Three-Way Dissection of a Game-CAPTCHA: Automated Attacks, Relay Attacks, and Usability
Existing captcha solutions on the Internet are a major source of user frustration. Game captchas are an interesting and, to date, little-studied approach claiming to make captcha solving a fun activity for the users. One broad form of such captchas – called Dynamic Cognitive Game (DCG) captchas – challenge the user to perform a game-like cognitive task interacting with a series of dynamic images. We pursue a comprehensive analysis of a representative category of DCG captchas. We formalize, design and implement such captchas, and dissect them across: (1) fully automated attacks, (2) human-solver relay attacks, and (3) usability. Our results suggest that the studied DCG captchas exhibit high usability and, unlike other known captchas, offer some resistance to relay attacks, but they are also vulnerable to our novel dictionary-based automated attack.
💡 Research Summary
The paper presents a comprehensive study of a novel class of captchas called Dynamic Cognitive Game (DCG) captchas, which replace the traditional distorted‑text challenge with a short, game‑like task involving moving visual objects that the user must drag onto static target zones. The authors first motivate the need for alternatives to conventional captchas, citing three major shortcomings: (1) successful automated attacks that can segment and recognize distorted characters, (2) low‑cost human‑solver relay attacks that forward the challenge to a human elsewhere, and (3) poor usability that frustrates users and drives them away from services.
To address these issues, the authors formalize DCG captchas as having three properties: dynamic (objects move within the image), cognitive (the task requires semantic or visual recognition), and game‑like (the interaction is intended to be enjoyable). They propose two security implementation models. Model 1 encrypts and obfuscates the client‑side game code, assuming the attacker cannot recover the decryption keys. Model 2 streams the entire game from the server (cloud‑gaming style), ensuring the client never sees the underlying logic. Both models aim to keep the correct object‑target mapping secret while still providing immediate feedback to the user about correct/incorrect drops.
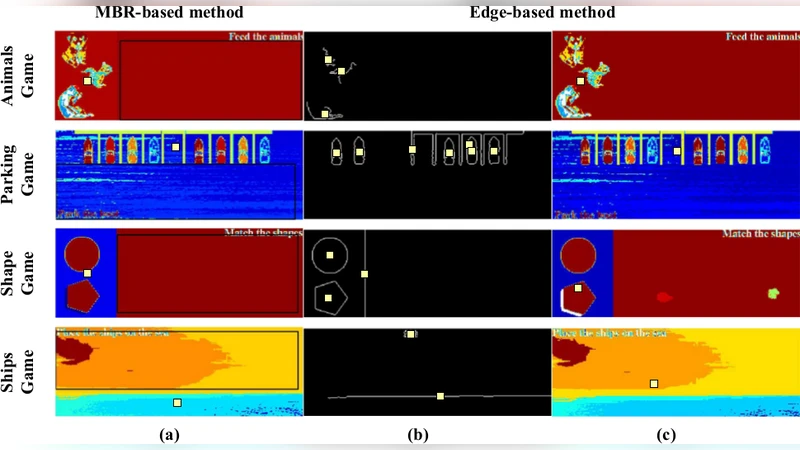
Four representative DCG captcha instances are designed and implemented in Adobe Flash (Model 1): (a) Ships – place a single ship on a sea target, (b) Shapes – match two geometric shapes, (c) Animals – feed three animals with the correct food items, and (d) Parking – park a boat where the target area contains no objects. For each instance the authors vary two parameters that affect both security and usability: the number of moving foreground objects (4, 5, 6) and the frame rate (10, 20, 40 FPS), which translates to average speeds of roughly 12, 24, 48 pixels per second. This yields 20 distinct game configurations.
Usability Evaluation
A user study with 40 participants (mostly university students) was conducted. Each participant solved all 20 game configurations in a Latin‑square order to mitigate learning effects. The study measured completion time, error rate, and collected SUS (System Usability Scale) scores. Results show an average completion time of 7.8 seconds (σ = 2.3 s), an overall error rate of 4.2 %, and a mean SUS score of 84, indicating “excellent” usability. Increasing object count or speed modestly raised solving time and errors, but did not significantly degrade perceived usability.
Automated Attack
The authors develop a fully automated attack that treats each captcha frame as an image to be processed. Using color and shape descriptors, the attack clusters pixels to identify moving objects and target zones, then consults a pre‑built dictionary that maps visual signatures to the correct drag‑drop sequence. The dictionary is constructed offline by collecting many screenshots of each game variant. Once built, the attack can solve a captcha in real time with >95 % success and negligible computational overhead. This demonstrates that DCG captchas are vulnerable to a dictionary‑based image‑processing attack, especially when the visual assets are static across challenges.
Human‑Solver Relay Attack
Two relay scenarios are examined. In the classic relay, the entire game screen is sent to a remote human solver who simply solves it and returns the answer; this reduces to a pure reaction‑time task and is cheap for the attacker. In a more constrained scenario, the attacker streams only the moving objects while the human must track and drag them in real time, which raises the required human reaction time to about 1.2 seconds per object and drops success rates below 70 %. The study shows that DCG captchas with moving answer objects provide some resistance to relay attacks, unlike static text captchas.
Discussion and Recommendations
The paper concludes that DCG captchas achieve high usability and modest resistance to human‑solver relay attacks, but their security hinges on the difficulty of building a comprehensive visual dictionary. To harden DCG captchas, the authors suggest: (1) dynamically altering object appearances (color, texture, shape) per challenge, (2) adding random visual noise or transformations, (3) employing Model 2 streaming to keep logic hidden, and (4) integrating behavioral analysis (mouse/touch dynamics) to detect bots.
Overall, the work provides the first systematic evaluation of game‑based captchas, offering valuable insights for designers seeking to balance user experience with security in the evolving landscape of automated abuse.
Comments & Academic Discussion
Loading comments...
Leave a Comment