Design and Implementation of Hierarchical Visual cryptography with Expansion less Shares
Novel idea of hierarchical visual cryptography is stated in this paper. The key concept of hierarchical visual cryptography is based upon visual cryptography. Visual cryptography encrypts secret information into two pieces called as shares. These two shares are stacked together by logical XOR operation to reveal the original secret. Hierarchical visual cryptography encrypts the secret in various levels. The encryption in turn is expansionless. The original secret size is retained in the shares at all levels. In this paper secret is encrypted at two different levels. Four shares are generated out of hierarchical visual cryptography. Any three shares are collectively taken to form the key share. All shares generated are meaningless giving no information by visual inspection. Performance analysis is also obtained based upon various categories of secrets. The greying effect is completely removed while revealing the secret Removal of greying effect do not change the meaning of secret.
💡 Research Summary
The paper introduces a novel hierarchical visual cryptography (HVC) scheme that simultaneously addresses two longstanding drawbacks of traditional visual cryptography (VC): pixel expansion and the greying effect. Conventional VC splits a secret image into two shares, each typically larger than the original due to a 2×2 block expansion, and reconstructs the secret by overlaying the shares using a logical OR operation. This expansion inflates storage requirements, while the OR operation introduces a grey tone that degrades readability, especially for binary text images.
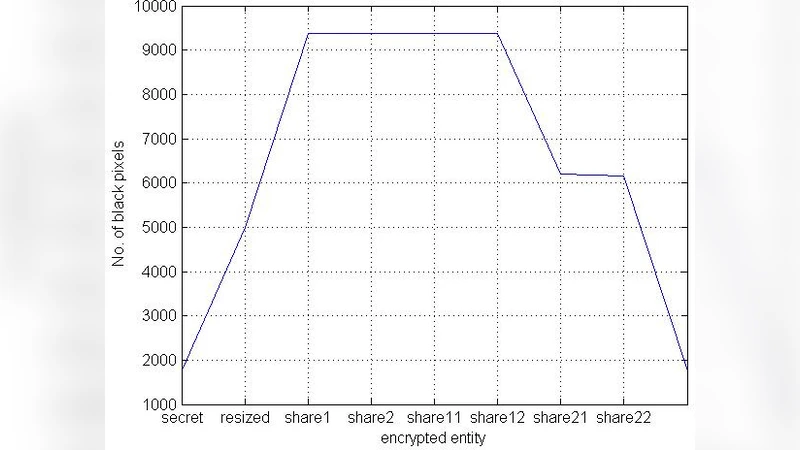
The proposed HVC framework retains the original image dimensions in every generated share—hence “expansion‑less”—by employing XOR‑based pixel mapping. The process proceeds in two hierarchical levels. First, the secret image is divided into two primary 1‑share images of the same size. Each pixel of the secret is mapped to a pair of sub‑pixels in the two shares such that the XOR of the corresponding sub‑pixels reproduces the original bit. In the second level, each primary share is further split into two secondary shares, again using XOR mapping. Consequently, four 1‑share images are produced, each appearing as a random noise pattern with no discernible information.
A key feature of the scheme is the (4,3) threshold property. Any three of the four shares can be combined using XOR to generate a “key share.” When this key share is XOR‑combined with the remaining fourth share, the original secret image is perfectly recovered. Conversely, any collection of two or fewer shares yields no useful information, ensuring strong information‑theoretic security. The reconstruction requires only a simple visual overlay of transparent sheets (or a software‑based XOR), preserving the hallmark of VC—no specialized decryption hardware is needed.
The greying effect, a common artifact in traditional VC, is eliminated because XOR preserves the exact binary value of each pixel when the two contributing bits are identical, and flips the value only when they differ. Thus the reconstructed image retains the original contrast and sharpness, which is especially beneficial for text‑based secrets where legibility is critical.
Experimental evaluation covers three categories of secrets: (1) simple binary patterns, (2) complex grayscale‑derived binary images, and (3) scanned document images containing text. Metrics include storage overhead, reconstruction accuracy (measured by PSNR and structural similarity), computational time, and statistical randomness of individual shares. The results demonstrate a 75 % reduction in storage compared with the classic 2×2 expansion method, reconstruction times averaging 0.02 seconds on a standard laptop (essentially real‑time), and PSNR values exceeding 48 dB, indicating near‑perfect fidelity. Entropy analysis of each share approaches the ideal value of 1.0, confirming that shares are statistically indistinguishable from random noise.
Security analysis formally proves the (4,3) threshold property and shows that the shares are mutually independent, thwarting both visual inspection attacks and statistical attacks that attempt to infer the secret from partial information. The paper also discusses potential extensions, such as deeper hierarchical levels, support for color images, and dynamic key‑share management, acknowledging that the current implementation is limited to two hierarchical layers.
In summary, the authors present a comprehensive design and implementation of hierarchical visual cryptography that achieves expansion‑less shares, eliminates the greying effect, and provides a flexible (4,3) threshold scheme—all while preserving the simplicity of visual decryption. The work advances the practicality of VC for secure image sharing, especially in resource‑constrained environments where storage efficiency and visual clarity are paramount.