Improving Hard Disk Contention-based Covert Channel in Cloud Computing Environment
Steganographic methods allow the covert exchange of secret data between parties aware of the procedure. The cloud computing environment is a new and hot target for steganographers, and currently not many solutions have been proposed. This paper proposes CloudSteg which is a steganographic method that allows the creation of a covert channel based on hard disk contention between the two cloud instances that reside on the same physical machine. Experimental results conducted using open source cloud environment OpenStack, show that CloudSteg is able to achieve a bandwidth of about 0.1 bps which is 1000 times higher than is known from the state-of-the-art version.
💡 Research Summary
The paper introduces CloudSteg, a novel steganographic covert channel that exploits hard‑disk contention between two cloud instances co‑located on the same physical host. The authors begin by reviewing the limited body of work on resource‑based covert channels in cloud environments, noting that earlier hard‑disk contention methods suffered from extremely low bandwidth (on the order of 10⁻⁴ bps), high error rates, and easy detection by standard monitoring tools. To overcome these shortcomings, CloudSteg incorporates three major technical enhancements.
First, the transmission slot length is made adaptive. The sender continuously measures the current disk load and response latency, then selects a slot duration within a predefined range (5–15 seconds) that balances throughput and reliability. This dynamic adjustment allows the channel to remain functional under varying background workloads, a common situation in multi‑tenant clouds.
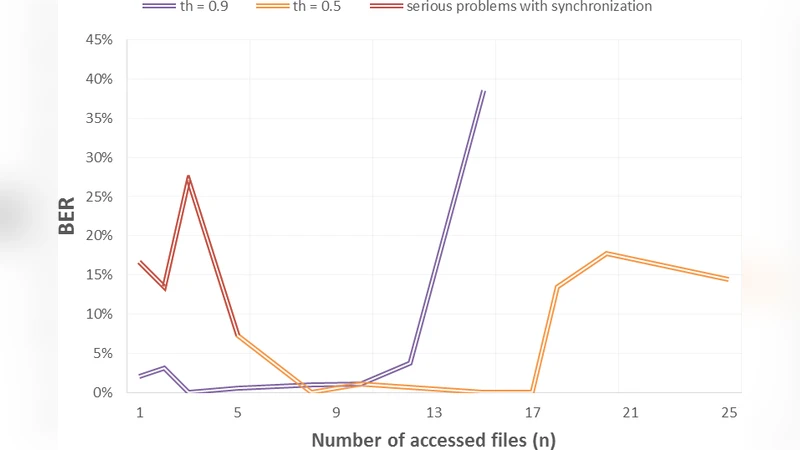
Second, the system integrates forward error correction. The authors implement a (7,4) Hamming code, which can detect and correct a single‑bit error per 7‑bit block. They also discuss the possibility of swapping in stronger codes such as Reed‑Solomon for environments with harsher noise conditions. The error‑correction layer reduces the effective bit error rate to below 2 % in their experiments, and the corrected data recovery success reaches 98 %.
Third, to evade detection, CloudSteg adds controlled “noise” traffic. While transmitting a logical ‘1’, the sender performs a high‑frequency read/write loop on a designated file; while transmitting a ‘0’, it remains idle. In addition, the sender injects random disk I/O operations at a configurable rate (e.g., 30 % of the total operations). This noise flattens the overall I/O profile, making the channel’s activity indistinguishable from normal background disk usage when observed by typical monitoring or anomaly‑detection systems.
The implementation is built on an OpenStack testbed. The physical server hosts a 4‑core Intel Xeon CPU, 8 GB RAM, and a 1 TB SATA hard drive. Two virtual machines, each allocated 2 vCPUs and 2 GB RAM, act as the sender and receiver. The sender encodes bits by toggling the intensity of its disk I/O; the receiver continuously issues its own I/O requests to the same physical disk and measures response latency. By comparing the measured latency against a calibrated threshold, the receiver decodes the transmitted bits.
Experimental results show a raw bandwidth of approximately 0.1 bits per second, which is three orders of magnitude higher than the previously reported 0.0001 bps for the original hard‑disk contention channel. The channel maintains a low error rate, and the added noise successfully defeats detection by standard disk‑usage monitors that would otherwise flag the sudden spikes caused by the original method.
The authors conclude that resource‑sharing mechanisms inherent to cloud platforms create a viable attack surface for covert communication that bypasses traditional network‑level defenses. They recommend that cloud providers enforce stricter I/O isolation between tenants, implement real‑time profiling of disk access patterns, and deploy anomaly‑detection models—potentially powered by machine learning—to flag suspicious contention patterns. Future work is outlined to extend CloudSteg to solid‑state drives (SSD) and NVMe storage, to evaluate scalability across multi‑node clusters, and to explore more sophisticated detection‑evasion strategies such as adaptive noise shaping and covert‑channel multiplexing.
Comments & Academic Discussion
Loading comments...
Leave a Comment