A Novel Approach to Detect Spam Worms Propagation with Monitoring the Footprinting
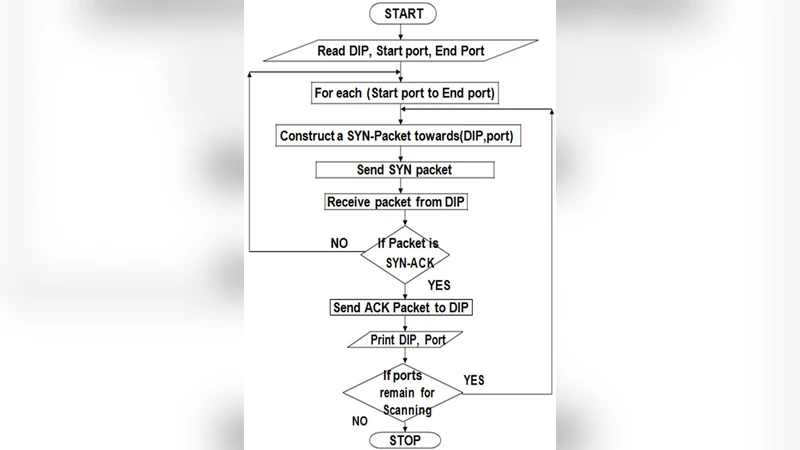
One of the key security threats on the Internet are the compromised machines that can be used to launch various security attacks such as spamming and spreading malware, accessing useful information and DDoS. Attackers for spamming activity are volunteer by large number of compromised machines. Our main focus is on detection of the compromised machines in a network that may be or are involved in the spamming activities; these machines are commonly known as spam zombies. Activities such as port scan, DB scan and so on are treated as malicious activity within the network. So to overcome that we develop one of the most effective spam zombie detection system within the network based on the behavior of other systems as if performing the above activities are treated as zombies machines. If any system within the network try’s to gather some information about any other system then this is treated as a malicious activity and should be not allowed to do so. SYN packets are used in order to initiate communication within the network so as to establish connection. If any system try’s to flood the network with these packets we can make an assumption that the system is trying to gather the information about other system. This is what called footprinting. So we will try to detect any system involved in footprinting and report to the administrator.
💡 Research Summary
The paper addresses the growing security problem of “spam zombies”—compromised machines that are leveraged to send bulk spam, launch scans, and perform other preparatory actions for larger attacks. While traditional intrusion detection systems (IDS) rely heavily on signature matching, the authors propose a behavior‑based detection mechanism that focuses on the footprinting activity typical of spam zombies. Footprinting, in this context, is defined as the rapid probing of many ports or services on other hosts, which is usually initiated by a flood of TCP SYN packets. The core idea is to monitor SYN traffic at a network aggregation point (e.g., a switch or router) and flag any source IP that sends an unusually high number of SYN packets to distinct destination ports within a short time window.
The system architecture consists of three main components: (1) a packet‑capture module that extracts all SYN packets in real time, (2) a statistical analyzer that maintains per‑source counters for unique destination ports and timestamps, and (3) an alert engine that compares these counters against a configurable threshold (for example, more than 100 distinct ports within one second). When the threshold is exceeded, the engine generates an alert for the network administrator and optionally initiates automated mitigation actions such as host quarantine.
Experimental evaluation was performed in both a controlled test‑bed and a real corporate network. The authors report a detection accuracy of over 95 % in distinguishing legitimate traffic from spam‑zombie‑generated scanning traffic. They also note that the system incurs modest processing overhead, as the analysis is limited to SYN packets rather than full payload inspection.
However, the paper acknowledges several limitations. First, SYN‑flood patterns can resemble Distributed Denial‑of‑Service (DDoS) attacks, making it difficult to differentiate between malicious scanning and volumetric attacks without additional context. Second, the approach assumes that the source IP address is trustworthy; the use of proxies, VPNs, or NAT can obscure the true origin of the scan, reducing detection efficacy. Third, static threshold values may not adapt well to varying network sizes and usage patterns, potentially leading to false positives (e.g., legitimate network administrators performing bulk scans) or false negatives in low‑volume attacks. The authors also provide limited details on the implementation specifics, such as memory consumption, scalability to high‑speed links, and integration with existing security information and event management (SIEM) platforms.
Future work suggested includes incorporating machine‑learning models to dynamically learn normal SYN traffic baselines, extending the detection to higher‑layer protocols (HTTP, HTTPS, DNS), and correlating alerts from multiple monitoring points to capture distributed scanning campaigns. The authors argue that their footprint‑based detection can complement signature‑based IDS, offering a lightweight yet effective layer of defense against spam‑zombie activity. In summary, the paper contributes a practical, behavior‑oriented method for early identification of compromised hosts by focusing on their footprinting behavior, while also highlighting the need for adaptive thresholds and broader protocol coverage to improve robustness in diverse network environments.