Keys through ARQ: Theory and Practice
This paper develops a novel framework for sharing secret keys using the Automatic Repeat reQuest (ARQ) protocol. We first characterize the underlying information theoretic limits, under different assumptions on the channel spatial and temporal correl…
Authors: ** (논문에 명시된 저자 정보가 제공되지 않아, 여기서는 “저자 정보 미제공”으로 표기합니다.) **
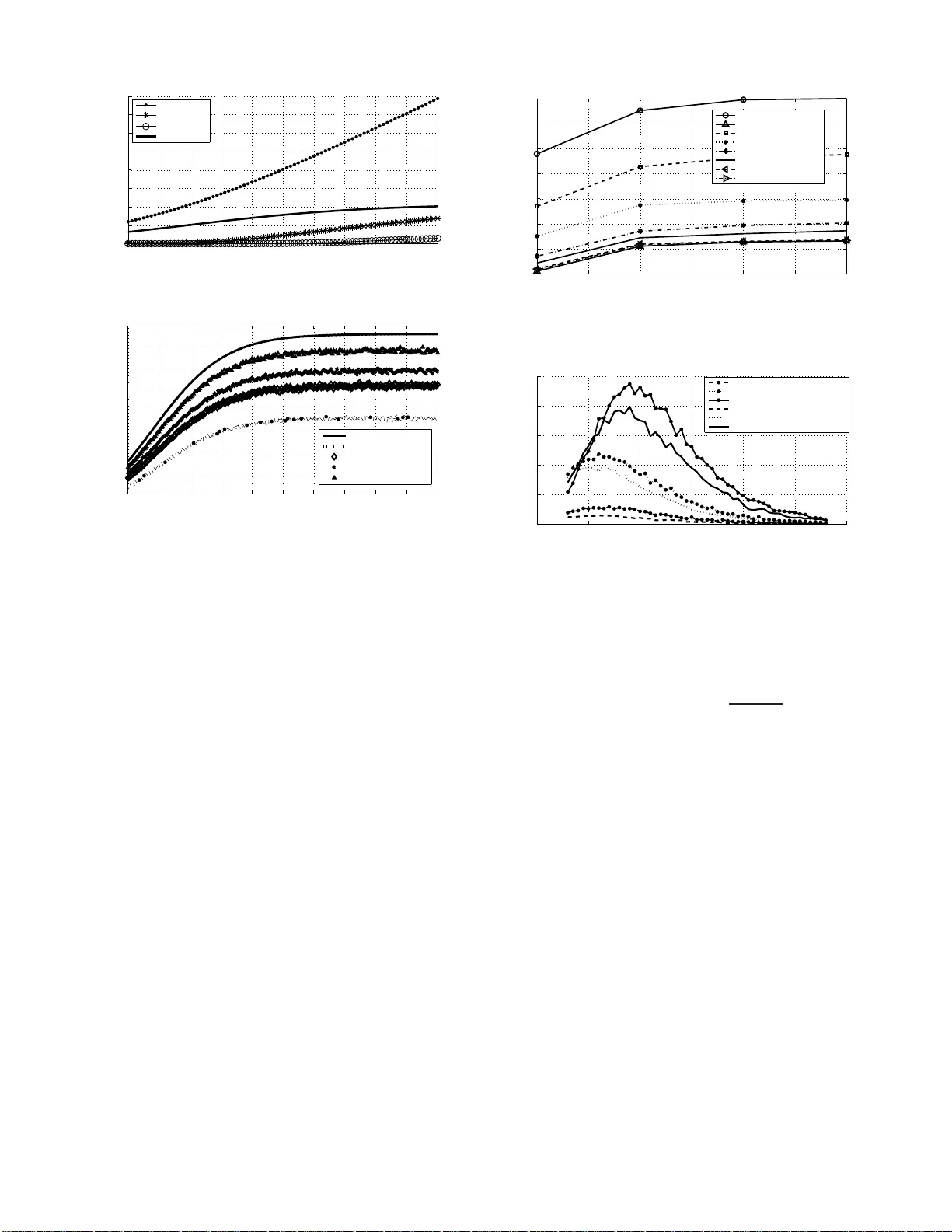
1 K e ys through ARQ: Theory and Pract ice Y ara Abdallah*, Student Member , IEEE, Mohame d Abdel Latif, Student Member , IEEE, Moustafa Y oussef, Senior Member , I EEE, Ahme d Sultan, Member , IEEE, and Hesham El Gama l, F ellow , IEEE Abstract —This paper develops a nov el framework for sharing secret keys using the Automatic Repeat reQuest (ARQ) p roto- col. W e first characterize the und erlying informa tion th eoretic limits, under different assumpt ions on the chann el spatial and temporal correla tion functi on. Our analysis re veals a n ov el role of “dumb antennas” in o vercoming the negativ e impact of spatial correlation on the achiev able secrecy rates. W e fu rther deve lop an adaptive rate allocation policy , which achi ev es higher secrecy rates in temporally correlated channels, and explicit constructions f or ARQ se crecy co ding that enjoy lo w imple- mentation complexity . Buildin g on this theoretical foundation, we propose a unified framewor k for ARQ-based secrecy in Wi- Fi networks. By exploitin g the existing ARQ mechanism in the IEEE 80 2.11 stand ard, we de ve lop securit y over lays that offer stro ng security guarantees at the expense of only min or modifications in the medium access layer . Our n umerical results establish the achievability of n on-zero secrecy rates even when the ea vesdr op per channel is less noisy , on the av erage, than the legitimate channel, while our li nux-based prototype demonstrates the efficiency o f our ARQ o verlays in mitigating all kno wn, passiv e and active, Wi-Fi attacks at the expense of a mini mal increase in the link setup t ime an d a small loss in throughput. I . I N T RO D U C T I O N The recent flurry o f interest on wireless physical layer secrecy is inspired by W yner’ s pio neering work on the wiretap channel [1] wh ich establishes th e achievability of perf ectly secure com munication b y h iding the message in the a dditional noise le vel seen b y the eavesdropper . Mo re re cently , the effect of fading on th e secrecy capacity was stud ied in wh ich it was shown that, b y approp riately distributing the message across different fading r ealizations, the m ulti-user div ersity gain can be harnessed to enh ance th e secrecy cap acity , e.g . [2], [3]. Indepe ndent an d para llel to ou r work, the autho rs of [4], [5], [6] co nsidered using the well-known Hybrid ARQ protoc ol to facilitate th e exchange of secure messages over fading channels. One innovati ve aspect of our framework, com pared to [4], is the distrib ution o f key bits over an asy mptotically large number of ARQ epochs. This approach allows for This work is funded in part by NSF , QNRF , USAID and the Egyptian Science and T echnol ogy De velopment Fund (STDF) unde r the US-Egypt Joint Research Grants Program. T he materia l in this paper was presented in part at the Communication theory symposium, Interna tional Conference of Communications, Dresden, Germany , June, 2009, the IEEE Informati on Theory W orkshop, T aormina, Sicily , Italy , October , 2009 , and the IEEE Information T heory W orkshop, C airo, Egypt, January , 2010. Y . Abdalla h, M. Y oussef and A. Sult an are with the W ireless Intelli gent Net- works Cent er (WINC), Nile Unive rsity , Cairo, Egypt (e-mail: yara.a bdalla h, asultan , mayoussef @nileu.edu.e g). M. Abdel Latif was with the Wirel ess Intellige nt Netw orks Center (WINC), Nile Univ ersity , Cairo, Egypt and is now with the Department of Electric al and Compute r Engineerin g, Univ ersity of Cali fornia, Irvine, CA, 92717 USA (e-mail: m ohamed.abde llati f@uci.edu ). H. El Gamal is with the Department of E lectri cal and Computer Engi- neering , Ohio State Univ ersity , Columb us, OH, 43210 USA (e-mail: helga- mal@ece .osu.edu). overcoming the secrecy ou tage pheno menon observed in [ 4] at the expense of incr eased d elay . Contr ary to [6], we build an informa tion theoretic foun dation for key sharing th rough ARQ which inspires lo w complexity imple mentation of practical coding schem es and reveals a novel role of dum b antenn as in overcoming the negati ve impact of spatial cor relation, between the legitimate and ea vesdropper chan nels, on the achie vable key rate. Moreover, we propose a new greedy rate adaptatio n algorithm tha t is capable of transfo rming the temporal co rre- lation in th e legitimate chann el into add itional gains in the secrecy rate. Building on our information theoretic foundation, we de - velop a unified ARQ secu rity framew ork for W i- Fi networks (ARQ-seCuRity fOr W irele ss Network s: ARQ-CRO WN); an- other d istinguishing featu re o f ou r work as comp ared with [ 4], [5], [6]. This framew ork is used to co nstruct security overlays which provide informa tion theor etic co nfidentiality g uarantees to comp lement the un derlying W i-Fi security pr otocols. More specifically , care ful analy sis of the state o f the art attacks o n these pro tocols (e.g., [7], [8], [9]) reveals that they depend critically on the a vailability of certain security par ameters as plain text in the tr ansmitted packets. By judiciously using the av ailable ARQ mech anism in th e IEEE 802.1 1 standard, our overlays transfo rm those security parameters in to a secret key that is shared on ly by the legitimate nodes. Remarkably , this goal is achieved throu gh on ly minor modification s in the MA C layer that treat all p rotocols unif ormly , and hence, does not entail additional n etwork manag ement tasks. T he exper- imental resu lts, ob tained from ou r Madwifi driver prototype, demonstra te the ability of ARQ-CRO WN to def end against all known ea vesdropping attacks (whether acti ve or passi ve), at the expen se of a mino r loss in through put and a small incr ease in link setup time. This, to the best of our k nowledge, th e first attempt to demon strate the utility o f in formatio n theoretic security concep ts in practice. The remaind er of this pape r is organized as follows. W e develop our information theoretic foundation in Section II. The design o f our A RQ secrecy fram ew o rk for W i- Fi network s is p resented in Section III. Our num erical and experimental results are gi ven in Section IV . Section V of fers some conclud- ing rema rks whereas the p roofs are co llected in the app endices to enhance the flow of the paper . I I . I N F O R M AT I O N T H E O R E T I C F O U N DAT I O N A. S ystem Model and Notation s Our mo del assumes o ne tran smitter (Alice), on e legitimate receiver (Bob), and one p assi ve eavesdropper (Eve). W e adopt a block fading mo del in wh ich e ach channel is assumed to be fixed over one coherence in terval and changes from on e 2 interval to the next. I n order to obtain rigorou s informatio n theoretic r esults, we consider the scenario of asympto tically large cohere nce intervals and allow for sharing the secret key across an asymp totically large nu mber of those intervals. The finite delay case will be considere d in Section II-D. In any particular interv al, the signals received b y Bob and Eve are respectively given by , y ( i, j ) = g b ( i ) x ( i, j ) + w b ( i, j ) , z ( i, j ) = g e ( i ) x ( i, j ) + w e ( i, j ) , where x ( i, j ) is the j th transmitted symbo l in the i th block, y ( i, j ) is the j th received symbol by Bob in the i th block, z ( i, j ) is the j th received symb ol by Eve in th e i th block, g b ( i ) an d g e ( i ) are the co mplex block channel gain s from Alice to Bob and Eve, respectively . Th e chan nel gains can also be wr itten as g b ( i ) = p h b ( i ) exp( j θ b ( i )) , an d, g e ( i ) = p h e ( i ) exp( j θ e ( i )) , where θ b ( i ) and θ e ( i ) , the ph ase shifts at Bob and Eve respectively , are assumed to b e indep endent in all conside red scenarios. Moreover , w b ( i, j ) and w e ( i, j ) are the zero-m ean, unit variance white complex Gaussian noise coefficients at Bob and Eve, respectively . W e do not assume any prior knowledge abo ut the chann el state in formation at Alice. Bob, howe ver , is assumed to kn ow g b ( i ) and Eve is assumed to kn ow bo th g b ( i ) and g e ( i ) a-priori . W e impose the following sho rt-term av erage power con straint E | x ( i, j ) | 2 ≤ ¯ P . Our mod el only allows for on e bit o f ARQ f eedback fro m Bob to Alice. Each ARQ epoch is assumed to b e containe d in one coheren ce inter val (i.e., fixed channel g ains) and that different epochs corr espond to different coherence intervals. The trans- mitted packets are assumed to car ry a perf ect error detection mechanism allowing Bob (and E ve) to d etermine wheth er the packet has b een received correctly o r not. Bob sends back to Alice an A CK/NA CK bit, throu gh a public feedback c hannel which is o nly accessible by Bob but Mon itored by E ve. T o minimize Bob’ s rece i ver complexity , we ad opt the mem oryless decodin g assumption implying that f rames r eceiv ed in erro r are discarded and not used to aid in future decoding attempts. Finally , Ev e is assum ed to be passi ve (i.e., c an not tran smit); an assumption which can be justified in se veral pr actical setting s. W e will argue in Section III, h owe ver, that our approac h can mitigate all known acti ve attack s on W i-Fi networks as well. In ou r setup, Alice wishes to share a secre t key W ∈ W = { 1 , 2 , · · · , M } with Bob . T o tran smit this key , Alice and Bob use an ( M , m ) cod e con sisting o f : 1) a stochastic encod er f m ( . ) at Alice that m aps the key w to a codew ord x m ∈ X m , 2) a d ecoding functio n φ : Y m → W wh ich is used b y Bob to recover the key . The codeword is partitioned into a blocks, each one correspon ds to one AR Q-epoch and contain s n 1 symbols where m = a n 1 . Unless oth erwise stated, we focus on the asym ptotic scenario wher e a → ∞ an d n 1 → ∞ . Alice starts with a r andom selection o f th e first block o f n 1 symbols. Upon r eception, Bob attem pts to dec ode this bloc k. If successful, it sen ds an A CK bit to Alice who moves ahead and makes a rando m choice of the second n 1 and sends it to Bob. Here, Alice must ma ke sure that the c oncatenatio n of the two b locks belong to a valid cod ew o rd. As shown in the sequel, this constraint is e asily satisfied. If an error was detected, then Bob send s a NA CK bit to Alice; in whic h case both Alice and Bob will discard this block. Alice will the n replace the first block of n 1 symbols with anoth er rand omly chosen b lock an d tr ansmits it. Th e pr ocess th en r epeats until Alice and Bob agree on a sequence of a blocks, each o f length n 1 symbols, corr esponding to the key . It is interesting to note that this strategy does not include any retransmissions . The optimality of this appr oach, as proved in ou r main r esults, hinges on this pr operty which minimizes the inf ormation leakage to Eve. The code con struction must allow for reliable deco ding at Bob while hiding the key fro m Eve. It is clear that the p roposed protoco l exploits th e error d etection mechanism to ma ke sur e that b oth A lice and Bob ag ree on th e key (i.e., ensures reliable decodin g). What r emains is the secrecy requirem ent which is measured by the equiv ocation rate R e defined as the entropy rate of th e tran smitted key conditioned o n the inter cepted A CKs o r N ACKs and the chann el ou tputs at Eve, i.e., R e ∆ = 1 n H ( W | Z n , K b , G b b , G b e ) , where n is the n umber of symbols transmitted to exchange the key (includ ing the symbols in the discarded b locks due to decodin g errors), b = a n m , K b = { K (1) , · · · , K ( b ) } denotes sequence of A CK/N AC K bits, G b b and G b e are the sequences of cha nnel coefficients seen by Bob and Eve in the b blocks, and Z n = { Z (1) , · · · , Z ( n ) } denotes Eve’ s c hannel o utputs in the n symbol intervals. W e limit our attentio n to the perfect secrecy scenar io, which requires the equiv ocation r ate R e to be arbitrarily close to the key rate. The secrecy r ate R s is said to be achievable if for any ǫ > 0 , there exists a sequence of codes (2 nR s , m ) such that for any m ≥ m ( ǫ ) , we hav e R e = 1 n H ( W | Z n , K b , G b b , G b e ) ≥ R s − ǫ , and the key rat e f or a giv en in put distribution is d efined as the max imum achie vable perfect secrecy rate with this distribution. B. Ma in Result Our main r esult is derived for the scen ario where the feedback ch annel is error f ree and h e , h b vary independently from on e block to a nother acco rding to a join t distribution f ( h b , h e ) . W e will conside r the ef f ect of spatial and tempo ral correlation in Section I I-C. T he following result character izes the Gaussian key rate under these assump tions. Theor em 1: T he key rate for the memoryless ARQ protoc ol with Gaussian inputs is given by: C ( g ) s = max R 0 ,P ≤ ¯ P E n R 0 − log 2 (1 + h e P ) + I R 0 ≤ log 2 (1 + h b P ) o , (1) for a fixed average power P ≤ ¯ P and tran smission rate R 0 . [ x ] + = max(0 , x ) and I ( x ) = 1 if x is tru e and 0 otherwise. For the special case of spatially ind epende nt fading, i.e. f ( h b , h e ) = f ( h b ) f ( h e ) ) the above expression simplifies to C ( i ) s = max R 0 ,P ≤ ¯ P n Pr R 0 ≤ log 2 (1 + h b P ) E R 0 − log 2 (1 + h e P ) + o . (2) 3 A few rem arks are now in order . 1) It is c lear f rom (1) that a p ositiv e secret key rate is achiev able under very mild condition s on the chann els experienced by Bob and Eve. More precisely , u nlike the approach p ropo sed in [4], Theorem 1 establishes the achiev ability of a po siti ve perfect secrecy r ate by approp riately exploiting the ARQ feed back even when Eve’ s a verage SNR is high er th an that of Bob. 2) Theorem 1 character izes the fundamenta l limit on secret key sharing and no t message tran smission. The differ- ence between the tw o scenarios stems from the f act that the message is known to Alice before starting the trans- mission of the first blo ck, wher eas Alice and Bob can defer the agreemen t on the key till the last successfully decoded b lock. This observation was exploited by ou r approa ch in mak ing Eve’ s observations of the fr ames discarded by Bob, du e to failure in deco ding, useless. 3) It is in tuitiv ely pleasing that the secrecy key rate in (2) is the pro duct of the proba bility of success at Bob and the expec ted value of t he add itional mutual informa tion gleaned b y Bob, as compared to Eve, in those successfully deco ded frames. 4) The achiev ability of (1) hinges o n a r andom binnin g argument which on ly establishes th e existence of a coding schem e that achiev es the desired rate. Our resu lt, howe ver, stops short o f explicitly find ing such optima l coding schem e and characterizing its en coding/d ecoding complexity . Th is observation motivates the development of the explicit secrecy coding schemes in Section II -D. 5) In the afor emention ed secu rity protoco l, using a no isy feedback channel will lead to mis-synch ronizatio n be- tween Alice and Bob. This problem ca n b e easily overcome at the expense o f a lar ger overhead in the feedfor ward channel. Alice w o uld inclu de all the history of rece i ved A CK/NA CK in each fra me. Once an A CK is received, Alice will b e assured that Bob has correctly received the past history . Alice will then flush the past history and will on ly inclu de the recen tly received A CK/NA CK message s in futur e transmissions. Addi- tionally , one may b e tempted to assume that the noisy feedback from Bob to Eve will allo w for increasing the secret key capacity . Unf ortunately , Eve can easily overcome the loss of AC K bits via an exhaustive trial and error appr oach. More rig orously , since the ratio of feedback b its over feed forward bits is v anishingly small, the loss of A CK b its will not lead to an incr ease in the equiv ocation at Eve. C. Spatial an d T emporal Corr ela tion One of the impo rtant insights re vealed by Theorem 1 is the negativ e relatio n between the achiev able key r ate and the spa- tial cor relation between the m ain and eav esdropper chann els. In fact, on e can easily verify that th e key ra te collap ses to zer o in the fully correla ted case (i.e., h b = h e with pro bability one) indepen dent of the marginal distrib ution of h b . In this section, we propose a solution to this problem based o n a nov el utilization of “dumb anten nas. ” The co ncept of dumb antenn as was introduced in [10] as a m eans to create artificial channel fluctuations in slow fading environments. These fluctuations are u sed to h arness o pportu nistic perfo rmance gains in m ulti- user cellular n etworks. As indicated by th e na me, one of the attractive featur es of th is approach is that the recei ver(s) can be oblivious to the presence of multiple transmit antennas [10]. W e use dumb transmit an tennas to de-correlate the main a nd eav esdroppe r chann els as follows. Alice is equ ipped with N transmit antennas, wh ereas both Bob and Eve still hav e only one rec ei ve antenna. In ord er to simplif y the presentation, we focus on the case of th e symmetric fu lly correlated line o f sight c hannels; wh ereby the magnitud es of th e chann el gains are all equal to o ne. The rest of our modeling assump tions remain as detailed in Section II-A. The same data stream is transmitted f rom the N transmitted after app lying an i.i.d unifor m phase to each of th e N signals. Also, Bob is a ssumed to perturb its location in each ARQ frame resulting in a random and indep endent p hase shift (fr om that experienced by Eve). Our multiple transmit antenna scenario, therefor e, reduces to a single anten na fading wiretap ch annel with the f ollowing equivalent cha nnel gains g eq b = N X n =1 1 √ N exp( θ iR + θ iB ) , g eq e = N X n =1 1 √ N exp( θ iR + θ iE ) , where θ iB , θ iE , and θ iR are i.i.d. and unifo rm over [ − π , π ] that remain fixed over one ARQ frame and chang e random ly from one ARQ frame to th e next. One can now easily see that as N in creases, th e margin al distribution of each equivalent channel gain appr oaches a zero-mea n complex Gaussian with unit v ariance (b y th e Central Limit Theo rem (CL T) [1 1]). I t is worth n oting that the co rrelation coefficient between the two channels’ equiv alen t po we r gains d epends on the instantaneous channels’ phases θ iB ’ s and θ iE ’ s for i = 1 , . . . , N . It can be easily sho wn th at, in the lim it o f N → ∞ , this correlatio n coefficient between the two channels power gains conv erges, in a mean- square sense, to zero (please ref er to Appendix B for the pro of). Theref ore, in the asym ptotic limit of a large N , our dumb an tennas approach has successfully tran sformed our fully co rrelated lin e of sight c hannel into a sy mmetric and spatially independent Rayleigh wiretap chann el; who se secrecy cap acity (assumin g Gaussian inputs) is r eported in Theorem 1 . T he numerical re sults rep orted in the sequel (Section IV -A) dem onstrate tha t this result is n ot lim ited to line of sight chan nels, and that th is asymptotic beh avior ca n be observed for a relatively small num ber of transmit antennas. Thus far, we have assumed that the chan nel gain s affecting different fr ames are independen t. This assumption ren ders optimal th e stationary rate alloca tion strategy o f Theo rem 1. In this section, we relax this assump tion by introducin g temporal correla tion b etween the chan nel gains e xperienc ed by successiv e frames. Assuming high temp oral correla tion, if a station ary rate strategy is emp loyed and it is less than Eve’ s channel capa city , all the in formatio n tra nsmitted will be leaked to Eve. On the othe r han d, if the rate is m uch less than Bob’ s cha nnel capacity , a dditional g ains in the secrecy 4 capacity will n ot be h arnessed. Hence, we are going to emp loy a rate a daptation strategy in which the op timal rate used in each f rame is deter mined b ased on the p ast histor y o f A CK/NA CK fee dbacks an d the rates used in previous blocks. More specifically , f ollowing in the footsteps of [ 12], the optimal rate allocation policy can b e formu lated as follows (assuming a short ter m average power constraint P and a Gaussian input distribution). R t = arg max R t ( C s,t + ∞ X k = t +1 C s,k ! R t − 1 , K t − 1 ) , ( 3) where C s,t = Pr R t ≤ lo g 2 (1 + h b,t P ) E h e R t − log 2 (1 + h e P ) + , where R t − 1 = [ R 0 , · · · , R t − 1 ] is the vector of previous transmission rates and K t − 1 = [ K 0 , · · · , K t − 1 ] is the vector of pr eviously r eceived AC Ks and N A CKs. The b asic idea is that, a fter frame ( t − 1 ) , the posterio ri d istribution o f h b is updated using R t − 1 and K t − 1 . The exp ected secrecy rate, in future transmissions, is the n maximized based on this updated distribution. It is worth noting that the ab ove expression assumes no spatial correlation between h e and h b . This assumption repr esents the worst c ase scenar io since it pr ev ents Alice from lear ning the chan nel gains impairing E ve th rough the ARQ feedb ack. Since the chan nel gain is not o bserved directly , but thr ough an ind icator in the form of ARQ feedb ack, the optim al rate assignment, when the ch annel is Mar kovian, is a Partially Observable Mar kov Decision Process (POMDP). The solu tion of th is POMDP is comp utationally intractab le except f or trivial cases. This mo ti vates the f ollowing greedy rate allocatio n p olicy R t = a rg max R t n C s,t R t − 1 , K t − 1 o . Interestingly , the numerical r esults repo rted in Section IV -A demonstra te the ability of th is simple strategy to harness significant pe rforman ce g ains in first ord er Markov channels. Note that the perfor mance of a ny rate allocation p olicy can be upperbou nded by the ergod ic capacity with tran smitter CSI (and short term average p ower co nstraint P ) , i.e., C er = E h e ,h b log 2 (1 + h b P ) − log 2 (1 + h e P ) + , (4) which is ach iev ed b y the optimal rate allocatio n policy R t = log 2 (1 + h b,t P ) . In fact, o ne can v iew the rate assignm ent policy of (3 ) as an attemp t to ap proach th e rate of (4) b y using the ARQ feed back to o btain a better estimate of h b,t after each fading blo ck. D. Ex plicit Coding Schemes This section de velops explicit secr ecy coding schemes th at allow f or sharing ke ys using th e underlyin g me moryless ARQ protoco l with realizab le en coding/d ecoding co mplexity and delay . W e proc eed in th ree steps. Th e first step replaces the random b inning construc tion, used in the achiev ability p roof of Theorem 1, with an explicit coset coding sch eme fo r the erasure-wiretap chan nel. This erasu re-wiretap chan nel is created by the AC K/N ACK feed back an d accou nts fo r th e computatio nal c omplexity a vailable to Eve. In the secon d step, we limit the decoding delay by d istributing the ke y bits over only a finite num ber of ARQ fram es. Finally , we replace the capacity ach ieving Gaussian channe l code with practical co ding schem es in the third step . Overall, o ur thr ee- step ap proach allows for a u seful per formanc e-vs-comp lexity tradeoff. The perfect secrecy r equiremen t used in the information the- oretic analysis does not impo se any limits on E ve’ s d ecoding complexity . The idea now is to exploit the finite comp lexity av ailab le at Eve in simp lifying the secrecy codin g scheme. T o illustrate the id ea, let’ s first assume that E ve can only afford maximu m likelihood (ML) decoding. He nce, su ccessful decodin g at Eve is only possible when R 0 ≤ lo g 2 (1+ h e P ) , for a given tran smit p ower level P . Now , using th e ide alized e rror detection mechanism, Eve will be able to id entify and erase the frames decod ed in error resultin g in an er asure wiretap channel model . In practice, Eve m ay b e able to go beyond the perfo rmance o f the ML decod er . For e xample, Eve can generate a list o f candidate cod ew ords a nd then use th e error detection mech anism, or other means, to id entify the c orrect one. In our setup, we quantify the com putational complexity of Eve by the amount of side infor mation R c bits per chann el use offered to it b y a Genie. With this side inf ormation, the erasure pro bability at Eve is given by ǫ = Pr ( R 0 − R c > lo g 2 (1 + h e P )) , (5) since now the chan nel has to sup ply only enou gh mu tual informa tion to close the gap between the transmission rate R 0 and the side info rmation R c . The ML p erforma nce ca n be obtained as a specia l case of (5) b y setting R c = 0 . It is now clear that using this idea w e have transformed our ARQ ch annel into an erasure-wire tap chan nel. In this equiv alent mo del, we ha ve a noiseless link between Alice and Bob, ensured by the idealized error detection algorithm, and an erasure chann el b etween Alice a nd Eve. The following r esult characterizes the achievable perfo rmance over th is channe l. Lemma 2: The secrecy c apacity fo r th e equ iv alen t erasure- wiretap chann el is C e = max R 0 ,P ≤ ¯ P R 0 E h I ( R 0 ≤ lo g 2 (1 + h b P ) ( R 0 − R c ≥ lo g 2 (1 + h e P )) i = max R 0 ,P ≤ ¯ P n R 0 Pr R 0 ≤ lo g 2 (1 + h b P ) , R 0 − R c > lo g 2 (1 + h e P ) o . In the ca se of spatially in depend ent channels, the above expression reduces to C e = max R 0 ,P ≤ ¯ P n R 0 Pr R 0 ≤ lo g 2 (1 + h b P ) Pr R 0 − R c > log 2 (1 + h e P ) o . (6) The pr oof follows fro m the classical result on th e er asure- wiretap channel [ 13]. I t is intu iti vely app ealing that the ex- pression in (6) is simply the pro duct of th e transmission rate per ch annel use, the pro bability of successful decoding at Bob, and the proba bility o f erasure at Eve. The main 5 advantage of this equiv alent model is that it lend s itself to the explicit coset LDPC coding scheme co nstructed in [ 14], [15], [16]. I n summa ry , ou r first low complexity construction is a concatenated co ding scheme where th e o uter code is a co set LDPC fo r secrecy an d the inner one is a capac ity achieving Gaussian code. Th e underlying memory less ARQ is used to create the erasure-wiretap c hannel mat ched to this concatenated c oding scheme . The second step is to lim it the dec oding dela y resulting from the distribution of key bits over an asymptotically large number of ARQ blocks in the previous ap proach . T o a void this problem, we limit th e number of ARQ frames used by the key to a finite num ber k . The implication for this choice is a no n-vanishing value for the secrecy outage probability . For example, if we encode the message a s th e syndr ome of the rate ( k − 1) / k parity chec k code, Eve will be completely blind about the key if a t least on e of the k A RQ frame s is erased [14], [ 15], [ 16] ( Here the distilled key is the mod ulo- 2 sum of the key parts receiv ed correctly) . Th e secrecy outage p robab ility , assumin g spatially independe nt ch annels, is therefor e P out = Pr min j ∈{ 1 ,...,k } log 2 (1 + h e ( j ) P ) > R 0 − R c , (7) where h e (1) ,..., h e ( k ) are i.i.d. random v ariables drawn accord- ing to th e marginal distribution of Eve’ s chann el. Assuming a Rayleigh fading distribution, we get P out = ex p − k P 2 R 0 − R c − 1 . (8) Under the same assumption, it is straightforward to see that the av erage nu mber o f Bernoulli trials required to tr ansfer k ARQ frames successfully to Bob is g iv en by N 0 = k exp 2 R 0 − 1 P , resulting in a key rate R k = R 0 N 0 = R 0 k exp − 2 R 0 − 1 P . (9) Therefo re, for a given R c and P , one can obtain a trad eoff between P out and R k by varying R 0 . Ou r thir d, an d fin al, step is to relax the assump tion of a c apacity ach ieving inner co de. Section IV -A rep orts num erical results with pr actical co ding schemes, includin g uncod ed transmission, with a finite frame length n 1 . Overall, these results demonstrate the ability of the propo sed proto cols to achieve near-optimal key rates, under very mild assum ptions, with r ealizable encodin g/decod ing complexity and bounded delay that are of p ractical relev ance. In the next sectio n, we introduc e an ARQ-b ased secrecy scheme fo r W i-Fi networks that builds, in p rinciple, on these protoco ls. I I I . A R Q S E C U R I T Y F O R W I - F I N E T W O R K S A. W i-Fi Se c urity: The State of the Art Before going in to th e details of ou r d esign, we provid e some necessary b ackgro und about the existing W i-Fi secur ity protoco ls. More specifically , we describe how “per-frame keys” are genera ted and the critical depend ence of all the currently -known eavesdropping attacks on weak nesses in the per-frame key gener ation mech anisms. In general, the security functions o f different W i-Fi p roto- cols could be separ ated into three layers, name ly , an authenti- cation layer , an access con trol layer and a WLAN layer [17]. In this paper, we focus o nly on the pro cesses in volved with encryp ting and decryp ting fram es, that a re found in th e WLAN laye r solely ( the W ired Equiv alent Priv acy (WEP) , the T empo ral Key Integrity Pro tocol (TKI P), and the Counter Mode w ith Ciph er Block Chaining Message Authenticatio n Code Protoco l ( CCMP) standards). The reader is referre d to [17] for details on the other two layers. W e refer to the overall processes of sending and receiving frames securely as encapsulation and decapsulation , respectively . Those pro cesses fall within WEP , TK IP (in WP A or WP A2) a nd CCMP (in WP A2). Fig ure 1 shows two abstract sche matic d iagrams of frame en capsulation and decapsulation which will b e u seful in describing the in tegration of the ARQ-CRO WN overlay with each of these p rotocols. 1) Sec u rity at the WLAN La y er: The encapsulation p rocess starts b y wh at we refe r to as “security param eters g eneration” , which is the first blo ck in Figu re 1(a). T he sole functio n of those gen erated param eters is to en sure the use o f a fresh ke y f or each frame. In the WEP p rotocol, a 2 4-bit value, called the Initialization V ecto r (IV), is gener ated in this step. TKIP generates a similar 48-b it value, c alled TKIP Sequence Counter (TSC), while CCMP gen erates the Packet Numbe r (PN), of length 4 8 bits as well. The WEP protocol do es not sp ecify how the I V sho uld be generated , although it reco mmends that the IV v alu e should be different for each fra me [ 18]. In TKIP and CCMP , b oth the TSC o r the PN are initialized b y an agreed-up on value and are in cremented by one for each new frame. There are two basic reason s f or incremen ting the TSC (or PN) versus using a rand om v alue. First, to ensure covering the entire sequence space. Second, and more importantly , to defend against r eplay attacks, as will b e illustrated sh ortly . Since tho se param eters will be needed for decapsulation at the recei ver , they ar e sent, in-the-clear , in a special security header ( H s ) that is inserted between the frame’ s MA C header and the encr ypted message. The remainder of the encapsulation process in volves frame k ey generation ( this is w here the secu rity par ameters are co mbined with so me secr et ro ot key , K s , to o btain a key for a sp ecific frame), encryp tion, a dding an Integrity C heck V alue (ICV) and possibly a Message I ntegrity Che ck ( MIC) value. W e refer the reader to [1 7] for a comp rehensive study on each o f tho se steps. At the rece i ver side (Figure 1(b )), the security param eters are extracted from the security head er . The WEP pro tocol does not perfor m any che cks on this value and directly proceeds to the next steps. Howe ver, for TKIP and CCMP , once the TSC (or the PN) is extracted from th e security head er , a check is perf ormed. If the recovered TSC ( PN) is less tha n the last receiv ed TSC (PN), the frame is c onsidered a r eplayed version o f a previous fram e and is discar ded . Subsequ ent decapsulation processes include decryption and ICV and MIC tests. Those tests serve as means to ensur e that the fra me has been de crypted co rrectly a nd has no t been maliciously tampered with. For the purpo se of this paper, we use the symbol V to refer to WEP’ s IV , TKIP’ s TSC or CCMP’ s PN. 6 (a) The enc apsulat ion process. (b) T he decapsulati on process. Fig. 1: WLAN- layer security function s. For a given fra me, M is the plain text, C is the cipher text, and F is the transmitted packet. H M AC and H s denote the MAC an d security header s for th at frame, respectively . 2) W i-F i S ecurity Atta cks: Borisov , Gold berg, and W agner first reported WEP design failures in [18]. They showed th at the ICV test fails to detect malicious attac ks and th at IV r euse allows fo r packet injec tion. Later , the first ke y recovery attack against WEP (the FMS attack) was presented b y Fluh rer, Mantin and Sham ir [19] using some weak nesses of the RC4 Ke y Schedu ling Algorithm. They also showed th e recovery of the WEP key be comes much e asier if some I Vs that satisfy certain pr operties (weak IVs) were used . The KoreK chopchop attack a ttempted at b reaking WEP using the CRC32 ch ecksum (the ICV test) [2 0]. K oreK also presen ted an other g roup of attacks that d o no t rely on weak IVs [ 21]. A ra ther efficient iterativ e alg orithm that recovers the WEP key was prop osed by Klein in [22]. On the other h and, the Bittau attack made use o f the frag mentation sup port o f IEEE 802.1 1 to br eak WEP [2 3]. Finally , Pysh kin, T e ws, an d W einm ann p resented more enh ancements to the Klein attack by using r anking technique s [7]. At the m oment, this recent attack is considered to be the most p owerful attack ag ainst WEP . Statistical WEP attacks, e.g. [1 9], could , in principle, use only passive ea vesdro pping in ord er to collect a large num ber of frames with known IVs. Howe ver, they often use injection or replay techniques to shorten the lis tening time. F or e xample, an attacker mig ht continuously replay c aptured ARP (Address Resolution Protocol) req uest pac kets. Consequ ently , the Ac- cess Poin t (AP) will begin to broad cast those ARP re quest packets, and IVs will be generated at a high er rate. Other WEP attacks do no t need a large number of IVs. Instead, they rely on injection , e.g., [20] or [23]. In 200 4, weaknesses in th e tempor al ke y hash o f TKIP were shown [24]. An attacker c ould use the k nowledge of a few keystreams and TSCs to predict the T emporal Key and the MIC Key u sed in TKIP . Later in 2 008, T e ws and Beck [2 5] made the first practical attack against TKIP . In a chopchop -like manner, an attacker c an recover the plaintext o f a shor t p acket and falsify it within ab out 12-1 5 minu tes, in a WP A network that supports IEEE 802.1 1e QoS features. In 20 09, a p ractical falsification attack against T KIP was p roposed [8], in which the Beck-T e ws attack was a pplied to a man-in -the-mid dle attack to target any WP A network. The latter attack takes about o ne minu te. CCMP arguably provides robust secu rity . Howe ver, a we akness in the nonce constru ction mechanism in CCMP was recently discov ered [9]. A predictable PN in CCMP was shown to d ecrease the effecti ve en cryption key length from 128 bits to 85 bits [9]. In su mmary , the previously me ntioned a ttacks rely o n collecting a large number of ciph ertext along with the cor- respond ing secur ity parameters which are sent in-the -clear , whether throug h passi ve eavesdropping or innovati ve activ e technique s. As detailed in the following section, the ARQ- CR OW N overlay solves this problem by explo iting th e oppor- tunistic secre cy princ iple resulting from the wireless multipath fading en v ironmen ts. B. A RQ-CR O WN: An Overview ARQ-CR OW N is designed f or W i- Fi networks op erating in in frastructure mo de that may use any of the IEEE8 02.11 security proto cols, i. e., WEP , TKIP or CCMP for encryp tion. The network is compo sed of one AP a nd L clien ts, in th e presence of on e attacker . The AP and all clients follow th e ARQ mechanism adopted in th e IEEE 802.11 standard, i.e., for each tran smitted frame , the rece i ver acknowledges the receip t of that fra me th rough a shor t AC K message. W e assume disabled retransmissions, i.e., if a time out ev ent o ccurs at the transmitter (th e data frame or th e ACK messag e were lost), it simply discar ds the cur rent fr ame and moves to furth er transmissions 1 . Ke y m anagemen t and re-keying policies ar e aspects th at fall outside the scope of this paper . F or th is r eason, we assume that once a wireless clien t is auth enticated and h as gain ed access to the network, it shar es roo t keys with the AP . Fro m 1 The ana lysis provide d in this pape r could be easil y extende d to the case of enabled ret ransmissions. 7 (a) The enc apsulat ion process. (b) T he decapsulati on process. Fig. 2: WLAN-layer security functio ns incorp orating the ARQ-CR O WN overlay . Th e shaded blocks represent ARQ-CR O WN modification s the simp lest settin g o f on e-key-for-all in th e WEP protoco l, to a rather com plicated key hierarc hy in WP A and WP A2, our d iscussion would b e on a per-frame ba sis. Hence, we assume that, f or each fra me, the client an d the AP ag ree on which key is used to encapsulate/d ecapsulate th is f rame. Throu ghout the seq uel, this secret key is referred to as K s . In the proposed ARQ-CR O WN ov erlay , we tran sform the V values of dif ferent fram es into addition al private ke ys that are shared among th e legitimate node s. ARQ-CR O WN entirely focu ses on the V v alue of each fr ame, leaving the secret ro ot key , K s , un altered. Figure 2 shows the modified WLAN layer when overlaid b y A RQ-CR OW N. Th e figu re shows three ne w separate modules that run independently from the encapsulation a nd decapsulation pr ocesses; n amely , an initialization mod ule, an ACK/T imeout detectio n module and a grou p update module. Those modules interact solely with the security parameters generation and extraction blocks that are modified to incorpo rate ARQ security . O utputs of those steps are fed to the remainin g fu nctional blocks of en capsulation and dec apsulation, which rem ain exactly the same as in the original stan dards. For ease o f p resentation, we begin by using a simple three- node network mode l. In this ne twork, Alice correspo nds to o ne legitimate clien t, Bob corresp onds to the AP and Eve is a malicious attacker . W e late r show how to extend o ur scheme to secu re multicast flows. The initialization m odule work s on letting Alice an d Bob agree o n an initial value, V 0 , that will be later used in securing unicast flows in the Alice-Bob and Bob- Alice directions. It runs, only on ce, after Alice is associated a nd authenticated and before data po rts are open. In essence, the process is similar to the one descr ibed in Section II-A but with some modifications that better utilize the MAC lay er of the IEEE 802 .11 standard and that tak e into acco unt dealin g with an acti ve eavesdropper, as will be clear with fu rther discussion. Once this in itialization phase is comple te, secur e da ta com munication is allo wed. The A CK/T imeo ut detectio n mo dule runs du ring open data sessions. It works on deciding on the status of each transm itted Fig. 3: The ARQ-CR O WN initialization phase. unicast fr ame, which is ref erred to as Q . T his status help s both Alice and Bob update the V v alues for the unicast frames they exchang e, for each tr ansmitted frame. Finally , the group update modu le allo ws for securin g multicast data. In the f ollowing section, we show ho w each of th ose modules operate and rigor ously an alyze their security . C. ARQ- CR O WN: Operation an d Security Analysis 1) The Initialization Ph ase: The initializatio n phase works as illustrated in Fig ure 3. First, Alice tra nsmits an initialization frame, c arrying a seq uence nu mber 1 and random n umber R 1 , and starts a timer . Once Bob r eceiv es this fr ame, he replies with an other initialization frame, carryin g a sequ ence numb er 2 , and ano ther rando m number R 2 . If Alice r eceiv es this frame before a timeout event occu rs, she stores the pair ( R 1 , R 2 ) for later use, and tr ansmits an other initialization frame with sequence numbe r 3 and a new random number R 3 . Otherwise 8 (a tim eout event occu rs), Alice d iscards R 1 , and transm its another initializatio n frame with sequen ce n umber 1 and a new rand om numb er R 3 . Th e process co ntinues till Alice has stor ed n in itialization ran dom values. On the other side, Bob keeps on respo nding to each initialization frame he gets with a sequenc e numb er incr emented by o ne, an d a n ewly generated random number . However , he stores only the last pair it has for any g iv en seq uence number . The length of each transmitted random number is 24 bits if WEP is used, or 48 bits other wise. Finally , th e initial value, V 0 , is the mo dulo- 2 sum of the ra ndom nu mber p airs succ essfully r eceived by both Alice and Bob. The security of this protocol in the presence o f a passi ve Eve directly b u ilds on the results provid ed in Section II -D. More specifically , as Eve becom es completely blind abo ut V 0 if she misses one of th e v alu es con stituting V 0 , the pr obability of secrecy outage in our ca se (corresp onding to (7)) is P 0 = Y i ∈A (1 − γ AE i ) Y j ∈B (1 − γ B E j ) , (10) where A and B are the sets of time indices that c orre- spond to the frames stored by Alice an d Bob, r espectiv ely . γ AE 1 , . . . , γ AE n − 1 denote the f rame loss probabilities in the Alice-Eve channel whereas γ B E 2 , . . . , γ B E n denote the fram e loss pro babilities in the Bob-Eve channel. All o f those p roba- bilities are random variables that are indepen dently and iden- tically d istributed accor ding to Eve’ s chann els’ distributions. Since the size of each of A an d B is n/ 2 . It is evident that, a s n increases, P 0 decreases and we a chieve better secur ity gains, at the expen se of a larger delay in the initialization phase. On th e other hand, if Eve is acti ve, she will be capable of injecting or rep laying initialization frames, since they are no t encrypted . Howev er , any injection or replay attempt will cause a disagreem ent between Alice and Bob on V 0 . W e will later show that if Alice and Bob do not agr ee on V 0 , they will no t be able to exchan ge any d ata fr ames. Consequently , a replay or injectio n attack directly co rrespond s to a Den ial of Service (DoS) attack. W e finally no te that in the case of using the WEP protoco l, the in itialization frames, bein g un- encrypte d, r ev eal no infor mation ab out the secret key , K s , and thus canno t be used in any statistical WEP a ttack. 2) Securing Un ic a st Data : Right after initialization, our protoco l w orks on up dating the V values, used to encap sulate each un icast data frame sent o n the Alice-Bob and Bob -Alice channels. T o illustrate, first consider the i th data fram e to be secu rely transmitted, u sing any security pro tocol, fr om Alice to Bob. Alice starts by ge nerating a random num ber (of length 24 if WEP is used, or 48 bits o therwise) referred to as the head er-V , V h ( i ) . Th e ARQ-CRO WN p rotocol mu st not use two co nsecutive equa l head er-V’ s. This p roperty will b e shown to be useful for defen ding a gainst replay attacks. This value, V h ( i ) , is put in the frame’ s security heade r , according to the specificatio ns o f the security p rotocol used. Howe ver , unlike th e stand ards, the value u sed b y ARQ-CRO WN in encapsulating th e fra me, denoted by V e ( i ) , is the modulo-2 sum of the cur rent head er-V , V h ( i ) , and all o f the h eader-V’ s previously transmitted by Alice and successfully rece i ved by Bob . The update equation for V e is then V e ( i ) = ( V h ( i ) L V e ( i − 1) , if Q ( i − 1) = 1 , V h ( i ) L V e ( i − 1) L V h ( i − 1 ) , o therwise, (11) where Q ( i ) = 1 if Alice receiv ed an A CK for the i th transmitted frame, Q ( i ) = 0 other wise. Th is status is obtained throug h th e A CK/T imeo ut detection mo dule runn ing at Alice (Figure 2(a)). The initial value for this alg orithm is set by the agreed- upon V 0 of the in itialization phase, i.e. , V e (0) = V 0 , while V h (0) = 0 . Similarly , when Bob receives the i th frame, he fir st extracts V h ( i ) from the security header, and then perfor ms a ch eck. If V h ( i ) = V h ( i − 1) , Bob discar ds the frame and treats it as a sign o f a replay attack . If not, Bob attempts to decap sulate th e frame with V d ( i ) , V d ( i ) = V h ( i ) M V d ( i − 1) , (12) where V d (0) = V 0 . If d ecryption fails (an ICV failure occu rs), this would be du e to an erasur e o f th e ( i − 1) th A CK. Bob then goes thr ough another d ecryption attempt, after excluding V h ( i − 1) from th e sum, i.e., with V d ( i ) = V h ( i ) L V d ( i − 1) L V h ( i − 1) . Another failure in decryption is tr eated as a sign of an attack and co untermeasu res could be inv oked (the reason behind this will become clear in the security analysis to follow). Following this pr otocol, Alice an d Bob perfectly agree on the V values used for each f rame. W e av o id any mis-synchro nization that could h appen du e to the loss of an A CK fram e; without any additional feedback bits (as opposed to Section I I-B). The unicast flow from Bob to A lice could be secured in the sam e manner illustrated above. W e now an alyze the secur ity of this p hase. In our schem e, the collected tr affic b y a passi ve Eve b ecomes useful for any attack dep ending on E ve’ s ab ility to co rrectly co mpute V e for each ca ptured fram e. T o achieve this, Eve first has to correctly com pute V 0 , in the in itialization phase betwe en Alice and Bob. Th is hap pens with probab ility P 0 (as given in (10)). Afterwards, for each captured frame, Eve h as to keep track of all the previously ackn owledged data fram es preceding that frame. Eve becom es, again , completely blind if she misses a single acknowledged frame. Based on this ob servation, we let u deno te the total numb er of data fram es that Eve can correctly com pute th eir V e , i.e. , th e usefu l fr ames for Eve. If γ AE = γ AB = γ E for all time indices, the expected number of such frames is upper-bound ed by E [ u ] ≤ E [ γ ´ E ] n +1 − E [ γ ´ E ] N +1 E [ γ E ] , (13) where γ ´ E = 1 − γ E , n is the total nu mber of in itialization frames con stituting V 0 and N is the un icast data session size. As shown in Eq. (13), a sligh t increase of the nu mber o f initialization f rames results in a significant de crease in the number of useful f rames for E ve in each session. This has a direct impact o n the feasibility of m any attack s, especially the statistical WEP attacks, e. .g. [19], as those d epend on collecting a large nu mber of IVs ( V e ’ s in the ARQ-CR O WN case) to run efficiently . W e now consider the case o f an active Eve. F or the u nicast flow from Alice to Bob, Eve cou ld use Alice’ s MA C address to inject or replay data frames of h er choice, or use Bob’ s 9 MA C ad dress to inject A CK messages to confuse Alice. Howe ver, any injected or replayed fram e will lead to m is- synchro nization b etween A lice and Bob . This will b e detected by Bob throu gh two successiv e ICV failur es. As we alread y mentioned , Bob would treat this as a sign of an attack and co untermeasu res co uld follow . The mo st straightfo rward counterm easure is to change the keys of the whole network o r of the attacked sessions. Still, the history of V values b uilt up thus far could b e used after inv oking cou ntermeasur es throug h fast means of “re-sync hronizatio n” as will be later d iscussed. Frame interception (jamm ing), in general, is often used as par t of p hishing and MI TM attacks. Ad ditionally , when ARQ-CR OW N is dep loyed, intercep tion could be u sed to delay the key update process for a certain data flow in the network. Defend ing again st those attacks requires additiona l modification s, which ar e outlined in Section II I-D. 3) Securing Multicast T raffic: Th us far , o ur discussion was limited to u nicast sessions. Since mu lticast f rames are not A CKed, the previously d emonstrated scheme can not be used to secu re these f rames. Ou r scheme for multicast traffic goes as follows: When ev er a client subscrib es to a mu lticast group, g , the AP send s a new rand om value, V g , to every associated client that belongs to this gro up along with an I D fo r this V g value (the updates can be period ic or trigge red based on group membership changes). Those v alues are transmitted to each client over its secure pairwise link with the AP , i.e., as encrypted fram es. Once the AP makes sure that all clients in the group h av e recei ved V g , through individual ACKs, the AP uses this value to compu te V e g , tha t will be used for encap sulating each upcomin g multicast fram e, within this group , i.e., V e g ( i ) = V h ( i ) M V g . (14) where V h ( i ) is a rand om header-V as illu strated before. V h ( i ) and the ID of the u sed V g are sent in the security header of the multicast fram e. Similarly , for mem bers of a particu lar multicast g roup g , a c lient u ses th e rec overed inform ation from the security head er to co mpute V d g ( i ) and decap sulate any mu lticast f rame addressed to this group. Any failure in decryp tion (ICV test failur e) is treated as a sign of attack. Finally , in or der to defend against replay attack s, the AP should not u se rep eated V h values within the lifetime of a certain V g . Similarly , whe never a client receiv es a multicast frame, it must c heck for this condition and treat rep eated V h ’ s as a sign of attack. Using this ARQ-CR OWN multica st overlay , a passi ve Eve cannot make use of any of the m ulticast frames, as secure pairwise lin ks are used to inco rporate hid den and periodically- updated values in to m ulticast V e ’ s. On the oth er hand , an activ e Eve is not capa ble o f injecting o r replaying any of th e multicast frame s, as any replay or injection attempt would lead to a decr yption failure at the legitimate recipients. Finally , for WP A an d WP A2, since there is a different group key fo r each multicast gro up and tha t is u pdated with g roup mem bership changes, our prop osed multicast approach fits nicely within their framework an d incre ases their security . For the WEP case, which uses a shared ke y fo r all mu lticast groups, o ur group -V updates ad d a natura l way fo r g roup mem bership handling . This g iv es an a dditional security advantage f or the WEP case, without having to change the secret root key , K s . D. Discu ssion The enhan ced security , offered by our scheme, is mostly evident in the case of WEP . In particular, using the ARQ- CR OW N overlay , any statistical WEP attack would req uire a sub stantially longer listening time before la unching th e attack; which makes such attacks v irtually impossible. This is demonstra ted by the e xperimen tal results of Sec tion IV -B. It is worth nothin g that in o rder fo r Eve to have a po tential u se of any u nicast session, she ha s to be p resent from the be ginning of this session. Also, our analy tical estimate of the lower bound on the numb er o f u seful fr ames for Eve (Eq. (1 0)) implicitly assumes that Eve is totally capab le of tracking ACKs, i.e. , she perfectly knows the status of each un icast frames. I n practice, especially in large n etworks wh ere channel conditions cou ld be relativ ely worse, such k nowledge is not perfect which causes more confusion at Eve’ s side. One can envision several enhan cements fo r the basic im- plementation p resented h ere. Fir st, settin g the timeout pe- riods in the ARQ-CR O WN in itialization ph ase sho uld b e carefully designed so as to defend a gainst MITM attacks and at the same time keep the in itialization delay within a practically acceptab le ra nge. A related p oint is to an alyze the AC K/timeout events at the legitimate sen ders to detect anomalies in the b ehavior of the connected n odes for be tter detection o f f rame interc eption (jam ming). Secon d, in order to reduce the overhead of the in itialization phase, the legitimate nodes can use the current h istory for future sessions. Up on disassociation, the AP and any legitimate client can store the last point in their ARQ-histor y , and build up o n it in newer sessions instead of go ing throu gh new in itialization p hases. This way , the additional link setup delay imposed by the ARQ- CR OW N overlay is minimized an d secu rity is e nhanced at th e expense o f additional n egligible m emory at bo th sid es. This is especially useful for d esigning seamless ha ndoff mechan isms for Wi-Fi ne tworks as this inform ation can be transferr ed to the n ew AP using the I EEE 8 02.11 f p rotocol. Finally , throug h small modifications, the ARQ-CR OWN overlay co uld be further extended to secure the secret root keys to p rovide more security . Th e ARQ-CR OWN overlay c ould also be used for security at layers h igher than the MA C layer , using the same underly ing prin ciples. I V . N U M E R I C A L A N D E X P E R I M E N TA L R E S U L T S A. Nu m e rica l Results Throu ghout this part, we f ocus on th e symmetric scenario where E ( h b ) = E ( h e ) = 1. W e furth er a ssume Rayleig h fading channels, for both Bob and Eve. Assuming spatially and tempor ally indepen dent ch annels, the ach iev ab le secrecy rate in (2) b ecomes C s = ma x R 0 exp − 2 R 0 − 1 P R 0 − exp (1 /P ) log e (2) E i (1 /P ) − E i 2 R 0 /P , (15) 10 0 2 4 6 8 10 12 14 16 18 20 0 0.2 0.4 0.6 0.8 1 1.2 1.4 1.6 SNR (dB) Capacity (Bits) Rc = 0 R c = 3 R c = 7 Secrecy Capacity Fig. 4: C s and C e against SNR fo r R c = (0 , 3 , 7) . 0 5 10 15 20 25 30 35 40 45 50 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 Mean SNR dB Secrecy Capacity Independent Channels N = 2 N = 3 N = 4 N = 8 Fig. 5: The key rates using N du mb antenn as, assumin g fully corre lated expo nential ch annel gains. where E i ( x ) = R ∞ x exp ( − t ) /t dt . Figu re 4 g iv es the varia- tion of C s and C e (as given in (6)) with SNR un der different constraints on th e dec oding capabilities of Eve, captured b y the genie- given side info rmation, R c . It is clea r from the figur e that C e can be greater th an C s for cer tain R c and SNR values. For instance, in the case o f R c = 0 , a packet r eceiv ed in error at Eve will be discarded w ithout any furt her a ttempts at decoding . Th erefore, the secre cy r ate becom es R 0 , which is larger than that used in (2); C s ( i ) = R 0 − log 2 (1 + h e ( i ) P ) , where C s ( i ) , h e ( i ) are the instantaneous secrecy rate , and Eve’ s channe l power gain , r espectiv ely . A veraging over all fading realizations, we get a greater C e than C s . I t is worth noting that, un der the assum ptions of th e symmetric scena rio and the Rayleigh fading model, the scheme pr oposed in [4] is not able to achieve any p ositiv e secrecy rate (i.e., probab ility of secrecy o utage is one). T he r ole o f d umb an tennas in increasing the secr ecy capacity of spatially correlated ARQ channels is inv estigated next. In our simulations, we assume that the chan nel gain s are fully cor related, but the chann el phases are indepen dent. The independenc e assump tion for the phases is justified as a small change in distance between Bob and Eve in th e orde r of several electr omagnetic wa velengths translates to a sign ificant chang e in phase. Un der these as- sumptions, it is easy to see that with one transmit an tenna the secr ecy capacity is zero . In Figure 5, it is shown th at as the number of a ntennas N increases, the secret key rate approa ches the upper boun d given by ( 2), which assum es that the ma in an d eavesdropper ch annels are indep endent. Th e same trend is obser ved assumin g chi-squ are distribution with different degrees of freedom (the figur es were omitted to avoid 10 15 20 25 30 35 40 0.4 0.5 0.6 0.7 0.8 0.9 1 Secrecy Capacity Under Different Scenarios Mean SNR (dB) Key Rate (bits) Ergodic Secrecy − Main CSI Independent Blocks α = 0.001 α = 0.02 α = 0.1 α = 0.2 α = 0.5 α = 0.8 Fig. 6: The ach ie vable key r ates using the gre edy scheme under different tem poral correlation coefficient α . 0 5 10 15 20 25 30 0 0.005 0.01 0.015 0.02 0.025 SNR dB Key Rate Kb = 480, Uncoded BPSK Kb = 480, 7/8 Convolutional Coded BPSK Kb = 480, 7/8 Convolutional Coded QPSK Kb = 240, Uncoded BPSK Kb = 240, 7/8 Convolutional Coded BPSK Kb = 240, 7/8 Convolutional Coded QPSK Fig. 7: The key rates requ ired to obtain an outage of 1 0 − 10 against SNR fo r different packet sizes, K b = 240 an d 480 bits, and different m odulation schemes. redund ancy). Figure 6 reports the performan ce of the greedy rate adap tation algo rithm for tempora lly correlated cha nnels. The channel is assumed to fo llow a first order Markov m odel: g ( t ) = (1 − α ) g ( t − 1) + p 2 α − α 2 w ( t ) where w ( t ) is the innovation process f ollowing C N (0 , 1) distribution. As exp ected, it is shown that as α d ecreases, the ke y r ate incr eases. F or th e extreme p oints w hen α = 0 or α = 1 , we ge t an upper bound , which is the ergodic secrecy under the main-chan nel tr ansmit CSI assumption, and a lower bound , wh ich is the ARQ secrecy capacity in c ase of indepen dent blo ck fadin g channel, respectively . Finally , we turn our attention to th e delay-limited co ding construction s prop osed in Section II -D. I n Figure 7, we relax the o ptimal channe l coding assumption and plot key rates for practical cod ing schemes and finite frame lengthes (i.e ., finite n 1 ). The code used in the simulatio n is a pun ctured conv olu tional code d erived fro m a basic 1 / 2 code with a constraint length o f 7 and gen erator p olynom ials 133 an d 171 (in o ctal). W e assume that Eve is g enie-aided and can correct an additiona l 50 er roneou s symbols (beyon d the erro r correction capability of the chann el co de). Note that the transmission ra te is fixed and is indep endent of the SNR. Therefo re, a low SNR means mor e tran smissions to Bo b an d a consequen t lo w key rate. As the SNR increases, while keeping the transmission rate fixed, the key r ate increases. Howev er , increasing the SNR also m eans an increa sed ability of E ve to correctly deco de the code word-carryin g packets. T his explains 11 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 x 10 −3 10 0 10 2 Overhead Average Number of Useful Frames Experimen t al Observat io ns Anal yt ica l Expecta t io n (a) E [ γ AB ] = 0 . 005 , E [ γ BA ] = 0 . 009 and E [ γ AE ] = 0 . 004 . 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 x 10 −3 10 −20 10 −10 10 0 Overhead Average Number of Useful Frames Experimen t al Observati o ns Anal yt ica l Expecta ti o n (b) E [ γ AB ] = 0 . 01 , E [ γ BA ] = 0 . 01 and E [ γ AE ] = 0 . 02 . Fig. 8: The average number of usefu l frames at Eve. why the k ey rate cu rves a peak and then dec ays with SNR . W e also observe that, fo r a certain m odulation an d ch annel co ding scheme, reducing th e pa cket size increases the p robability o f correct deco ding by Bob and, thus, decreases th e numb er of transmissions. Howe ver , it also increases the prob ability of correct deco ding b y Eve and the overall effect is a decr eased key rate. B. E xperimental Results Our experim ents are con ducted with a modified version of the Mad wifi driver that has ARQ-CR O WN capab ilities. All of our testbed nodes are Dell Latitude D830 laptops that are e quipped with Athe ros-based D-Lin k DWL-G650 WLAN cards. All traffic is generated using Netp erf [26]. 1) Security: O ne-way traffic was generated be tween a client node ( Alice) an d th e AP (Bob) in the pr esence of one eav esdroppe r (Eve). Eve’ s d riv er was eq uipped with the ARQ- CR OW N algorith ms, i. e. Eve c alculates V e for eac h f rame based on the capture d tra ffic. T wo experiments were laun ched in d ifferent en vironm ents. In the first exper iment, Eve had relativ ely better channel conditions, as compared to B ob, while in th e second, the situation was re versed. W e comp ared the V e values that Eve an d Bob o btained for ea ch f rame, an d calculated the n umber of usefu l fra mes for E ve ( with d ifferent number s of initializatio n frames). The results are reported in lo g scale in Figu re 8. For both experiments, the data session size is taken to be 1000 00 frames. The large disagreem ent between the analytical esti- mates (ev aluated as g iv en in 13) and the experim ental results in Figu re 8(b) is due to the very small average num ber (u p to 10 − 20 ) of u seful frames when th e channe l conditio ns ar e against Eve, wh ich requires an infea sible expe riment du ration to be captured in practice. Th ese r esults can b e used to estimate the required time for Ev e to captur e a total of 1 . 5 m illion useful frames that is typica lly re quired to launch a com bined f orm 200 400 600 800 1000 1200 1400 0 5 10 15 20 25 30 Frame Size (bytes) Throughput (Mbps) HW−WEP SW−WEP ARQ−WEP (a) WE P is used for encryption. 200 400 600 800 1000 1200 1400 0 5 10 15 20 25 Frame Size (bytes) Throughput (Mbps) HW−TKIP SW−TKIP ARQ−TKIP (b) T KIP is use d fo r e ncrypti on. 200 400 600 800 1000 1200 1400 0 5 10 15 20 25 Frame Size (bytes) Throughput (Mbps) HW−CCMP SW−CCMP ARQ−CCMP (c) CCMP is used for encryption. Fig. 9: Ne twork thr oughp ut for TCP flows with different security proto cols. of the FMS an d K o reK attacks ( [27]). Un der th e origin al WEP op eration, we assume that Eve needs 10 minutes to gather suc h traffic u sing p assi ve eavesdropping only . Based on this estimate, using ARQ-WEP protocol extends the required av erage listening time for Eve to 1 . 24 years and 5 . 07 years , for the first and second experimen ts, respectiv ely , using only an initialization overhead of 0 . 0 0 1 . Note that un der ARQ- CR OW N op eration, Eve canno t use any active techniques to reduce the listening time. For TKIP and CCMP , the decreased number of useful frames at Eve hampe rs her ability to exploit the weaknesses that were discussed in Section III -A2. 2) Thr oughpu t: Her e we compar e the pe rforman ce o f the propo sed ARQ-CRO WN overlay with the baseline software implementatio ns o f WEP , TKIP , and CCMP in the Mad wifi driver . T o obtain a measu re o f performan ce if th e proposed ARQ-CR OW N overlay was impleme nted in h ardware, we also include the results of all hardware implementation s. Figur e 9 reports the aggr egate n etwork throughp ut fo r TCP flows, with different p acket sizes, for WEP , TKI P , and CCMP . One can see that using th e ARQ-CR O WN on top of WEP (ARQ- WEP) resu lts in a throug hput degradation of 11 .57% over the Madwifi software implem entation of WEP (SW -WEP), for a packet size of 1500 bytes. The co rrespond ing degradation for TKIP an d CCMP is 15.61% an d 1 5.26%, r espectively . This quantifies the processing o verhead of ARQ-CR O WN operation (as de scribed in Section III- C2). As the packet size in creases, the overhe ad in troduce d by the ARQ-CR OW N decreases, as it is amortized over a larger packet size. 12 V . C O N C L U S I O N S This p aper developed a unified framework for sharing secret keys using existing A RQ p rotocols. The unde rlying idea is to distribute the key b its over m ultiple ARQ fram es and th en u se the authen ticated A CK/N AC K feedbac k to cr eate an eq uiv a- lent degrad ed ch annel at th e eavesdropper . Our informatio n theoretic found ations estab lished the ach iev ab ility of non -zero secrecy rates even when the eav esdropp er is experien cing a higher average SNR than the legitimate receiv er and she d light on the structu re o f o ptimal ARQ secrecy protocols. I t is worth noting that o ur app roach does not assume any prio r knowledge about the instan taneous CSI; only pr ior knowledge of the aver - age SNRs seen by the ea vesdropper and the legitimate receiver are needed. Our secrecy capacity ch aracterization r ev ealed th e negativ e impa ct of spatial correlation and th e positive impa ct of temporal correlation on the achiev ab le key rates. The former pheno menon was m itigated v ia a novel “dumb antennas” technique , wherea s the la tter was explo ited via a greed y rate adaptation policy . Furthe rmore, lo w comp lexity secrecy coding schem es were c onstructed by transforming our ch annel to an erasure wiretap c hannel which lends itself to explicit coset cod ing approach es. Buildin g on this solid f ounda tion, we developed a n ovel app roach for ARQ security in W i-Fi networks ( i.e., ARQ-CR O WN). Our ARQ-CR O WN overlay is shown to offer p rovable inf ormation the oretic con fidentiality guaran tees w hich complem ent the security measures provided by the underly ing WEP , WP A, and WP A2 proto cols. T hese claims wer e validated by experimental results, obtained fro m our prototype, w hich illustrate th e ability o f ARQ-CR O WN to mitigate all known eaves dropp ing attacks, whether active o r passiv e, at the expense o f a throu ghput loss in the order of 10% – 15 % using sof tware e ncryptio n. The most interesting part of our work is, perhaps, the demonstration of the utility of information t heoretic secu- rity concepts in securing state of the art wireless networks. In our op inion, th e success of such conc epts in practice will depend cr itically on the ability to apply them to compleme nt existing secur ity mech anisms ra ther than replacin g them . W e hope that this first step will stimu late f urther work a iming at bridgin g the g ap b etween the two worlds. A P P E N D I X A P R O O F O F T H E O R E M 1 A. A chievability Pr o of The pro of is given for a fix ed average power P ≤ ¯ P and transmission rate R 0 . The ke y rate is th en o btained by the ap propr iate maximiz ation. Let R s = C ( g ) s − δ fo r some small δ > 0 and R = R 0 − ǫ . W e first gen erate a ll b inary sequences { V } of length mR and then indepen dently assign each of th em rand omly to one of 2 nR s group s, according to a unifo rm distrib ution. This en sures that any of the sequences are e qually likely to be within any of the groups. E ach secr et message w ∈ { 1 , · · · , 2 nR s } is then assigned a g roup V ( w ) . W e then generate a Gaussian codebook co nsisting of 2 n 1 ( R 0 − ǫ ) codewords, each of leng th n 1 symbols. The cod ebook s are then revealed to Alice , Bob, and Eve. T o transmit th e co dew ord, Alice first selects a ra ndom gro up v ( i ) of n 1 R bits, and th en transmits th e co rrespond ing codeword, drawn fro m th e cho sen Gaussian codebook . If Alice receiv es an ACK bit from Bob, both ar e g oing to store th is group of bits an d selects another group o f bits to send in the next coherenc e interval in the same manner . If a NA CK was received, this group of bits is discarded and ano ther is gen erated in the same m anner . This process is repeated till both Alice and Bob have shared the same key w co rrespond ing to nR s bits. W e observe that the channel coding theorem implies the existence of a Gaussian codebo ok whe re the f raction of successfully d ecoded frames is given by m n = Pr ( R 0 ≤ lo g 2 (1 + h b P )) , as n 1 → ∞ . The equivocation rate at the eavesdropper can then be lower bound ed as fo llows. nR e = H W | Z n , K b , G b b , G b e ( a ) = H ( W | Z m , G a b , G a e ) = H ( W , Z m | G a b , G a e ) − H ( Z m | G a b , G a e ) = H ( W , Z m , X m | G a b , G a e ) − H ( Z m | G a b , G a e ) − H ( X m | W , Z m , G a b , G a e ) = H ( X m | G a b , G a e ) + H ( W, Z m | X m , G a b , G a e ) − H ( Z m | G a b , G a e ) − H ( X m | W , Z m , G a b , G a e ) ≥ H ( X m | G a b , G a e ) + H ( Z m | X m , G a b , G a e ) − H ( Z m | G a b , G a e ) − H ( X m | W , Z m , G a b , G a e ) = H ( X m | G a b , G a e ) − I ( Z m ; X m | G a b , G a e ) − H ( X m | W , Z m , G a b , G a e ) = H ( X m | Z m , G a b , G a e ) − H ( X m | W , Z m , G a b , G a e ) ( b ) = a X j =1 H ( X ( j ) | Z ( j ) , G b ( j ) , G e ( j )) − H ( X m | W , Z m , G a b , G a e ) ( c ) ≥ X j ∈N m H ( X ( j ) | Z ( j ) , G b ( j ) , G e ( j )) − H ( X m | W , Z m , G a b , G a e ) = X j ∈N m H ( X ( j ) | G b ( j ) , G e ( j )) − I ( X ( j ); Z ( j ) | G b ( j ) , G e ( j )) − H ( X m | W , Z m , G a b , G a e ) ≥ X j ∈N m n 1 R 0 − log 2 (1 + h e ( j ) P ) − ǫ − H ( X m | W , Z m , G a b , G a e ) ≥ a X j =1 n 1 [ R 0 − log 2 (1 + h e ( j ) P )] + − ǫ − H ( X m | W , Z m , G a b , G a e ) ( d ) = n C ( g ) s − H ( X m | W , Z m , G a b , G a e ) − mǫ. (16) In the above der iv ation , (a) results from the independen t choice of the codew ord sym bols transmitted in each ARQ frame which d oes not allow Eve to be nefit fro m the ob servations correspo nding to the N ACK ed frames, (b) f ollows from the memory less pro perty of th e ch annel an d the in depend ence of the X ( j ) ’ s, ( c) is ob tained by removing all those ter ms which corresp ond to the co herence intervals j / ∈ N m , where 13 N m = { j ∈ { 1 , · · · , a } : h b ( j ) > h e ( j ) | ψ = 1 } , where ψ is a bin ary random variable and ψ = 1 ind icates that an A CK was received, and (d) fo llows from the e rgodicity of the chan nel as n, m → ∞ . No w we show that the ter m H ( X m | W , Z m , G a b , G a e ) vanishes as n 1 → ∞ by using a list decodin g argumen t. In this list decoding , at coherence inte rval j , the wiretapper first co nstructs a list L j such that x ( j ) ∈ L j if ( x ( i ) , z ( i )) are jointly ty pical. Let L = L 1 × L 2 × · · · × L a . Giv en w , the wiretap per declares that ˆ x m = ( x m ) was trans- mitted, if ˆ x m is the only code word such th at ˆ x m ∈ B ( w ) ∩ L , where B ( w ) is the set of codewords correspo nding to the message w . I f the wiretap per finds non e or more than o ne such sequence, then it d eclares an error . Hence, there a re tw o types of error events: 1) E 1 : the transmitted cod ew ord x m t is no t in L , 2) E 2 : ∃ x m 6 = x m t such th at x m ∈ B ( w ) ∩ L . T hus the er ror probab ility Pr ( ˆ x m 6 = x m t ) = Pr ( E 1 ∪ E 2 ) ≤ Pr ( E 1 ) + Pr ( E 2 ) . Based on the Asympto tic Equipartition Property (AEP), we know that Pr ( E 1 ) ≤ ǫ 1 . In or der to b ound Pr ( E 2 ) , we first bound the size of L j . W e let φ j ( x ( j ) | z ( j )) = 1 , ( x ( j ) , z ( j )) are jointly typ ical, 0 , otherwise. Now E {kL j k} = E X x ( j ) φ j ( x ( j ) | z ( j )) ≤ E 1 + X x ( j ) 6 = x t ( j ) φ j ( x ( j ) | z ( j )) ≤ 1 + X x ( j ) 6 = x t ( j ) E { φ j ( x ( j ) | z ( j )) } ≤ 1 + 2 n 1 [ R 0 − log 2 (1+ h e ( j ) P ) − ǫ ] ≤ 2 n 1 [ R 0 − log 2 (1+ h e ( j ) P ) − ǫ ] + + 1 n 1 . Hence E {kLk} = a Y j =1 {kL j k} = 2 a P j =1 n 1 [ R 0 − log 2 (1+ h E ( j ) P ) − ǫ ] + + 1 n 1 . Pr ( E 2 ) ≤ E X x m ∈L , x m 6 = x m t Pr ( x m ∈ B ( w )) ( a ) ≤ E kLk 2 − nR s ≤ 2 − nR s 2 a P j =1 n 1 [ R 0 − log 2 (1+ h e ( j ) P ) − ǫ ] + + 1 n 1 ≤ 2 − n R s − 1 c a P j =1 [ R 0 − log 2 (1+ h e ( j ) P ) − ǫ ] + + 1 n 1 ! = 2 − n R s − 1 c a P j =1 [ R 0 − log 2 (1+ h e ( j ) P )] + + 1 n 1 + |N m | ǫ c ! , where (a) follows from the unifo rm distribution of the code- words in B ( w ) . Now as n 1 → ∞ an d a → ∞ , we get Pr ( E 2 ) ≤ 2 − n ( C ( g ) s − δ − C ( g ) s + aǫ ) = 2 − n ( cǫ − δ ) , where c = Pr ( h b > h e ) . Th us, by choosing ǫ > ( δ/ c ) , the error pro bability Pr ( E 2 ) → 0 as n → ∞ . Now u sing Fano’ s inequality , we g et H ( X m | W , Z m , G a b , G a e ) ≤ nδ n → 0 as m, n → ∞ . Com bining this with (16), we get th e d esired result. B. Co nverse Pr oo f W e now prove the converse part b y showing th at fo r any perfect secrecy ra te R s with equivocation rate R e > R s − ǫ as n, m → ∞ , there exists a transmission rate R 0 , such that R s ≤ E n [ R 0 − log 2 (1 + h e P )] + I ( R 0 ≤ log 2 (1 + h b P )) o . Consider any sequence of (2 nR s , m ) codes with per- fect secrecy rate R s and equiv ocation rate R e , such that R e > R s − ǫ as n → ∞ . W e n ote that th e eq uiv o cation H ( W | Z n , K n , G b b , G b e ) only d epends on the marginal distri- bution of Z n , an d th us does not d epend on whether Z ( i ) is a physically or stoch astically d egraded version o f Y ( i ) or vice versa. Hence we assume in the following der iv ation th at fo r any fading state, either Z ( i ) is a p hysically degraded version of Y ( i ) or v ice versa (sinc e the noise pr ocesses are Gaussian). Thus we have nR e = H ( W | Z b , K n , G b b , G b e ) ( a ) = H ( W | Z m , G a b , G a e ) ( b ) ≤ H ( W | Z m , G a b , G a e ) − H ( W | Z m , Y m , G a b , G a e ) + mδ m = I ( W ; Y m | Z m , G a b , G a e ) + mδ n ( c ) ≤ I ( X m ; Y m | Z m , G a b , G a e ) + mδ m = H ( Y m | Z m , G a b , G a e ) − H ( Y m | X m , Z m , G a b , G a e ) + mδ m = a X i =1 [ H ( Y ( i ) | Y i − 1 , Z m , G a b , G a e ) − H ( Y ( i ) | Y i − 1 , X m , Z m , G a b , G a e )] + mδ m ( d ) ≤ a X i =1 [ H ( Y ( i ) | Z ( i ) , G b ( i ) , G e ( i ) − H ( Y ( i ) | X ( i ) , Z ( i ) , G b ( i ) , G e ( i ))] + mδ m = a X i =1 I ( X ( i ); Y ( i ) | Z ( i ) , G b ( i ) , G e ( i )) + mδ m ( e ) = a X i =1 I ( X ( i ); Y ( i ) | G b ( i ) , G e ( i )) − I ( X ( i ); Z ( i ) | G b ( i ) , G e ( i )) + mδ m ≤ a X i =1 R 0 − log 2 (1 + h e ( i ) P ) + mδ m ≤ a X i =1 [ R 0 − log 2 (1 + h e ( i ) P )] + + mδ m R e ( f ) ≤ E [ R 0 − log 2 (1 + h e P )] + 14 I ( R 0 ≤ log 2 (1 + h b P )) + β δ m , where β = Pr ( R 0 ≤ log 2 (1 + h b P )) . In the above deriv ation, (a) results from th e independe nt choice of the codew ord symbols tr ansmitted in each ARQ fram e which does no t allow E ve to benefit from the observations corresp onding to the N AC Ked f rames, (b) follo ws f rom Fano’ s inequal- ity , (c) follows from the data processing in equality since W → X m → ( Y m , Z m ) forms a Markov chain, (d) follows from the fact that condition ing reduces en tropy and f rom th e memory less p roperty of the chann el, (e) follows from the fact that I ( X ; Y | Z ) = I ( X ; Y ) − I ( X ; Z ) as shown in [1], (f) follows fro m ergodicity of the ch annel as m, n → ∞ . Th e claim is thus pr oved. A P P E N D I X B P R O O F O F D E C O R R E L A T I O N In this ap pendix, we sh ow that employing multiple tran smit antennas makes the correlation between Eve’ s and Bob ’ s channel p ower gains con verge to zero , in a m ean-squar e sense, as the numb er of anten nas N g oes to ∞ . Let l 1 = | g eq b | 2 and l 2 = | g eq e | 2 . Assuming all θ ’ s to b e unifo rmly distributed in the interval [ − π , π ] , we get, l 1 = 1 N N X i =1 cos ( θ iR + θ iB ) 2 + N X i =1 sin ( θ iR + θ iB ) 2 = 1 N " N + 2 N − 1 X i =1 N X j = i +1 n cos ( θ iR + θ iB ) cos ( θ j R + θ j B ) + sin ( θ iR + θ iB ) sin ( θ j R + θ j B ) o # = 1 + 2 N N − 1 X i =1 N X j = i +1 cos ( θ iR + θ iB − θ j R − θ j B ) . (17) Similarly for l 2 , l 2 = 1 + 2 N N − 1 X i =1 N X j = i +1 cos ( θ iR + θ iE − θ j R − θ j E ) . (1 8) Now , taking the e x pectation o f (17) a nd (18 ) with resp ect to the random p hases ap plied on the transmit antenn a array θ iR for giv en values of θ iE ’ s and θ iB ’ s, we get E ( l 1 ) = E ( l 2 ) = 1 , and E ( l 1 ) = E ( l 2 ) = 1 , E ( l 1 l 2 ) = 1 + 2 N 2 N − 1 X i =1 N X j = i +1 cos [( θ iB − θ iE ) − ( θ j B − θ j E )] , E l 2 1 = E l 2 2 = 1 + 2 N 2 N ( N − 1) 2 = 1 + N − 1 N . So, the variance of l 1 and l 2 is given by var ( l 1 ) = v ar ( l 2 ) = σ 2 l 1 = σ 2 l 2 = N − 1 N . Therefo re, the co rrelation coefficient ρ b etween the cha nnels’ power gains is gi ven by ρ = E ( l 1 l 2 ) − E ( l 1 ) E ( l 2 ) p v ar ( l 1 ) p V ar ( l 2 ) = 2 N ( N − 1) N − 1 X i =1 N X j = i +1 cos [( θ iB − θ iE ) − ( θ j B − θ j E )] = 2 N ( N − 1) N − 1 X i =1 N X j = i +1 cos [∆ i − ∆ j ] , where ∆ i = θ iB − θ iE and ∆ j = θ j B − θ j E . Assum ing θ iB , θ iE , θ j B , θ j E are all independen t, and unifor mly dis- tributed in the in terval [ − π , π ] , and taking the expectation of ρ over them , we get E ( ρ ) = 0 . (19) The diver gence of ρ around its mean is given by var ( ρ ) = σ 2 = 4 N 2 ( N − 1) 2 N − 1 X i =1 N X j = i +1 var (cos (∆ i − ∆ j )) = 4 N 2 ( N − 1) 2 . N ( N − 1) 2 . 1 2 = 1 N ( N − 1) . (20) Thus, the standa rd de viation of ρ is given b y σ = 1 √ N ( N − 1) ≃ 1 N . It is evident from (2 0) that v ar ( ρ ) g oes to zero as N → ∞ . That is, the corr elation coefficient ρ co n verges, in a mea n- square sense, to zer o. R E F E R E N C E S [1] A . D. W yne r , “The wire- tap channel , ” B ell Syste ms T ec hnical J ournal , vol. 54, no . 8, pp. 1355–1387, Jan uary 19 75. [2] P . K. Gopala, L. Lai, and H. El Gamal, “On the secrec y capa city of fadi ng cha nnels, ” v ol. 54, no. 10, pp. 4687–4698, Oct. 2008 . [3] X . T ang, R. Liu, and P . Spasojevi c, “On the achie v able secrec y through- put of block fading channel s with no channel state information at transmitt er , ” in CISS’07 , Mar ch 2007, p. 917922. [4] X . T ang, R. Liu, P . Spasoje vic, and H. V . Poor , “On the throughput of secure hybrid-AR Q protocols for gaussian block-fadi ng channels, ” in ISIT 2007 , jun 2007, pp . 1355–1387. [5] S . Xiao, H. Pishro-Ni k, and W . Gong, “Dense pari ty check based secrec y sharing in wirele ss communica tions, ” in Globecom07 , 2007. [6] S . Xiao, W . Gong, and D. T owsle y , “Secure wirele ss communicatio n with dynamic secre ts, ” in INFOCOM’10 , 2010 . [7] E . T e ws, R.-P . W einmann, and A. Pyshkin, “Breaking 104 bit WE P in less than 60 seconds, ” v ol. 4867, pp. 188–202, 2008. [8] T . Ohi gashi and M. Morii, “ A practical message fa lsificat ion attack on WP A. ” [Online]. A v ailable : http:// tin yurl.com/nban35 [9] M. A. Khan, A. R. Cheema, and A. Hasan, “I mprov ed nonce c onstruc- tion scheme for AES CCMP to ev ade initial counter prediction, ” in SNPD ’08 , Aug. 6–8, 2008, pp. 307–311. [10] P . V iswanath, D. Tse, and R. Laroia, “Opportuni stic beamforming using dumb antennas, ” vol . 48, pp. 1277–1294, 20 02. [11] A. Papoulis and S. U. Pillai, Pr obabili ty , Random V ariabl es and Stoch as- tic P r ocesses , 4th ed. McGraw-Hil l, 2001. [12] R. Aggarwa l, P . Schniter , and C. E. K oksal, “ Rate adapt ation via li nk- layer feedba ck for goodput m aximiza tion ove r a time-v arying channel, ” T rans. W ir eless. Comm. , v ol. 8, no. 8, pp. 4276–4285, 2009 . [13] L . H. Ozaro w an d A. D. W yner , “The wire-tap channel II, ” Bell System T ec hnical J ournal , v ol. 63, no. 10, pp. 2135–2157, 1984. [14] M. Bloch, A. Thangaraj , S. W . McLaughlin, and J.-M. Merolla, “LDPC- based secret key agreement over the gaussian wiretap channel, ” in Proc . ISIT’06 , Jul. 9–14, 2006, pp. 1179–1183. [15] A. Thangaraj, S. Dihidar , A. R. Calderba nk, S. W . McLaughlin, and J. Merolla, “On achie ving capacit y on the wire tap channel using L DPC codes, ” in ISIT 2005 , sep 2005, pp . 1498–1502. [16] A. Thangara j, S. D ihidar , A. R. Calde rbank, S. Mc Laughlin, and J.-M. Merolla , “ Applicati ons of L DPC code s to the wi retap channe l, ” vol. 53, no. 8, pp. 2933–2945, aug 2007. 15 [17] J. Edney and W . A. Arbaugh, R eal 802.11 Secu rity: W i-F i Protec ted Access and 802.11i . Addison W esley , July 2003. [18] N. Boriso v , I. Goldberg, an d D. W agner , “Interc epting mobile commu- nicat ions: The insecurity of 802.11, ” 20 01, pp . 180–189. [19] S. Fluhrer , I. Mantin, and A. Shamir, “W eaknesses in the ke y scheduli ng algorit hm of RC4, ” pp. 1–24, 2001 . [20] KoreK, “chopchop (experimen tal WEP attacks), ” 2004. [Online]. A v ailab le: http://www .netstu mbler .org/sho wthread.php?t=12489 [21] ——, “Next generation of WEP attacks, ” 2004. [Online]. A vail able: http:/ /www .netstumbler .org /sho wpost.php?p=93942&postcount=35 [22] A. Klein, “ Attacks on the RC4 stream cipher , ” Designs, Codes and Crypto graphy , vol . 48, no. 3, pp. 269–286, Septe mber 2008. [Online]. A v ailab le: http://www .springer link.com/c ontent/6086867367826646/ [23] A. Bittau, M. Handley , and J. Lacke y , “The final nail in WEP’ s cof fin, ” in Proc. ISSP’06 , Ma y 21 –24, 2006, pp. 15pp.–400. [24] V . Moen, H. Raddum, and K. J. Hole, “W eaknesses in the temporal key hash of WP A, ” SIGMOBILE Mob . Comput. Commun. Rev . , vol. 8, no. 2, pp. 76–83, 2004. [25] E . T e ws and M. Beck, “Practical attacks agai nst WEP and WP A, ” in W iSec ’09: P r oceedings of the second ACM confer ence on W ir eless network security . Ne w Y o rk, NY , USA: A CM, 2009, pp. 79–86. [26] “Netperf, a netw orking performanc e benchmark, ” http:/ /www .netperf.or g/netp erf/ . [27] “ Aircrack-ng toolset . ” [Online]. A va ilabl e: http:/ /airc rack- ng.org/doku.php
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment