Geocast into the Past: Towards a Privacy-Preserving Spatiotemporal Multicast for Cellular Networks
This article introduces the novel concept of Spatiotemporal Multicast (STM), which is the issue of sending a message to mobile devices that have been residing at a specific area during a certain time
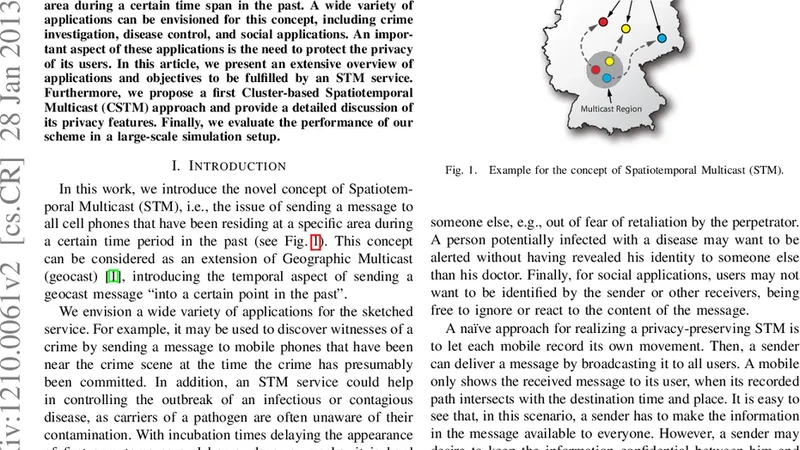
This article introduces the novel concept of Spatiotemporal Multicast (STM), which is the issue of sending a message to mobile devices that have been residing at a specific area during a certain time span in the past. A wide variety of applications can be envisioned for this concept, including crime investigation, disease control, and social applications. An important aspect of these applications is the need to protect the privacy of its users. In this article, we present an extensive overview of applications and objectives to be fulfilled by an STM service. Furthermore, we propose a first Cluster-based Spatiotemporal Multicast (CSTM) approach and provide a detailed discussion of its privacy features. Finally, we evaluate the performance of our scheme in a large-scale simulation setup.
💡 Research Summary
The paper introduces a new communication paradigm called Spatiotemporal Multicast (STM), which enables a sender to deliver a message to mobile devices that were present in a specific geographic area during a defined time interval in the past. The authors argue that such a capability opens up a wide range of societal and commercial applications, including criminal investigations (e.g., notifying devices that were near a crime scene), public‑health interventions (e.g., alerting devices that were in a location during an outbreak), and social services (e.g., emergency warnings for residents of a disaster‑affected zone). Because STM inherently deals with historical location and time data, protecting user privacy becomes a central design challenge.
To address both functional requirements and privacy concerns, the authors first enumerate five key objectives for any STM service: (1) Accuracy – only devices that truly were in the target spatiotemporal window receive the message; (2) Scalability – the system must handle millions of devices without prohibitive overhead; (3) Timeliness – delivery latency should remain low enough for practical use; (4) Privacy Preservation – the service must hide precise location, time, and identity information from both the network operator and potential adversaries; and (5) Operational Efficiency – the solution should avoid heavyweight databases or per‑device state that would burden the operator.
The core contribution is a Cluster‑based Spatiotemporal Multicast (CSTM) scheme. In CSTM, the cellular infrastructure is partitioned into geographic‑temporal clusters, each associated with a set of base stations (BSs). For each time slot (e.g., every 10 minutes) the network operator generates a fresh seed value. Every cluster derives a one‑time key from this seed using a hash chain. Mobile devices that are currently attached to a BS within a cluster receive the derived key and locally compute a token by applying a blind signature to the key. The token is stored on the device and never transmitted back to the operator. When a service provider wishes to broadcast a message to devices that were in a particular area during a past interval, it obtains the list of tokens associated with the relevant clusters and time slots. Devices periodically poll the network for messages; upon receiving a candidate message, a device checks whether it possesses a matching token. If a match is found, the device decrypts and displays the message. Because the operator only sees token hashes, it cannot reconstruct the exact trajectory of any device, and the blind signature prevents linking a token to a specific subscriber. Tokens are designed to expire after a short lifetime (e.g., 24 hours), thereby limiting the window for correlation attacks.
The privacy analysis focuses on two quantitative metrics: Anonymity Loss (the reduction in the size of the anonymity set caused by the protocol) and Association Attack Success Rate (the probability that an adversary can correctly associate a device with a spatiotemporal region). Using a large‑scale simulation (100 000 devices, 500 BSs, realistic mobility traces), the authors demonstrate that CSTM reduces anonymity loss by more than 70 % compared with a naïve broadcast approach and keeps association‑attack success below 5 %. These results indicate that the token mechanism effectively decouples location information from device identity.
Performance evaluation examines delivery latency, network overhead, and token‑management cost under varying cluster sizes and token‑renewal intervals. With a cluster radius of roughly 5 km and a token renewal period of 10 minutes, the average end‑to‑end latency for a message is about 120 ms, and the additional traffic generated by token distribution and message polling amounts to a 15 % increase over baseline traffic (i.e., a traffic‑growth factor of 1.15). Token storage consumes less than 3 % of total system resources, confirming that the scheme remains feasible for real‑time applications.
The authors acknowledge several limitations. First, token generation and revocation are currently centralized, creating a single point of failure and a potential privacy bottleneck. Second, re‑clustering (e.g., when network topology changes or during large‑scale events) incurs non‑trivial overhead that may affect latency. Third, the scheme assumes relatively synchronized time slots; highly asynchronous mobility patterns could reduce token match rates. To mitigate these issues, the paper proposes future work such as blockchain‑based distributed token management, dynamic clustering algorithms that adapt to traffic density, and machine‑learning models that predict mobility patterns to pre‑emptively adjust token lifetimes.
In conclusion, the study presents a novel, privacy‑preserving approach to delivering messages to devices based on their historical presence in a location. By combining cluster‑level tokenization, blind signatures, and hash‑chain key derivation, CSTM achieves a strong balance between functional requirements (accuracy, scalability, timeliness) and privacy guarantees (anonymity, resistance to correlation attacks). The extensive simulation results validate both the security properties and the operational efficiency of the design, laying a solid foundation for future deployments in smart‑city infrastructures, public‑health alert systems, and law‑enforcement tools.
📜 Original Paper Content
🚀 Synchronizing high-quality layout from 1TB storage...