Vulnerabilities and Attacks Targeting Social Networks and Industrial Control Systems
Vulnerability is a weakness, shortcoming or flaw in the system or network infrastructure which can be used by an attacker to harm the system, disrupt its normal operation and use it for his financial, competitive or other motives or just for cyber escapades. In this paper, we re-examined the various types of attacks on industrial control systems as well as on social networking users. We have listed which all vulnerabilities were exploited for executing these attacks and their effects on these systems and social networks. The focus will be mainly on the vulnerabilities that are used in OSNs as the convertors which convert the social network into antisocial network and these networks can be further used for the network attacks on the users associated with the victim user whereby creating a consecutive chain of attacks on increasing number of social networking users. Another type of attack, Stuxnet Attack which was originally designed to attack Iran’s nuclear facilities is also discussed here which harms the system it controls by changing the code in that target system. The Stuxnet worm is a very treacherous and hazardous means of attack and is the first of its kind as it allows the attacker to manipulate real time equipment.
💡 Research Summary
The paper attempts to provide a broad overview of vulnerabilities and attacks that affect both online social networks (OSNs) and industrial control systems (ICS). It begins by describing the rapid growth of OSNs, especially Facebook, and how the platform’s openness—through APIs such as FBML, FQL, and FBJS—creates opportunities for malicious third‑party applications. The authors introduce a hypothetical “JPGvirus” that embeds a hidden FBML iframe tag in a Facebook photo album page; when a user clicks the photo, a self‑executable file named windows.exe is silently written to the Windows system directory. This file, a simple C program, can be used to launch a distributed denial‑of‑service (DDoS) attack, turning the compromised user’s machine into a bot. The paper also mentions “Puppetnets,” describing how malicious links embedded in web pages can be used to deliver payloads to OSN users, though it provides no concrete implementation details.
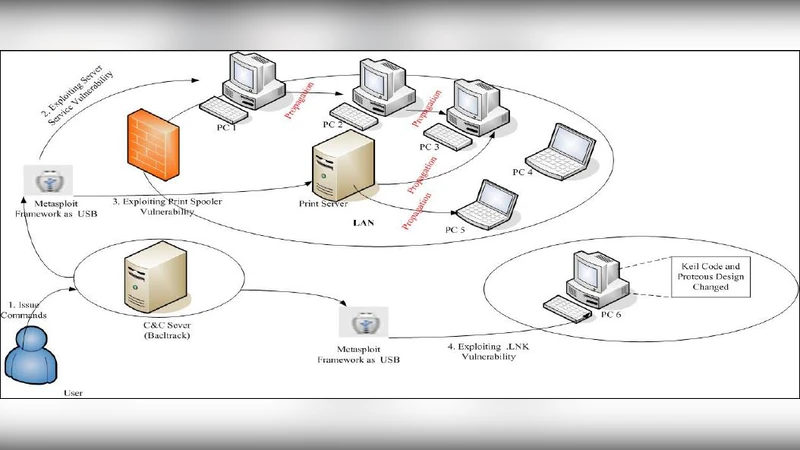
The second major focus is the Stuxnet worm, described as the first cyber‑physical weapon targeting Iran’s nuclear facilities. The authors outline Stuxnet’s two‑phase operation: a propagation phase that spreads via network shares, print spooler services, and removable media, and an injection phase that seeks Siemens WinCC/PLC systems to alter their control logic. Three specific Windows vulnerabilities are highlighted—MS08‑067 (a server service flaw), MS10‑061 (print spooler), and MS10‑046 (LNK shortcut handling). The paper claims these can be reproduced using the Metasploit framework on a Backtrack 4 platform, and presents a schematic network diagram showing a C&C server, a Backtrack attacker machine, and a target system.
Experimental evaluation for the Facebook‑based attack describes creating a malicious FBML tag that generates the windows.exe file when a user visits a photo page. The authors assert that the file is created without triggering Facebook’s internal security checks, but they do not discuss Facebook’s Content Security Policy, app review process, or other mitigations that would likely block such behavior. For Stuxnet, the authors report successful exploitation of the three listed vulnerabilities using Metasploit modules, achieving remote code execution on a test machine. However, the paper lacks detailed logs, timestamps, or performance metrics, and it does not address the fact that these vulnerabilities have been patched in modern Windows releases, limiting the relevance of the demonstration.
Defensive measures are presented in a relatively superficial manner. For OSNs, the paper recommends reliance on Facebook’s built‑in security checks, third‑party services like Websense for link scanning, and stricter privacy settings for users. For Stuxnet, it suggests disabling executable printing, limiting shortcut creation, and applying patches for the cited CVEs. These recommendations are essentially baseline hardening steps and do not cover advanced mitigation techniques such as behavior‑based anomaly detection, memory‑only (fileless) malware defenses, or network segmentation for critical PLC environments.
In conclusion, the authors argue that the expanding user base of social networks creates a fertile ground for “antisocial” platforms that can be weaponized for broader network attacks, while the increasing connectivity of industrial control systems exposes them to sophisticated cyber‑physical threats like Stuxnet. The paper’s ambition to bridge OSN and ICS security is commendable, but the execution falls short: the attack scenarios are either oversimplified or outdated, experimental validation is weak, and the defensive discussion lacks depth. Future work should focus on up‑to‑date vulnerability analysis, reproducible experiments with current toolchains, and comprehensive mitigation strategies that reflect the evolving threat landscape.
Comments & Academic Discussion
Loading comments...
Leave a Comment