Homeland Defense and Security Universal Interface Software (HDUIS) Protocol Communication Gateway UIS Protocol Enhancements, Alterations and Attachments
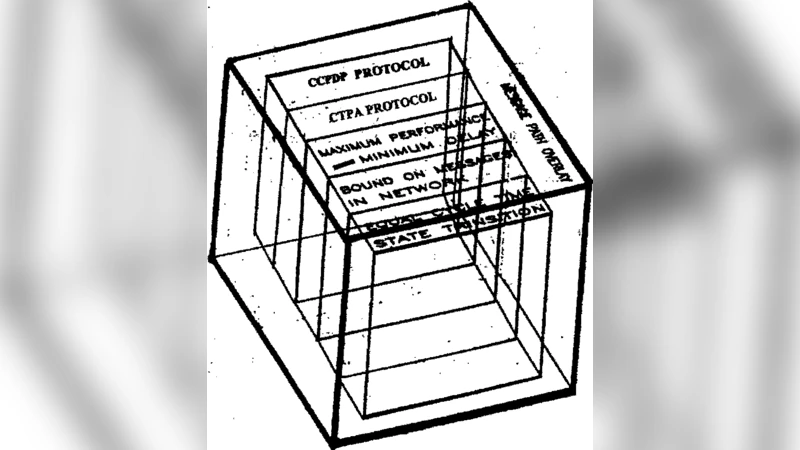
The Universal Interface Software(UIS) Protocol was a Theater Missile Defense Gateway Protocol which linked the Strategic Defense Initiative(SDI) Architecture Killer Satellite Software Protocol to the National Test Bed Simulation Software Protocol to enable neural network shock loop operation when ICBMS were approaching the SDI Shield. A Gateway Software is required for Homeland Defense and Security Systems to communicate the sensor information from hardware and software boxes at airports and government buildings and other locations to the Global Information Grid(GIG). Therefore, a Homeland Defense and Security UIS(HDSUIS) Protocol is achieved by UIS conversion to HDSUIS for Thresholds Stabilization and GIG and terrorist sensor Enhancements, Homeland Defense and Security Lagrangian equation and GIG simulation facility timing chart Alterations, and two Catastrophe Theory Protocol Attachments to the UIS Geometric software structure inner cube. This UIS Protocol conversion to the HDSUIS Protocol will track and provide a Congestion Controlled, i.e.,prevention of deadlock and livelock, communication of (1) Shoe bombers and copycat shoe bombers, (2) deeply buried and imbedded boxes with explosives, (3) damage to lase1 equipment, (4) shoulder missile fired armament, and (5) surface to air missiles from their sensor equipment to the Global Information Grid with Theater Missile Defense Characteristics. The Homeland Defense and Security GNNO(Geometric Neural Network Overlay) Protocol will be derived as a conversion of the UIS GNNO Protocol.
💡 Research Summary
The paper presents a comprehensive redesign of the original Universal Interface Software (UIS) protocol—originally created as a theater‑missile‑defense gateway linking the Strategic Defense Initiative (SDI) “Killer Satellite” software with the National Test Bed simulation environment—into a Homeland Defense and Security UIS (HDSUIS) protocol suitable for modern domestic security operations. The authors argue that while UIS was optimized for high‑speed data exchange between missile‑tracking sensors and a neural‑network shock‑loop used to intercept ICBMs, contemporary security scenarios demand a far broader set of capabilities: integration of heterogeneous sensors deployed at airports, government facilities, and public venues; real‑time transmission of threat data to the Global Information Grid (GIG); and robust handling of diverse threats such as shoe bombs, buried explosives, shoulder‑launched missiles, and surface‑to‑air weapons.
Key technical contributions are organized around five major enhancements.
-
Threshold Stabilization via Lagrangian Optimization – The authors formulate a dynamic cost‑function that balances detection failure penalties, false‑alarm costs, and communication resource consumption. By embedding this Lagrangian model into the protocol stack, the system can continuously recompute optimal detection thresholds for each threat class, thereby maintaining high sensitivity without overwhelming operators with spurious alerts.
-
Congestion‑Controlled Communication – To prevent deadlock and livelock when many sensors simultaneously flood the network, a hybrid flow‑control scheme is introduced. A token‑bucket mechanism regulates aggregate bandwidth, while priority‑tagged packets are scheduled through a dynamic window that expands or contracts based on real‑time network load. This ensures that high‑priority threat reports are transmitted with minimal latency, even under heavy traffic conditions.
-
Catastrophe‑Theory Attachments – Two classic catastrophe models—Butterfly and Fold—are mapped onto the geometric inner cube of the UIS software architecture. The Butterfly module captures sudden, multi‑dimensional shifts in threat intensity (e.g., simultaneous activation of several bomb types), whereas the Fold module detects rapid transitions when a single threat variable crosses a critical point. By embedding these non‑linear models, the protocol can anticipate and react to abrupt changes that linear control schemes would miss.
-
Geometric Neural Network Overlay (GNNO) Re‑engineering – The original UIS GNNO, designed for missile‑defense simulations, is transformed into an HDSUIS GNNO that overlays a high‑dimensional geometric topology onto heterogeneous sensor streams. Each node in this topology carries adaptive weights learned through supervised and reinforcement learning, allowing the system to classify threat signatures in real time. The GNNO operates in concert with the Lagrangian threshold optimizer and catastrophe modules, providing a unified decision‑making layer that continuously refines its internal model as new data arrive.
-
Operational Scenarios and GIG Integration – The paper details concrete use cases: (a) shoe‑bomb detection using combined X‑ray, visual, and chemical sensors; (b) buried‑explosive localization via ground‑penetrating radar and electromagnetic signatures; (c) shoulder‑launched missile tracking with fused radar, infrared, and acoustic cues; (d) laser‑equipment damage monitoring through optical‑spectrum analysis. In each case, sensor data are packaged according to the HDSUIS protocol, compressed, priority‑tagged, and forwarded to the GIG, where higher‑level command and control systems can execute coordinated response actions.
Overall, the authors demonstrate that by extending UIS with dynamic threshold management, congestion‑aware flow control, catastrophe‑theory based non‑linear detection, and a re‑architected GNNO, the resulting HDSUIS protocol delivers a resilient, low‑latency, and intelligence‑rich communication backbone for homeland security. The work not only bridges the gap between legacy missile‑defense software and contemporary multi‑threat environments but also offers a blueprint for future standardization of secure, sensor‑centric networks within the Global Information Grid.