Information Security Management of Web Portals Based on Joomla CMS
Information is the key asset of all organizations and can exist in many forms. It can be printed or written on paper, stored electronically, transmitted by mail or by electronic means, shown in films, or spoken in conversation. In today’s competitive business environment, such information is constantly under threat from many sources, which can be internal, external, accidental, or malicious. Joomla is a very popular Content Management System (CMS) used for web page maintenance. This highly versatile software has found itself in both large corporate web portals, and simple web pages such as blogs. Such popularity increases its vulnerability to potential attacks and therefore needs an appropriate security management. ISO (the International Organization for Standardization) and IEC (the International Electrotechnical Commission) created the series of standards aimed at providing a model for establishing, implementing, operating, monitoring, reviewing, maintaining and improving an Information Security Management System (ISMS). This paper shows how principles set in ISO/IEC 27000 series of standards can be used to improve security of Joomla based web portals.
💡 Research Summary
The paper investigates how the security of web portals built on the popular open‑source Joomla content‑management system (CMS) can be strengthened by applying the principles of the ISO/IEC 27000 family of information‑security standards. After outlining the growing reliance on web‑based applications and the attendant risks to organizational information, the authors review prior research on open‑source versus closed‑source security, noting that empirical studies have found no consistent superiority of one model over the other. They also discuss the broader ecosystem of CMS tools, highlighting Joomla’s widespread adoption and the consequent attractiveness to attackers.
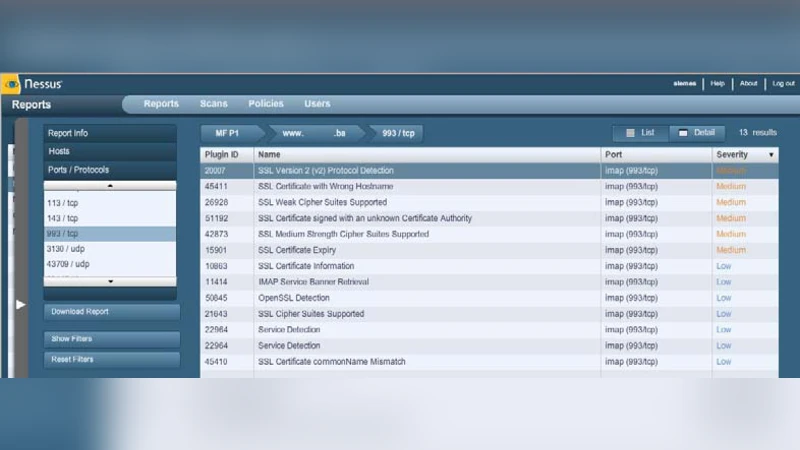
A key contribution of the work is a practical risk‑assessment case study. Using widely available security tools such as Snort, Snare, Tripwire, Nessus and SAINT, the authors scanned a freshly installed Joomla server configured with default settings. The Nessus scan reported 44 medium‑severity vulnerabilities, including default administrative accounts, unnecessary services, and outdated libraries. The paper then maps ISO/IEC 27001’s Plan‑Do‑Check‑Act (PDCA) cycle and the detailed controls of ISO/IEC 27002 onto the Joomla environment. Specific remediation steps—applying security patches, disabling superfluous modules, tightening file permissions, enforcing strong authentication policies, and establishing regular log‑monitoring procedures—are implemented in accordance with the standard’s recommendations. A subsequent scan shows that the number of detected vulnerabilities drops to zero, demonstrating that systematic application of ISO‑based controls can effectively eliminate the known risk surface.
The authors argue that the openness of Joomla’s source code is not an inherent security weakness; rather, security depends on disciplined management, continuous monitoring, and well‑trained personnel. They contend that ISO/IEC 27000 series standards provide a robust framework for establishing an Information Security Management System (ISMS) that can be integrated with existing quality or environmental management systems, thereby offering a comprehensive, auditable approach to protecting web‑portal data.
In conclusion, the study confirms that open‑source CMS platforms like Joomla can be safely deployed for sensitive and confidential web portals, provided that organizations adopt ISO‑aligned security policies, perform regular vulnerability assessments, keep software up‑to‑date, and maintain a culture of security awareness among administrators. The paper thus bridges the gap between theoretical security standards and concrete, actionable steps for securing Joomla‑based web applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment