An efficient dynamic ID based remote user authentication scheme using self-certified public keys for multi-server environment
Recently, Li et al. analyzed Lee et al.’s multi-server authentication scheme and proposed a novel smart card and dynamic ID based remote user authentication scheme for multi-server environments. They claimed that their scheme can resist several kinds of attacks. However, through careful analysis, we find that Li et al.’s scheme is vulnerable to stolen smart card and offline dictionary attack, replay attack, impersonation attack and server spoofing attack. By analyzing other similar schemes, we find that the certain type of dynamic ID based multi-server authentication scheme in which only hash functions are used and no registration center participates in the authentication and session key agreement phase is hard to provide perfect efficient and secure authentication. To compensate for these shortcomings, we improve the recently proposed Liao et al.’s multi-server authentication scheme which is based on pairing and self-certified public keys, and propose a novel dynamic ID based remote user authentication scheme for multi-server environments. Liao et al.’s scheme is found vulnerable to offline dictionary attack and denial of service attack, and cannot provide user’s anonymity and local password verification. However, our proposed scheme overcomes the shortcomings of Liao et al.’s scheme. Security and performance analyses show the proposed scheme is secure against various attacks and has many excellent features.
💡 Research Summary
This paper presents a comprehensive security analysis of a specific type of multi-server remote user authentication scheme and proposes a novel, more robust alternative. The work begins by critically examining a dynamic ID-based authentication scheme proposed by Li et al., which is designed for multi-server environments and operates without the active participation of a Registration Center (RC) during the authentication phase, relying solely on hash functions.
The cryptanalysis reveals that Li et al.’s scheme is susceptible to several serious attacks under a reasonable adversary model. The authors demonstrate that if an adversary can compromise one user and one server (or is a malicious insider), they can obtain long-term system secrets like h(x||y) and h(y). With these secrets and information extracted from a stolen user smart card (containing values like b and h(y)), the adversary can mount an offline dictionary attack. By intercepting a legitimate login request from the public channel, the attacker can reverse-engineer values to recover the user’s true identity (ID_i) and password (PW_i). This complete breach enables subsequent replay attacks (reusing the intercepted login message), user impersonation attacks (creating new login requests), and server spoofing attacks (faking server responses). The paper further notes that other similar hash-based, non-RC-dependent schemes by Shao et al. and Lee et al. suffer from the same fundamental flaws. The core insight is that constructing a perfectly secure and efficient dynamic ID-based, non-RC-dependent scheme using only hash functions is inherently difficult.
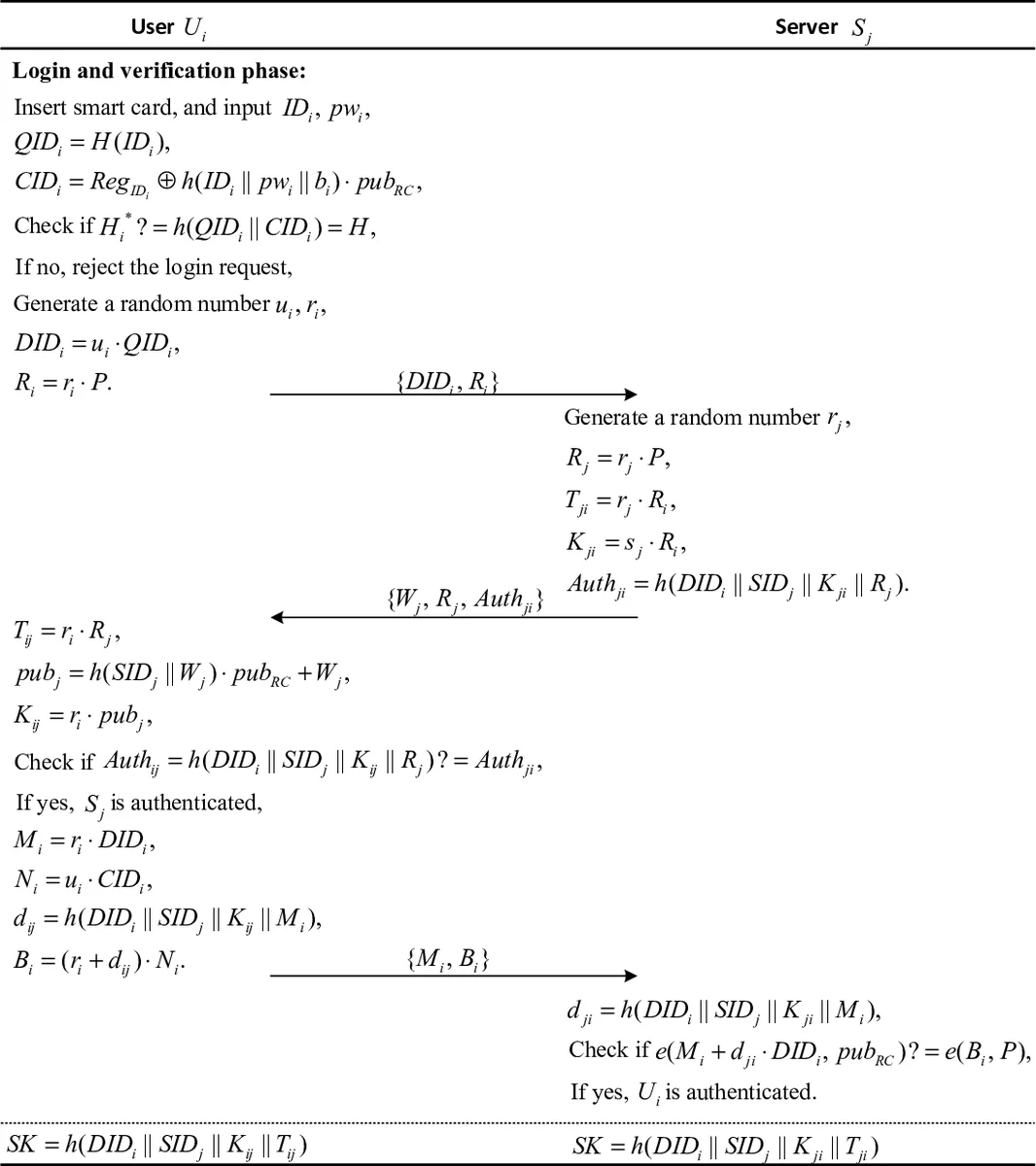
To address these shortcomings, the authors propose an improved scheme. They choose Liao et al.’s scheme as a foundation, which utilizes bilinear pairings and self-certified public keys—a shift towards public-key cryptography. However, Liao et al.’s scheme itself is found vulnerable to offline dictionary attacks and denial-of-service (DoS) attacks, and it lacks user anonymity and local password verification. The novel scheme presented in this paper enhances Liao et al.’s work in several key ways. It strengthens the dynamic ID mechanism to ensure user anonymity and untraceability across different sessions. It incorporates a local password verification step on the smart card itself, which immediately rejects incorrect passwords, thereby preventing unnecessary server requests and mitigating a vector for DoS attacks. The proposed protocol facilitates mutual authentication and session key agreement between the user and the server without requiring the RC’s online involvement.
A detailed security analysis follows, arguing that the new scheme resists a wide range of known attacks, including smart card theft, replay attacks, impersonation attacks, server spoofing, insider attacks, and man-in-the-middle attacks. While the use of pairing operations introduces higher computational cost compared to hash-only schemes, the paper contends that this is a reasonable trade-off for the significantly enhanced security and the additional features provided, such as true anonymity and local verification. In conclusion, this research highlights the critical vulnerabilities in simplistic hash-based authentication architectures for complex multi-server environments and provides a concrete, more secure alternative leveraging pairing-based cryptography and self-certified keys.
Comments & Academic Discussion
Loading comments...
Leave a Comment