Automatic Generation of Security Argument Graphs
Graph-based assessment formalisms have proven to be useful in the safety, dependability, and security communities to help stakeholders manage risk and maintain appropriate documentation throughout the system lifecycle. In this paper, we propose a set of methods to automatically construct security argument graphs, a graphical formalism that integrates various security-related information to argue about the security level of a system. Our approach is to generate the graph in a progressive manner by exploiting logical relationships among pieces of diverse input information. Using those emergent argument patterns as a starting point, we define a set of extension templates that can be applied iteratively to grow a security argument graph. Using a scenario from the electric power sector, we demonstrate the graph generation process and highlight its application for system security evaluation in our prototype software tool, CyberSAGE.
💡 Research Summary
The paper addresses the need for automated, graph‑based security assessments that can integrate heterogeneous information such as workflow descriptions, system topology, device specifications, known vulnerabilities, and attacker models. Building on earlier work that introduced “security argument graphs” (G‑graph, GS‑graph, GSA‑graph), the authors propose a systematic method to generate these graphs automatically.
The core idea is to capture recurring logical relationships among the various inputs as argument patterns. Five patterns (P1‑P5) are identified, split into inter‑type (connecting different vertex types) and intra‑type (connecting vertices of the same type). For example, P1 links a security goal to the relevant workflows, P2 captures predecessor/successor relationships among workflow steps, P3 associates workflow steps with required actors, P4 maps actors to concrete devices, and P5 decomposes device properties into sub‑properties.
Each pattern is formalized as an extension template γ, consisting of a matching function mγ(v, Σ) that scores the applicability of the template to a given vertex v in the context Σ (the collection of all auxiliary data), and a generation function fγ(v, Σ) that produces a local extension—a star‑shaped subgraph that adds new vertices and edges to the existing graph. The graph itself is defined as a triple (V, E, l) where V is the set of vertices, E the directed edges, and l a mutable labeling function (e.g., probabilities, costs).
Algorithm 1 iteratively scans all vertices, selects the highest‑scoring applicable template for each, and applies the corresponding local extension. This loop continues until no further extensions are possible. The algorithm is generic; by supplying different input datasets it can generate a G‑graph (goal + workflow), a GS‑graph (goal + workflow + system details), or a GSA‑graph (adding attacker actions).
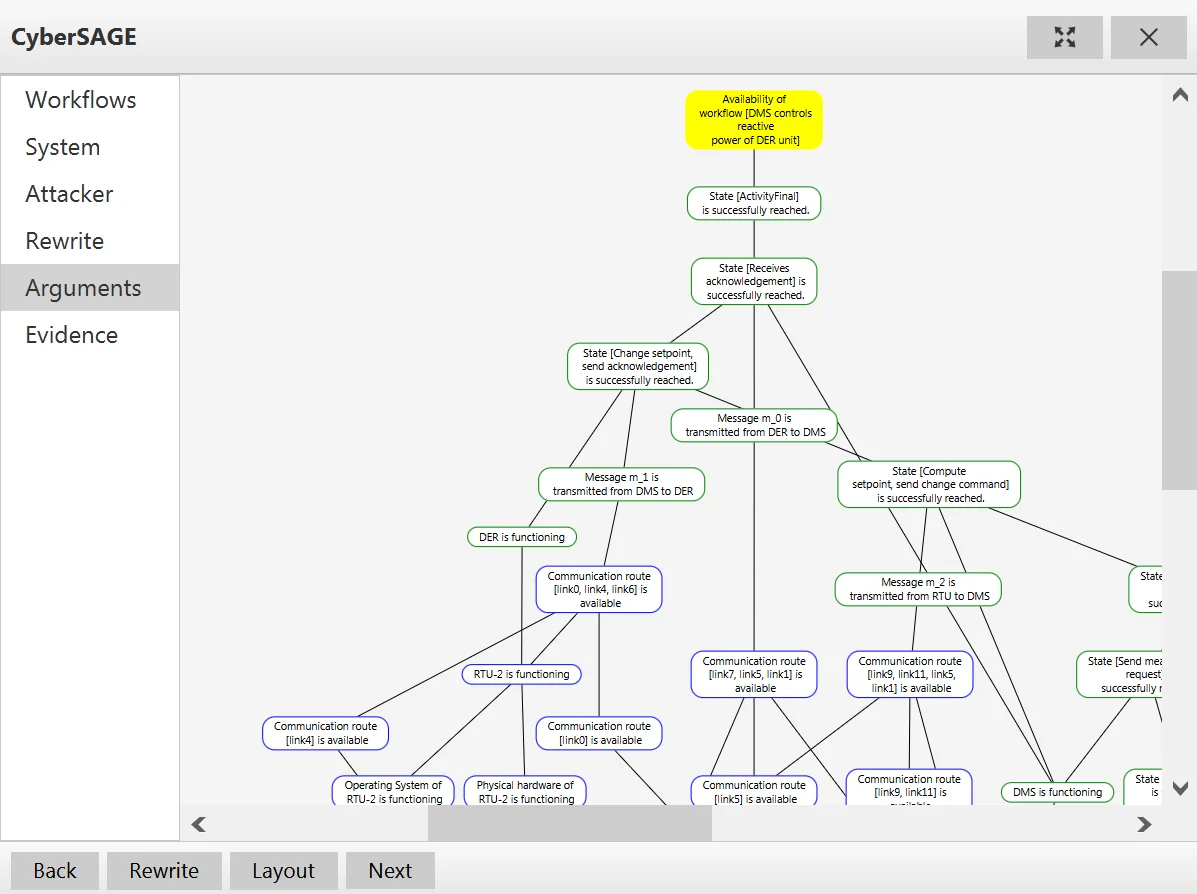
A concrete case study from the electric power sector demonstrates the approach. The security goal is the availability of a substation. The workflow includes SCADA commands, the system model provides RTU and network topology, and vulnerability data supplies known CVEs. Templates T1‑T5 (corresponding to P1‑P5) automatically construct the GS‑graph, while two additional templates (T6, T7) introduce potential attacks on leaf properties and create corresponding attack‑step requirements, yielding the final GSA‑graph. The resulting graph can be fed into the prototype tool CyberSAGE, which visualizes the graph and supports quantitative evaluation (e.g., propagating availability probabilities using Bayesian inference).
Strengths of the work include: (1) a reusable, pattern‑driven methodology that can be extended to new domains by defining additional templates; (2) a clear separation between static graph structure and mutable attributes, simplifying later quantitative analysis; (3) a concrete implementation and demonstration on a realistic critical‑infrastructure scenario.
Limitations are also acknowledged. The matching process may become computationally expensive as the template library grows, requiring efficient indexing or heuristic pruning. The current framework assumes well‑structured, mostly static inputs, making integration of unstructured data (e.g., logs, human behavior) non‑trivial. The case study focuses on availability; extending the method to simultaneously handle confidentiality, integrity, and other multi‑objective security goals will likely need new patterns and more complex aggregation semantics.
In conclusion, the paper presents a rigorous, extensible approach for automatically constructing security argument graphs from diverse security‑related inputs. By formalizing argument patterns as extension templates and providing an iterative generation algorithm, the authors enable systematic, repeatable, and potentially scalable security assessments. Future work will likely explore richer template libraries, performance optimizations for large‑scale systems, and integration with multi‑goal security metrics.
Comments & Academic Discussion
Loading comments...
Leave a Comment