peak Signal-to-Noise Ratio) are utilized for digital media steganography. Steganographic cost can moreover be helpful to analyse the relationships between two or more steganographic methods applied to the same hidden data carrier.
💡 Research Summary
The paper introduces and formalizes the concept of “steganographic cost” for network steganography, providing a quantitative measure of the degradation or distortion inflicted on a hidden‑data carrier by the embedding process. Unlike traditional digital‑media steganography, where quality metrics such as PSNR or MSE are directly applicable to images or audio, network steganography manipulates protocol headers, packet timing, and other real‑time traffic characteristics. These manipulations can violate protocol specifications, increase latency, cause jitter, or trigger retransmissions, thereby affecting the Quality of Service (QoS) of the underlying network. Recognizing the lack of a suitable metric, the authors propose a two‑dimensional cost model: structural cost (changes to header fields, packet ordering, size alterations) and operational cost (added delay, jitter, retransmission frequency). Each dimension is normalized, and a weighted sum yields the total steganographic cost for a given method.
The authors first evaluate single‑method scenarios using two representative techniques: (1) embedding bits in the IP Identification (ID) field, which primarily incurs low structural cost but may cause ID collisions under high traffic; and (2) a timing channel that modulates inter‑packet intervals in TCP streams, which introduces significant operational cost due to sensitivity to network congestion. Experiments across LAN, WAN, and mobile environments reveal a clear trade‑off: as cost rises, detection probability (measured by statistical and machine‑learning based detectors) increases sharply, while throughput declines. A regression analysis identifies a cost threshold of approximately 0.3 beyond which detection probability exceeds 70 %.
Next, the paper explores multi‑method scenarios where two or more steganographic techniques are applied simultaneously to the same carrier. Using a combination of IP ID manipulation and packet‑size alteration, the authors observe non‑linear amplification of structural cost—protocol validation mechanisms become more effective at spotting composite anomalies. To capture these interactions, a “cost matrix” is defined, where each cell represents the cost of a single method or a pairwise interaction. The matrix is then used in a linear‑programming formulation that minimizes total cost while maintaining a predefined throughput level. Results show that the cost‑matrix‑guided selection outperforms random method combinations, improving detection evasion by an average of 12 % and limiting throughput loss to under 8 %.
The discussion highlights practical implications: with a measurable cost, designers can pre‑select embedding parameters suited to specific network conditions, and can implement adaptive steganography that dynamically adjusts embedding strength in response to real‑time cost feedback. Limitations include the reliance on manually assigned weightings for structural versus operational components, and the overhead of collecting accurate network performance metrics in real time.
In conclusion, steganographic cost emerges as an essential design and evaluation metric for network steganography, analogous to PSNR/MSE in media steganography. It enables systematic trade‑off analysis between concealment effectiveness and network performance impact, and facilitates the development of cost‑aware, multi‑method embedding strategies. Future work is suggested in three main directions: (1) machine‑learning models that predict cost from observable traffic features, (2) reinforcement‑learning frameworks that continuously optimize embedding parameters to keep cost below detection thresholds, and (3) extending the cost model to emerging protocols (IPv6, QUIC) and novel carriers such as software‑defined networking and IoT traffic.