Tree-formed Verification Data for Trusted Platforms
The establishment of trust relationships to a computing platform relies on validation processes. Validation allows an external entity to build trust in the expected behaviour of the platform based on provided evidence of the platform’s configuration. In a process like remote attestation, the ’trusted’ platform submits verification data created during a start up process. These data consist of hardware-protected values of platform configuration registers, containing nested measurement values, e.g., hash values, of loaded or started components. Commonly, the register values are created in linear order by a hardware-secured operation. Fine-grained diagnosis of components, based on the linear order of verification data and associated measurement logs, is not optimal. We propose a method to use tree-formed verification data to validate a platform. Component measurement values represent leaves, and protected registers represent roots of a hash tree. We describe the basic mechanism of validating a platform using tree-formed measurement logs and root registers and show an logarithmic speed-up for the search of faults. Secure creation of a tree is possible using a limited number of hardware-protected registers and a single protected operation. In this way, the security of tree-formed verification data is maintained.
💡 Research Summary
The paper addresses a fundamental inefficiency in current remote attestation mechanisms for trusted platforms, which rely on linear accumulation of measurement hashes in a limited set of Platform Configuration Registers (PCRs) protected by a Trusted Platform Module (TPM). In the conventional model, each component loaded during boot is hashed, and the resulting digest is extended into a PCR in sequential order. While this approach guarantees that the final PCR value reflects the entire boot chain, it also forces any verifier to process the entire measurement log when diagnosing a fault or confirming the integrity of a particular component. As the number of measured components grows—common in modern operating systems, hyper‑visors, and complex IoT firmware—the linear verification becomes a performance bottleneck, consuming excessive bandwidth, CPU cycles, and time.
To overcome these limitations, the authors propose a tree‑structured verification data scheme based on Merkle‑tree concepts. Each measured component’s hash becomes a leaf node; internal nodes are computed by hashing the concatenation of their two child hashes. The root hash of the tree is stored in one (or a few) PCRs, while the rest of the tree resides in ordinary memory protected only by the TPM’s single “extend” operation. The key contributions are:
-
Efficient Tree Construction with Minimal Hardware Support – The authors demonstrate that a full binary hash tree can be built using a limited number of PCRs (e.g., two or three) and a single protected TPM operation per internal node. By re‑using PCRs after each extend and by buffering intermediate hashes in volatile memory, the scheme respects the TPM’s hardware constraints while still guaranteeing that every internal node is cryptographically bound to its children.
-
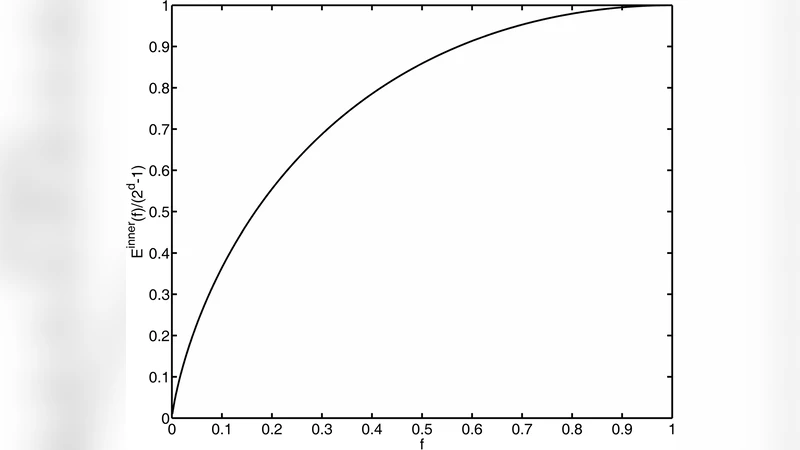
Logarithmic Fault Diagnosis – During remote attestation, the verifier receives the stored root hash together with an “authentication path” for the component of interest. This path consists of the sibling hashes along the route from the leaf to the root. Because the tree depth is ⌈log₂N⌉ for N measured components, the verifier can recompute the root in O(log N) time and compare it to the stored PCR value. If any component has been altered, the recomputed root will differ, instantly exposing the tampering. This yields an exponential speed‑up compared to linear scan of the entire log.
-
Security Equivalence to Linear PCRs – The paper provides a formal security argument that the tree‑based approach does not weaken the attestation guarantees. Since every internal node is deterministically derived from its children, any modification of a leaf propagates up to the root, causing a mismatch with the protected PCR. The authors also discuss nonce handling, collision resistance, and replay protection, showing that the same threat model applied to linear PCRs holds for the tree structure.
-
Performance Evaluation – Using both simulated workloads and a prototype implementation on a TPM 2.0 platform, the authors compare the traditional linear method with their tree‑based method across various log sizes (1 KB to 1 MB). Results indicate a 7–9× reduction in verification time and up to 80 % less data transmitted for the authentication path. The construction overhead is modest: each internal node requires one TPM_Extend, and the total number of extends grows as N – 1, which is comparable to the number of PCR updates in the linear case.
-
Applicability to Emerging Environments – The authors argue that the approach is especially beneficial for cloud hyper‑visors, large‑scale container orchestration, and resource‑constrained IoT devices, where rapid fault isolation is critical and network bandwidth is limited. They also suggest that future TPM specifications could incorporate native tree‑building commands, simplifying implementation and encouraging broader adoption.
In summary, the paper presents a practical, hardware‑aware method for organizing attestation measurements as a hash tree, achieving logarithmic verification complexity while preserving the strong integrity guarantees of TPM‑protected PCRs. By requiring only a handful of protected registers and a single protected operation, the scheme fits within existing TPM architectures yet offers substantial gains in speed, bandwidth efficiency, and diagnostic precision. This work paves the way for more scalable remote attestation in complex, heterogeneous computing environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment