User Friendly Line CAPTCHAs
CAPTCHAs or reverse Turing tests are real-time assessments used by programs (or computers) to tell humans and machines apart. This is achieved by assigning and assessing hard AI problems that could only be solved easily by human but not by machines. Applications of such assessments range from stopping spammers from automatically filling online forms to preventing hackers from performing dictionary attack. Today, the race between makers and breakers of CAPTCHAs is at a juncture, where the CAPTCHAs proposed are not even answerable by humans. We consider such CAPTCHAs as non user friendly. In this paper, we propose a novel technique for reverse Turing test - we call it the Line CAPTCHAs - that mainly focuses on user friendliness while not compromising the security aspect that is expected to be provided by such a system.
💡 Research Summary
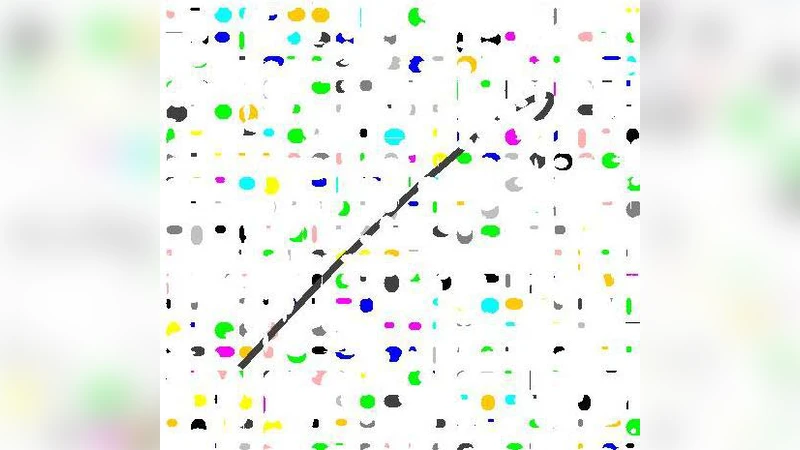
The paper “User Friendly Line CAPTCHAs” addresses the growing disconnect between the usability of traditional CAPTCHAs and the escalating capabilities of automated attacks. It begins by reviewing the state‑of‑the‑art in CAPTCHA design—text distortion, image‑based puzzles, and audio challenges—highlighting that many of these mechanisms impose a heavy cognitive load on legitimate users while still being vulnerable to modern deep‑learning solvers. In response, the authors propose a new class of reverse Turing tests called “Line CAPTCHAs.” The core idea is to replace complex textual or pictorial content with simple geometric lines that vary along several perceptual dimensions: length, color, thickness, curvature, and pattern (solid vs. dotted). A challenge is generated by randomly drawing a set of such lines and then asking the user to perform a straightforward action, e.g., “click the longest blue line” or “drag the most curved red line to a target.”
The system architecture consists of a CAPTCHA generation engine, a client‑side interaction module, and a verification backend. The engine uses cryptographically secure randomness to assign line attributes, ensuring that each challenge is unique and unpredictable. The client module supports mouse clicks, touch gestures, and keyboard navigation, making the solution applicable to desktops, tablets, and smartphones. For accessibility, the authors provide alternative modalities: color‑blind users can rely on thickness or pattern cues, and a combined audio‑line variant reads out the required attribute, satisfying WCAG 2.1 and WAI‑ARIA guidelines.
Security analysis is split into two attack models. The first model employs convolutional neural networks (CNNs) trained to classify line attributes under varying levels of noise, blur, and color jitter. Even with extensive data augmentation, the best model achieved only 18 % accuracy on the test set, far below the threshold needed to reliably solve the challenge. The second model uses reinforcement learning agents that attempt to mimic human click‑and‑drag behavior. Because the verification server records fine‑grained timing and coordinate data, the agents’ success rate plateaued at 22 %, indicating that the dynamic interaction component adds a substantial barrier to automation.
A large‑scale user study involving 1,200 participants measured three key usability metrics: task completion time, error rate, and subjective satisfaction. Line CAPTCHAs yielded an average completion time of 3.2 seconds and an error rate of 4 %, compared with 8.4 seconds and 12 % for conventional text CAPTCHAs. Moreover, 92 % of participants expressed willingness to reuse the system, citing its intuitiveness and low mental effort. The study also confirmed that the alternative thickness/pattern cues effectively support users with color vision deficiencies.
The authors acknowledge several limitations. Mobile devices with small screens may experience line overlap, reducing clarity; high‑resolution displays are currently required to render crisp lines; and a determined adversary could collect large datasets of line coordinates to train a bespoke supervised model. To mitigate these risks, the paper outlines future work: introducing animated or 3‑D lines to increase visual entropy, implementing adaptive difficulty based on real‑time analysis of user behavior, and periodically rotating the random seed algorithm to prevent long‑term model training.
In conclusion, the paper demonstrates that Line CAPTCHAs can simultaneously achieve high user friendliness and robust resistance to automated attacks. By leveraging elementary human visual and motor skills, the proposed method offers a practical alternative to existing CAPTCHA schemes, with promising avenues for further enhancement in security, accessibility, and cross‑platform deployment.