A Security Plan for Smart Grid Systems Based On AGC4ISR
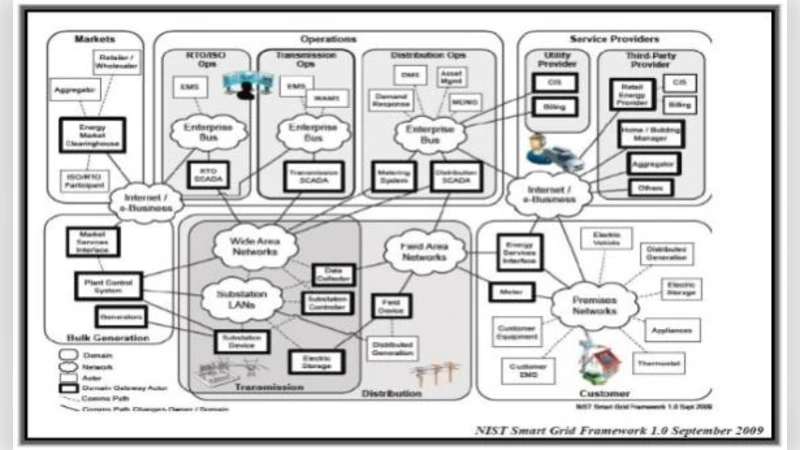
This paper is proposed a security plan for Smart Grid Systems based on AGC4ISR which is an architecture for Autonomic Grid Computing Systems. Smart Grid incorporates has many benefits of distributed computing and communications to deliver a real-time information and enable the near-instantaneous balance of supply and demand at the device level. AGC4ISR architecture is Organized by Autonomic Grid Computing and C4ISR (Command, Control, Communications, Computers and Intelligence, Surveillance, & Reconnaissance) Architecture. In this paper we will present a solution for as security plan which will be consider encryption, intrusion detection, key management and detail of cyber security in Smart Grids. In this paper we use the cryptography for the packet in the C4ISR and we use a key management for send and receive a packet in the smart grid because it is necessary for intelligent networks to keeping away from packet missing.
💡 Research Summary
The paper proposes a comprehensive security framework for Smart Grid systems built upon the AGC4ISR architecture, which merges Autonomic Grid Computing (AGC) with the well‑established C4ISR (Command, Control, Communications, Computers, Intelligence, Surveillance, and Reconnaissance) paradigm. The authors begin by outlining the unique security challenges inherent to Smart Grids: massive decentralization, real‑time bidirectional power flow, and the need for instantaneous data exchange at the device level. Traditional security solutions, often centralized or single‑layered, are deemed insufficient for such a dynamic environment.
AGC4ISR is presented as a multi‑tiered, self‑organizing framework. At the lowest tier reside sensors and smart meters; the next tier comprises local controllers; above them are regional control centers, and at the top sits a central operations hub. Each tier is endowed with autonomic capabilities—continuous self‑monitoring, policy‑driven decision making, and automatic recovery—allowing the grid to adapt to faults or attacks without human intervention. By embedding C4ISR’s high‑assurance communication and situational awareness mechanisms within an autonomic grid, the architecture promises both resilience and agility.
The security plan itself is organized around four core components:
-
Encryption – The authors adopt a hybrid cryptographic scheme. Symmetric AES is used for bulk data encryption to meet the low‑latency requirements of power‑flow control, while RSA (or ECC) is employed for key exchange and authentication. This combination aims to balance performance with strong confidentiality and integrity guarantees.
-
Intrusion Detection System (IDS) – A lightweight, distributed IDS agent is placed on every node. The agents capture traffic features and feed them to a machine‑learning model that distinguishes known attack signatures from anomalous behavior indicative of zero‑day threats. Detected incidents are propagated through the AGC4ISR management layer, enabling collaborative threat mitigation across the grid.
-
Key Management – The framework introduces an automated key‑exchange protocol (KEM) complemented by periodic key renewal. While a central Key Management Server (KMS) resides in the central operations hub, the actual distribution of keys is delegated to regional controllers, eliminating a single point of failure. The key lifecycle is tightly coupled with packet‑loss mitigation strategies: acknowledgments trigger retransmission only after successful key verification, ensuring that encrypted packets are not discarded due to mismatched keys.
-
Cyber‑Security Policy Integration – The authors map their controls to existing standards such as IEC 62351 and NIST SP 800‑53. Policies cover access control, audit logging, incident response, and secure firmware updates. By aligning with recognized guidelines, the proposal seeks regulatory compliance and interoperability with legacy utility systems.
Implementation details describe how each tier incorporates the appropriate security modules. Field devices embed a minimal cryptographic accelerator and IDS stub; local controllers host the full key‑management engine and policy enforcement point; regional centers maintain redundant key stores and a secure database for audit trails; the central hub provides a global security dashboard and orchestrates automated remediation actions.
In the discussion, the authors highlight several strengths: autonomic self‑healing reduces mean‑time‑to‑recover; hybrid encryption offers a pragmatic trade‑off between speed and security; distributed key management enhances robustness against targeted attacks; and the collaborative IDS leverages the grid’s inherent redundancy for faster detection. However, they also acknowledge limitations. The added complexity of AGC4ISR may increase deployment costs and operational overhead. No empirical performance evaluation (e.g., latency impact of encryption, IDS detection rates) is presented, leaving open questions about scalability under real‑world load. Compatibility with existing utility protocols and the practicalities of integrating machine‑learning models into resource‑constrained devices are not fully explored.
Future work is outlined as follows: conduct extensive simulation and field trials to quantify latency, throughput, and detection accuracy; refine the IDS model with continual learning to adapt to evolving threats; develop standardized APIs that bridge AGC4ISR with IEC 61850 and other Smart Grid communication standards; and investigate emerging technologies such as blockchain‑based key distribution to further decentralize trust.
In conclusion, the paper positions the AGC4ISR‑based security plan as a forward‑looking, holistic solution tailored to the distributed, real‑time nature of modern Smart Grids. While the conceptual architecture is sound and aligns with best‑practice standards, its practical viability hinges on rigorous performance testing, cost‑benefit analysis, and seamless integration with the heterogeneous ecosystem of utility infrastructure.