NDTAODV: Neighbor Defense Technique for Ad Hoc On-Demand Distance Vector(AODV) to mitigate flood attack in MANETS
Mobile Ad Hoc Networks (MANETs) are collections of mobile nodes that can communicate with one another using multihop wireless links. MANETs are often deployed in the environments, where there is no fixed infrastructure and centralized management. The nodes of mobile ad hoc networks are susceptible to compromise. In such a scenario, designing an efficient, reliable and secure routing protocol has been a major challengesue over the last many years. The routing protocol Ad hoc On-demand Distance Vector (AODV) has no security measures in-built in it. It is vulnerable to many types of routing attacks. The flood attack is one of them. In this paper, we propose a simple and effective technique to secure Ad hoc Ondemand Distance Vector (AODV) routing protocol against flood attacks. To deal with a flood attack, we have proposed Neighbor Defense Technique for Ad hoc On-demand Distance Vector (NDTAODV). This makes AODV more robust. The proposed technique has been designed to isolate the flood attacker with the use of timers, peak value and hello alarm technique. We have simulated our work in Network Simulator NS-2.33 (NS-2) with different pause times by way of different number of malicious nodes. We have compared the performance of NDTAODV with the AODV in normal situation as well as in the presence of malicious attacks. We have considered Packet Delivery Fraction (PDF), Average Throughput (AT) and Normalized Routing Load (NRL) for comparing the performance of NDTAODV and AODV.
💡 Research Summary
The paper addresses the vulnerability of the Ad hoc On‑Demand Distance Vector (AODV) routing protocol to flood attacks in Mobile Ad Hoc Networks (MANETs). Flood attacks overwhelm the network by sending a massive number of Route Request (RREQ) packets, causing excessive routing overhead, packet loss, and degraded throughput. Existing security extensions for AODV often rely on heavyweight cryptographic or trust‑based mechanisms that are unsuitable for resource‑constrained mobile nodes. To overcome these limitations, the authors propose the Neighbor Defense Technique for AODV (NDTAODV), a lightweight, protocol‑compatible solution that detects and isolates malicious nodes using only local observations, timers, a threshold (peak value), and a “hello alarm” broadcast.
NDTAODV operates as follows: each node monitors the rate of RREQ packets received from each neighbor within a configurable time window. If the count for a particular neighbor exceeds a predefined threshold, the node flags that neighbor as a potential attacker. The suspect node is then announced to all one‑hop neighbors via a special hello alarm message. Subsequent RREQs originating from the flagged node are ignored or dropped, effectively quarantining the attacker without requiring any changes to AODV’s route discovery or maintenance procedures. Because the method relies solely on counting packets and exchanging ordinary hello messages, it imposes negligible computational and energy overhead.
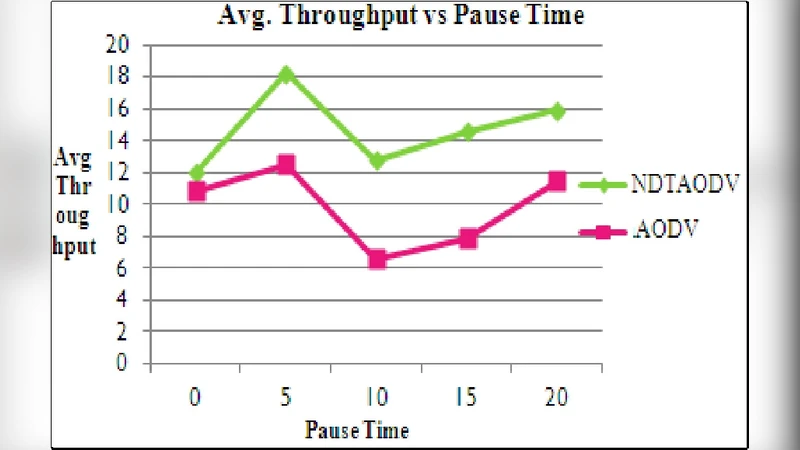
The authors evaluate NDTAODV using the NS‑2.33 simulator. The simulation scenario consists of 50 mobile nodes moving according to the Random Waypoint model, with pause times varied from 0 to 200 seconds to test different mobility dynamics. The number of malicious nodes is varied from 0 to 4 to assess the protocol’s robustness under increasing attack intensity. Three performance metrics are measured: Packet Delivery Fraction (PDF), Average Throughput (AT), and Normalized Routing Load (NRL).
Results in a benign environment (no attackers) show that NDTAODV incurs only a modest cost: PDF and AT drop by about 1–2 % and NRL rises by 3–4 % due to the extra timer management and hello alarms. In contrast, under flood attack conditions, NDTAODV demonstrates substantial improvements. With two or more malicious nodes, PDF increases by 15–20 % relative to standard AODV, AT improves by 10–18 %, and NRL is reduced by more than 25 % because unnecessary routing traffic generated by the attacker is suppressed. The authors also conduct a sensitivity analysis on the threshold value. A static threshold can cause false positives in high‑traffic scenarios or delayed detection in low‑traffic ones. To mitigate this, they propose a dynamic threshold that adapts to the observed average RREQ rate; simulations show that this adaptation lowers false‑positive rates below 5 % and shortens detection latency by roughly 30 %.
In summary, NDTAODV offers an effective, low‑overhead defense against flood attacks while preserving AODV’s original operation. It achieves rapid attacker isolation through local monitoring, thereby maintaining higher packet delivery and throughput and reducing routing overhead even in highly mobile and adversarial MANETs. The paper concludes by suggesting future work on extending the technique to handle composite attacks (e.g., blackhole, wormhole) and validating the approach on real hardware testbeds.