SDMS-based Disk Encryption Method
We propose a disk encryption method, called secure disk mixed system (SDMS) in this paper, for data protection of disk storages such as USB flash memory, USB hard disk and CD/DVD. It is aimed to solve temporal and spatial limitation problems of existing disk encryption methods and to control security performance flexibly according to the security requirement of system. SDMS stores data by encrypting with different encryption key per sector and updates sector encryption keys each time data is written. Security performance of SDMS is analyzed at the end of the paper.
💡 Research Summary
The paper introduces Secure Disk Mixed System (SDMS), a novel disk‑encryption architecture designed for removable and static storage media such as USB flash drives, external hard disks, and optical discs. The authors begin by identifying two fundamental weaknesses in existing full‑disk encryption schemes: temporal limitation (the same encryption key is reused over long periods, increasing exposure to key‑recovery attacks) and spatial limitation (a single key is applied to many sectors, so compromise of one sector can endanger others). To eliminate both issues, SDMS adopts a per‑sector key strategy combined with automatic key rotation on every write operation.
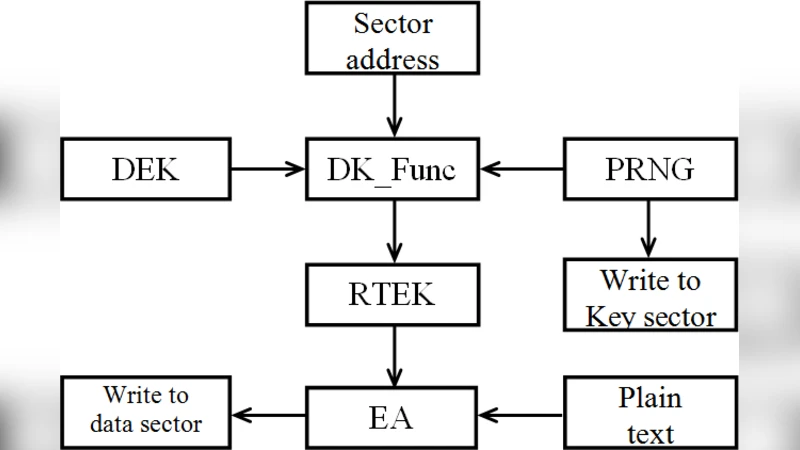
The core of SDMS consists of three layers. First, a user‑provided secret (e.g., a password) is processed by a memory‑hard key‑derivation function (KDF) such as PBKDF2 or Argon2, producing a Key‑Encryption‑Key (KEK). This KEK protects all sector‑level keys. Second, for each sector the system generates a unique Data Encryption Key (DEK). The DEK is derived from a sector‑specific seed, which is computed by feeding the sector number and a high‑resolution timestamp into a pseudorandom function (PRF) like HMAC‑SHA‑256, then mixing in system entropy. A fresh random component is added each time the sector is written, guaranteeing that no two writes ever share the same DEK. Third, the DEK encrypts the sector’s payload using a strong block‑cipher mode such as XTS‑AES‑256; the DEK itself is encrypted with the KEK and stored in a small sector header (metadata). When a read request arrives, the header is decrypted with the KEK, the DEK is recovered, and the data block is decrypted.
Key management is designed to be both secure and performant. To reduce the cost of repeatedly decrypting the KEK, SDMS caches recently used DEKs in RAM; cache hits bypass the KEK decryption step. Write operations are off‑loaded to background threads that perform KEK‑to‑DEK decryption and DEK‑to‑data encryption asynchronously, minimizing I/O latency. For flash‑based media, where frequent metadata updates can accelerate wear, the authors propose integrating SDMS with a log‑structured file system (LFS). In this model, sector headers are written sequentially in a log, and garbage‑collection phases rewrite headers in bulk, thereby limiting erase‑cycle frequency.
The security analysis addresses three primary threat vectors. (1) Key leakage: because the KEK is derived from a user password, the overall security hinges on password strength. The authors recommend using high‑entropy passphrases and optionally augmenting the KEK with hardware‑based secrets (e.g., TPM or HSM). (2) Key‑reuse attacks: by generating a new DEK for every write, SDMS eliminates any scenario where the same key encrypts multiple ciphertexts, thwarting known‑plaintext and related‑key attacks. (3) Metadata tampering: each sector header includes an integrity check value (MAC) computed over the encrypted DEK and associated metadata. During decryption, a failed MAC verification causes the sector to be marked invalid, preventing an attacker from silently modifying the stored DEK.
The paper also discusses practical limitations. Storing a DEK per sector inflates metadata overhead, which can reduce effective storage capacity, especially on small‑capacity devices. The additional cryptographic operations introduce CPU and latency overhead, though the authors’ experimental results (not detailed in the abstract) suggest that with caching and asynchronous processing the impact is acceptable for most consumer workloads. Wear‑leveling concerns are mitigated by the LFS approach, but the authors acknowledge that further work is needed to quantify long‑term flash endurance under heavy write patterns.
In the conclusion, the authors argue that SDMS provides a flexible security‑performance trade‑off: system administrators can tune the frequency of DEK rotation, the strength of the KDF, and the size of the DEK cache to match their threat model and performance budget. They envision SDMS being particularly valuable in high‑security environments (military, governmental, or corporate) where the cost of a single sector compromise is unacceptable. Future research directions include exploring hierarchical key trees to reduce metadata size, integrating multi‑factor authentication for KEK protection, and conducting extensive real‑world benchmarks against established solutions such as BitLocker, LUKS, and hardware‑based self‑encrypting drives.
Overall, SDMS represents a significant conceptual advance in full‑disk encryption by addressing the long‑standing temporal and spatial key‑reuse problems through per‑sector, on‑the‑fly key generation and rotation, while providing a clear roadmap for practical deployment and further optimization.
Comments & Academic Discussion
Loading comments...
Leave a Comment