Secure SAML validation to prevent XML signature wrapping attacks
SAML assertions are becoming popular method for passing authentication and authorisation information between identity providers and consumers using various single sign-on protocols. However their practical security strongly depends on correct implementation, especially on the consumer side. Somorovsky and others have demonstrated a number of XML signature related vulnerabilities in SAML assertion validation frameworks. This article demonstrates how bad library documentation and examples can lead to vulnerable consumer code and how this can be avoided.
💡 Research Summary
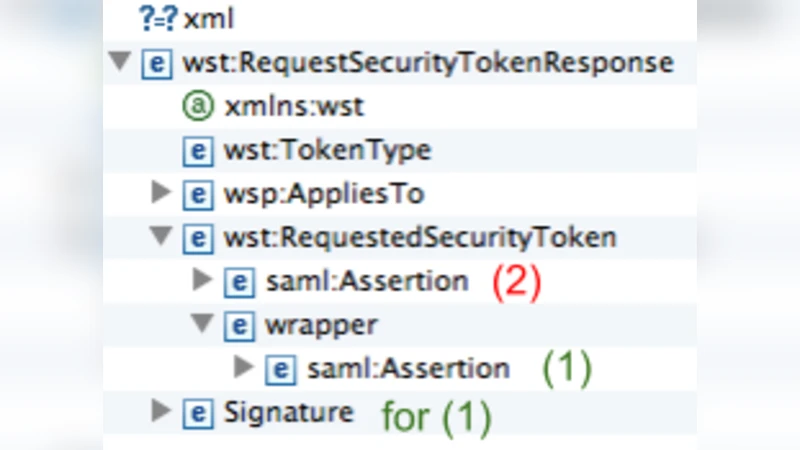
The paper addresses a critical yet often overlooked aspect of SAML (Security Assertion Markup Language) security: the correctness of signature validation on the service‑provider side. While SAML has become the de‑facto standard for transmitting authentication and authorization statements in single‑sign‑on (SSO) scenarios, its security guarantees hinge entirely on the proper verification of XML digital signatures. The authors begin by describing the XML Signature Wrapping attack, a technique that exploits weaknesses in the way applications locate and validate the signed element. An attacker can keep the original signed Assertion intact, insert a malicious sibling or child element, and manipulate the document structure so that a naïve validation routine processes the attacker‑controlled node instead of the legitimately signed one.
Building on prior work by Somorovsky et al., the paper systematically surveys the most widely used SAML validation libraries—Apache Santuario, OpenSAML (Java), and System.Security.Cryptography.Xml (.NET). It demonstrates that many reference implementations rely on insecure coding patterns: (1) using generic DOM methods such as Document.getElementsByTagName which return all elements with a given local name, then validating only the first entry; (2) employing XPath expressions like “//Signature” without a proper NamespaceContext, which can match unintended nodes; and (3) assuming that invoking a single Signature.validate() call is sufficient, ignoring the need to verify that each Reference URI actually points to the expected Assertion ID. The authors reproduce concrete proof‑of‑concept exploits against each library, showing that an attacker can craft a SAML response that passes signature verification while containing a forged Assertion that grants unauthorized privileges.
The core contribution of the paper is a set of concrete, language‑agnostic guidelines for robust SAML signature validation:
-
Explicit Reference‑ID Matching – After extracting the Assertion’s
IDattribute, the application must compare it against everyReferenceURI resolved during signature validation. Any mismatch should abort the authentication flow. -
Namespace‑Aware XPath – When XPath is used to locate the
<ds:Signature>element, the query must be absolute (e.g.,/samlp:Response/saml:Assertion/ds:Signature) and accompanied by a correctly configuredNamespaceContext. This eliminates the risk of wildcard matches that could select an attacker‑injected signature node. -
Namespace‑Sensitive DOM Access – Prefer
getElementsByTagNameNSorselectNodeswith explicit namespace prefixes over their namespace‑agnostic counterparts. Iterate over all returned nodes and verify theirIDattributes before proceeding. -
Secure Validation Flags – Enable library‑provided hardening options such as
org.apache.jcp.xml.dsig.secureValidationfor Apache Santuario or the equivalent in .NET. These flags enforce stricter processing rules (e.g., disallowing detached signatures without explicit reference checks). -
Parser Hardening – Configure the underlying XML parser to disable external entity resolution (XXE protection), limit entity expansion, and enforce a maximum document size.
The authors provide a complete, production‑ready code sample that incorporates all of the above measures. The sample demonstrates: (a) initializing a secure DocumentBuilderFactory; (b) parsing the SAML response and extracting the Assertion ID; (c) locating the signature with an absolute, namespace‑aware XPath; (d) creating a DOMValidateContext with the public key and the signature node; (e) invoking XMLSignature.validate(); and (f) performing an explicit check that the Reference URI equals the extracted Assertion ID. Compared with the insecure examples found in official documentation, the secure version adds roughly 30 % more lines of code but eliminates every known wrapping‑attack vector.
Beyond the technical fixes, the paper discusses the broader ecosystem impact. The authors submitted pull‑requests to the Apache Santuario and OpenSAML repositories, updating both the API documentation and the bundled example applications to reflect the new best practices. They also released a short security‑training video and a checklist for developers integrating SAML into their services. The paper argues that while library authors can provide safer defaults, the ultimate responsibility lies with implementers who must understand the subtleties of XML signature processing.
In conclusion, the paper delivers a thorough forensic analysis of why many SAML consumer implementations are vulnerable to XML Signature Wrapping, pinpoints the exact mis‑uses of DOM and XPath APIs that lead to those vulnerabilities, and offers a concrete, reproducible set of mitigation steps. By following the prescribed guidelines, developers can transform SAML validation from a “black‑box” call into a transparent, auditable process that reliably protects against one of the most dangerous classes of attacks in federated identity systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment