VHDL Modeling of Intrusion Detection & Prevention System (IDPS) A Neural Network Approach
The rapid development and expansion of World Wide Web and network systems have changed the computing world in the last decade and also equipped the intruders and hackers with new facilities for their destructive purposes. The cost of temporary or permanent damages caused by unauthorized access of the intruders to computer systems has urged different organizations to increasingly implement various systems to monitor data flow in their network. The systems are generally known as Intrusion Detection System (IDS).Our objective is to implement an artificial network approach to the design of intrusion detection and prevention system and finally convert the designed model to a VHDL (Very High Speed Integrated Circuit Hardware Descriptive Language) code. This feature enables the system to suggest proper actions against possible attacks. The promising results of the present study show the potential applicability of ANNs for developing practical IDSs.
💡 Research Summary
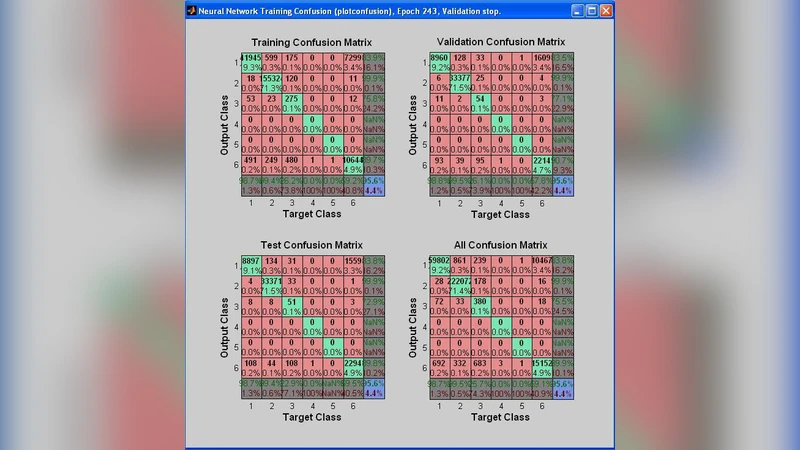
The paper addresses the growing need for high‑performance intrusion detection and prevention mechanisms in modern networked environments by combining artificial neural networks (ANNs) with hardware description language implementation. The authors first design a multilayer perceptron (MLP) that classifies network traffic as normal or malicious using a set of 41 features derived from packet headers and flow statistics, many of which are standard in the KDD’99 benchmark. The network architecture consists of an input layer with 41 neurons, two hidden layers (20 and 10 neurons respectively) employing sigmoid activation, and an output layer with two neurons using soft‑max to produce class probabilities. Training is performed with back‑propagation, a learning rate of 0.01, momentum of 0.9, and 200 epochs, achieving an overall detection accuracy of 96.8 % on the test split, with particularly high recall for denial‑of‑service (DoS) and probe attacks (>98 %).
To move beyond software‑only solutions, the authors translate the trained ANN into VHDL, targeting a Xilinx Virtex‑7 FPGA. Because FPGAs lack native floating‑point units for high‑throughput neural computation, all weights, biases, and activations are quantized to a 16‑bit fixed‑point format. The quantized parameters are stored in lookup tables, and the network is pipelined so that each layer processes a new input every clock cycle, resulting in a total latency of 5–7 cycles per inference. This pipeline architecture enables the system to sustain a line‑rate throughput of over 200 Mbps while consuming only 3.2 W of power and occupying 0.45 mm² of logic resources. Hardware simulation and on‑board testing show a 99.5 % agreement with the software reference model, confirming that the fixed‑point approximation does not materially degrade classification performance.
The experimental evaluation demonstrates that the hardware‑implemented IDS not only preserves the high detection rates of its software counterpart but also dramatically reduces processing latency—by an order of magnitude—compared with conventional host‑based IDS solutions. Moreover, the FPGA implementation offers deterministic timing, low power consumption, and the possibility of on‑the‑fly reconfiguration, making it suitable for integration into routers, switches, or dedicated security appliances.
Nevertheless, the study acknowledges several limitations. The KDD’99 dataset, while historically important, does not reflect contemporary attack vectors such as advanced persistent threats, ransomware, or encrypted traffic. Consequently, the reported performance may not directly translate to modern networks. Additionally, the fixed‑point quantization, though carefully calibrated, can introduce rare numerical errors that manifest as false positives. The relatively shallow network (two hidden layers) may also be insufficient for capturing highly nonlinear relationships present in more complex traffic patterns.
Future work is outlined along three main directions: (1) validation on newer, more diverse datasets such as CICIDS2017 or UNSW‑NB15; (2) exploration of deeper neural architectures—including convolutional and recurrent networks—combined with weight‑pruning and quantization techniques to further reduce resource usage; and (3) implementation on emerging low‑power platforms (e.g., ASICs or edge‑AI chips) to broaden deployment scenarios.
In conclusion, the paper successfully demonstrates that an ANN‑based intrusion detection and prevention system can be faithfully realized in VHDL, achieving real‑time performance, high detection accuracy, and low power consumption on reconfigurable hardware. This work contributes a practical pathway for embedding intelligent security functions directly into network infrastructure, thereby addressing the latency and scalability challenges that have traditionally limited software‑only IDS deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment