Analysis of Security Threats in Wireless Sensor Network
Wireless Sensor Network(WSN) is an emerging technology and explored field of researchers worldwide in the past few years, so does the need for effective security mechanisms. The sensing technology combined with processing power and wireless communication makes it lucrative for being exploited in abundance in future. The inclusion of wireless communication technology also incurs various types of security threats due to unattended installation of sensor nodes as sensor networks may interact with sensitive data and /or operate in hostile unattended environments. These security concerns be addressed from the beginning of the system design. The intent of this paper is to investigate the security related issues in wireless sensor networks. In this paper we have explored general security threats in wireless sensor network with extensive study.
💡 Research Summary
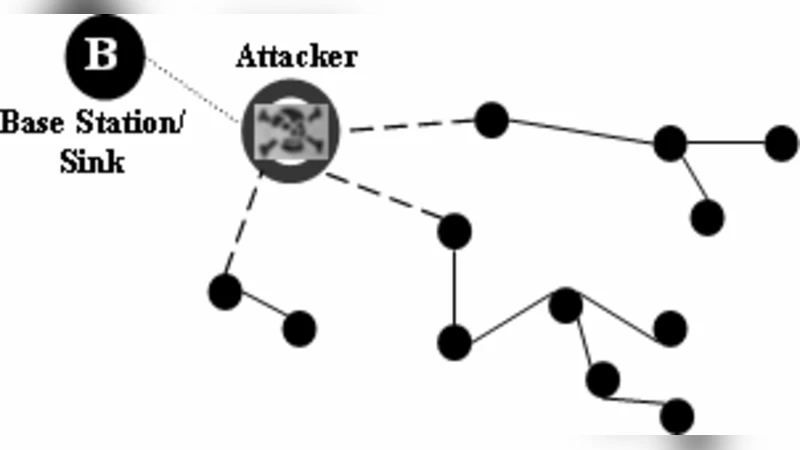
The paper provides a comprehensive overview of security challenges inherent to Wireless Sensor Networks (WSNs) and argues that security must be integrated from the earliest stages of system design. WSNs consist of numerous low‑cost sensor nodes that collect environmental data and forward it wirelessly to a sink or base station. Because these nodes operate with severe constraints on power, memory, and processing, and are often deployed unattended in hostile or remote locations, they present a unique attack surface that differs from traditional wired networks.
The authors categorize threats into four principal groups. Physical attacks include node capture, tampering, and destruction, which can expose cryptographic material and allow adversaries to reprogram or clone devices. Wireless channel attacks exploit the broadcast nature of the medium: eavesdropping, packet injection, replay, and man‑in‑the‑middle attacks compromise confidentiality and integrity when encryption is absent or weak. Network‑layer attacks target routing protocols; malicious nodes may falsify route advertisements, create black‑hole or worm‑hole tunnels, or selectively drop packets, thereby disrupting data delivery. Finally, denial‑of‑service (DoS) and energy‑exhaustion attacks flood the network with spurious traffic or repeated authentication requests, rapidly draining node batteries and shortening network lifetime.
To mitigate these threats, the paper surveys a range of existing countermeasures and evaluates their suitability for resource‑constrained environments. For physical protection, hardware hardening (tamper‑evident enclosures, anti‑tamper sensors) and rapid key revocation mechanisms are recommended. At the link and physical layers, lightweight symmetric ciphers (e.g., AES‑128 variants, RC5, Skipjack) and elliptic‑curve cryptography (ECC) are highlighted as feasible options for confidentiality and authentication, provided that key management is carefully designed. The authors discuss several key distribution schemes, including pre‑shared keys, key pools, and probabilistic key establishment, emphasizing the trade‑off between scalability and resilience to node capture.
Routing security is addressed through trust‑based routing protocols, multipath routing, and geographic or position‑based authentication. Trust metrics derived from neighbor behavior histories enable the network to isolate misbehaving nodes without incurring heavy computational overhead. Intrusion detection systems (IDS) tailored for WSNs monitor traffic patterns, power consumption anomalies, and routing changes to flag suspicious activity.
A central thesis of the work is that effective defense requires a multi‑layered approach: security mechanisms must be coordinated across the physical, data‑link, network, transport, and application layers while remaining lightweight enough to preserve node longevity. The paper also stresses the importance of lifecycle security—continuous key renewal, firmware updates, and policy enforcement throughout deployment, operation, and decommissioning phases.
In conclusion, the authors synthesize the surveyed literature, identify gaps (e.g., limited real‑world evaluations of combined trust‑and‑cryptography schemes), and propose future research directions such as adaptive security frameworks that dynamically balance energy consumption against threat level, and standardized testbeds for benchmarking WSN security solutions. This comprehensive analysis serves as a valuable reference for researchers and practitioners seeking to design robust, energy‑efficient security architectures for emerging sensor‑network applications.