Importance and Techniques of Information Hiding : A Review
Information or data is very crucial resource to us. Thus securing the information becomes all the more necessary. The communication media through which we send data does not provide data security, so other methods of securing data are required. Information hiding plays a very crucial role today. It provided methods for encrypting the information so that it becomes unreadable for any unintended user. This paper reviews the techniques that exist for data hiding and how can these be combined to provide another level of security.
💡 Research Summary
The paper provides a broad review of information‑hiding techniques that are employed to protect data when the transmission medium itself offers no security. After outlining the growing importance of protecting personal, sensitive, and confidential information, the authors identify four essential attributes of any hiding method: capacity (how much data can be embedded without degrading the cover), security (resistance to unauthorized detection or extraction), robustness (survival of the hidden data through compression, transmission, or other transformations), and perceptibility (the inability of human observers to distinguish the stego‑object from the original).
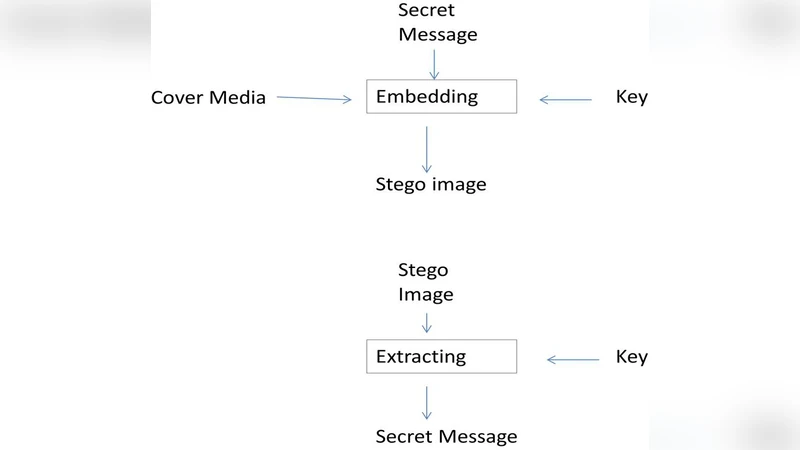
Three major families of techniques are examined. Watermarking, originally a physical‑paper method, is described as a means of embedding imperceptible patterns into images, audio, or video to assert ownership, trace distribution, or embed authentication data. The authors discuss digital watermarking’s need for robustness against common signal processing operations and its role in copyright enforcement. Cryptography is presented as the process of converting plaintext into unreadable ciphertext, providing confidentiality, integrity, authentication, and non‑repudiation. Both symmetric (e.g., AES, DES) and asymmetric (public‑key) schemes are outlined, together with their respective key‑management challenges. Steganography is defined as the concealment of a secret message within a cover object so that the very existence of the hidden data is hidden. The paper distinguishes pure steganography, secret‑key steganography, and public‑key steganography, and lists typical media (text, image, audio/video, IP packets).
A comparative discussion highlights that steganography hides the existence of a message, whereas cryptography obscures its content; the two are complementary. The authors propose hybrid approaches: first encrypting the payload and then embedding the ciphertext using steganography, and alternatively embedding a watermarked document within a stego‑image. These combined schemes are claimed to satisfy all three goals of data hiding—security, capacity, and robustness—more effectively than any single technique.
The conclusion restates the surveyed methods, acknowledges the advantages of hybrid solutions, and notes the lack of experimental validation and the reliance on outdated references (mostly pre‑2014). Overall, the paper serves as an introductory overview of information‑hiding concepts but falls short of providing quantitative performance analysis or coverage of recent advances such as deep‑learning‑based steganography, post‑quantum cryptography, or modern robust watermarking standards.
Comments & Academic Discussion
Loading comments...
Leave a Comment