Forensic Analysis of Phone Call Networks
In the context of preventing and fighting crime, the analysis of mobile phone traffic, among actors of a criminal network, is helpful in order to reconstruct illegal activities on the base of the relationships connecting those specific individuals. Thus, forensic analysts and investigators require new advanced tools and techniques which allow them to manage these data in a meaningful and efficient way. In this paper we present LogAnalysis, a tool we developed to provide visual data representation and filtering, statistical analysis features and the possibility of a temporal analysis of mobile phone activities. Its adoption may help in unveiling the structure of a criminal network and the roles and dynamics of communications among its components. By using LogAnalysis, forensic investigators could deeply understand hierarchies within criminal organizations, for example discovering central members that provide connections among different sub-groups, etc. Moreover, by analyzing the temporal evolution of the contacts among individuals, or by focusing on specific time windows they could acquire additional insights on the data they are analyzing. Finally, we put into evidence how the adoption of LogAnalysis may be crucial to solve real cases, providing as example a number of case studies inspired by real forensic investigations led by one of the authors.
💡 Research Summary
The paper addresses the growing need for advanced forensic tools capable of handling massive mobile phone call logs in criminal investigations. It introduces LogAnalysis, a Java‑based platform that integrates visual network exploration, social network analysis (SNA) metrics, and temporal filtering to help investigators uncover the structure, key actors, and dynamic behavior of phone‑call networks.
The authors begin by outlining how mobile devices are exploited by organized crime and how telecom operators retain detailed call‑detail records (CDRs) that can be transformed into graph representations where nodes correspond to phone numbers and edges to communications. Traditional forensic workflows often rely on textual queries or static reports, which become unwieldy when dealing with millions of records. Existing tools such as i2 Analysts Notebook, COPLINK, TRIST, GeoTime, and NodeXL provide various visual or analytical capabilities, but none combine full‑graph visualization, interactive SNA ranking, and fine‑grained temporal slicing specifically for telecom data.
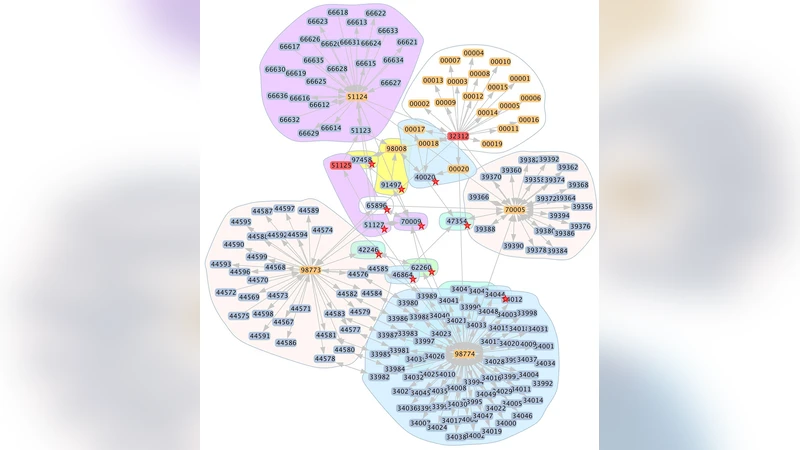
LogAnalysis fills this gap through a three‑layer architecture: (1) data ingestion parses raw CDR files and converts them to GraphML, a portable XML‑based graph format; (2) a processing layer uses the open‑source Prefuse library for dynamic graph layouts (force‑directed and radial) and the JUNG library for computing SNA measures such as degree, betweenness, closeness, eigenvector centrality, and community detection via modularity optimization; (3) a user interface presents the graph with customizable visual encodings (node size, color, edge thickness) and provides a time slider that lets analysts focus on arbitrary windows, observe bursts of activity, and trace the evolution of sub‑communities before, during, and after a crime event.
The implementation emphasizes extensibility: developers can plug in additional metrics or import alternative data sources, while the GraphML backbone ensures compatibility with other graph tools. The system also supports filtering by node attributes (e.g., subscriber type) and edge attributes (e.g., call duration), enabling rapid isolation of suspicious patterns.
To demonstrate practical utility, the authors describe five real‑world case studies drawn from investigations led by one of the authors. In the first case, LogAnalysis identified a “bridge” node that linked two otherwise separate gangs, revealing a hidden liaison who facilitated coordination across the groups. In a second scenario, temporal analysis highlighted a sharp increase in call volume within a 48‑hour window preceding a planned robbery, providing a timeline of operational planning. A third case used narrow time windows to expose a series of short, repetitive calls between two numbers, suggesting a covert channel for exchanging encrypted messages. The remaining cases illustrated the tool’s scalability: even with datasets containing hundreds of thousands of calls, the combination of layout optimization and interactive filtering allowed investigators to pinpoint dominant clusters, monitor community re‑formation after arrests, and generate visual evidence admissible in court.
The discussion acknowledges several limitations. Data preprocessing can be fragile when CDR formats vary across providers, requiring custom parsers. Rendering performance degrades with very large graphs, indicating a need for GPU‑accelerated layouts or hierarchical aggregation techniques. Moreover, LogAnalysis currently lacks geographic mapping, which limits its ability to correlate movement patterns with network dynamics—a feature present in tools like GeoTime. The authors propose future work that integrates GIS layers, adopts streaming analytics for near‑real‑time monitoring, and explores machine‑learning‑driven anomaly detection to complement the visual approach.
In conclusion, LogAnalysis represents a significant step forward for forensic analysts dealing with phone‑call networks. By unifying visual exploration, quantitative SNA metrics, and temporal slicing within a single, user‑friendly environment, it enables faster identification of central actors, hidden sub‑structures, and time‑dependent communication patterns—capabilities that are essential for modern crime fighting and that have already proven effective in real investigative contexts.
Comments & Academic Discussion
Loading comments...
Leave a Comment