VoIP Steganography and Its Detection - A Survey
Steganography is an ancient art that encompasses various techniques of information hiding, the aim of which is to secret information into a carrier message. Steganographic methods are usually aimed at hiding the very existence of the communication. Due to the rise in popularity of IP telephony, together with the large volume of data and variety of protocols involved, it is currently attracting the attention of the research community as a perfect carrier for steganographic purposes. This paper is a survey of the existing VoIP steganography (steganophony) methods and their countermeasures.
💡 Research Summary
The surveyed paper provides a comprehensive overview of steganographic techniques that exploit Voice over IP (VoIP) as a covert communication channel, together with the state‑of‑the‑art detection and mitigation methods. After introducing the motivation—namely, the high data volume, protocol diversity, and real‑time nature of IP telephony—the authors dissect the VoIP stack (SIP, SDP, RTP/RTCP, SRTP) and the most common audio codecs (G.711, G.729, Opus, etc.) that can serve as carriers. They categorize existing “steganophony” methods into four principal families.
-
Codec‑based hiding manipulates the internal representation of voice frames. Techniques include Least‑Significant‑Bit (LSB) replacement, quantization‑error embedding, codebook index alteration, and parameter‑level modulation. These approaches generally offer high payload capacity and straightforward implementation, but they risk detectable audio quality degradation, especially when the codec’s error‑concealment mechanisms are triggered.
-
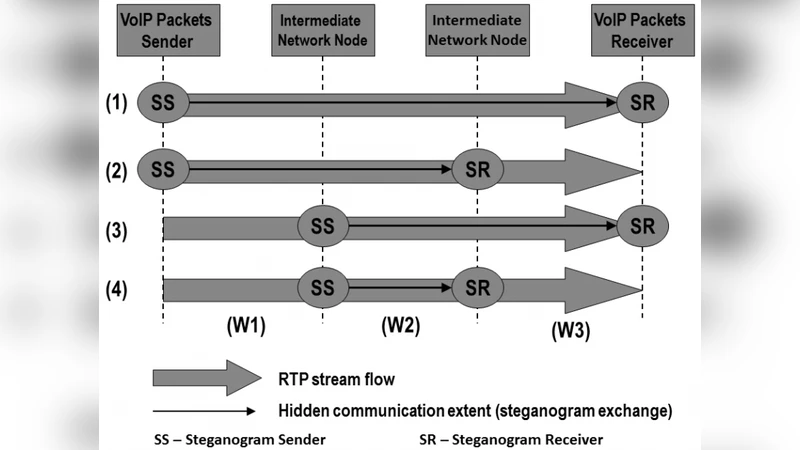
Header‑based hiding exploits mutable fields in RTP (sequence number, timestamp, SSRC) or SIP messages. By staying within the permissible ranges defined by the standards, the modifications can evade simple checksum or sanity checks. However, network middleboxes that normalize or rewrite headers may unintentionally strip the hidden data.
-
Timing/flow‑based hiding encodes information in packet inter‑arrival times, deliberate jitter, or controlled packet loss patterns. Because the payload remains untouched, this method preserves codec‑level integrity and is compatible with encrypted streams (SRTP). Its main drawback is sensitivity to natural network latency variations, which can corrupt the covert signal.
-
Hybrid/multi‑layer approaches combine two or more of the above techniques, or embed additional layers inside already encrypted RTP payloads. While these schemes dramatically increase stealth, they also raise computational overhead and implementation complexity.
On the detection side, the survey outlines four major strategies. Statistical analysis builds models of expected LSB distributions, RTP timestamp variance, or inter‑arrival time histograms and flags deviations. Machine‑learning classifiers extract feature vectors (e.g., header entropy, spectral differences in decoded audio, timing jitter) and train supervised models to separate benign from steganographic traffic. Pattern‑matching looks for known signatures of specific embedding algorithms, while protocol‑normality verification checks whether header fields obey protocol specifications. The authors note that most detection methods struggle with encrypted VoIP (SRTP), where payload‑level cues are unavailable and only header or timing anomalies can be examined.
The paper evaluates each technique along four axes—stealthiness, capacity, robustness, and real‑time suitability—presenting a comparative matrix. Codec‑based LSB methods score high on capacity and stealth but low on robustness under network impairments. Header‑based schemes are moderately robust and maintain real‑time performance, whereas timing‑based methods excel in stealth but offer limited bandwidth. Hybrid solutions achieve balanced scores but are the most demanding to implement.
In conclusion, the authors identify the combination of codec LSB manipulation with subtle RTP header tweaks as the most practical current approach, given its trade‑off between payload size and detectability. They emphasize that detection technologies lag behind embedding techniques, especially in encrypted environments. Future research directions include developing multi‑layer detection frameworks, lightweight real‑time machine‑learning models, and deeper protocol‑normality analyses that can operate under SRTP. The survey thus serves both as a reference map of existing steganophony methods and a call to action for more robust, scalable countermeasures.
Comments & Academic Discussion
Loading comments...
Leave a Comment