All Your Location are Belong to Us: Breaking Mobile Social Networks for Automated User Location Tracking
Many popular location-based social networks (LBSNs) support built-in location-based social discovery with hundreds of millions of users around the world. While user (near) realtime geographical information is essential to enable location-based social discovery in LBSNs, the importance of user location privacy has also been recognized by leading real-world LBSNs. To protect user’s exact geographical location from being exposed, a number of location protection approaches have been adopted by the industry so that only relative location information are publicly disclosed. These techniques are assumed to be secure and are exercised on the daily base. In this paper, we question the safety of these location-obfuscation techniques used by existing LBSNs. We show, for the first time, through real world attacks that they can all be easily destroyed by an attacker with the capability of no more than a regular LBSN user. In particular, by manipulating location information fed to LBSN client app, an ill-intended regular user can easily deduce the exact location information by running LBSN apps as location oracle and performing a series of attacking strategies. We develop an automated user location tracking system and test it on the most popular LBSNs including Wechat, Skout and Momo. We demonstrate its effectiveness and efficiency via a 3 week real-world experiment with 30 volunteers. Our evaluation results show that we could geo-locate a target with high accuracy and can readily recover users’ Top 5 locations. We also propose to use grid reference system and location classification to mitigate the attacks. Our work shows that the current industrial best practices on user location privacy protection are completely broken, and it is critical to address this immediate threat.
💡 Research Summary
The paper “All Your Location are Belong to Us: Breaking Mobile Social Networks for Automated User Location Tracking” investigates the privacy guarantees of popular location‑based social networks (LBSNs) that claim to protect users by only exposing relative distances, limiting accuracy, or restricting coverage. The authors focus on three widely used Chinese apps—WeChat, Momo, and Skout—each of which implements one or more of these obfuscation techniques.
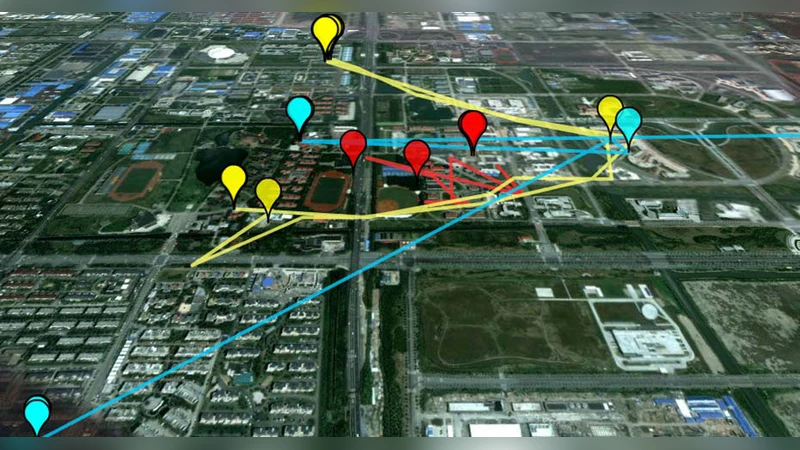
The threat model assumes a very limited adversary: the attacker possesses only the privileges of a regular LBSN user, cannot hack the server, and can only interact with the unmodified client app. By exploiting the fact that the client app acts as a location oracle, the attacker can manipulate its own reported position (e.g., via GPS spoofing) and observe the distance that the app reports to the target user. Repeating this process from multiple attacker‑controlled locations yields a set of distance measurements that can be combined mathematically to infer the target’s absolute coordinates.
The authors formalize a four‑step attack pipeline, which they implement in a system called FreeTrack:
- Oracle Construction – The attacker creates several “virtual” positions by moving (or spoofing) their device and records the relative distance shown for the target.
- Range‑Free Localization – Using the collected distances, the attacker solves a set of nonlinear equations (essentially a multilateration problem). When distances are reported as intervals (e.g., “within 100 m”), the attacker samples uniformly inside the interval and averages over many trials to converge to a narrow region.
- Continuous Tracking – By periodically repeating step 1, the attacker obtains a time‑series of estimated positions. A Kalman filter (or similar Bayesian estimator) smooths the series, reducing measurement noise caused by rounding and coverage limits.
- Top‑K Location Extraction – The filtered trajectory is clustered (using DBSCAN or K‑means) to identify the user’s most frequently visited places. The authors show that the top‑5 locations can be recovered with high precision, which is significant because prior work demonstrates that just two frequent locations can uniquely identify >50 % of individuals.
A three‑week field study with 30 volunteers (distributed across the United States, China, and Japan) validates the approach. The average localization error is 51 m for WeChat (74 tests), 25 m for Momo (119 tests), and 130 m for Skout (156 tests). These numbers are well within the “privacy‑preserving” bounds advertised by the services (e.g., WeChat’s 100 m accuracy limit). Moreover, the system reliably recovers the users’ top‑5 venues, confirming that the relative‑distance obfuscation provides insufficient protection in practice.
To mitigate the attacks, the authors propose two complementary strategies:
- Grid Reference System – Instead of exposing raw coordinates or precise distances, the service maps users to grid cells and only shares the cell identifier. Cell size can be dynamically adjusted based on population density (large cells in dense urban areas, smaller cells in rural zones) to balance utility and privacy.
- Multi‑Level Location Classification – Distance information is released at several granularity levels (e.g., 10 m, 100 m, 1 km) rather than a single fixed precision. This hierarchical disclosure reduces the amount of information an attacker can extract from any single query.
The paper acknowledges that even with these defenses, a determined adversary could combine multiple queries across different granularity levels or exploit cell‑boundary overlaps to regain some accuracy. Consequently, the authors argue that the current industry practice of “relative distance only” is fundamentally flawed. They recommend moving toward cryptographic privacy‑preserving techniques such as homomorphic encryption‑based proximity testing or zero‑knowledge proofs, which can enable proximity discovery without revealing any location information at all.
In summary, the work demonstrates that location‑obfuscation mechanisms employed by major LBSNs can be broken by a regular user using only publicly available client‑side data. The automated tracking system achieves sub‑100‑meter accuracy and reliably extracts frequent user locations, exposing a serious privacy risk for hundreds of millions of users. The findings call for a reassessment of privacy guarantees in mobile social platforms and the adoption of stronger, provably secure location‑privacy solutions.
Comments & Academic Discussion
Loading comments...
Leave a Comment