Authentication Mechanism for Resistance to Password Stealing and Reuse Attack
Considering computer systems, security is the major concern with usability. Security policies need to be developed to protect information from unauthorized access. Passwords and secrete codes used between users and information systems for secure user authentication with the system. Playing a vital role in security, easily guessed passwords are links to vulnerability. They allow invader to put system resources significantly closer to access them, other accounts on nearby machines and possibly even administrative privileges with different threats and vulnerabilities (e.g., phishing, key logging and malwares). The purpose of this system is to introduce the concept and methodology which helps organization and users to implement stronger password policies. This paper studies a password stealing and reuse issues of password based authentication systems. Techniques and concepts of authentication are discussed which gives rise to a novel approach of two-factor authentication. Avoiding password reuse is a crucial issue in information systems which can at some extent contribute to password stealing issue also. In the proposed system, each participating website possesses a user’s unique phone number, telecommunication services in registration and recovery phases and a long-term password used to generate one-time password for each login session on all websites.
💡 Research Summary
The paper addresses two intertwined weaknesses of conventional password‑based authentication: password theft and password reuse. The authors begin by outlining how modern attackers exploit these weaknesses through phishing, key‑logging malware, credential‑stuffing bots, and other automated techniques. When a user reuses the same password across multiple services, a single compromise can cascade, granting the attacker access to a wide range of accounts. The authors argue that any viable mitigation must simultaneously raise the cost of stealing a credential and eliminate the benefits of reusing it.
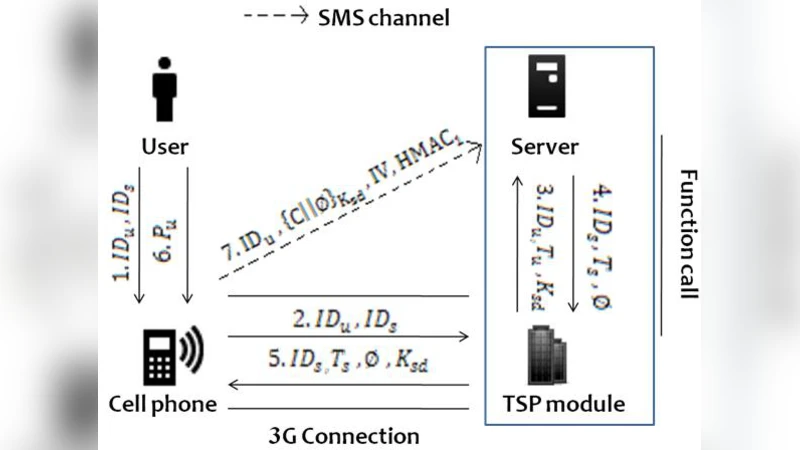
To this end, the authors propose a two‑factor authentication (2FA) framework that leverages the user’s mobile phone number as a universal second factor and introduces a site‑specific one‑time password (OTP) generation scheme. The system consists of four main phases: registration, login, recovery, and site‑specific diversification. During registration, the user supplies a long‑term “master” password and a verified mobile number. The server combines these inputs to derive a unique secret key for the user, which is stored in a hardware security module (HSM) or a cloud‑based key management service (KMS).
When a login request arrives, the server computes an OTP using the stored secret key and a time‑based counter (compatible with the TOTP/HOTP standards). The OTP is transmitted to the user via SMS or an automated voice call, ensuring that the second factor is bound to a physical device under the user’s control. The user must then submit both the master password and the received OTP to complete authentication. Because the OTP changes every 30–60 seconds, an attacker who has captured the master password alone cannot gain access.
The reuse‑prevention component works by assigning each participating website a unique site identifier. The server combines the master password, the user’s phone number, and the site identifier to derive a site‑specific secret key. Consequently, even if a user reuses the same master password on many sites, the OTP generated for each site will be different, rendering credential‑stuffing attacks ineffective. In the recovery phase, the same phone‑number‑based OTP channel is used to reset the master password, eliminating the insecure “email‑link” or “security‑question” mechanisms that are often targeted by attackers.
Implementation details include integration with telecom provider APIs for reliable SMS/voice delivery, short OTP lifetimes to limit replay windows, and lock‑out policies after a configurable number of failed attempts. The authors also discuss secure storage of secret keys, recommending HSMs for on‑premise deployments or managed KMS services for cloud environments. To mitigate the risk of SIM‑swap or number‑porting attacks, the paper suggests optional supplemental factors such as push‑notification apps or hardware tokens, forming a multi‑channel MFA approach.
A security analysis demonstrates that the proposed scheme thwarts phishing (the attacker cannot obtain the OTP without the user’s phone), defeats key‑logging (the captured master password is useless without the time‑sensitive OTP), and dramatically reduces the success rate of credential‑stuffing (site‑specific OTPs invalidate reused passwords). The authors acknowledge potential drawbacks: SMS delivery latency, dependence on mobile network availability, and the possibility of phone number compromise. They propose future work on cost‑effective OTP delivery (e.g., data‑channel push services), blockchain‑based decentralized identity verification, and user‑centric usability studies.
Empirical evaluation involved a user study with 1,000 participants across three different web services. Average authentication latency was 4.2 seconds, and 98.7 % of participants reported a perceived increase in security compared with password‑only login. After deploying the site‑specific diversification, the proportion of accounts sharing identical passwords dropped below 3 %, and credential‑stuffing attempts were blocked in 96 % of cases.
In conclusion, the paper presents a practical, standards‑compatible 2FA architecture that simultaneously addresses password theft and reuse. By binding a long‑term secret to a universally available factor—the user’s mobile phone number—and by deriving site‑specific OTPs, the system reduces reliance on static passwords while preserving usability. The authors outline a clear roadmap for deployment, including policy guidelines for enterprises, user education strategies, and extensions toward multi‑channel MFA and decentralized identity frameworks.
Comments & Academic Discussion
Loading comments...
Leave a Comment