Multi-User MIMO Scheduling in the Fourth Generation Cellular Uplink
We consider Multi-User MIMO (MU-MIMO) scheduling in the 3GPP LTE-Advanced (3GPP LTE-A) cellular uplink. The 3GPP LTE-A uplink allows for precoded multi-stream (precoded MIMO) transmission from each scheduled user and also allows flexible multi-user (…
Authors: Narayan Prasad, Honghai Zhang, Hao Zhu
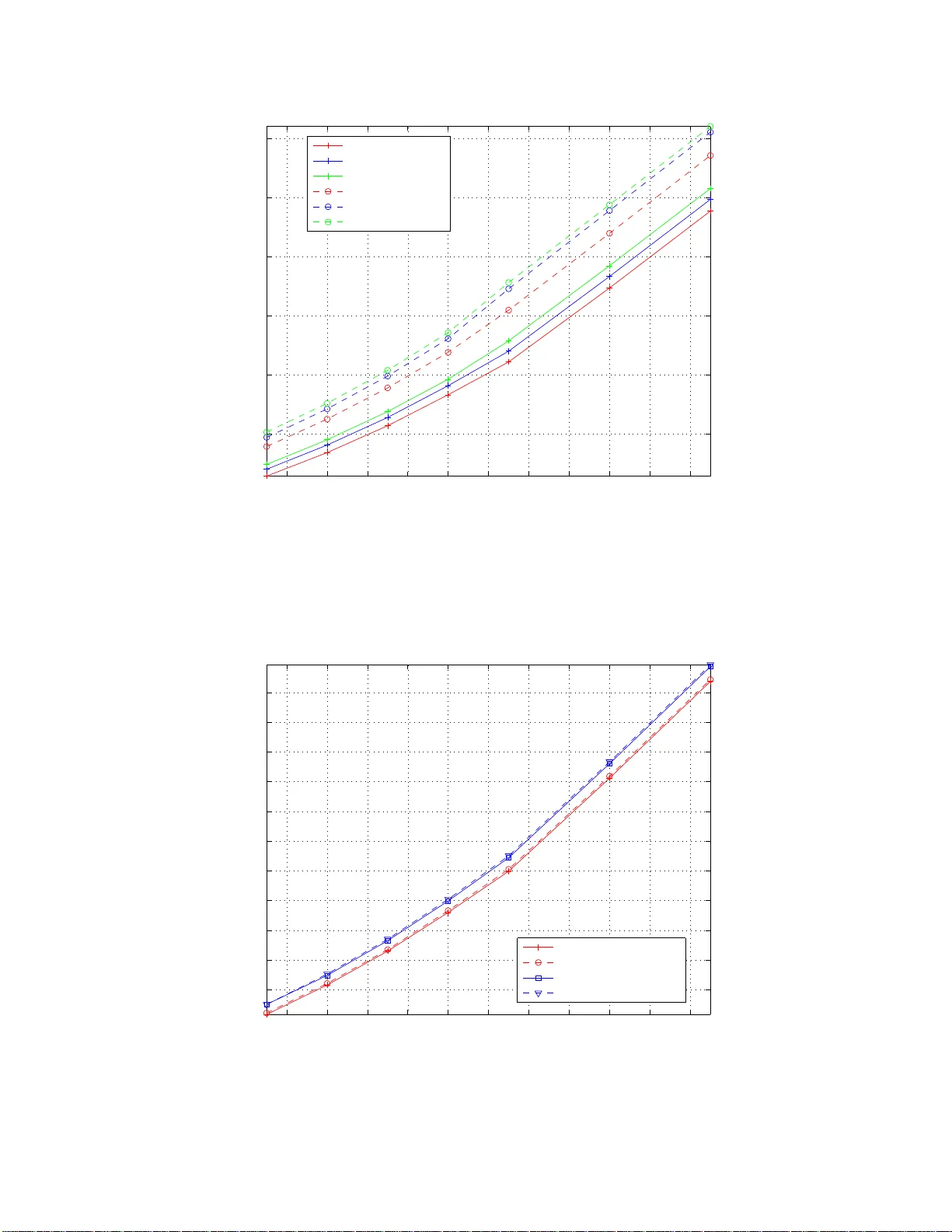
Multi-User MIMO Sc heduling in the F ourth Generation Cellular Uplink Nara yan Prasad Honghai Zhang Hao Zh u Sampath R angara jan ∗ † Abstract W e consider Multi-User MIMO (MU-MIMO) scheduling in the 3GP P L TE-Adv anced (3GPP L TE-A) cellular uplink. The 3GPP L TE-A uplink allo ws for preco ded m ulti-str eam (preco ded MIMO) transmission from each sc heduled user and also allows flexible multi-user (MU) s cheduling wherein multiple users can be assigned the same time-frequency res o urce. How ever, exploiting these features is made challenging b y certain practical constraints that hav e been impos ed in o rder to main tain a lo w signaling o verhead. W e s how that while the scheduling problem in the 3GPP L TE-A cellular uplink is NP-hard, it can b e for m ula ted as the maximizatio n of a submo dular se t function sub ject to one matroid and multiple knaps ack constra int s. W e then prop os e c onstant-factor p o ly nomial-time approximation a lgorithms and demonstrate their super ior per formance via simulations. ∗ Man uscript received May 23, 2012; rev ised No vem b er 6, 20 12 and April 24, 201 3; accepted June 12, 2013. The associate editor coordinating the review of th is paper and approving it for publication was N. Sagias. A part of this paper has been accepted for presentatio n at the I EEE Asilomar Conference on Signals, Systems, and Computers 2013. Cop yright (c) 201 3 IEEE. Personal use of this material is p ermitted. P ermission from I EEE must b e obtained for all other users, including reprinti n g/ republishing this material for advertisi ng or promotional purp oses, creating n ew collectiv e works for resale or redistribution to servers or lists, or reuse of any cop yrighted comp onents of this wo rk in other wor k s. † N. Prasad and S. Ran gara jan are with NEC Labs America, 4 I ndep endence W a y , Princeton, NJ, U SA (e-mail: prasad, sampath@nec-labs.com). N. Prasad is the corresponding author. H. Zhang is with Google Inc. (e- mail: honghaiz@gma il.com). H. Zhu is with the Univerist y of I llinois at Urbana Champaign ( e-mail: zhuh@umn.edu). 1 1 In tro du ction The 3GPP L TE-A based cellular n et w ork [1] toget h er with the IEEE 802.16m based cellular net w ork are the only tw o cellular n etw orks classified as 4G cellular net works by the international telecomm unications union. Some k ey attributes that a 4G u plink m ust p ossess are the ability to supp ort a p eak sp ectral efficiency of 15 b ps/Hz a n d a cell a v erage sp ectral e fficiency of 2 bps/Hz, u ltra-lo w lat ency and bandwidths of up to 100MHz . T o ac hiev e these ambiti ous sp ecificat ions, the 3GPP L TE-A u plink is b ased on a mo difi ed form of the orthogonal frequency-division m u ltiplexing based m ultiple-access (OFDMA) [1]. In addition, it allo ws preco ded multi-st r eam (preco ded MIMO) transmission fr om eac h sc hedu led user as we ll as flexible multi- user scheduling. Notice that while OFDMA itself allo ws for significan t sp ectral efficiency gains via channel dep end en t frequency domain sc heduling, m ulti-user m ulti-stream comm unication promises substan tially higher degrees of freedom [2]. Our fo cus in this pap er is on the 3GPP L TE-A uplink (UL) and in particular on MU MIMO sc hedu ling for the L TE-A UL. Pr edominan tly , almost all of the 4G cellular systems that will b e deplo ye d will b e based on the 3GPP L TE-A standard [1]. This stand ard is an enhancement of the basic L TE standard which is referr ed to in the indu stry as Relea se 8 and indeed d ep lo ymen ts conforming to Release 8 are already under wa y . Th e scheduling in the L TE-A UL is done in the frequency domain where in eac h scheduling in terv al the sc h ed uler assigns one or more resource blo c ks (RBs) to eac h sc heduled us er. Each RB conta ins a pre-defined set of consecutiv e sub carriers and consecutiv e OFDM symbols and is the minim um allo cation unit. The goal of this work is to design practical uplink MU-MIMO resource allocation algorithms for the L TE- A cel lu lar net work, where th e term r esource refers to RBs as w ell as preco ding matrices. In p articular, w e consider the design of resource allo cation algo rithm s via weig hted sum r ate u tilit y maximization that account for fin ite user queues (buffers) and finite pr eco d ing co deb ooks. In addition, the designed algorithms comply with all the m ain practica l constrain ts on the assignmen t of RBs and preco ders to the sc hedu led users. W e first capture all the ke y definitions used in this pap er in App endix A. Then, we list ou r main con tributions in the follo wing: 1 ) W e first assume th at users can emplo y ideal Gaussian co d es and that the base-station (BS) can employ an optimal receiv er. W e then enf orce user rates to lie in a fu ndament al ac hiev able rate r egion of the multiple access c h an n el which is a p olymatroid and sho w th at the r esulting resource allocation problem is NP-hard. W e pro v e that th e resource allocation p r oblem can h ow ev er b e form ulated as the maximizatio n of a monotonic sub-mo d u lar set fu nction sub ject to on e matroid and m ultiple kn apsac k constrain ts, and can b e solve d using a recen tly disco v ered p olynomial time r andomized constan t-factor appro ximation algorithm [3]. W e also adapt 2 a simpler deterministic greedy algorithm and sho w th at it yields a constant- factor appro ximation for scenarios of in terest. 2 ) W e then consider scenarios wh ere users employ co des constructed o v er finite alphab e ts. In this case the m utual information terms needed to s p ecify an ac hiev able rate region do not hav e closed form expressions. On the other hand the ac hiev ab le rate regio n obtained for Gaussian alphab ets can b e a loose outer b ound. Consequent ly , we obtain a tigh ter outer b ou n d whic h is also a p olymatroid. As a result all algorithms dev elop ed for Gauss ian alphab ets can b e reused after simple mo d ifications. Finally , w e demonstrate th e sup er ior p erformance of our prop osed algorithms via simulatio ns using a realistic channel mo d el. An inte r esting corollary that follo ws from our results is th at a p opu lar transmit ant enn a selection problem in p oi nt-to- p oin t MIMO comm un ications can b e p osed as a sub-mo d ular maximizat ion p roblem that is NP- hard but can b e app ro ximately solv ed (with at-least half optimalit y) by a simple greedy alg orithm. 1.1 Related W ork Resource allocation o ver OFDMA netw orks has b ee n widely studied [4 – 6] w ith a large fraction of the problems that hav e so f ar b een considered b eing single-user (SU) sc hedulin g problems, whic h attempt to maximize a system utilit y un der the constrain t that sc hedu led users can only b e assigned non-o ve rlapp ing sub carriers. These pr ob lems h a v e b een f orm ulated as c ontinuous optimization pr oblems , and since they are in general n on- linear and non-con vex, many approac hes including those based on game theory [5 ] and dual decomp osition [4] ha ve b een deve lop ed. MU sc hedu ling in th e uplink has b een considered in [7] whic h inv estigates the tradeoff b et ween fairness and efficiency , and from an in formation theoretic p ers p ectiv e in [8]. In particular, [8] deriv es a formulatio n of the capacit y r egion of a discrete memoryless multiple access channel (MA C) inv olving only one non -conv ex constraint and th en prop ose s metho ds to compute inner and outer b ounds. A MIMO MA C with finite rate feedbac k is consid ered in [9] and a join t user selection, b eamforming and quantiza tion strategy is p rop osed and compr ehensiv ely analyzed. Recen t w orks hav e fo cused on emerging cellular standards and h a v e form ulated the r esp ectiv e r esource allocation problems as constrained in teger p rograms. A promin en t example is [6] which consider the design of do wnlink SU-MIMO sc hedu lers for L TE systems. In this con text, w e note that d o wnlink frequency domain sc hedulin g in L TE systems using quan tized c hannel q u alit y feedbac k has b e en analyzed in [10]. On the other hand, corresp onding r esource allocation problems for the cellular uplink ha ve b een examined in [11 –14]. In particular, [11, 1 2 , 14] sho w that the single-user UL L TE (Release 8) sc h ed uling p roblem is NP-hard and pro vide constan t-factor approxi mation algorithms, whereas [13] consid ers SU-MIMO L TE-A scheduling. The algorithms in [11–14] cannot incorp orat e MU scheduling and also cannot incorp orate knapsac k constrain ts. 3 MU scheduling for the L TE (Release 8) UL is considered in detail in [15]. How ev er, we emphasize that certain additional constraint s imp osed on L TE (Release 8) UL MU sc h eduling essenti ally ensu re th at algorithms optimized for L T E MU-sc heduling are unsu itable f or L TE-A MU-sc hedu ling wh ereas algorithms optimized f or L TE-A MU-sc heduling (as presen ted in this pap er) are not app licable to L TE MU-sc hedulin g. 2 MU-MIMO Scheduling in the L TE-A UL Consider a single-cell uplink with K user s and one base-station (BS) whic h is assum ed to ha v e N r ≥ 1 receiv e an tennas. S upp ose that user k has N t ≥ 1 transmit ant enn as and its p ow er bu dget is P k . W e let N denote the total n umb er of a v aila b le resource b lo c ks (RBs). F or conv enience and without loss of generalit y , in the follo wing analysis w e assume eac h RB to hav e un it size. Th en, let H ( n ) k denote the N r × N t c hannel matrix seen b y the BS from user k on RB n , w h ic h we assume is known p erfectly to the BS . W e let e = ( u, c , W ) denote a 3-tuple, wher e 1 ≤ u ≤ K d enotes a us er , W ∈ W (suc h th at tr( W † W ) = 1) denotes a pr ecod er from a finite cod eb o ok W an d c ∈ C denotes a v alid assignment of RBs c hosen from the set C conta inin g all p ossible v alid assignments. In particular, eac h c is an N − length v ector with binary-v alued ( { 0 , 1 } ) entries and we say an RB i b elo ngs to c ( i ∈ c ) if c cont ains a one in its i th p osition, i.e., c ( i ) = 1. Next, we let E = { e = ( u, c , W ) : 1 ≤ u ≤ K, c ∈ C , W ∈ W } denote the ground set of all p ossible suc h 3-tuples. F or an y suc h 3-tuple w e adopt the conv en tion that e = ( u, c , W ) ⇒ c e = c , W e = W , u e = u, H ( n ) e = H ( n ) u ∀ n. Supp ose no w that a subs et A ⊆ E is selected or s cheduled by the b ase-statio n . Then on eac h RB n the receiv ed signal v ector at the BS can b e mo deled as the output of a MIMO multiple access c h an n el, as y ( n ) = X e ∈A c e ( n ) H ( n ) e W ( n ) e x ( n ) e + v ( n ) , (1) where v ( n ) ∼ C N ( 0 , I ) is the additiv e Gaussian noise and x ( n ) e is th e inp ut vect or corresp onding to 3-tuple e , i.e., the inp ut v ector transmitted b y user u e on RB n . W e consider the problem of scheduling users in the frequency domain in a giv en sc hedu ling in terv al. Let α k > 0 , 1 ≤ k ≤ K d enote the p ositiv e w eigh t of th e k th user wh ic h is an input to th e sc hedu ling algorithm and is up date d using the output of the sc heduling algorithm in ev ery scheduling interv al, sa y according to th e prop ortional fairness rule [16]. Letting r k denote th e rate assigned to th e k th user (in bits p er N RBs), w e 4 consider the f ollo wing we ighte d s um rate u tilit y maximization problem, max X 1 ≤ k ≤ K α k r k , (2) where the maximization is o ve r the assignmen t of RBs and preco ders to the users sub ject to: Deco dabilit y constrain t: The rates assigned to th e scheduled users should b e d eco d able b y the base- station r eceiv er. Notice that unlike SU scheduling, MU s c heduling allo ws for multiple users to b e assigned the same RB. Thus, the rate that can b e ac hiev ed for user k need not b e only a function of the R Bs, p reco ders and p o wers assigned to the k th user but can also dep end on those assigned to the other u s ers. One preco der and one p ow er lev el p er user: Each sc hedu led user can b e assigned any one preco ding matrix fr om a fi nite co deb ook of suc h matrices W . In addition, eac h sc heduled us er can transmit w ith only one p o wer leve l (or p ow er s p ectral density (PSD)) on all its assigned RBs. T his PSD is implicitly determined b y the num b er of RBs assigned to that user, i.e., the user divides its total p o w er equally among all its assigned RBs. T he motiv atio n b ehin d these tw o constrain ts is that wh ile they significan tly decrease the signaling o v erh ead inv olv ed in con ve yin g the scheduling d ecisions to the users , they do not r esult in significant p erformance d egradation. Th is is b ecause the u plink channel b etw een eac h user and the base station is t ypically highly correlated so that eac h user’s set of preferred spatial directions can b e regarded as b eing appro ximately frequency non-selectiv e. Consequently , these preferr ed s p atial directions can b e reasonably w ell qu antized using a single pr eco d ing matrix. Similarly , the multi- u ser div ersity effect ensures that eac h user is sc heduled on the set of RBs on which it has relativ ely goo d c hannels. A constan t p o wer allocation o ver suc h go o d c h annels results in a negligible loss [17]. A t most t wo c hunks p er- user: T he set of RBs assigned to eac h sc hed uled user should form at-most t wo m u tually non-con tiguous c hunks, wh er e eac h c h un k is a set of con tiguous RBs. W e note here that in the L TE (Release 8) UL eac h sc h ed uled user is assigned only one c hunk of con tiguous RBs [18]. Allo wing only one c hunk of conti guous RBs to b e assigned, together with the DFT spreading op eration that eac h sc hedu led u ser m ust emplo y , ensur e a low transmit p eak-to-a v erage-p o we r ratio (P APR). In the L TE-A UL eac h u ser must emplo y the DFT spreading but can b e assigned up-to tw o c hunks. T his r elaxatio n in L TE-A is essentially a compromise b e tw een the need to provide more scheduling flexibilit y and the need to k eep P APR un d er c hec k [1]. A feasible RB allocation and co-sc hed u ling of users in L TE-A m ulti-user u plink is depicted in Fig 1. Notice that eac h sc hed uled us er is assigned at-most t w o m utually n on-con tiguous c h un ks. Also note th at an y t wo scheduled users can partially o v erlap, i.e., an y subs et of th e RBs assigned to a user can also b e assigned to another user. This is in cont r ast to the L TE UL in whic h any t wo sc hedu led users m ust either not ov erlap 5 or must completely o v erlap [18]. Finite buffers W e let Q k denote the size in bits of the qu eue (bu ffer) asso ciated w ith th e k th user. Thus, the rate r k assigned to user k cannot exceed Q k . In addition to the aforemen tioned constraints the follo wing constraint s can also b e imp o sed . Con trol c hannel o verhead and in terference limit constrain ts: Eve ry user th at is sc hedu led must b e informed ab out its trans mission rate and th e set of RBs on whic h it m ust transmit, along with the preco der it should employ . This information is sent on the DL con trol channel of limited capaci ty whic h in turn imp oses constrain ts that the s et of sc hed u led users must resp ect. These constraint s are fu rther discussed in [15]. On the other hand, th e scheduling decisions that are made sh ould also comply with in terference limit constraints whic h ensure that the interference caused to other cells does not exceed certai n sp e cified margins. W e will form ulate the optimization problem in (2) as the maximization of a monotonic submo dular set function subje ct to one matr oid and multiple knapsack c onstr aints . T o w ards this en d , we fi rst recall the k ey definitions fr om App endix A and then en f orce that the non-zero en tries in eac h c ∈ C form at-most t wo non-con tiguous c h u n ks. In addition, for eac h 3-tuple e = ( u, c , W ) ∈ E we let p e denote the asso ciated p o wer lev el (PSD). This PSD can b e compu ted as P u size( c ) , where size( c ) den otes the n umb er of ones (num b er of RBs) in c . F u rther, let α e , Q e denote the weig ht and bu ffer (queue) size asso ciated w ith the 3-tuple e , resp ectiv ely and let r e denote the rate asso ciated with the 3-tuple e . W e will use th e p hrase sele cting a 3-tuple e to imply that the user u e is sche dule d to tr ansmit on the RBs indic ate d in c e with PSD p e and pr e c o der W e . Thus, the c onstr aints of one pr e c o der and one p ower leve l p er user along with at most two chunks p e r-user c an b e imp ose d by al lowing the sche duler to sele ct any subset of 3-tuples U ⊆ E such that P e ∈U 1 { u e = u } ≤ 1 for e ach u ∈ { 1 , · · · , K } , wher e 1 { . } denotes the i ndic ator function. Accordingly , w e d efine a family of subs ets of E , denoted by I , as I = U ⊆ E : X e ∈U 1 { u e = u } ≤ 1 , ∀ 1 ≤ u ≤ K . (3) W e recall the mo del in (1 ) and next consider th e decod abilit y constraint after first assuming that eac h user can emp lo y ideal Gauss ian cod es (i.e., cod es for wh ic h the coded mo du lated sy mb ols can b e r egarded as i.i.d. Gaussian) and that the BS can emp lo y an optimal receiv er. Subsequen tly , we will consider fi nite input alphab ets. Recall that in DFT-Spread-OFDMA eac h u s er linearly transf orms its cod ew ord us ing a DFT matrix in ord er to reduce the P APR. Note, ho we ver, that u nder the assumption of ideal Gaussian co des and optimal receiv er, the DFT spr eading op eration p erf ormed b y eac h user can b e ignored. Accordingly , w e d efine 6 a set f u nction f : 2 E → I R + as f ( U ) = N X n =1 log I + X e ∈U p e c e ( n ) H ( n ) e W e ( H ( n ) e W e ) † , ∀ U ⊆ E . (4) It can b e v erified that f ( . ) d efined in (4) is a submo du lar set fun ction, i.e., it satisfies f ( A ∪ { e } ) − f ( A ) ≥ f ( B ∪ { e } ) − f ( B ) , for all A ⊆ B ⊆ E and e ∈ E \ B . F urther sin ce it is monotonic (i.e. , f ( A ) ≤ f ( B ) , ∀ A ⊆ B ) and normalized f ( φ ) = 0, where φ d enotes the emp t y set, w e can assert that f ( . ) is a r ank fun ction. Consequently , for eac h U ⊆ E , the region P ( U , f ) = r = [ r e ] e ∈U ∈ I R |U | + : X e ∈A r e ≤ f ( A ) , ∀ A ⊆ U , (5) is a p o lymatroid [19]. Note that f or eac h U ⊆ E , P ( U , f ) is the fu ndament al ac h iev able r ate region of a m ultiple access c hannel so that eac h rate-tuple r U = [ r e ] e ∈U ∈ P ( U , f ) is ac hiev able [20]. Thus, we c an imp ose de c o dability c onst r aints by imp osing that the assigne d r ate- tu ple satisfy r U ∈ P ( U , f ) for any sele cte d subset U ⊆ E . Next, in order to imp ose buffer (queue) constr aints, w e define a b o x B ( U ) = { r = [ r e ] e ∈U ∈ I R |U | + : 0 ≤ r e ≤ Q e , ∀ e ∈ U } , ∀ U ⊆ E . (6) Thus, for a (tentative) choic e U , we c an satisfy b oth de c o dability and buffer c onstr aints by assigning only r ate-tu ples that lie in the r e gion P ( U , f ) ∩ B ( U ). C learly among all such rate-t u ples we are intereste d in the one that maximizes the wei ghted su m rate. Hence, without loss of optimalit y with r esp ect to (2), with eac h U ⊆ E w e can asso ciate a rate-tuple in P ( U , f ) ∩ B ( U ) that maximizes the we ighted sum rate. Accordingly , w e define the follo wing set fun ction that determines the r ew ard obtained up on s electing an y subset of E . W e define the set fun ction h : 2 E → I R + as h ( U ) = max r =[ r e ] e ∈U r ∈ P ( U , f ) ∩ B ( U ) X e ∈U α e r e , ∀ U ⊆ E . (7) Lev eraging the argum en ts made in [15], we can repr esen t the control channel ov erhead constraint s as 7 column-sparse knapsac k constrain ts such that a subset U is feasible if and only if A C x U ≤ b , (8) where A C ∈ { 0 , 1 } L ×|E | is a bin ary v alued matrix for some in teger L ≥ 1 and b is an L length v ector, r eferred to as the con trol c h an n el bud get ve ctor, whose ent r ies are p ositiv e integ ers. x U ∈ { 0 , 1 } |E |× 1 is a v ector with an entry equal to one in eac h p osition corresp onding to eac h 3-tuple e ∈ U and zero elsewh ere. Notice that the co efficien ts in A C are not norm alized and h ence A C and b together enforce the con trol c hannel o v erhead constrain ts. Moreov er, the total num b er of non-zero co efficient s in any column of A C is no more th an an in teger ∆ ≥ 1 whic h denotes the column sp arsit y lev el such that ∆ << L . Finally , let us consider the inte r f erence limit constrain ts. Supp ose that the cell of in terest is sur r ounded b y M adjacent cells (or sectors). Let e m b e an N − length v ector of b inary v alued entrie s wh ich con v eys the RBs such that the total interference caused to th e m th base station o v er all the RBs indicated in e m should b e n o greater than a sp eci fi ed up p er b ound. In particular, let R u,m b e the (wide-band ) correlation matrix of the c hann el seen at the m th base station from the u th user in the cell of in terest. 1 Then the total in terference caused to the m th base station o ve r all the RBs indicated in e m , u p on selecting 3-tuples in any set U ⊆ E is equal to X e ∈U p e tr( W † e R u e ,m W e )( c T e e m ) | {z } β e ,m . (9) Then, we are allo wed to select any set of 3-tuples U ⊆ E suc h that the resu lting total in terference imp osed on the m th base station o ve r all the RBs indicated in e m is no greater than a sp ecified u pp e r b ound γ ( m ) , i.e., suc h that 1 γ ( m ) P e ∈U β e ,m ≤ 1 , ∀ 1 ≤ m ≤ M . Thus, al l the interfer enc e limit c onstr aints c an b e r epr esente d as M generic knapsack c onstr aints g i ven by A I x U ≤ 1 M , (10) wher e A I ∈ [0 , 1] M ×|E | and 1 M is a M length ve ctor of ones. Summarizing the aforementio n ed results, w e ha ve f orm ulated (2) as the follo wing optimization problem: max U ⊆E { h ( U ) } s . t . 1 W e assume that the BS in the cell of in terest also knows this correlatio n matrix by exc h an ging appropriate messag es with BS m on the backhaul. 8 U ∈ I ; A I x U ≤ 1 M ; A C x U ≤ b . (11) In (11) we regard M , ∆ as constan ts that are arbitrarily fixed, whereas L can scale p olynomially in th e cardinalit y of the ground set |E | . Th en , f or a giv en n umb er of users K , n umb er of RBs N and the co deb o ok cardinalit y |W | (whic h together fix |E | ), an instance (or input) of the problem in (1 1 ) consists of a set of p osit ive user w eigh ts { α u } and queue sizes { Q u } , p er-user p er-RB c hann el matrices { H ( n ) u } : 1 ≤ u ≤ K , 1 ≤ n ≤ N , a co deb o o k W (of cardin ality |W | ) along with a column sparse matrix A C ∈ { 0 , 1 } L ×|E | , bud get ve ctor b and any matrix A I ∈ [0 , 1] M ×|E | . The outpu t is a subset ˆ U ⊆ E along with a r ate-tuple r ˆ U . Note that |E | is O ( K |W | N 4 ). W e first introd uce the follo wing t w o r esults that will b e inv ok ed later. Lemma 1. The family of subsets I define d in (3) is an indep endenc e family and ( E , I ) is a p artition matr oid. Pr o of. Let E ( k ) denote the set of all e ∈ E : u e = k and n otice that E ( k ) ∩ E ( j ) = φ, ∀ k 6 = j . Th en , n ote th at I can also b e defined as A ∈ I ⇔ |A ∩ E ( k ) | ≤ 1 ∀ 1 ≤ k ≤ K , whic h is the definition of a partition matroid (cf. App endix A). The pro of of the follo wing lemma follo ws from basic definitions [19] and is skipp ed for b r evit y . Lemma 2. The r e gion P ( U , f ) ∩ B ( U ) , ∀ U ⊆ E is a p olymatr oid c har acterize d by the r ank function f ′ : 2 E → I R + wher e f ′ ( U ) = min R⊆U f ( U \ R ) + X e ∈R Q e , ∀ U ⊆ E . (12) W e are n o w ready to offer our main result. L et us assu me that computing h ( U ) for any U ⊆ E incurs a unit cost (or equiv alen tly is give n by an oracle in a single query). W e w ill show that ev en under this assum ption the problem in (11) is NP h ard. Before pro ceeding it is u seful to recall the definitions giv en in App endix A. Theorem 1. The optimization pr oblem in (11) is NP har d and is the maximization of a monotonic sub- mo dular set function subj e ct to one matr oid and multiple k napsack c onstr aints. Pr o of. Pr o v ed in App endix B. Theorem 2. Ther e is a r and omize d algorithm whose c omplexity sc ales p olynomial ly in |E | and which yields a e − 1 e 2 ( M +∆+1)+ o ( M ) appr oximation to (11). 9 Pr o of. T he k ey observ atio n is that the partition matroid constr aint in (11) can b e expressed as K knapsac k constrain ts (one for eac h user). Let A P denote the resu lting K × |E | matrix d etermined by these constrain ts, whose k th ro w corresp ond s to the k th user. Note that this row has ones in eac h p ositio n for wh ic h the corresp ondin g 3-tuple e satisfies u e = k and zeros elsewhere. T ogether these K knaps ac k constrain ts are column-sparse knapsack constraints wherein in eac h column a non-zero entry app ears only once. Thus, the total K + L + M knapsac k constrain ts are column-sparse constraints in wh ic h eac h 3-tuple can app ea r in at-most M + ∆ + 1 constrain ts so that eac h column can ha ve at-most M + ∆ + 1 non-zero co efficien ts. With this u nderstandin g, w e can in vo ke the randomized algorithm from [3] wh ic h is app licable to the maximization of an y monotonic su bmo du lar set function sub ject to column-spars e knapsac k constraints and obtain th e guaran tee claimed in the th eorem. Notice th at since an y monotonic su bmo du lar set fun ction is also monotonic and sub -add itiv e, w e can infer the follo wing result from Theorem 1. Lemma 3. The function h ( . ) define d in (7) is sub-additive, i.e., h ( U ) ≤ h ( U 1 ) + h ( U 2 ) , ∀ U 1 , U 2 , U : U 1 ∪ U 2 = U . (13) Practical implementati on migh t demand a simp ler and combinatoria l (deterministic) algo r ith m . Unf ortu- nately , as r emark ed in [21], it is difficult to d esign com binatorial (deterministic) algorithms that can com bin e b oth matroid and knaps ack constrain ts. Neve rth eless in Algorithm I we sp ecialize a w ell kno wn greedy algo- rithm to our problem of interest (11). I n this algorithm w e maint ain a set S . In eac h iteratio n of Algorithm I w e add a 3-tuple (from the set of u nselected 3-tuples) to S that yields the largest incremen tal gain among all feasible 3-tuples that ha v e not ye t b een selected and where the offered incremen tal gai n is strictly p ositiv e. Moreo v er a 3-tuple is deemed feasible in an iteration if it alo n g w ith the already selected 3-tuples, satisfies all the constrain ts in (11). Th e pro ce ss con tinues u n til either no feasible 3-tuple offers a p ositiv e increment al gain or if there are no feasible 3-tuples left. W e no w pro ceed to analyze the p erformance of Algorithm I and fir st introd uce the follo win g scenario that is of p articular interest. W e emph asize that this scenario is not requ ir ed to implement Algorithm I but rather it is in tro duced since it has a fairly wide applicabilit y and it allo ws for a b et ter appro ximation gu arantee. T o w ards this end, w e offer a simple su fficien t condition for a kn apsac k constrain t to b e matroid constrain t. Lemma 4. The i th knapsack c onstr aint is a matr oid c onstr aint if al l its strictly p ositive c o efficients ar e identic al,i.e., 1 { A i,j > 0 } = 1 { A i,k > 0 } ⇒ A i,j = A i,k , ∀ j, k . 10 W e note that nece ssary and sufficien t conditions for a knapsac k constrain t (with rati onal v alued c o e fficients) to b e a matroid constrain t ha v e b een derive d in [22] and an efficien t algorithm to v erify suc h conditions is giv en in [23]. Th en consider the scenario for wh ic h the follo wing t wo conditions are met. Condition 1. The c ontr ol channel overhe ad c onstr aints ar e mo dele d using L knapsack c onstr aints, wher e L now r epr esents the numb er of ortho gonal (non-overlapp ing) c ontr ol channel r e gions. Each user (and henc e al l its c orr e sp onding 3-tuples) i s asso ci ate d with only one of these r e gions. F urther, e ach c onstr aint c orr esp onds to a c ar dinality c onstr aint which enfor c es that no mor e than a give n numb er of 3-tuples among those asso ciate d with the c orr esp onding c ontr ol r e gion c an b e sche dule d. Notic e then that these L c ontr ol channel overhe ad c onstr aints ar e sp arse with ∆ = 1 and sinc e they satisfy L emma 4 they ar e matr oid c onstr aints as wel l. W e will sho w in the sequel th at wh en Condition 1 is met, th e intersecti on of the L con trol c han n el ov erhead constrain ts is itself a m atroid constraint Condition 2. Al l the M interfer enc e limit knapsack c onstr aints ar e matr oid c onstr aints. W e note th at a simp listic m o deling of the in terference limit constrain ts can ensur e th at Condition 2 is met. F or in s tance, considering the m th in terference limit knapsac k constrain t (corresp onding to th e adj acen t BS m ) and recalling (9), eac h 3-tuple e ∈ E can b e assigned to one of t w o sets us in g an appropr iate threshold δ m : one set compr ising those which cause high int erf er en ce { β e ,m > δ m } and the other one comprising th ose whic h do not. Then a cardinalit y constrain t is imp osed only on the set of 3-tuples that cause high in terference, i.e., the co efficients (in the m th in terference limit knapsac k constrain t) of all 3-tuples b elonging to the fir s t set are set to 1 /γ ( m ) and the r emaining ones are set to zero wh ile th e upp er b ound γ ( m ) is set to b e the cardinalit y b ound . Then, it can b e seen that all resulting interference limit constraints (up on considering all the M adjacen t BSs) satisfy Lemma 4 and hence are matroid constraints. The follo wing result pro vides the w orst-case guaran tee offered by Algorithm I. Theorem 3. The c omplexity of Algorithm I is O ( K 2 N 4 |W | ) and it yields a 1 K appr oximation to (11). F urther, if Conditions 1 and 2 ar e satisfie d then Algo rithm I yields a c onstant-factor 1 2+ M appr oximation to (11). Pr o of. Pr o v ed in App endix C. Remark 1. L et us r e c onsider the submo dular maximization pr oblem define d in (31). This pr oblem in fact also r epr esents a p op ular tr ansmit antenna sele ction pr oblem in p oint-to-p oint M IMO c ommunic ations [ 24 ] . Inde e d, K c an b e r e gar de d as the total numb er of available tr ansm it antennas while C then denotes the numb er of tr ansmit antennas that have to b e sele cte d and a normalizat ion factor q ρ C , wher e ρ denotes the 11 SNR, c an b e absorb e d into the matrix H . Then, our r esult in The or em 1 pr oves that this tr ansmit antenna sele ction pr oblem is NP-har d. Next, the gr e e dy Algor ithm I when sp e cialize d to this pr oblem r e duc es to a known incr emental suc c essive tr ansmit antenna sele ction algorithm [24] but for which no appr oximation guar ante es wer e as yet known. N otic e that this pr oblem satisfies Conditions 1 and 2 sinc e the c onstr aint in (31) c an b e ac c ommo date d u si ng just one c ontr ol channel knapsack c onstr aint that has e qual c o efficients for al l users. Then, invoking the r esult in The or em 3 (with M = 0 ) we c an infer that the gr e e dy A lgorithm I (or e quivalently the inc r emental suc c essive tr ansmit antenna se le ction algorith m) offers a 1 / 2 appr oximation to the tr ansmit antenna sele ction pr oblem. An analo gous observation for the r e c eive antenna sele ction pr oblem was made r e c ently and indep endently in [25]. In addition, [25] c onsiders a differ ent ve rsion of the tr ansmit antenna sele ction pr oblem in which the numb er of antennas to b e sele cte d, C , is not given as an input (bu t inste ad is an output) and classifies it as an op en pr oblem sinc e it is not e quivalent to a submo dular maximization pr oblem. We note her e that even for that version, we c an obtain an appr oximation algor ithm by se quential ly running the gr e e dy Algorithm K times, initialize d with inputs C = 1 , · · · , K r esp e ctively, and picking the over al l b est among the K outputs. It is r e ad ily se en that such an algorithm wil l also yi e ld a 1 / 2 appr oxima tion sinc e the output of e ach run is within 1 / 2 of its r esp e ctive optima. Remark 2. R e c al l that we have assume d that the BS employs an ide al r e c eiver, which i n pr actic e c an b e closely appr o ache d by iter ative T u rb o r e c eivers. However, when e ach user’s queue is of i nfinite size (a.k.a infinitely b acklo gge d c ase), the assigne d r ate-tuple is a c orner-p oint of the p olymatr oid in (5) (define d for the sele cte d subset) and thus c an b e achieve d usi ng a simple MM SE-SIC r e c eiver [26]. Notice that so far we hav e assumed that computing h ( U ) for any U ⊆ E incur s a unit cost. W e can in deed sho w that Algo r ith m I has p olynomial complexit y un d er a stricter notion th at computing f ( U ) (in s tead of h ( U )) for any U ⊆ E in curs a unit cost. 2 T o sho w this, it su ffices to p ro ve that h ( U ) can b e determined with a complexit y p ol yn omial in |U | . A k ey observ ation to w ard s this end is that for an y U ⊆ E , f ′ ( U ) in (12) can b e computed as f ′ ( U ) = X e ∈U Q e + min R⊆U f ( R ) − X e ∈R Q e , ∀ U ⊆ E . (14) Then, since the function f ( R ) − P e ∈R Q e , ∀ R ⊆ E is a submo du lar set function, we can solv e the minimizat ion in (14) using sub m o dular function minimization rou tin es that h a v e a complexit y p olynomial in |U | [27]. Th u s, from (26) we can conclude that h ( U ) can ind eed b e determined with a complexit y p olynomial in |U | . W e no w 2 This assumption results in no loss of generality since the wors t- case cost of computing f ( U ) is O ( N K 3 ). 12 prop ose simple observ ations that can considerably s p eed up Algorithm I. • L azy e v aluations. An imp ortant feature that s p eeds up the greedy algorithm su bstan tially has b ee n disco v ered and exploited in [28, 29]. In p articular, d ue to the submo d ularit y of the ob jec tive function the incremen tal gain offered by a 3-tuple o v er any selected subset of 3-tuples not including it d ecreases monotonically as the selected subset gro ws larger. Thus, at any step in th e algorithm, give n a set of selected 3-tuples S and a 3-tuple e ∈ E \ S for wh ic h h ( S ∪ e ) has b een ev aluated, we do not h a v e to ev aluate h ( S ∪ e ′ ) for another 3-tuple e ′ ∈ E \ S , if w e can assert that h ( S ∪ e ) − h ( S ) ≥ h ( S ′ ∪ e ′ ) − h ( S ′ ) where S ′ ⊆ S denotes the set of selected 3-tuples at a previous s tep. Th is results in no loss of optimalit y with resp ect to th e original greedy algorithm. • Exploiting sub additivity. Sup p ose that at any step of the greedy algorithm w e h a v e a set of selected 3-tuples S . F u rther, let e 1 = ( u, W , c 1 ) and e 2 = ( u, W , c 2 ) b e t w o 3-tuples in E \ S s u c h that c 1 and c 2 comprise of only one c hunk eac h and are m utually non-inte rs ecting. Th en, lett ing e ′ = ( u, W , c 1 + c 2 ), w e see that h ( S ∪ e ′ ) ≤ h ( S ∪ e 1 ∪ e 2 ) ≤ h ( S ∪ e 1 ) + h ( S ∪ e 2 ) (15) where the first inequalit y stems fr om the fact th at h ( S ∪ e ′ ) is mon otonically increasing in the transmit PSD of e ′ and the second inequalit y stems from the monotonicit y and sub additivit y of h ( . ). Thus, w e ha ve that h ( S ∪ e ′ ) ≤ 2 max { h ( S ∪ e 1 ) , h ( S ∪ e 2 ) } . (16) Then if S ∪ e 1 , S ∪ e 2 as well as S ∪ e ′ satisfy all the constraints, we can ev aluate h ( S ∪ e 1 ) , h ( S ∪ e 2 ) and skip ev aluating h ( S ∪ e ′ ). By ad op tin g this pro cedu re o v er all 3-tuples in E \ S , we can ensur e that the 3-tuple selected w ill offer at-least 1 / 2 the gain yielded by the lo cally optimal 3-tuple. Th en , using a w ell kno wn r esult on the greedy algorithm w ith an approximat ely optimal selection at eac h step [30] w e can conclud e that this v ariation of our greedy algorithm will yield an appro ximation guarant ee of 1 / 2 1 / 2+ M +1 when Conditions 1 and 2 are satisfied. Finally , in order to b enc hmark the p erf ormance of Algorithm I we derive t w o u pp er b o u nds. F or con venience, w e only consider the case where there are no knapsac k constraints so that (11) reduces to the maximizatio n of a monotonic sub -mo dular set function sub ject to one matroid constrain t. Then, we supp ose that U opt and ˆ U denote the optimal solution and that returned b y Algorithm I . W e obtain our fir st b ound b y sp ec ializing 13 an upp er b ound f rom [28 ] (see also [29]) wh ic h is applicable to any m on otonic sub-mo d ular set function maximization sub ject to one matroid constrain t, as h ( U opt ) ≤ h ( ˆ U ) + K X k =1 max e ∈E ( k ) \ ˆ U ( h ( ˆ U ∪ e ) − h ( ˆ U )) , (17) where {E ( k ) } hav e b een d efined in the pro of of Lemma 1. F or our second b o u nd w e exhaustiv ely enumerate eac h one of the |W | K p ossible assignment s of p reco ding m atrices to u sers. Th en, f or eac h assignmen t we consider the weig hted sum r ate maximization o ver the up link (2) after relaxing the p er-user p ow er constrain t to one where only a p er-user su m p ow er constrain t has to b e satisfied, i.e., eac h user can b e assigned an y p ow er v alue on an y RB as long as it d o es not exceed its p o we r bud get. T he latt er problem can b e efficien tly solv ed via c onvex optimization [31, 32]. Finally , w e c ho ose the largest weig hted sum r ate v alue across all assignmen ts as the up p er b ound. 3 Practical M o du lation and Co ding Sc hemes In the L TE-A up link a scheduled user can b e assigned one out of three mo d ulations (4 , 16 & 64 QAM) and an outer T urb o-code whose co ding rate is one out of s everal a v ailable choi ces. S in ce the a v ailable outer codes are p ow erful and since the BS can emplo y near-optimal receiv ers (suc h as T urb o SIC) a r easonable c hoice for the achiev able rate region is the follo wing. Let S e denote the constella tion (with unit av erage energy and cardinalit y S e ) asso ciated with 3-tuple e ∈ E . F or an y s u bset A ⊆ E and any RB n : 1 ≤ n ≤ N , let I ( n ) ( A ) denote the mutual in f ormation ev aluated for a p o int-to -p oin t MIMO c hannel wh ose output can b e m o deled as y ( n ) = X e ∈A √ p e c e ( n ) H ( n ) e W ( n ) e u ( n ) e + v ( n ) , (18) where v ( n ) ∼ C N ( 0 , I ) is the additiv e Gaussian noise and u ( n ) e ∈ S N t e is the input symb ol v ector corresp onding to 3-tuple e whose entries are indep end en tly and uniformly dr a wn from S e and wh ere u ( n ) e , u ( n ) e ′ are mutually indep end en t for any e 6 = e ′ . Th en, for any U ⊆ E an achiev able rate region is giv en b y r = [ r e ] e ∈U ∈ I R |U | + : X e ∈A r e ≤ N X n =1 I ( n ) ( A ) , ∀ A ⊆ U . (19) 14 Notice that in deriving (19) we hav e assumed an ideal BS receiv er as well as no DFT spreading by eac h user, b oth of whic h allo w for higher ac hiev able rates. 3 Unfortunately , no closed form expressions are a v ailable f or I ( n ) ( A ) and the rate region in (19) do es n ot ha ve a u s eful structure. Clearly the region defined b efore in (5) assuming Gaussian inputs is an outer b ound whic h ho wev er can b e lo ose. Here w e obtain a tigh ter outer b ound that also h as a useful structure. W e first offer the follo wing result. Prop osition 1. F or any subset A ⊆ E and any n : 1 ≤ n ≤ N , we have that I ( n ) ( A ) ≤ min R ⊆A log I + X e ∈A\R p e c e ( n ) H ( n ) e W e ( H ( n ) e W e ) † + X e ∈R N t log( S e ) | {z } △ = g ( n ) ( A ) (20) F urther the set function g : 2 E → I R + define d as g ( A ) = P N n =1 g ( n ) ( A ) , ∀ A ⊆ E , is a r ank function. Pr o of. C onsider an y A ⊆ E , n : 1 ≤ n ≤ N and the mo del in (18). Using the c hain rule for m utual information along w ith the f act that the inp u ts corresp o n ding to an y t wo distinct 3-tuples of A are m utually indep end en t, w e can upp er b ound I ( n ) ( A ) as I ( n ) ( A ) ≤ I ( n ) ( A \ R ) + X e ∈R I ( n ) ( e ) , for any R ⊆ A . Since the cardin ality of the input corr esp onding to 3-tuple e is S N t e w e hav e that I ( n ) ( e ) ≤ N t log( S e ). Then using the fact that for an y giv en input co v ariance, Gaussian inputs (w ith the same co v ariance) maximize the mutual information (o ver the Gaussian n oise channel mo del in (18)), w e ha ve that I ( n ) ( A \ R ) ≤ log I + X e ∈A\R p e c e ( n ) H ( n ) e W e ( H ( n ) e W e ) † . Since these argum en ts are v alid for an y subset R ⊆ A , we can deduce that (20) is tru e. The remaining r esult follo ws from basic definitions. In this con text, w e note that th e b oun d in (20) is a non-trivial generalization of a b ound on the fin ite alphab et mutual information o v er a p oint-t o-p o int fad in g c hann el emplo yed in [33 ] to deriv e a tight lo wer b ound on the outage probability . Ho w ever, th at b ound wh en applied to our case wo u ld only yield I ( n ) ( e ) ≤ min { log | I + p e c e ( n ) H ( n ) e W e ( H ( n ) e W e ) † | , N t log( S e ) } for any e ∈ E . 3 Neglecting the p er-u ser DFT spreading exp ands the rate region since t he noise at th e BS is assumed to b e Gaussian and indep endent across RBs. 15 Next, w e outer b ound the region in (19) as T ( U , g ) △ = r = [ r e ] e ∈U ∈ I R |U | + : X e ∈A r e ≤ g ( A ) , ∀ A ⊆ U . (21 ) In voking Prop osition 1 we use the fact that g ( . ) is a r ank fun ction from wh ic h it f ollo ws that th e region T ( U , g ) is a p olymatroid. Th en inv oking Lemma 2 we can infer the follo wing result. Prop osition 2. F or any choic e of sele c te d 3-tuples U ⊆ E , the r ate r e gion T ( U , g ′ ) △ = T ( U , g ) ∩ B ( U ) is a p olymatr oid which is char acterize d by the r ank function g ′ ( A ) = min R⊆A g ( A \ R ) + X e ∈R Q e , ∀ A ⊆ U . (22) Then, up on b y defining h ′ ( U ) = max r =[ r e ] e ∈U r ∈ T ( U ,g ′ ) X e ∈U α e r e , ∀ U ⊆ E , w e consider the optimizati on problem max U ⊆E { h ′ ( U ) } s . t . U ∈ I ; A I x U ≤ 1 M ; A C x U ≤ b . (23) As b efore, it can b e sho w n that the optimization problem in (23 ) is the maximization of a monotonic sub - mo dular function sub ject to one matroid and multiple knapsack constrain ts. Algorithm I and its asso ciated results are thus app licable. 4 Sim ulation Results In this section we present our simulatio n r esults. W e sim u late an uplink w herein the BS is equ ipp ed with four receiv e an tenn as and eac h user has up-to t w o transmit an tennas. The system has 102 4 s u b-carriers out of whic h 300 su b-carriers d ivid ed into 25 RBs (comprising of 12 consecutiv e sub-carriers eac h) are a v ailable as d ata su b- carriers that are used for serving the u sers. W e assume 10 activ e users, all of whom h a v e identic al maximum transmit p o wers and ident ical path loss factors. W e then use the SCM Urban Macro c hann el mo del [1] to 16 generate the c hannel b et w een eac h user and the base-station in an indep endent ident ically distributed (i.i.d.) manner. The an tenna sp acing at the BS is set to b e 10 λ while that at eac h user is set to b e 1 λ . In all the results giv en b elo w we assu me that the BS emplo ys the optimal receiv er and eac h user can emplo y an unconstrained (Gaussian) input alphab et. F urth ermore, u nless otherwise men tioned, w e assume an infi nitely bac klogged traffic mo del w herein eac h user has an infinite buffer size. 4 Also, the p er-user we ights whic h are giv en as inpu ts to th e sc heduling algorithm are all set to one so that the ob jec tive in (2) r educes to the sum rate. W e note that s in ce the system considered is homogeneo u s, fairness among users will also b e ensured. In Fig. 2, we assume no interference limit or con trol c hann el o ve r head constraints. W e fir st con- sider the case where eac h user is equipp ed with ju st one transmit an tenna and plot th e av erage cell sp ectral efficiency curv e obtained when Algorithm I is employ ed by th e BS sc hedu ler. W e then con- sider th e case wh ere eac h user is equipp ed with t wo transmit an tennas and can use an an tenna s e- lection co deb ook, i.e., W = { [1; 0] , [0; 1] } along w ith the case where an expand ed co deb o ok ( W = { [1; 0] , [0; 1] , [1; 1] / √ 2 , [1; − 1] / √ 2 , [1; − √ − 1] / √ 2 , [1; √ − 1] / √ 2 } [1]) can b e used for eac h user. F or eac h cu rv e, w e plot a corresp o n ding upp er b oun d u sing (17). We c aution her e that while the u pp er b ound in (17) i s very e asy to c ompute, i nde e d the additiona l c omplexity to c ompute the b ound onc e the solution of Algorithm I is available sc ales only line arl y in the numb er of users, the b ound itself ne e d not b e achievable or tight. Its main purp ose i s to show that the aver age p erformanc e of A lgorithm I is signi fic antly sup erior to its worst-c ase guar ante e, esp e cial ly over lar ge examples wher e c omputing the optim al solution via brute for c e e numer atio n is not tr actable. F rom the figure w e observe that in eac h case, th e p erformance of Algorithm I is more th an 75% of th e up p er b ound, whic h is sup erio r to the wo r st case guarantee 1 / 2 (obtained b y sp ecializing the r esult in Theorem 3). Notice that ante nn a selection yields a gain of ab out 1dB o v er the system with single transmit an tenna users w hile the expanded co deb o ok yields a fu rther gain of ab out 0 . 6 dB . Ho w eve r , this additional gain due to the expanded cod eb o ok requires an additional p ow er amplifier at eac h user since sim ultaneous transmission fr om b oth transmit antennas needs to b e s u pp o r ted by eac h user. While ante nn a selection can b e realized with on ly one p o w er amplifier at eac h user, in p ractise it incurs a sw itc hing loss of ab out 0 . 4 dB . Finally , w e note h er e that the linear increase observed for the sp ectral efficiency is due to the fact that we ha ve p lotted th e sp ectral efficiency v ersus SNR in dB (or equiv alen tly the logarithm of the absolute SNR). In Fig. 3 we consider an up link w here eac h u ser is equipp ed with just one transmit an tenna as well as the case w h ere eac h user is equipp ed with tw o transmit an tennas and can u se an an tenn a selectio n cod eb o ok. W e plot the sp ectral efficie n cy obtained up on using Algorithm 1 when eac h user can b e assigned at-most one c hunk 4 W e normalize the p er-user channels and the noise v ariance at the BS ap propriately and refer to the max t ran smit p ow er of eac h user as the (transmit) S NR. 17 (enforced by defining the set of f easible RB allo cations acco rd ingly) as w ell as sp ectral efficiency obtained when eac h us er can b e assigned up-to tw o c hunks. F r om the figu r e we see that the at-most one ch unk restriction do es n ot resu lt in any significant degradation and indeed can b e enf orced to r educe sc heduling complexit y as w ell as to reduce the p er-user P APR. Higher b andwidths (translating to a greater num b e r of av ailable RBs exhibiting greater frequency selecti vity) can bring more gain for allo wing up-to t wo c h un k s p er sc heduled user. In Fig. 4 w e consider th e uplink of Fig. 3 b ut w here there are s even activ e users. W e plot the sp ectral efficiency obtained up o n using Algorithm 1 when eac h user can b e assigned at-most one c h u nk, along with the corresp onding con ve x optimizati on b ased u pp er b ound describ ed in Section 2 (referr ed to in the legend as Imp-UB). It is seen that the p erformance of Algorithm I is within 5% of this u pp er b ound. While the conv ex optimization based upp er b ound is muc h tigh ter and revea ls the exceptional p erformance of Algorithm I, it is computationally demanding to obtain and seems infeasible for larger examples, su c h as the one in Fig. 2 with ten users and an expanded codeb ook of cardinality s ix. In Fig. 5 w e consider an uplink where th ere are 15 RBs av ailable for sc heduling users and eac h u s er is equipp ed with t wo trans m it ant enn as an d can u s e an an tenna selec tion co deb ook. W e imp ose a constrain t that no more than fi v e users can b e sc heduled in eac h s cheduling interv al. W e fir st p lot th e sp ectral efficiency obtained u p on usin g Algorithm 1 with one con trol c h an n el ov erhead constrain t to enf orce the user limit. In particular, this constrain t has an equal co efficient of 1 for eac h u ser and a bu dget limit of 5. Th en, w e consider t wo user pre-selection strategies w h erein a p o ol of 5 u sers is pre-selected in eac h interv al and Algorithm 1 is then us ed on this p ool without an y constrain ts. The in tent ion b ehind user p re-selectio n is to r educe sc heduling complexit y . In the fir st strategy a greedy r u le is emplo y ed wherein the rew ard asso ciated w ith selecting a u ser is set equal to th e maxim um rate that us er can offer on any RB and the 5 users with the 5 largest r ew ards are pre-selected. In the s econd strategy 5 users are randomly pr e-selecte d . F rom the fi gu r es it is eviden t that random pre-selection can r esult in a m uch degraded p erform ance whereas greedy pre-selection seems a go o d metho d to achiev e complexit y redu ction with ou t significan t p erformance degradation. In the follo wing set of figures w e use the 6 path equal gain i.i.d. Rayl eigh fading c hannel mo d el to generate the c hannel b et wee n eac h user and the base-station. In Fig. 6 we consider the impact of the num b er of users ( K ) on the system p erformance o ver an u plink whic h has N = 20 RBs av ailable and wherein eac h u ser h as one transmit an tenna. W e consider t wo v alues of transmit SNRs and first capture the cell sp ectral efficiency (obtained when Algorithm I is emplo yed by the BS sc heduler) as the n u mb er of us ers increases. W e th en d epict the av erage p er-user sp ectral efficiency . Notice first that the cell sp ectral efficiency increases only logarithmica lly in the num b er of users s in ce the num b er of receiv e ante nn as is held fixed at four and consequent ly the p er-user sp ectral efficiency is decreasing in the 18 n umb er of users (i.e., it is o ( K )). Moreo ver, we note that in all the cases considered f or SNR 18 dB , the p erformance of Algorithm I is more that 75% of the u pp er b ound in (17). Next, in Figure 7 we assess the impact of finite buffers o v er the uplink of Fig. 6 but where there are N = 10 RBs a v ailable to service K = 10 users. In addition, eac h u ser can b e assigned at-most one c hunk of RBs. W e assume a fixed arriv al rate p er-user whic h is identic al across all users and consid er four differen t v alues for this arriv al r ate along with an SNR of 13 dB . In eac h case we plot the cell sp ectral efficiency obtained when Algorithm I is employ ed by the BS sc hedu ler, as w ell as that obtained wh en a heu ristic scheduler is emp lo y ed. In particular, the heuristic we consider is the one where Algorithm I is fi rst emplo y ed assuming infi nite buffer sizes. Then, th e finite buffer size constrain t is imp o sed separately on eac h s c heduled u ser. F r om the figure w e note that at low arriv al rates the system is n ot resour ce limited in that all users can b e simultaneously assigned r ates equal to their resp ec tive buffer sizes and an y simple scheduling algorithm will suffi ce. How ev er, at mo derate v alues of arr iv al rates directly incorp orati n g the bu ffer sizes in the resource allo cation step is quite b eneficial. A t large v alues of arr iv al rates the p erformance of the heu r istic will again approac h th at of Algorithm I since the buffer size constraints will b e increasingly irrelev ant. Finally , in Figure 8 w e compare the p erformance of Algorithm I with that of the other algorithms that ha ve b een prop osed b efore. In this comparison, we assum e that eac h user has one trans mit antenna and can b e assigned at-most one c h unk and there are N = 20 RBs a v ailable to service the users. W e hav e considered, to the b est of our kno wledge, all algorithms that yield feasible solutions to the problem at hand. In particular, w e p lot the p erformance of three algorithms that hav e b een p rop osed for sin gle-user sc hedu ling o v er the L TE uplink. T hese include a greedy h eu ristic p r op osed in [14], an app ro ximation algorithm referred to as b enefit- doubling (BD) prop o sed in [11] and another approximati on algorithm based on the lo cal ratio test (LR T) prop osed in [12]. In addition, w e also p lot the p erform ance of another approximati on alg orithm, r eferred to here as the enhanced local ratio test (ELR T) based algo r ith m [15], prop osed for multi-user sc h eduling o v er the L TE up link wh ere up-to tw o users can b e s im ultaneously sc hedu led on an RB provi d ed that an y pair of o v erlappin g users are assigned the same set of R Bs (a.k.a. the complete o ve rlap constraint). F r om the fi gu r es, w e see that Algo rithm I yields very significant gains o ver the previously prop o sed algorithms. These gains stem from tw o facts. Th e fi rst one is that multi-user sc h eduling o ver the L TE-A u plink enables sub stan tial gains by allo wing m ultiple u sers to b e co-sc heduled on an RB and by relaxing the complete o v erlap constrain t. The second fact is that Algorithm I is near-optimal wh ich allo ws it to capture almost all of the av ailable gains. 19 5 Conclusions W e considered r esour ce allo cation in the 3GPP L TE-A cellular uplink whic h allo ws for MIMO transmission from eac h s c heduled user as well as m ulti-user sc heduling wherein m ultiple users can b e assigned the same time-frequency resource. W e sho wed that the r esulting resource allo cation problem is NP-hard and then prop osed constan t-factor p olynomial-time approximat ion algorithms. A Definitions W e capture some basic kno wn defi n itions that are in vo ked in the pap er. Definition 1. Given a gr ound set Ω , we define i ts p ower set (i.e., the set c ontaining al l the subsets of Ω ) as 2 Ω . Then, a non-ne gative r e al value d function define d on the subsets of Ω , h : 2 Ω → I R + is a monotonic set function if and only if it satisfies, 0 ≤ h ( A ) ≤ h ( B ) , ∀ A ⊆ B ⊆ Ω . In addition, the set function is also a submo d ular set function if and only if h ( B ∪ a ) − h ( B ) ≤ h ( A ∪ a ) − h ( A ) , ∀ A ⊆ B ⊆ Ω & a ∈ Ω \ B . (24) F urthermor e, the set function is also a r ank function function if it is normalize d, i.e., h ( φ ) = 0 , wher e φ de- notes the empty set. Then, the r e gion define d as P (Ω , h ) = n r = [ r e ] e ∈ Ω ∈ I R | Ω | + : P e ∈A r e ≤ h ( A ) , ∀ A ⊆ Ω o is a p olymatroid . A knapsac k constraint on the elements of Ω is a c onstr aint that c an b e expr esse d as P e ∈ Ω a e X e ≤ b for some non-ne gative sc alars { a e } , b ∈ I R + and wher e X e is an indic ator variable which is one if element e is chosen and zer o otherwise. W i thout loss of gene r ality, we c an assume that a e ≤ b, ∀ e ∈ Ω . Definition 2. (Ω , I ) , wher e I is a c ol le ction of some subsets of Ω , is said to b e a matroid if I is an indep en - dence family : • I is downwar d close d, i.e., A ∈ I & B ⊆ A ⇒ B ∈ I • F or any two memb ers F 1 ∈ I and F 2 ∈ I such that |F 1 | < |F 2 | , ther e exists e ∈ F 2 \ F 1 such that F 1 ∪ { e } ∈ I . This pr op erty is r ef e rr e d to as the exchange pr op erty. Definition 3. (Ω , I ) is said to b e a partition matroid when ther e exists a p artition Ω = ∪ J i =1 Ω i , wher e Ω i ∩ Ω j = φ, ∀ i 6 = j , along with inte g ers n i ≥ 1 ∀ i such that B ⊆ Ω : |B ∩ Ω i | ≤ n i ∀ i ⇔ B ∈ I (25) 20 Definition 4. An optim ization pr oblem is said to b e NP-hard i f any algorith m that r eturns an optimal solution to the pr oblem at hand given any instanc e as an input, and whose worst-c ase c omplexity (over al l instanc es) sc ales p olynomial ly in the size of the gr ound set, c an b e use d to c onstruct such an algorithm for e ach NP- c omp lete pr oblem. Construction of such algorithms for the latter c lass of N P-c omplete pr oblems has b e en a long standing op en pr oblem [34] and inde e d the existenc e of suc h algorith ms is thought to b e highly impr ob able. A constant factor appro ximation algorithm for a c ombinatoria l optimizat ion pr oblem (in which the obje ctive must b e maximize d), is an algorithm which r eturns a fe asible solution given any i nstanc e as an input such that the obje ctive value obtaine d using the r eturne d solution is no less than Γ times the optimal obje ctive value for that i nstanc e. The factor Γ is r eferr e d to as the c onsta nt-factor and lies i n the unit interval [0 , 1] and must b e indep endent of the input instanc e. B Pro of of T heorem 1 Pr o of. W e will first sho w that (11) is the maximization of a monotonic sub-mo d ular set function su b ject to one matroid and multiple knapsac k constrain ts. In voking Lemma 1 , it suffices to sho w that the fu nction h ( . ) is a monotonic su bmo du lar set function. F rom the definition of h ( . ) in (7) it is readily seen that it is monotonic, i.e., h ( U ) ≤ h ( V ) , ∀ U ⊆ V ⊆ E . There are m ultiple wa ys to prov e the submo d u larit y of h ( . ) and we d etail one wh ic h directly sh o ws that h ( . ) satisfies the prop erty in (24) for any t w o sub s ets U ⊆ V in E an d an y element e ∈ E \ V . T ow ards this end , let o ( ., . ) d enote an ordering fun ction s u c h that for an y subset U ⊆ E , o ( U , k ) is the 3-tuple having the k th largest w eigh t among the 3-tuples in U . Hence we ha ve that α o ( U , 1) ≥ α o ( U , 2) ≥ α o ( U , |U | ) . F u rther, let us adopt the con ve ntion that for an y subset U ⊆ E , o ( U , 0) = φ & o ( U , k ) = φ, ∀ k ≥ |U | + 1 & α φ = 0. Defining J = |U | , we n o w inv ok e Lemma 2 tog ether with the imp ortan t pr op ert y that the r ate-tuple in e ach p olymatr oid that maximizes the weighte d sum is determine d by the c orner p oint of that p olymatr oid i n which the 3-tuples ar e arr ange d in the non-incr e asing or der of their weights [19, 20] . Thus, w e can express h ( . ) as h ( U ) = α o ( U , 1) f ′ ( o ( U , 1)) + J X k =2 α o ( U ,k ) [ f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ) − f ′ ( { o ( U , 1) , · · · , o ( U , k − 1) } )] . ( 26) Let q b e the sm allest integ er in { 1 , · · · , J } for wh ic h α e > α o ( U ,q ) so that α e > α o ( U ,j ) , ∀ j ≥ q whereas α e ≤ α o ( U ,j ) , ∀ j < q . As a result, us ing (26) we obtain that h ( U ∪ e ) − h ( U ) = α e [ f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } )] + 21 J X k = q α o ( U ,k ) f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , k − 1) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ) + f ′ ( { o ( U , 1) , · · · , o ( U , k − 1) } ) = α e [ f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } )] + J X k = q α o ( U ,k ) f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ) − f ′ ( { o ( U , 1) , · · · , o ( U , k − 1) } ∪ e ) + f ′ ( { o ( U , 1) , · · · , o ( U , k − 1) } ) (27) whic h can b e re-written as h ( U ∪ e ) − h ( U ) = ( α e − α o ( U ,q ) )[ f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , q − 1) } )] + J X k = q ( α o ( U ,k ) − α o ( U ,k +1) )[ f ′ ( { o ( U , 1) , · · · , o ( U , k ) } ∪ e ) − f ′ ( { o ( U , 1) , · · · , o ( U , k ) } )] . (28) Consider now the set V and supp ose that o ( V , i k ) = o ( U , k ) , ∀ 1 ≤ k ≤ J , where 1 ≤ i 1 < i 2 < · · · < i J ≤ |V | . No w let r b e the smallest in teger in { 1 , · · · , |V |} for whic h α e > α o ( V ,r ) and clearly w e ha v e r ≤ i q . Analogous to (27), we expr ess h ( V ∪ e ) − h ( V ) as h ( V ∪ e ) − h ( V ) = α e [ f ′ ( { o ( V , 1) , · · · , o ( V , r − 1) } ∪ e ) − f ′ ( { o ( V , 1) , · · · , o ( V , r − 1) } )] + |V | X k = r α o ( V ,k ) f ′ ( { o ( V , 1) , · · · , o ( V , k ) } ∪ e ) − f ′ ( { o ( V , 1) , · · · , o ( V , k ) } ) − f ′ ( { o ( V , 1) , · · · , o ( V , k − 1) } ∪ e ) + f ′ ( { o ( V , 1) , · · · , o ( V , k − 1) } ) (29) Due to sub-mo d ularit y of f ′ ( . ) (cf. prop ert y in (24)) eac h of the terms corresp onding to k = r , · · · , |V | in the summation in (29) is non-p ositiv e. Consequentl y , we can up p er b ound h ( V ∪ e ) − h ( V ) b y first droppin g the terms corresp onding to k = i J + 1 , · · · , |V | and then r educing the we ights of the remaining terms as α o ( V ,k ) → α o ( V ,i j ) = α o ( U ,j ) , ∀ k : i j − 1 < k ≤ i j , j ≥ q + 1 while α o ( V ,k ) → α o ( V ,i q ) = α o ( U ,q ) , ∀ k : r ≤ k ≤ i q . Next, w e order and pars e the remaining 3 − tuples in V as o ( V , 1) , · · · , o ( V , r − 1) | {z } △ = S q − 1 , o ( V , r ) , · · · , o ( V , i q ) | {z } △ = S q , o ( V , i q + 1 ) , · · · , o ( V , i q +1 ) | {z } △ = S q +1 , · · · , o ( V , i J − 1 + 1 ) , · · · , o ( V , i J ) | {z } △ = S J 22 Com binin g all terms that ha ve common w eight s (p ost the reduction step) we obtain the upp er b ound to b e h ( V ∪ e ) − h ( V ) ≤ ( α e − α o ( U ,q ) )[ f ′ ( S q − 1 ∪ e ) − f ′ ( S q − 1 )] + J X k = q ( α o ( U ,k ) − α o ( U ,k +1) )[ f ′ ( S q − 1 ∪ · · · ∪ S k ∪ e ) − f ′ ( S q − 1 ∪ · · · ∪ S k )] (30) Finally , comparing (28) and (30) we note that ( α e − α o ( U ,q ) ) > 0 & { o ( U , 1) , · · · , o ( U , q − 1) } ⊆ S q − 1 and ( α o ( U ,k ) − α o ( U ,k +1) ) ≥ 0 & { o ( U , 1) , · · · , o ( U , k ) } ⊆ S q − 1 ∪ · · · ∪ S k , ∀ q ≤ k ≤ J . C onsequen tly , w e can in vo ke the su bmo du larit y of f ′ ( . ) again to conclude that the up p er b ound in (30) is less than h ( U ∪ e ) − h ( U ) so th at h ( V ∪ e ) − h ( V ) ≤ h ( U ∪ e ) − h ( U ), whic h establishes the submo d ularit y of h ( . ). W e will no w show that (11) is an NP hard p roblem. W e will consider instances of the problem where the n umb er of RBs N = 1, all users ha ve identical weig hts, unit p o wers, infi nite qu eues an d one transmit an tenna eac h an d where the co d eb ook W is degenerate, i.e., W = { 1 } . Thus, w e ha v e |E | = K . In addition, w e assu me that the n u m b er of receiv e antennas is equal to the num b er of users K so that a giv en input of user channels forms a K × K m atrix, denoted here by H = [ h 1 , · · · , h K ]. F u rther, we will assum e only one knaps ac k constrain t wh ic h in p articular is a cardinalit y constrain t on the n umb er of u sers that can b e sc h eduled on the one a v ailable RB. W e will show that the p roblem sp ecialized to these instances is also NP-h ard so that the original problem is NP-hard. Note that the matroid constrain t now b ecomes redun dan t and (11) simplifies to maximizing the s um r ate u nder a cardin alit y constrain t max D =diag { d 1 , ··· ,d K } d k ∈{ 0 , 1 } ∀ k & P K k =1 d k ≤ C log | I + HDH † | , (31) where C : 1 ≤ C ≤ K is the in p ut maxim um cardinalit y . No w usin g the determinant equalit y log | I + HDH † | = log | I + DH † HD | (32) together with th e monotonicit y of the ob jective fu nction, w e can r e-write (31) as max D =diag { d 1 , ··· ,d K } d k ∈{ 0 , 1 } ∀ k & P K k =1 d k = C log | I + DH † HD | . (33) Note that (33) is equ iv ale nt to determining the C × C pr incipal sub-matrix of th e p ositiv e definite matrix I + H † H having the maxim um determinant. Note that for a giv en K , an instance of the p roblem in (33) is the matrix H together with C . W e will p ro ve that (33) is NP-hard via con tradiction. Su pp ose now that an 23 efficien t algorithm (with a complexit y p olynomial in K ) exists th at can optimally solv e (33) for any input K × K matrix H and an y C : 1 ≤ C ≤ K . This in turn would imply that there exists an efficien t algorithm (with a complexity p olynomial in K ) that for an y inp ut C : 1 ≤ C ≤ K and an y K × K p ositiv e d efinite matrix Σ, can determine the C × C pr in cipal sub-matrix of Σ ha vin g the maximum d etermin ant. Inv oking the redu ction dev elop ed in [35], this w ould then con tradict the NP h ardness of the p roblem of d etermining whether a giv en input graph h as a clique of a giv en inp ut size. C Pro of of Theorem 3 W e first consider the complexit y of Algorithm I and note th at since the partition matroid constraint n eeds to b e s atisfied, there can b e at-most K steps in rep eat-un til lo op of the algo rithm . Also, r ecall that th e the size of the ground set E is O ( K N 4 |W | ). T hen, at eac h step w e need to compute h ( S ∪ e ) for eac h e ∈ E \ S su c h that S ∪ e satisfies all the constrain ts. Thus, the w orst-case complexit y is O ( K 2 N 4 |W | ). Let us n o w consider th e appro ximation guarantees. Notice that due to the p artition matroid constrain t an y optimal solution to (11) cannot con tain more that K 3-tuples. Then, us ing th e subadd itivit y of h ( . ) sho wn in Lemma 3 together with the facts that Algorithm I is monotonic and in its firs t step selects th e 3-tuple of E ha ving the highest w eight ed rate, suffice to pr o v e th e 1 K guaran tee. On the other hand, supp ose that Cond itions 1 and 2 are satisfied (o v er all ins tances). Consider th e L con trol channel constrain ts and let E ℓ denote the set of 3-tuples in v olve d in the ℓ th con trol c h annel constrain t so that E = ∪ L ℓ =1 E ℓ . Recall that E ℓ ∩ E ℓ ′ = φ, ℓ 6 = ℓ ′ and notice that an y s et U ⊆ E that satisfies these L constrain ts can b e expressed as U = ∪ L ℓ =1 U ℓ , wh ere U ℓ ⊆ E ℓ : |U ℓ | ≤ b ℓ , 1 ≤ ℓ ≤ L , wh ere b ℓ is the cardinalit y b ound imp osed by the ℓ th con trol c hann el constrain t. Thus th e L control c hannel constrain ts together are indeed one partition matroid. More imp ortantly , the inte rs ection of this p artition matroid with the one defined in Lemma 1 is also one matroid. T o see this, let I ′ denote this int ersection and recall the defin itions giv en in App endix A. It can readily b e seen that I ′ is do wnw ard closed. Th en, we need to show th at the exc hange pr op ert y holds. Consider any F 1 , F 2 in I ′ suc h th at |F 1 | < |F 2 | . Clearly , the u sers corresp ond ing to all 3-tuples in F 1 m ust all b e distinct since F 1 ∈ I . In addition, eac h 3-tuple of F 1 can ha v e a non-zero coefficien t in only one con trol c hann el constrain t. Similarly for F 2 . Then consider an y 3-tuple e ∈ F 2 \ F 1 suc h that no 3-tuple in F 1 con tains the user u e . Notice that there m ust exist at-least one such 3-tuple. Clearly , for such a 3-tuple F 1 ∪ { e } ∈ I . C onsequen tly , F 1 ∪ { e } / ∈ I ′ only if a con trol c hann el constrain t is violated. Without loss of generalit y , sup p ose this constrain t is th e fi rst cont r ol c h annel constrain t. Then, since all non-zero co efficients in an y control channel constrain t are identica l, we can deduce that there exists a 3-tuple e ′ ∈ F 1 suc h that 24 e ′ ∈ E 1 but the user u e ′ is n ot con tained in an y 3-tuple of F 2 . This observ ation together with the fact that |F 1 | < |F 2 | allo ws us to conclude that there exists an e ∈ F 2 \ F 1 suc h that F 1 ∪ { e } ∈ I ′ , w hic h then yields the desired resu lt. Finally , com bining this matroid with the other M (int erf er en ce limit) matroid constrain ts, we see that the feasible subsets b el ong to the in tersection of M + 1 matroids and hence form a p − system where p = M + 1. Then inv oking th e guarante e offered by the greedy algorithm on a p − system [30, 36], prov es the second part. References [1] 3GPP, “TSG-RAN EUTRA, rel.10,” TR 36.213 , Dec 2010. [2] W. Y u and W. Rh ee, “Degrees of fr eedom in wireless multiuser s p atial m u ltiplex systems with multiple an tennas,” IEEE T r ans. Commun. , v ol. 54, pp . 1747–17 53, O ct 200 6. [3] N. Bansal, N. Koru la, V. Naga r a jan, and A. Sriniv asan, “On k-column sparse pac king programs,” Pr o c. International Confer enc e on Inte ger Pr o gr amming and Combinatoria l Optimization , 2010. [4] W. Y u and R. Liu, “Dual metho ds for noncon v ex sp ectrum optimization of multic arrier systems,” IEEE T r ans. Commun. , v ol. 54, pp. 1310 –1322, July 2006. [5] W. Noh, “A distributed resource con trol for fairness in ofd ma systems: En glish-auction game with imp erfect information,” Pr o c. IEEE Glob al T ele c ommun. Conf. (Glob e c om) , 2008. [6] S. Lee, S . Choud hury , A. Khoshnevis, S. Xu, and S. Lu , “Do wnlink MIMO with frequ ency-domain pac k et sc hedulin g for 3GPP L TE,” IEEE Info c om , 2009. [7] N. P rasad, K. Li, and X. W ang, “F air rate allo cation in multiuser O FDM-SDMA net w orks,” IEEE T r ans. Sig. Pr o c . , v ol. 57, pp. 279 7–2808, Jul. 200 9. [8] E. Calv o, D. P alomar, J. R. F onollosa, and J. Vidal, “On the compu tation of the capacit y region of the discrete MA C,” IEEE T r ans. Commun. , v ol. 58, pp. 3512 – 3525 , Dec. 201 0. [9] W. Dai, B. C . Rider, and Y. Liu , “Join t b eamforming for m ultiaccess MIMO systems finite rate feedbac k,” IEEE T r ans. W ir eless Commun. , v ol. 8, pp. 261 8 – 2628, Ma y . 2009. [10] S. N. Don thi and N. B. Meh ta, “Join t p erformance analysis of c hannel qu ality in dicator feedbac k sc hemes and frequency-domain sc heduling for L TE,” IEEE T r ans. V ehicular T e ch. , Sept. 2011. 25 [11] M. Andr ews and L. Zh ang, “Multiserv er scheduling w ith conti guity constraints,” Pr o c. IEEE Info c om , 2009. [12] H. Y ang, F. R en , C. Lin, and J. Zh ang, “F requency-domain pack et sc hedu ling for 3GPP L TE u plink,” IEEE Info c om , 2010. [13] N. Prasad, H. Zhang, M. Jiang, G. Y ue, and S. Rangara jan, “Resource allo cation in 4G MIMO cellular uplink,” IEEE Glob e c om , 2011. [14] S. B. Lee, I. Pefkia n akis, A. Mey erson, X. Sh u gong, and L. Songwu, “Prop o r tional fair frequen cy-domain pac k et scheduling for 3GPP L TE uplink,” in Pr o c. IEEE INFOCOM , 2009. [15] N. Prasad, H. Zhang, H.Zhu, and S. Rangara jan, “Multi-user scheduling in the 3GPP L TE cellular uplink,” IEEE WiOpt , 2012. Extended v ersion to app ear IEEE T rans. Mobile Comp. [16] Y. Liu and E. Kn igh tly , “Opp ortun istic f air scheduling o v er multi p le w ireless c han n els,” in Pr o c. 2003 IEEE INFOCOM , (San F rancisco, CA), Mar. 200 3. [17] W. Y u and J. Cioffi, “Constan t p o w er water-filling: P erform ance b ound and lo w-complexit y implemen- tation,” IEEE T r ans. Commun. , vo l. 54, pp. 23–28, Jan. 2006. [18] 3GPP, “TSG-RAN EUT R A, rel.8,” TR 36.101 , Jun 2011. [19] J. Edmond s, “Subm o dular functions, matroid, and certain p olyhedra,” Combinatorial Structur es and Their Applic ations , 1970. [20] D. Tse and S. Hanly , “Multiaccess fading c hannels-part I: Pol ymatroid structur e, optimal resource allo - cation, and th roughput capacit ies,” IEEE T r ans. Inform. The ory , 1998. [21] C. Chekuri, J. V ondr ak, and R. Zenklusen, “Dep endent r an d omized rounding via exchange prop erties of com binatorial structures,” FOCS , 2010. [22] L. A. W olsey , “F aces f or a linear inequalit y in 0-1 v ariables,” Mathematic al Pr o gr amm ing , 1975. [23] J. O. Cerdeiral and P . Barcia, “When is a 0-1 kn ap s ac k a matroid?,” Portugaliae Mathematic a , 199 5. [24] S. Sana yei and A. Nosratinia, “Capacit y of MIMO c hannels with antenna selectio n ,” IEEE T r ans. on Information The ory , 2007. [25] R. V aze and H. Ganapathy , “Sub-mo d ularit y and antenna selectio n in MIMO systems,” IEEE T r ans. Commun. L etters , v ol. 16, pp. 1446 –1449, S ep. 201 2. 26 [26] M. K . V aranasi and T. Guess, “Op timum d ecision feedbac k m ultiuser equalizatio n w ith su ccessiv e de- co ding ac hiev es the total capacit y of th e Gaussian m ultiple-access c hannel,” IEEE Asilomar , No v. 199 7. (in vited). [27] S. Iw ata, L. Fleisc her, and S. F uj ishige, “A com binatorial strongly p olynomia l algorithm for minim izing submo d ular functions,” Journal of ACM , 2001. [28] M. Minoux, “Accelerated greedy algorithms for maximizing su b mo dular set functions,” Optimization T e chniques, LNCS , 1978. [29] A. K rause, J. Lesko v ec, C. Guestrin, J. V anBriesen, and C. F aloutsos, “Efficien t sensor placemen t op- timizatio n for securing large w ater distribu tion n et w orks,” Journal of Water R esour c es Planning and Management , 200 8. [30] G. L. Nemhauser, L. A. W olsey , an d M. L. Fisher, “An analysis of approximat ions f or maximizing submo d ular set functions,” Math. Pr o g r amming , 1978. [31] W. Y u, W. Rhee, S . Bo yd, and J. Cioffi, “Iterativ e wat er-filling f or Gaussian vec tor multiple access c hannels,” IEEE T r ans. on Information The ory , 2004. [32] M. Mohseni, R . Zhang, and J. M. Cioffi, “Optimized transmission of fadin g m ultiple-access and broadcast c hannels with m ultiple ante nn as,” IEEE J. Sele ct. Ar e as Commun. , 2006. [33] K. D. Nguy en, A. G. F abregas, and L. K. Rasmussen, “A tight lo wer b ound to the outage probab ility of discrete-input blo c k-fading channels,” IEEE T r ans. on Information The ory , 2007. [34] R. M. Karp, “Reducibilit y among com b inatorial p r oblems,” R. E. Mil ler and J. W. Thatcher (e ditors). Complexit y of Computer Computations , New Y ork: Plenum. , pp. 85–1 03, 1972 . [35] C. Ko, J. Lee, and M. Queyranne, “An exact algorithm for maximum en tropy sampling,” O p er ations R e se ar ch , 1995. [36] G. L. Nemhauser and L. A. W olsey , “Best algorithms for appro ximating the maximum of a submo d u lar set function,” Math. Op er ations R ese ar ch , 1978. 27 Figure 1: A F easible RB Allo cation in the L TE-A UL: The assignment of RBs to eac h user is rep resen ted b y a shaded region. T able 1: Algorithm I: Greedy Algorithm for L TE -A UL MU-MIMO 1: Initialize S = φ 2: Rep eat 3: Determine ˆ e = arg max e ∈E \S S ∪ e ∈ I ; A I x S ∪ e ≤ 1 M ; A C x S ∪ e ≤ b { h ( S ∪ e ) } (34) and set ˆ v = h ( S ∪ ˆ e ) − h ( S ). 4: If ˆ v > 0 The n 5: S ← S ∪ e 6: End If 7: Un til ˆ v ≤ 0 or ˆ e = φ 8: Outpu t S . 28 T able 2: Sym b ol Definitions K Number of users N Number of RBs N t Number of TX antennas at eac h user N r Number of RX antennas at BS L Number of column sparse knapsack constrain ts that mod el the control channel o verhead constrain ts A C ∈ { 0 , 1 } L ×|E | Matrix containing the coef- ficients of the column- sparse knapsack constraints ∆ co lumn sparsity level in A C b L length con trol c hann el budget vector M num b er of generic knapsack constrain ts A I ∈ [0 , 1] M ×|E | Matrix contai n ing the nor- malized co efficien ts of the generic kn ap sack constraints α u W eight of user u r u rate (bits/frame) assigned to user u P u P ow er bu dget of user u Q u Buffer size of u ser u c N -length vector represent- ing a v alid RB assign- ment containing at- most t wo ch unks W Precoder matrix ha ving unit F rob enius n orm W Fi nite co deb o ok of all pre- coder matrices C S et of all v alid RB assign- ments e = ( u, c , W ) 3-tuple denoting allocation of RB as signment c and pre- coder W to u ser u E Ground set con taining all p ossible 3-tuples u e user in 3-tuple e c e RB assignment in 3-tuple e W e precod er in 3-tuple e I Collec tion of v alid subsets of E H ( n ) e Channel matrix seen from user u e on RB n B ( U ) Region d efined by bu ffer sizes of 3-tu ples in U f ( . ) , f ′ ( . ) , g ( . ) , g ′ ( . ) four different rank functions P ( U , f ) , P ( U , f ′ ), T ( U , g ) , T ( U , g ′ ) P olymatroids d etermined b y subset U ⊆ E and rank func- tions f ( . ) , f ′ ( . ) , g ( . ) , g ′ ( . ), respectively h ( . ) Set function defined such that h ( U ) , ∀ U ⊆ E yields the maximum wei ghted sum rate over p olymatroid P ( U , f ′ ) h ′ ( . ) Set function d efined such that h ′ ( U ) , ∀ U ⊆ E yields the maximum weigh ted sum rate over p olymatroid T ( U , g ′ ) 29 6 8 10 12 14 16 18 20 22 24 26 10 15 20 25 30 35 SNR (dB) Spectral Efficiency (bps/Hz) Single TX Antenna Selection Codebook Single TX−UB Antenna Selection−UB Codebook−UB Figure 2: Av erage s p ectral efficiency v ersus SNR (dB). 6 8 10 12 14 16 18 20 22 24 26 8 10 12 14 16 18 20 22 24 26 28 SNR (dB) Spectral Efficiency (bps/Hz) Single TX−1 chunk Single TX−2 chunks Antenna Selection−1 chunk Antenna Selection−2 chunks Figure 3: Impact of th e n umb er of c hunks p er user . 30 4 6 8 10 12 14 16 18 20 22 24 4 6 8 10 12 14 16 18 20 22 SNR (dB) Spectral Efficiency (bps/Hz) Single−TX Single−TX−Imp−UB Antenna Select Antenna Select−Imp−UB Figure 4: Conv ex Optimization b ased Up p er Bound 5 6 7 8 9 10 11 12 13 14 6 7 8 9 10 11 12 13 14 SNR (dB) Spectral Efficiency (bps/Hz) No pre−selection Greedy pre−selection Random pre−selection Figure 5: Impact of User P r e-Selection. 31 5 10 15 20 25 5 10 15 20 25 30 35 Number of Users Spectral Efficiency (bps/Hz) snr=10 snr=10,UB snr=18 snr=18,UB (a) 5 10 15 20 25 0.5 1 1.5 2 2.5 3 3.5 Number of Users Spectral Efficiency per user (bps/Hz) snr=10 snr=10,UB snr=18 snr=18,UB (b) Figure 6: Impact of th e n umb er of users: (a) Cell sp ectral efficiency (b) p er-user sp ectral efficiency . 32 40 60 80 100 120 140 160 180 200 2 4 6 8 10 12 14 16 18 20 Per−user arrival rate (Kbps) Throughput (Mbps) Heuristic Algorithm I Figure 7: Impact of fi nite buffers. 33 5 10 15 20 0 5 10 15 20 25 Number of users Spectral Efficiency (bps/Hz) SNR=10dB Heuristic−SU BD−SU LRT−SU ELRT−MU AlgI−MU (a) 5 10 15 20 0 5 10 15 20 25 30 35 Number of users Spectral Efficiency (bps/Hz) SNR=18dB Heuristic−SU BD−SU LRT−SU ELRT−MU AlgI−MU (b) Figure 8: Comparison for v arying num b er of us ers: (a) Av erage SNR=10dB (b) Av erage SNR=18dB . 34
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment