Security Requirements, Counterattacks and Projects in Healthcare Applications Using WSNs - A Review
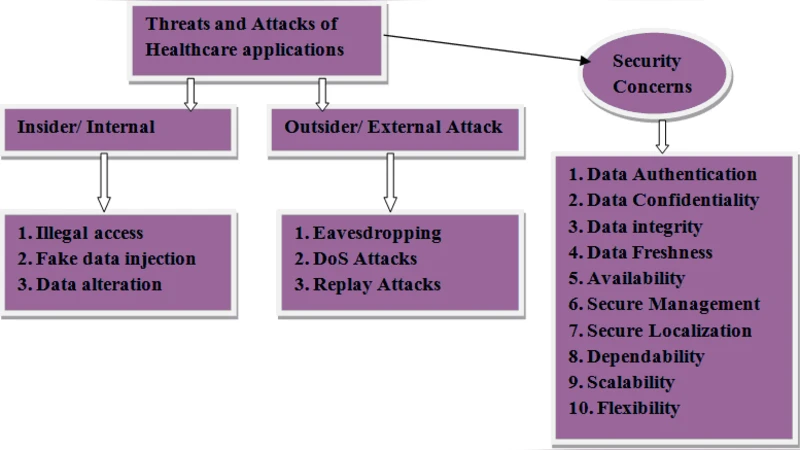
Healthcare applications are well thought-out as interesting fields for WSN where patients can be examine using wireless medical sensor networks. Inside the hospital or extensive care surroundings there is a tempting need for steady monitoring of essential body functions and support for patient mobility. Recent research cantered on patient reliable communication, mobility, and energy-efficient routing. Yet deploying new expertise in healthcare applications presents some understandable security concerns which are the important concern in the inclusive deployment of wireless patient monitoring systems. This manuscript presents a survey of the security features, its counter attacks in healthcare applications including some proposed projects which have been done recently.
💡 Research Summary
The paper provides a comprehensive review of security issues associated with the deployment of wireless sensor networks (WSNs) in healthcare applications. It begins by outlining the growing demand for continuous, mobile monitoring of patients’ vital signs within hospitals and long‑term care facilities, emphasizing that while much research has focused on energy‑efficient routing, reliable data delivery, and patient mobility, security has received comparatively less attention.
The authors identify four fundamental security requirements for medical WSNs: confidentiality, integrity, availability, and authentication/authorization. Confidentiality is critical because physiological data constitute protected health information (PHI) that must be encrypted during transmission. Integrity ensures that any tampering of sensor readings—potentially leading to misdiagnosis—is detectable through mechanisms such as message authentication codes (MACs) or digital signatures. Availability is essential for real‑time monitoring; denial‑of‑service (DoS) attacks could jeopardize patient safety. Authentication and fine‑grained access control prevent rogue devices from joining the network or accessing sensitive records. The paper also stresses privacy‑preserving techniques, including data minimization and anonymization.
A taxonomy of attacks specific to healthcare WSNs follows. Physical node capture is highlighted as a realistic threat because sensor nodes are battery‑powered, often unattended, and can be tampered with to extract stored keys. Eavesdropping and packet manipulation exploit the broadcast nature of wireless links. DoS attacks can overload routing protocols or drain node batteries. Sybil attacks allow a single compromised node to assume multiple identities, disrupting routing and trust calculations. Wormhole attacks create a low‑latency tunnel between two distant points, misleading routing decisions. Replay attacks resend previously captured legitimate packets to bypass authentication.
To counter these threats, the review surveys a range of technical countermeasures. Lightweight cryptography—particularly elliptic curve cryptography (ECC) and AES‑128‑based stream ciphers—is recommended to meet the stringent power constraints of sensor nodes. Key management solutions include pre‑distribution schemes, key pools, and dynamic re‑keying protocols that limit the impact of a compromised node. Authentication protocols move away from heavyweight PKI toward certificate‑based lightweight schemes or blockchain‑derived decentralized trust models. Secure routing protocols such as SAODV, Secure LEACH, and trust‑score based multipath routing are discussed, each integrating authentication tags, hop‑by‑hop verification, and energy‑aware metrics. Physical‑layer defenses against Sybil attacks involve radio fingerprinting, while wormhole mitigation relies on packet timestamps and geographic verification. Replay protection is achieved by embedding nonces or timestamps in every transmitted frame.
The paper then reviews several recent projects that have implemented these concepts. CodeBlue (MIT) demonstrates real‑time emergency alerts using lightweight encryption and authenticated routing. MobiHealth (EU) leverages smartphones as gateways, providing end‑to‑end encryption and secure data aggregation. Korea’s MedMon integrates low‑power sensors with a cloud backend and introduces a blockchain‑based access‑control layer. More recent proposals such as SecureHealthChain employ Hyperledger Fabric to guarantee immutable audit trails and use smart contracts for consent management and fine‑grained data sharing.
Finally, the authors outline future research directions. Quantum‑resistant cryptographic algorithms are identified as a long‑term necessity. Federated learning‑based anomaly detection offers a privacy‑preserving way to identify compromised nodes without transmitting raw data. Integration with emerging 5G/6G networks and edge computing is suggested to offload heavy security processing from constrained sensors while preserving low latency. The review concludes that effective security for healthcare WSNs must combine lightweight cryptography, dynamic authentication, and multi‑layered defense mechanisms, and that standardization and large‑scale field trials are essential for real‑world adoption.
Comments & Academic Discussion
Loading comments...
Leave a Comment