Fingerprinting Internet DNS Amplification DDoS Activities
This work proposes a novel approach to infer and characterize Internet-scale DNS amplification DDoS attacks by leveraging the darknet space. Complementary to the pioneer work on inferring Distributed Denial of Service (DDoS) activities using darknet, this work shows that we can extract DDoS activities without relying on backscattered analysis. The aim of this work is to extract cyber security intelligence related to DNS Amplification DDoS activities such as detection period, attack duration, intensity, packet size, rate and geo-location in addition to various network-layer and flow-based insights. To achieve this task, the proposed approach exploits certain DDoS parameters to detect the attacks. We empirically evaluate the proposed approach using 720 GB of real darknet data collected from a /13 address space during a recent three months period. Our analysis reveals that the approach was successful in inferring significant DNS amplification DDoS activities including the recent prominent attack that targeted one of the largest anti-spam organizations. Moreover, the analysis disclosed the mechanism of such DNS amplification DDoS attacks. Further, the results uncover high-speed and stealthy attempts that were never previously documented. The case study of the largest DDoS attack in history lead to a better understanding of the nature and scale of this threat and can generate inferences that could contribute in detecting, preventing, assessing, mitigating and even attributing of DNS amplification DDoS activities.
💡 Research Summary
The paper introduces a novel methodology for detecting and characterizing DNS amplification Distributed Denial‑of‑Service (DDoS) attacks by analyzing darknet traffic, without relying on backscatter packets. Traditional darknet‑based DDoS detection (e.g., Moore et al.) depends on responses that bounce back to spoofed victim addresses; such approaches cannot capture the malicious DNS queries themselves. The authors argue that attackers send a large number of spoofed DNS ANY queries to open resolvers, and the queries (not the replies) inevitably reach unused IP space (darknet). By monitoring these queries, one can infer the presence of a DNS amplification campaign.
The detection component works as follows: it filters all packets destined for port 53 that contain DNS queries of type ANY. A flow is defined as a series of packets sharing the same source IP and targeting distinct darknet addresses. A flow is classified as a DNS‑amplification attack if it satisfies four criteria: (1) at least 25 packets, (2) at least 25 distinct destination darknet IPs, (3) the query type is ANY, and (4) the queried domain name exists in a curated root/TLD database. These thresholds are chosen to eliminate noise from misconfiguration traffic and low‑rate scanning, while ensuring that the inferred activity involves at least 25 open resolvers.
After flows are identified, the authors further classify them by packet‑per‑second (pps) rate into three categories: low (≤ 0.5 pps), medium (0.5 < pps < 4700), and high (≥ 4700). The low‑rate threshold follows prior work and captures stealthy, slow scans that are otherwise hard to detect. The high‑rate threshold mirrors the propagation speed of the 2003 Slammer worm, serving as a proxy for flash attacks that generate massive traffic in a short time span.
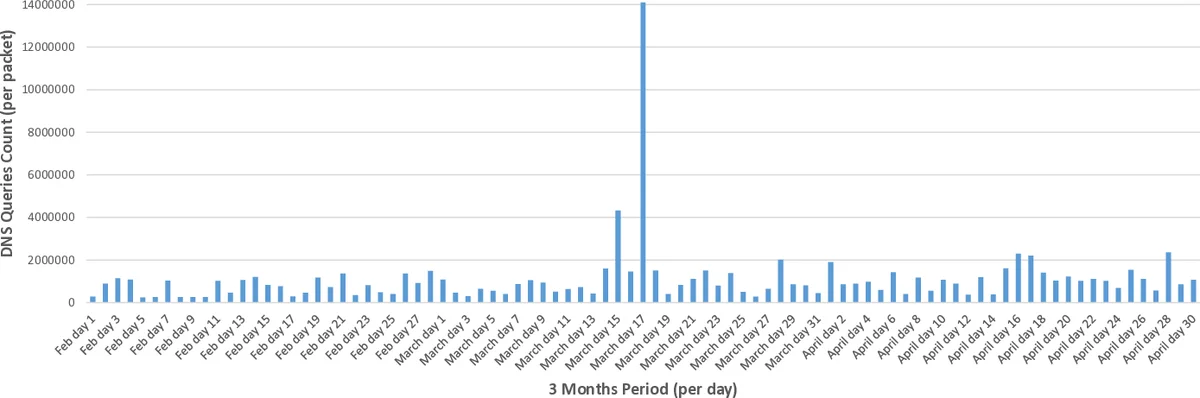
The methodology is evaluated on a real dataset collected over three months (February–April 2013) from a /13 darknet block (≈ 500 000 unused IPs), amounting to 720 GB of one‑way traffic. The analysis discovers 134 distinct DNS amplification attacks, spanning low, medium, and high‑rate categories. Notably, ANY‑type queries constitute 52 % of all DNS queries observed, a dramatic increase compared to earlier studies (≈ 0.02 %). This suggests a recent shift toward exploiting the amplification factor of ANY queries.
A detailed case study focuses on the largest DNS amplification attack reported in March 2013, which reached an estimated 300 Gbps and targeted a major anti‑spam organization. Two source IPs (labeled M1 and M2) each sent ANY queries to roughly 360 000 unique darknet addresses (about 68 % of the monitored space). The average packet size was 68 bytes, and the average rates were 92 pps (M1) and 155 pps (M2), placing them in the medium‑rate category. The queried domain was “ripe.net”, matching public statements from the victim. The timeline shows an initial burst on March 15, a second burst on March 17, and a larger peak later, consistent with the victim’s description of testing phases followed by the full‑scale attack.
The paper also reports that the most requested domain overall was the DNS root zone, followed by a major DNS operator, confirming that attackers aim to retrieve as much zone information as possible to maximize amplification. Peaks in packet volume (up to ~800 k packets per hour) correspond to the identified attacks.
In the discussion, the authors highlight the advantages of their approach: it can detect attacks in near real‑time, does not require cooperation from backscatter providers, and can uncover low‑rate stealth attempts that evade conventional IDS. Limitations include the inability to pinpoint the true victim when source IPs are spoofed, and the reliance on sufficient darknet coverage to observe enough queries. Future work is suggested on integrating passive DNS data, real‑time darknet monitoring, and techniques for attributing spoofed sources.
Overall, the study demonstrates that darknet‑based analysis of DNS queries is a viable and effective avenue for extracting actionable intelligence on DNS amplification DDoS campaigns, offering insights into attack timing, scale, rate, and methodology that can aid detection, mitigation, and attribution efforts.
Comments & Academic Discussion
Loading comments...
Leave a Comment